Salesloft Drift Hack Salesforce OAuth Token Theft
It began softly, like the slightest radio static. After that, every cybersecurity headline mentioned the same disturbing incident: Salesforce OAuth Token Theft via Salesloft Drift Hack. It sounded to most like just another technical scandal that would eventually go away. However, it was a loud alarm for those in corporate IT rooms.
This went beyond a ransomware splash screen or an email leak. This was not like the others. Hackers had figured out how to enter company treasure troves covertly without causing damage to windows or locks. They just entered using trusted keys, which were OAuth tokens.
What is the Salesloft Drift Hack?
Many business leaders initially questioned, “What even happened?” when news of the incident broke. The Salesloft Drift hack was not a malware download or a haphazard phishing scam. Rather, hackers exploited reliable software platform integrations. Both Salesloft and Drift are effective tools for sales teams that integrate with Salesforce to handle client relationships.
When hackers discovered this connection, they knew it was a treasure trove. They entered through unguarded side doors rather than directly attacking Salesforce’s large fortress. The Salesforce OAuth token theft method used in the Salesloft Drift hack functioned similarly to retrieving a dropped master key. Just silent access, with no brute force and no alarms.
How Salesforce Was Targeted by Hackers Tokens for OAuth
The purpose of OAuth tokens is to simplify life. They allow applications to communicate with one another without exchanging real passwords. However, they become skeleton keys when stolen. In this instance, OAuth tokens connected to Salesforce corporate accounts were taken by the attackers.
Consider giving a friend who has an extra key to your car. Imagine now that a stranger could duplicate that key and use your vehicle whenever they so choose. That’s what took place here. The hackers didn’t have to get past firewalls or guess login credentials. To access data directly within Salesforce, they merely replayed these tokens.
OAuth Tokens’ Silent Power
OAuth tokens’ invisibility is what makes them so dangerous. The majority of corporate monitoring tools keep tabs on suspicious devices, password resets, and logins. OAuth omits that. It is uncommon to question a token once it has been approved. Hackers used this trust as a weapon in the Salesforce OAuth token theft in the Salesloft Drift hack.
It’s similar to using a staff badge to enter a building covertly. When they see the badge, security personnel wave you through, assuming it is legitimate. These tokens frequently don’t need to be refreshed for days or even weeks. Attackers had plenty of time to investigate because of this.
The Reasons Salesforce Was the Ideal Target
Salesforce is home to thousands of businesses’ most valuable assets, including financial records, sales pipelines, contracts, and customer data. Hackers gained access to extremely private company data by targeting Salesforce via Drift and Salesloft.
Salesforce was a gold mine for attackers. Additionally, they obtained access without ever blowing the door open by using stolen OAuth tokens. It’s easy to understand their decision. They compromised the system that housed all of the customer data rather than breaking into individual laptops.
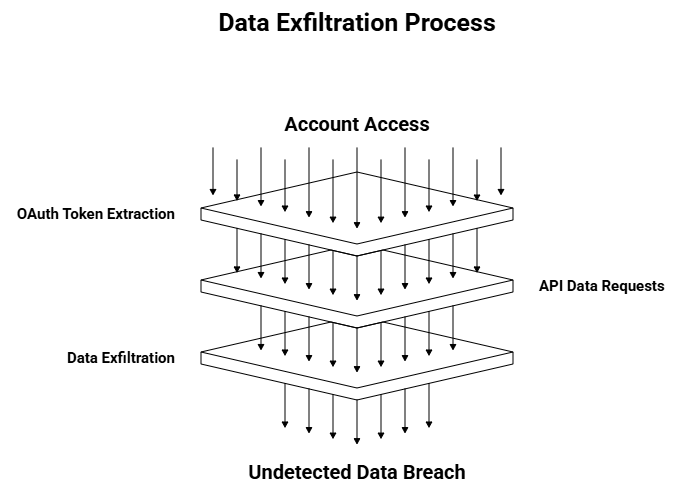
Step-by-Step Attack Workflow
Like detectives at a crime scene, investigators pieced together the workflow. Attackers first gained access to accounts on Drift or Salesloft. After that, they extracted OAuth tokens connected to Salesforce integrations. They used these tokens to make direct requests for data from Salesforce’s APIs.
