Cybercriminals are continuously evolving their methods to bypass traditional security measures, and a new sophisticated phishing campaign has emerged that uses virtual hard disk (.vhd) files to deliver the dangerous VenomRAT malware. This detailed analysis explains how the Attack works, the techniques used by the threat actors, and what individuals and organizations can do to defend themselves.
Modern phishing tactics have evolved well beyond simple spam emails. Cybercriminals now employ advanced methods to disguise malware and evade detection. In this campaign, virtual hard disk (.vhd) files—a trusted format typically used in IT environments—are repurposed to hide malicious code. The use of .vhd files in phishing attempts poses a new challenge for security solutions, requiring a multi-layered approach to detection and prevention. This article provides an in-depth exploration of the attack chain and offers practical recommendations for improving cybersecurity defenses.
The Evolving Threat Landscape
Digital threats are constantly adapting to new technologies and environments. Traditional phishing emails may be easily recognized, but the current trend involves integrating less suspicious file types, such as .vhd files, to camouflage malware. These files are commonly used in virtual machine environments and storage systems, making them a natural choice for attackers who want to avoid immediate detection.
The Shift in Attack Vectors
The move to incorporate legitimate file formats in phishing campaigns marks a significant shift in tactics. Cybercriminals understand that users and security systems may not scrutinize these files as rigorously as other types of attachments. By leveraging trusted formats, they can slip past many initial defenses and maintain a low profile while executing their malicious activities.
Challenges for Security Solutions
Traditional security tools, which rely heavily on signature-based detection, often overlook benign file formats. The sophisticated obfuscation techniques used within these files add another layer of complexity, making it even more difficult for automated systems to identify malicious intent. This shift calls for advanced monitoring and behavior analysis to spot anomalies that standard defenses might miss.
Phishing Emails: The Initial Point of Compromise
The Attack begins with phishing emails that are cleverly disguised as legitimate purchase order communications. These emails target employees involved in procurement or accounting, using familiar business language to instill trust and prompt action.
The Role of Social Engineering
Social engineering is a key element in this phishing strategy. The emails create a sense of urgency and authenticity, encouraging recipients to open the attached archive without suspecting any foul play. Once the archive is extracted, the unsuspecting user discovers a .vhd file—a file type that is generally not flagged by standard security protocols.
Mounting the .vhd File
Upon extraction, the .vhd file mounts itself as a new drive on the user’s system. This action is crucial, as it sets the stage for the execution of the hidden payload. Because the file appears as a standard disk drive, many users and security tools may overlook its malicious intent.
The Role of Virtual Hard Disk (.vhd) Files in the Attack
Virtual hard disk files serve legitimate purposes in many IT environments, such as hosting virtual machines or storing large datasets. However, cybercriminals have exploited this familiarity to disguise their malicious activities.
Concealing Malicious Code
Inside the mounted .vhd file, a hidden batch script resides. This script is designed to carry out several dangerous actions once executed. The attackers have embedded multiple layers of obfuscation within the script to prevent detection and analysis. The use of a trusted file format allows the malicious code to bypass many initial security scans.
Multi-Layered Obfuscation
The batch file employs several obfuscation techniques, including:
- Garbage Characters: Random characters are inserted into the code to confuse signature-based scanners.
- Base64 Encoding: This method transforms the script into a seemingly benign string that conceals its true intent.
- AES Encryption: A strong encryption technique secures the actual malicious commands, making them difficult to decode without the proper key.
These techniques ensure that the malicious content remains hidden until it is actively executed, complicating efforts to analyze and mitigate the threat.
The Execution Process: From Batch Script to PowerShell Commands
Once the .vhd file mounts, the hidden batch script is triggered, initiating a series of malicious operations that help the malware establish a foothold on the system.
Initial Execution Steps
The batch script first creates a copy of itself in a user-specific system directory (typically “C:\Users%userprofile%\dwm.bat”). This replication ensures that even if the initial script is removed, a backup remains to maintain the infection. This redundancy is a common tactic in persistent malware, designed to thwart removal efforts.
Leveraging PowerShell
After replicating itself, the script invokes Windows PowerShell—a powerful command-line tool that allows the execution of complex commands and scripts. By calling PowerShell, the malware can perform various system modifications without drawing attention. The obfuscated PowerShell commands further complicate detection, as they mask the underlying malicious operations and help the malware continue its attack chain with minimal risk of exposure.
