In today’s digital age, where virtually every aspect of our lives is connected to the internet, practicing good cyber hygiene has become essential. Just like personal physical hygiene—brushing your teeth, washing your hands, and exercising regularly—cyber hygiene involves everyday actions that protect your data and safeguard your online identity. With cyber threats evolving continuously, establishing daily habits to maintain your digital security is more critical than ever.
Understanding Cyber Hygiene and Its Importance
Cyber hygiene refers to the routine practices and steps you take to secure your digital presence, devices, and sensitive information. The concept revolves around proactive measures that can reduce the risk of cyber attacks, data breaches, and identity theft. Unlike reactive measures taken after an incident occurs, good cyber hygiene is about building robust defenses and a vigilant mindset every single day.
In recent years, the increase in ransomware attacks, phishing scams, and data breaches has underscored the need for improved cybersecurity practices for individuals and organizations alike. Cyber hygiene is not just about using antivirus software or updating your operating system—it’s a comprehensive lifestyle choice that requires commitment and regular maintenance. When practiced consistently, these habits not only protect your personal information but also reduce the burden on larger networks and systems that could be compromised if one weak link is exploited.
The Foundation of Cyber Hygiene: Strong Passwords and Authentication
One of the simplest yet most effective measures to protect your data is establishing strong passwords. Weak or reused passwords can be an easy target for hackers who use automated tools to guess common combinations. A robust password should be long, complex, and unique for each account. Alongside strong passwords, multi-factor authentication (MFA) adds an extra layer of security. MFA requires additional verification steps, such as a fingerprint scan, a one-time code sent to your mobile device, or a security token, making it significantly harder for unauthorized users to gain access.
Building Strong Passwords
Creating a password that is both memorable and secure can be challenging. One effective strategy is to use a passphrase—a sequence of words or a sentence—that is easy for you to remember but difficult for others to guess. Combining letters, numbers, and symbols further increases the strength of your passphrase. Using a trusted password manager can help store and generate strong, unique passwords for every account, ensuring that you never need to rely on the same password twice.
Embracing Multi-Factor Authentication
Multi-factor authentication transforms your online security by adding barriers that cannot be breached simply by knowing a password. Even if a hacker manages to obtain your password, they would still require the second factor to access your account. This habit, when adopted for critical services such as banking, email, and social media, greatly reduces the risk of unauthorized access.
Keeping Software and Devices Up-to-Date

One of the most overlooked aspects of cyber hygiene is the regular updating of software, operating systems, and applications. Developers routinely release patches and updates to fix security vulnerabilities that cybercriminals could exploit. By ensuring that your devices are always up-to-date, you minimize the chances of being exposed to known exploits.
The Role of Automatic Updates
Enabling automatic updates on your devices is one of the simplest ways to maintain good cyber hygiene. This habit not only saves time but also guarantees that you are always protected against the latest threats. For those who prefer manual updates, setting aside regular time each week to check for and install updates is a wise strategy.
The Benefits of Firmware and App Updates
Firmware updates for devices such as routers, printers, and IoT gadgets are equally important as software updates on your computer or phone. Many hackers exploit vulnerabilities in outdated firmware to infiltrate home networks. Similarly, keeping apps updated on your smartphone ensures that you are protected from potential exploits that could arise from older versions of the software.
Daily Internet Usage Habits: Safe Browsing and Email Practices
Safe browsing and email habits are integral components of a comprehensive cyber hygiene routine. The internet is replete with scams, malicious websites, and phishing attempts that can compromise your data if you are not cautious. Adopting safe browsing habits and being vigilant with email communications can save you from falling prey to these digital dangers.
Safe Browsing Practices
One key aspect of safe browsing is being cautious about the websites you visit and the links you click. It is important to verify the legitimacy of websites, especially when entering sensitive information such as passwords or credit card details. Look for secure indicators like “https://” in the URL and a padlock icon in the address bar. Avoid clicking on suspicious links, and be wary of websites that ask for unnecessary personal details.
Regularly clearing your browser cache and cookies also contributes to better online security. These actions reduce the amount of stored data that could be potentially exploited by hackers and improve your overall privacy.
Managing Email Security
Email remains one of the most common entry points for cyber attacks. Phishing emails often disguise themselves as legitimate messages from trusted sources. To safeguard your inbox, be skeptical of emails that request personal information or urge you to click on unexpected links. Always verify the sender’s address, and when in doubt, contact the organization directly using known contact details.
In addition to vigilance, consider using email services that offer built-in security features such as spam filters, encryption, and malware detection. These tools can significantly reduce the risk of falling victim to phishing attempts or other email-based scams.