Consider it akin to pilfering inter-system wiring. The hack’s cleanliness was the true surprise. No yelling alerts, no sloppy malware footprints. Just data, like water leaking from a broken pipe, quietly escaping Salesforce corporate instances.
Who Could Have Caused the Breach?
Early indications suggested organized groups that prioritized data theft over quick money grabs, even though attribution in cybercrime is always difficult. State-sponsored actors who profit from corporate intelligence were proposed by some experts. Others were more inclined to join gangs with financial incentives in the hopes of selling stolen Salesforce data in black markets.
It is evident that the Salesforce OAuth token theft in the Salesloft Drift hack was not an isolated incident. It was focused, accurate, and executed with an understanding of how enterprise integrations function. That degree of proficiency suggested professionals rather than amateurs.
The Scale of the Data Exfiltration
The scope of the data exfiltration reports suggested that thousands of corporate Salesforce instances were under investigation. Customer lists, contracts, private emails, and negotiation details were made public for many businesses. Some businesses acknowledged that outsiders might have noticed their competitive tactics.
It is challenging to quantify the actual harm when data flows so subtly. This breach left no obvious damage, in contrast to ransomware, which encrypts files and stops operations. What was taken and who might use it were the sources of the harm.
Effect on Businesses Using Drift and Salesloft
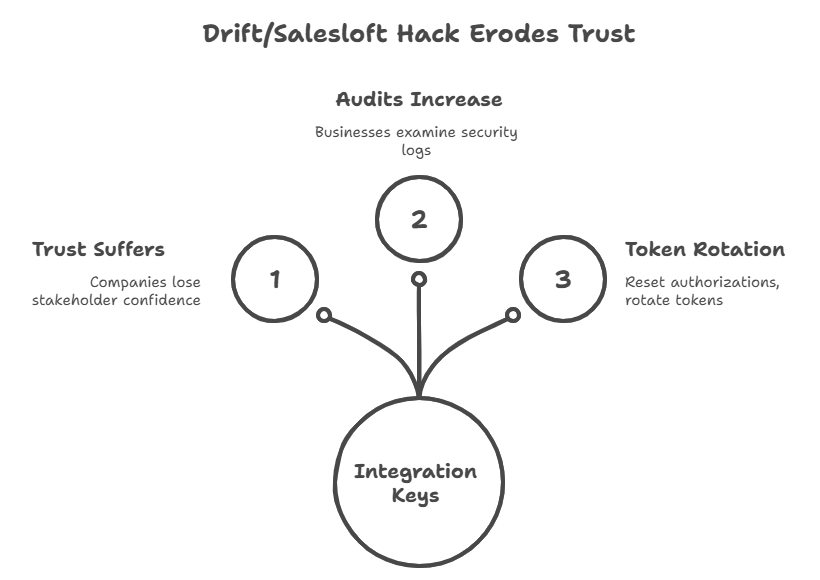
Trust suffered greatly for companies that depended on Drift and Salesloft. Instead of making sales riskier, these tools were meant to make them more seamless. Boardrooms were suddenly filled with questions for CIOs and CTOs. How could a catastrophe result from something as simple as integration keys?
Some businesses put these integrations on hold. Others hurried to examine audit logs, reset authorizations, and rotate tokens. The Salesforce OAuth token theft in the Salesloft Drift hack served as a sobering reminder that even convenient features can have unintended risks.
The Impact on Workers and Customers
Salespeople are concerned that their client information may now be circulating on hacker forums. Clients feared that private deals or personal data were exposed. When they discovered that their work tools had turned into entry points for criminals, even employees who had never interacted with Salesforce directly felt uneasy.
Many saw the incident as a reminder of the true interconnectedness of work tools. Entire business ecosystems were compromised by a single, minor flaw in a sales app. The focus shifted from a single breach to the repercussions on customers and partners.
Industry Reactions and Expert Opinions
Experts in cybersecurity swiftly offered their opinions. Some referred to it as an OAuth security wake-up call. Others emphasized that businesses had become overly accustomed to integrating third parties. It’s like giving delivery drivers extra keys to your office, according to one analyst. Until someone misplaces the keys, it functions perfectly.