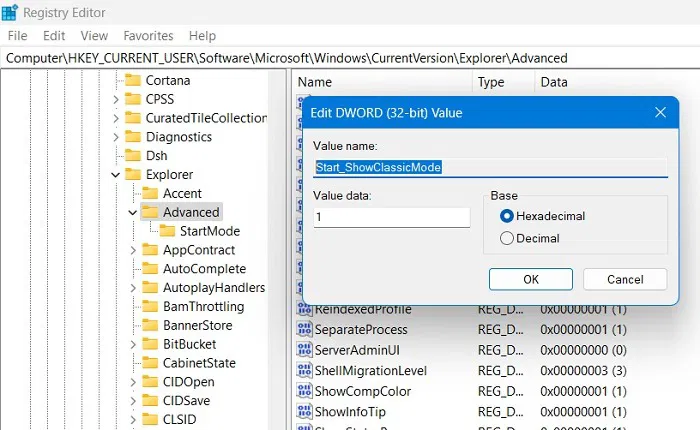
Registry Modifications and Persistence Mechanisms
Persistence is a hallmark of sophisticated malware. In this Attack, VenomRAT employs several methods to ensure it remains active in the infected system.
Modifying the Windows Registry
The malware makes deliberate changes to the Windows registry, a central database that controls system configuration. By altering registry entries, the malware ensures that its code is automatically executed every time the system boots. This mechanism provides a robust method of persistence, making the malware resilient to system restarts and other removal attempts.
Additional Persistence Techniques
Beyond registry modifications, the malware also drops files into the Startup folder. Files placed in this folder are automatically executed when the system starts, further reinforcing the malware’s ability to persist. This multi-pronged approach complicates traditional removal methods, as it embeds the malicious code in multiple system areas, ensuring continuous operation even if one vector is discovered and neutralized.
VenomRAT: Capabilities and Technical Breakdown
The payload identified in this phishing campaign is VenomRAT, specifically version 6.0.3, which comes equipped with advanced features for remote control and data exfiltration.
Hidden Virtual Network Computing (HVNC)
One of the standout features of VenomRAT is its support for Hidden Virtual Network Computing (HVNC). HVNC allows the attacker to remotely access and control the graphical user interface of the infected system without the user’s knowledge. This capability enables live monitoring of system activities and facilitates the extraction of sensitive data, posing a significant threat to both personal and corporate environments.
Data Logging and Secure Communication
VenomRAT drops a configuration file named DataLogs.conf in a user-specific directory (“C:\Users%userprofile%\AppData\Roaming\MyData\”). This file is critical for capturing keystrokes and other sensitive data. Embedded within the file are an AES encryption key and a salt value, which are used to secure communications between the infected system and the command and control servers. This encryption ensures that even if intercepted, the data remains inaccessible to unauthorized parties.
The Broader Impact of VenomRAT Infections
VenomRAT is not just another piece of malware—it represents a serious threat to both organizations and individuals. Its capabilities extend far beyond initial system compromise, leading to long-term security risks.
Risks to Organizations
For businesses, an infection by VenomRAT can result in the theft of sensitive corporate data, including intellectual property, financial records, and client information. The malware’s ability to capture keystrokes and take screenshots further amplifies these risks, potentially leading to identity theft, corporate espionage, or other forms of cybercrime. The persistence mechanisms embedded within the malware make it particularly challenging to remove, resulting in prolonged breaches that can significantly disrupt operations.
Risks to Individuals
On a personal level, the risks are equally severe. With access to keystroke data and system activity, attackers can steal personal credentials, monitor communications, and gain unauthorized access to banking or other secure accounts. The covert nature of VenomRAT’s operations means that many infections go unnoticed until significant damage has been done, underscoring the need for early detection and robust protection measures.
Mitigation Strategies: Strengthening Endpoint Security

Given the complexity and persistence of the VenomRAT threat, robust endpoint security measures are critical. Endpoint security involves protecting individual devices—such as laptops, desktops, and mobile devices—from malware and unauthorized access.
Real-Time Monitoring and Behavior Analysis
Modern endpoint security solutions employ real-time monitoring and behavior-based detection to identify anomalous activities that could indicate an infection. Advanced machine learning algorithms analyze patterns of behavior and flag any deviations that might signal a breach. By detecting unusual activities, such as unexpected batch file creation or unauthorized registry modifications, these systems can alert administrators to potential threats before they escalate.
Automated Remediation and Regular Updates
Automated remediation tools play an integral role in endpoint security. When suspicious activity is detected, these tools can isolate and neutralize the threat automatically, minimizing the potential impact. Furthermore, maintaining regular software updates and promptly applying security patches are essential for closing vulnerabilities that malware could exploit. This proactive approach forms the first line of defense against advanced phishing campaigns and persistent threats like VenomRAT.
