Cisco has recently released security advisories addressing multiple vulnerabilities within its Cisco IOS XR Software, primarily focusing on a critical memory corruption vulnerability in the Border Gateway Protocol (BGP) confederation implementation. This vulnerability, identified as CVE-2025-20115, has been assigned a CVSS score of 8.6, marking it as a high-severity issue. It could allow unauthenticated, remote attackers to trigger denial-of-service (DoS) conditions on affected network infrastructures if exploited.
In this article, we will delve into the specifics of the vulnerability, its potential impact, affected software versions, and the necessary mitigation steps organizations should take to secure their networks.
Understanding the Cisco BGP Confederation Vulnerability (CVE-2025-20115)
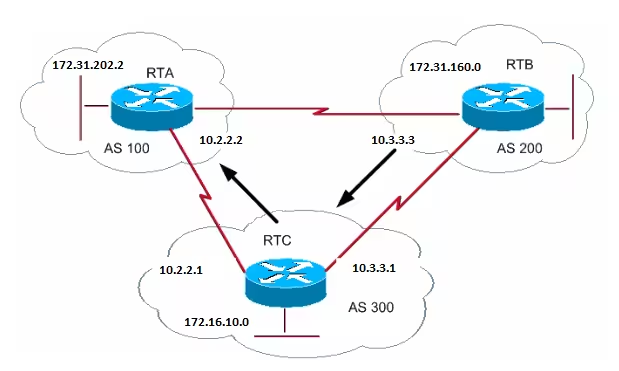
The CVE-2025-20115 vulnerability, also known as cisco-sa-iosxr-bgp-dos-O7stePhX, stems from memory corruption caused when a BGP update contains an AS_CONFED_SEQUENCE attribute with 255 or more autonomous system numbers (ASNs). This overflow results in a buffer overflow condition, classified under CWE-120 (Buffer Copy without Checking Size of Input).
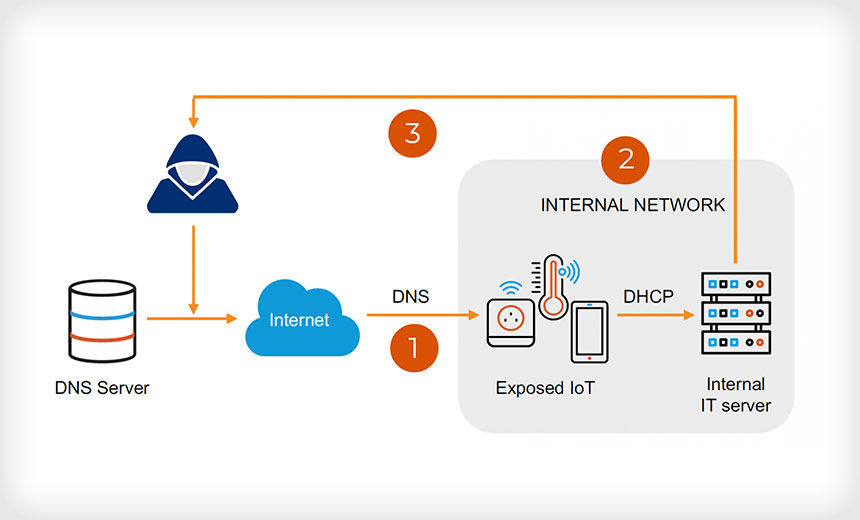
BGP is a crucial component of modern networking, exchanging routing information between autonomous systems (AS). When misconfigured or exploited, vulnerabilities within BGP can lead to severe network disruptions, routing failures, and even complete service outages.
Organizations utilizing Cisco IOS XR software with BGP confederation enabled should take immediate action to assess their network exposure and apply necessary security patches or mitigations.
Technical Details and Exploitation
According to Cisco’s official security advisory, released on March 12, 2025, this vulnerability allows attackers to disrupt networking operations through crafted BGP update messages. By exploiting this flaw, an attacker can cause memory corruption, forcing the BGP process to restart leading to a network-wide denial of service (DoS) condition.
Prerequisites for Exploiting the Vulnerability
To exploit CVE-2025-20115, an attacker must:
- Control a BGP confederation speaker within the same autonomous system (AS) as the victim.