The response from the industry was urgent and frustrated. The message was clear: linked apps can turn into weak points, even though Salesforce stressed that its own systems were not specifically compromised.
Implications for OAuth Security in 2025
OAuth security gained attention as a result of this breach. For many years, businesses viewed tokens as technical glue between apps and background information. They were now the focus of a corporate hack that made headlines.
Businesses need to reconsider their approaches to monitoring, revocation procedures, and token lifespans in 2025. The Drift hack for Salesloft Theft of Salesforce OAuth tokens demonstrated how an attacker’s primary tool can be something that appears to be a technical shortcut.
Takeaways from the Drift Hack in Salesloft: Theft of Salesforce OAuth Tokens
There are lessons to be learned from every hack, and this one was no exception. First, convenience may cause us to overlook dangers. Second, integrations require the same level of oversight as login systems. Third, businesses need to presume that attackers are more familiar with these shortcuts than defenses.
The incident turned into a case study of the distinct ways in which cybercriminals think. They entered the castle covertly through servant doors without anyone noticing, rather than by storming it. For many businesses that believed their defenses were strong, it was a sobering experience.
Preventing Similar Attacks on Corporate Systems
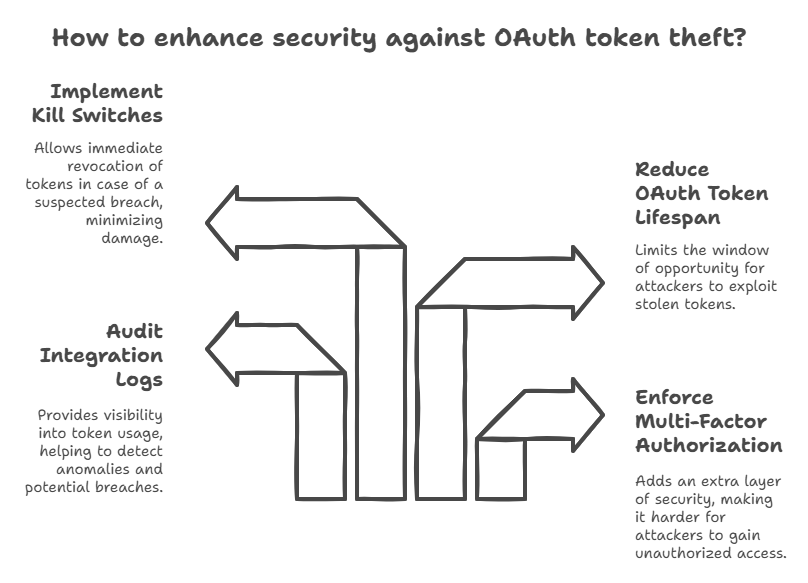
It is not impossible to be protected. Businesses can enforce multi-factor authorizations even on app connections, audit integration logs more thoroughly, and reduce the lifespan of OAuth tokens. In the event of a suspected breach, some experts advise constructing kill switches to immediately revoke all tokens.
Despite their technical sound, these measures are important. If the Salesforce OAuth token theft from the Salesloft Drift hack taught us anything, it was that invisibility is what attackers love. One way to stop them is to draw attention to token usage.
The Enterprise Security Big Picture
This hack ultimately involved more than just Drift, Salesloft, or Salesforce. It dealt with enterprise security’s future in an increasingly interconnected world. These days, every business uses dozens of integrated apps, each of which has relationships of silent trust. If one falls, the domino effect can be huge.
The lesson for leaders is obvious. Passwords and firewalls are no longer the only aspects of security. The hidden keys that we hardly ever consider are the invisible trust links. Not only will the Salesforce OAuth token theft from the Salesloft Drift hack be remembered as another security breach, but it will also be remembered as the moment tokens emerged as the new frontline of cyber defense.
Hoplon Infosec uses professional web application security and penetration testing to help stop incidents like the Salesforce OAuth token theft that occurred during the Salesloft Drift hack.
Follow us on X (Twitter) and LinkedIn for more cybersecurity news and updates. Stay connected on YouTube, Facebook, and Instagram as well. At Hoplon Infosec, we’re committed to securing your digital world.