critical chrome use-after-free vulnerability CVE-2025-9478
If you open your browser and think you’re safe, take a minute to read this. The important Chrome use-after-free bug A serious memory issue called CVE-2025-9478 lets an attacker take full control of a computer with just one bad webpage. This isn’t just a theoretical problem; it’s the kind of bug that happens when browser visuals, memory management, and real exploit code all come together. It has to be corrected right immediately.
Updating your browser may seem like a normal thing to do, but it’s actually one of the finest things you can do every day to protect yourself. You should think of this as a recall for your car: you should stop driving and take it to the shop as soon as you get the notice. The rest of this page goes into great depth on who is affected, how the problem works, and what to do next.
A short technical explanation of angle and why it mattersANGLE is a piece of code in Chrome that converts online graphics calls into commands that the GPU can understand. Think of it as a translator that makes it possible to safely create complex 3D or accelerated material on web pages that work on all platforms. Because visuals are so important to modern experiences, bugs in ANGLE have a big effect on the browser attack surface.
If that translator doesn’t handle memory correctly, a use-after-free scenario could happen. In short, the software starts using memory after it has been returned to the system. Attackers can go in via that hole, mess up the heap, and turn a pretty web animation into something far worse.
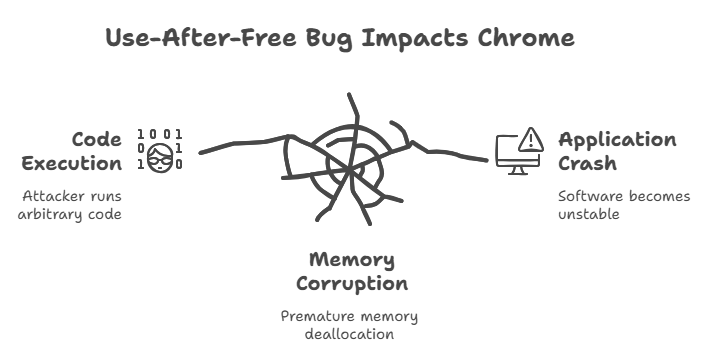
To put it simply, a use-after-free bug is when you lend someone a tool and then say you don’t own it anymore while they keep using it. The same mistake happens when a program frees up memory while another part of the program still has a reference to it. An attacker may use that old reference to put random values in places where the software expects harmless data.
This is the basic idea for regular users: Developers know how dangerous the use-after-free memory corruption problem is. In the worst cases, it lets an attacker run any code they want inside the compromised application. In a browser, this lets the attacker pretend to be your software. Most of the time, it causes crashes.
What this Chrome bug looks like on the insideThis particular issue has been assigned the CVE-2025-9478 number and is found in the ANGLE code path. A well-made HTML site could produce a succession of calls that free up memory too soon and then use it again in a way that damages heap structures. A sequence of exploits turns that corruption into code that can be run. What started as a simple visit to a website could end with arbitrary code execution.
In a recent stable release, Chrome developers solved the fault by changing how ANGLE handles object lifetimes and access patterns to stop memory from being reused incorrectly. The people who made the fix worked hard to close the window that hackers may utilize to put bad files into free RAM.
Timeline and discovery: how the bug was foundThe Chromium team found out about the flaw in August 2025 and quickly fixed it in a stable channel upgrade. Public advisories link to the exact builds that have the repair and explain what the problem is.
That speedy response is typical of modern browser security operations, which go quickly from detection to triage to patching to release. But just because a patch is there doesn’t mean the risk is gone. Some machines will still be susceptible until administrators or users apply the update because of how quickly attackers work and how long it takes to disclose information. The best thing to do is to check your version and update right away.
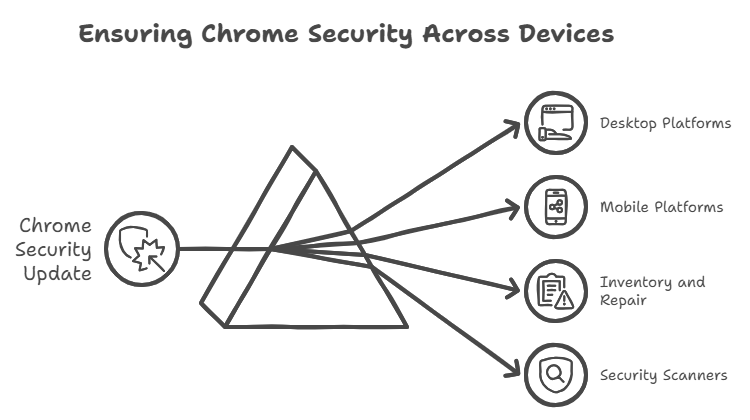
Chrome platforms and versions that were affectedAny version of Chrome before 139.0.7258.154 should be viewed as unsafe because the patch for this problem was included in Chrome 139 builds. You should assume that the update includes desktop and many mobile installs.
It was originally issued on desktop platforms and then quickly followed by mobile builds that were the same. Check both your personal and fleet devices for previous builds. Security scanners and vulnerability management programs have already implemented checks for this version boundary. If you are in charge of more than one device, rapidly take an inventory of them and mark anything below the corrected build for quick repair.
The risks of running random codeWhen a browser bug leads to arbitrary code execution, an attacker can get around the restricted context of a web page and run instructions on your computer. In fact, this might mean downloading malware, launching a backdoor that stays active after the browser session ends, or stealing session tokens.
Through the browser, an attacker can often get to the rest of the device.If you think you only visit trustworthy websites, remember that drive-by or hacked ad networks might secretly send people to meticulously made pages. The user doesn’t need to download anything to use the attack chain. If the memory flaw is used as a weapon, one well-made frame or resource may be enough.