- Access a network configuration where the AS_CONFED_SEQUENCE attribute naturally exceeds 255 ASNs.
This means that the risk of exploitation is higher in networks with complex BGP confederation setups where multiple ASNs are involved.
Affected Cisco IOS XR Versions
The vulnerability affects multiple Cisco IOS XR Software versions with BGP confederation enabled. The impacted versions include:
- 7.11 and earlier
- 24.1 and earlier
- 24.2 up to 24.2.20
Organizations using these versions should immediately verify their configurations and apply recommended security updates.
Potential Risks and Security Implications
The impact of CVE-2025-20115 is severe, as successful exploitation can result in:
- Complete denial of service (DoS): Network instability, traffic blackholing, or service disruptions.
- Disruption of routing operations: BGP session resets, leading to degraded network performance.
- Potential cascading failures: Network-wide outages affecting critical services and applications.
Since BGP is the backbone of internet routing, disruptions within autonomous systems (ASes) can have far-reaching consequences, potentially impacting internet service providers (ISPs), data centers, and enterprise networks.
How to Check if Your Devices Are Vulnerable
Network administrators should determine whether their Cisco devices are vulnerable by running the following command:
show running-config router bgp
If the output includes the line “BGP confederation peers,” it indicates that the device is using BGP confederation and may be affected by the vulnerability.
Mitigation and Security Patches
Cisco has provided security updates to address this vulnerability, and organizations should immediately update their devices to a secure version.
Recommended Updates
Organizations should upgrade to the following Cisco IOS XR Software versions that are not affected by CVE-2025-20115:
- 24.2.21 (upcoming release)
- 24.3.1
- 24.4
Applying these updates ensures that the BGP process remains stable, preventing potential denial-of-service attacks caused by buffer overflows.
Workarounds for Organizations That Cannot Upgrade Immediately
For organizations unable to immediately apply patches, Cisco has provided a temporary workaround to mitigate the risk of exploitation. The workaround involves restricting the AS_CONFED_SEQUENCE attribute to 254 or fewer AS numbers using a routing policy.
Implementing the Routing Policy Workaround
Administrators should create a max-asns route policy and apply it to BGP neighbor configurations.
Step 1: Create a Route Policy
route-policy max-asns
if the as-path length is 255, then
drop
endif
end-policyStep 2: Apply the Policy to BGP Neighbors
router bgp <ASN>
neighbor <PEER-IP> policy max-asns in
neighbor <PEER-IP> policy max-and outThis policy prevents BGP updates containing an AS_CONFED_SEQUENCE attribute with 255 or more ASNs from being processed, thereby mitigating the risk of memory corruption.
Cisco’s Response and Security Recommendations
The Cisco Product Security Incident Response Team (PSIRT) has confirmed that there are no known cases of malicious exploitation of this vulnerability in the wild. However, given the high CVSS score (8.6) and the potential impact on critical network infrastructures, organizations should urgently treat this advisory.
Recommended Actions for Organizations
- Upgrade to a secure version of Cisco IOS XR Software (24.3.1 or later) as soon as possible.
- If upgrading is not feasible, apply the routing policy workaround to restrict AS path lengths.
- Monitor network logs for unusual BGP activity and check for attempted exploitation.
- Regularly update security policies and maintain an up-to-date incident response plan for network disruptions.
- Follow Cisco’s advisories and subscribe to security alerts to stay informed about future vulnerabilities.
Conclusion
The CVE-2025-20115 vulnerability in Cisco IOS XR Software poses a significant security risk to BGP confederation networks. If exploited, it can lead to denial-of-service conditions, disrupting network operations and causing potential service outages.
Organizations must act swiftly to patch affected systems, implement mitigation strategies, and strengthen their BGP security configurations. By following Cisco’s recommended updates and workarounds, network administrators can protect their infrastructure from potential attacks and ensure network stability.
For further details, refer to Cisco’s official security advisory and consult with security professionals to assess your organization’s specific risk exposure.
More at:
https://cybersecuritynews.com/cisco-warns-of-ios-xr-software-vulnerability/