Best Practices for Organizations to Prevent Phishing Attacks
Organizations must adopt a comprehensive strategy to safeguard against phishing attacks that employ advanced tactics. This strategy should address both technical defenses and the human element of cybersecurity.
Employee Training and Awareness
Employee awareness is the cornerstone of any effective cybersecurity strategy. Regular training sessions should educate employees about the latest phishing tactics and the importance of verifying the legitimacy of unexpected attachments. Emphasizing caution with purchase order emails and similar communications can significantly reduce the risk of successful phishing attempts.
Implementing Multi-Factor Authentication (MFA)
Multi-factor authentication (MFA) is a critical measure for protecting sensitive systems. By requiring additional verification steps beyond just passwords, MFA adds an extra layer of security. This reduces the risk of unauthorized access even if login credentials are compromised, especially in environments where remote access is common.
Integrating Threat Intelligence into Security Operations
Incorporating threat intelligence into your security strategy provides a proactive defense against emerging threats. Threat intelligence involves collecting, analyzing, and acting upon data regarding potential and known attack vectors.
Leveraging Threat Intelligence Feeds
Organizations can use threat intelligence feeds to monitor for suspicious activity related to mounting .vhd files or executing obfuscated scripts. These feeds supply valuable context—such as known malicious IP addresses or domains associated with command and control servers—allowing security teams to take preemptive action before an attack fully materializes.
Collaborative Security Measures
Collaboration between different departments and with external cybersecurity communities can enhance threat intelligence efforts. Sharing information about emerging attack vectors and indicators of compromise builds a collective defense that is better equipped to handle sophisticated threats. This collaborative approach ensures that security teams remain informed about the latest cyber developments and can respond swiftly to potential incidents.
Future Considerations in Cyber Defense
As cyber threats continue to evolve, so too must the strategies used to combat them. Organizations must be prepared to adapt to new attack vectors and continuously update their security protocols.
Embracing Advanced Technologies
Investing in advanced security technologies—such as artificial intelligence and machine learning—provides a significant edge in detecting and mitigating novel threats. These technologies enable faster response times and more accurate threat detection, helping organizations stay ahead of increasingly sophisticated cybercriminals.
Continuous Learning and Adaptation
The dynamic nature of cyber threats means there is no one-size-fits-all solution. Organizations must continuously evaluate and adapt their security measures based on the latest threat intelligence and emerging attack trends. Regular security audits, penetration testing, and active participation in cybersecurity forums are all essential practices for maintaining a robust security posture.
Embracing Cyber Hygiene and Long-Term Security Practices
At the core of any effective cybersecurity strategy lies robust cyber hygiene. Daily practices that ensure the security and integrity of digital systems are essential in minimizing risk.
Essential Cyber Hygiene Practices
Key practices include:
- Regular updates of software and operating systems to patch known vulnerabilities.
- Strong, unique passwords are updated periodically.
- Cautious handling of email attachments and links, even from seemingly trusted sources.
- Frequent backups of critical data to ensure recovery in the event of an infection.
- Continuous monitoring for unusual system behavior and prompt reporting of any anomalies.
These routine measures form the foundation of a secure digital environment and can greatly reduce the likelihood of a successful malware infection.
Building a Culture of Security
Fostering a culture of security within an organization goes beyond technical measures. It requires regular training, clear communication about potential threats, and an environment where employees are encouraged to report any suspicious activities. By embedding security into the daily operations and mindset of every employee, organizations create a resilient defense against sophisticated cyber threats.
Conclusion
The sophisticated phishing campaign utilizing virtual hard disk (.vhd) files to distribute VenomRAT malware is a clear indicator of the evolving landscape of cyber threats. By exploiting trusted file formats and employing advanced obfuscation techniques, attackers can bypass traditional security measures, posing serious risks to both organizations and individuals.
Through careful analysis of the attack chain—from the initial phishing email to the execution of obfuscated scripts and persistent system modifications—this article has highlighted the complexity and potential impact of such infections. VenomRAT’s advanced capabilities, including Hidden Virtual Network Computing and secure data logging, further underscore the importance of robust cybersecurity measures.
To defend against these advanced threats, organizations must invest in comprehensive endpoint security solutions, promote a culture of cyber hygiene, and continuously integrate threat intelligence into their operations. While no single solution offers complete protection, a layered security approach provides the best defense against persistent and sophisticated attacks.
By taking these proactive steps, you not only mitigate the risks associated with advanced phishing campaigns but also lay the groundwork for long-term digital safety. Remember, in the face of sophisticated cyber threats, a well-prepared defense is not just an option—it is an absolute necessity.
Source: Cybersecurity News