Realistic attack examples and situationsOne possible scenario is when someone with an old version of Chrome clicks on what seems like a news link. The page, or an ad iframe on it, carries a payload that is specifically designed to add a remote access trojan by using the “use-after-free” method and then running shellcode.
Then, attackers might go off to the side or grab credentials. That is how other browser vulnerabilities have worked, so it’s not science fiction.Another example is shared workstations or public kiosks. An attacker might host or embed a malicious page and then wait for any browser that hasn’t been patched to visit. In short, any computer that connects to the internet without the patch could be easily hacked.
Public documents and evidence of abuseNews stories and public advisories about the fix and the nature of the issue were known at the time of publication, even though evidence of extensive exploitation in the wild is not always immediately available. Researchers and security teams usually send out advisories once a patch is published to stop attackers from getting an easy playbook before people update.
The risk level is severe, nevertheless, because the vulnerability lets prepared material corrupt memory from a distance. Assume active risk until your version is the same as or higher than the patched build.
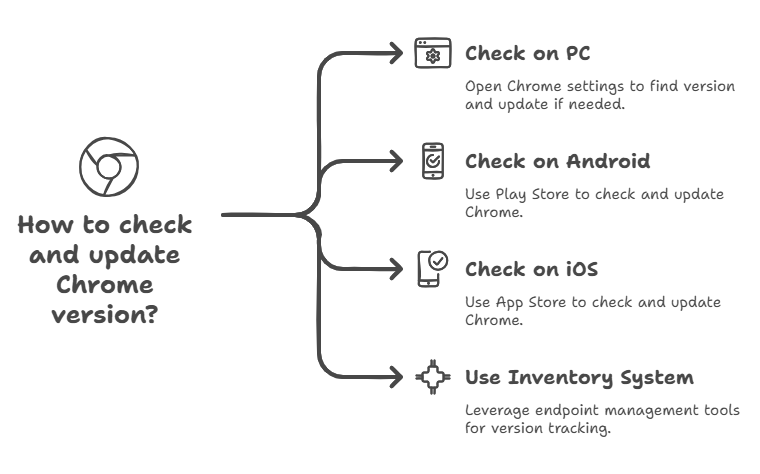
How to tell if Chrome is at riskOn your PC, open Chrome, then click on Settings, Help, and lastly About Google Chrome. After checking for updates, the browser will tell you the version number. If your version is less than 139.0.7258.154, you need to update right immediately. To check for Chrome updates on Android, open the Play Store. To check for updates on iOS, open the App Store when they are available.
If you have to keep track of a lot of PCs, you can either execute a simple script to get the browser version string or ask your inventory system what versions of Chrome are installed. Many endpoint management products already have this feature, which can automatically find hosts that are at danger.
1Step-by-step instructions for patching mobile and desktop devicesBuilt-in updating is the fastest way for most people to get updates. On a Mac or Windows machine, go to chrome://settings/help, wait for the update to finish downloading, and then restart the browser. Mobile users should use their device’s store to get the most recent version of Chrome.
If the automatic update doesn’t work, you can always download the latest installer from the official Chrome website. Use your patch management system to set up the update for business settings. Test it out with a small group first, then roll it out to the whole firm right away. If you can’t patch immediately away, think about short-term fixes like blocking access to harmful websites with web filtering or letting users who haven’t been patched utilize browser isolation.
Temporary fixes and other ways to lessen the damageIf you can’t update immediately away, hardening measures will help keep you safe. If you can, turn off or limit access to WebGL and other advanced graphics technologies. Set up content security policies at the web server level and, if you can, turn on strong site isolation to decrease the risk of loading untrusted frames.
Use endpoint detection tools to look for strange process activity that could be a sign of an exploitation attempt.Also, consider using a hardened browsing environment that keeps rendering on a distinct host, such as browser sandboxing or remote browser isolation. They lower the blast radius while you remedy the problem, but they don’t replace patching.
Ideas for businesses and their IT departmentsQuickly patch, then check the inventory, and then verify. To avoid problems at work, companies should make this upgrade their top priority and follow the rules for managing changes. Set up communication campaigns and work with help desks to help users understand why they need to update and restart their computers.Keep track of and record every time you try to upgrade something.
Also, make sure that essential systems like developer PCs, remote desktops, and shared workstations aren’t running old versions. If your environment supports version enforcement, utilize automated methods to stop earlier versions from running.
Questions that people often ask, things that people often get wrong, and blundersMyth: “It only affects people who use Windows.” No. Any platform that supports ANGLE rendering and the vulnerable Chrome build may be at risk. False: “I’m fine because I only go to safe sites.” Not true; ads and other information from outside sources can still spread exploit vectors on websites that you can trust.
Always verify your version again instead of believing you’re safe.Don’t believe anyone who says the bug is “just a crash.” Instability was often the first sign that memory corruption was about to happen, which led to earlier exploits. Keep an eye out for crashes and weird behavior; these are early warning indications that something is wrong.
Summary
Summary and helpful next steps: The best and easiest thing you can do right now is to update Chrome to the patched build. The update fixes the serious Chrome use-after-free vulnerability CVE-2025-9478, which is severe because it lets carefully prepared web content run arbitrary code.If you are in charge of devices, do an inventory scan, push updates, and turn on compensating controls if patching takes too long. If you are in charge of users, make sure to communicate carefully and treat the update like a safety recall. Quick, little acts can keep a lot of people safe in cybersecurity.
Hoplon Infosec’s Endpoint Security service can help keep devices safe from exploits like this Chrome vulnerability.
Follow us on X (Twitter) and LinkedIn for more cybersecurity news and updates. Stay connected on YouTube, Facebook, and Instagram as well. At Hoplon Infosec, we’re committed to securing your digital world.