Securing Your Devices and Home Network
Your digital security extends beyond your online accounts to the devices you use daily and the network they connect to. Ensuring that your devices are secure and that your home network is properly protected is crucial for maintaining overall cyber hygiene.
Device Security Measures
Every device you use, from your computer to your smartphone and even smart home devices, should have security measures in place. This includes installing reputable antivirus software, enabling firewalls, and ensuring that all security features provided by the manufacturer are activated. Regularly scanning your devices for malware and potential vulnerabilities is also a critical habit.
Furthermore, encrypting your devices adds another layer of protection. Encryption ensures that even if your device is lost or stolen, your data remains inaccessible to unauthorized individuals. Both Windows and macOS offer built-in encryption tools that can help secure your data with minimal effort.
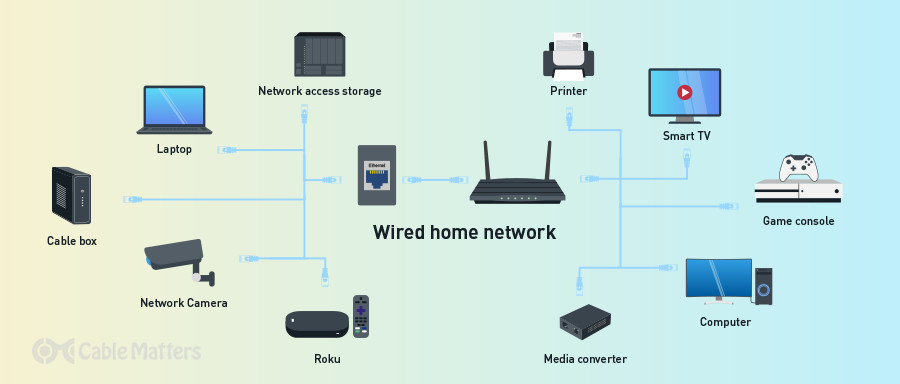
Protecting Your Home Network
Your home network serves as the gateway to all your devices, making it a prime target for hackers. Securing your Wi-Fi network starts with changing the default login credentials on your router. Default usernames and passwords are widely known among cybercriminals and can be a significant vulnerability if left unchanged.
Implementing WPA3 encryption (or WPA2 if WPA3 is not available) for your Wi-Fi network is essential. This encryption standard provides robust security for wireless networks. Additionally, consider setting up a guest network for visitors, which can keep your primary network and connected devices isolated from potential threats.
The Role of Data Backup in Cyber Hygiene
Even with the best preventive measures, data breaches and ransomware attacks can still occur. Regular data backups are a crucial part of a resilient cyber hygiene strategy. By maintaining up-to-date backups, you ensure that you can recover your important files and documents in the event of a cyber incident.
Establishing a Backup Routine
A reliable backup routine should include both local and cloud-based backups. Local backups, stored on external hard drives or network-attached storage devices, offer quick recovery options. However, they can also be susceptible to physical damage or theft. Cloud-based backups add an extra layer of redundancy and allow you to access your data from anywhere with an internet connection.
Setting a regular schedule for backups—such as daily incremental backups and weekly full backups—ensures that your data is continuously protected. Automating this process, where possible, minimizes the risk of human error or forgetting to perform backups.
Testing and Verifying Backups
Regularly testing your backups is just as important as creating them. Verifying that your data can be restored successfully ensures that you are prepared in case of an emergency. Establishing a routine for restoring a sample of your files and checking for integrity can save you significant time and stress during an actual data loss event.
Digital Footprint: Managing Privacy and Social Media
In addition to protecting your data, maintaining good cyber hygiene involves managing your digital footprint. This includes being mindful of the information you share online and understanding how your data can be used. Social media platforms, in particular, can be a double-edged sword—offering opportunities for connection while also posing significant privacy risks.
Evaluating Your Online Presence
Begin by reviewing your social media profiles and adjusting privacy settings to limit the amount of personal information visible to the public. Be cautious about accepting friend requests from unknown individuals, and think twice before sharing details about your location, travel plans, or daily routines. Many cyber attackers use this information to craft personalized phishing attacks or even physical break-ins.
Limiting Data Sharing
Consider the long-term implications of the content you share online. Social media posts, photos, and even check-ins provide a wealth of information that, when aggregated, might compromise your privacy. Regularly audit your online presence and remove outdated or unnecessary posts. By minimizing the amount of personal data available online, you reduce the risk of becoming a target for cybercriminals.
Educating Yourself and Staying Informed
Cyber hygiene is not a one-time fix but an ongoing process that requires continuous learning. The digital landscape is constantly evolving, with new threats emerging and cybersecurity measures being updated. Staying informed about the latest developments in cybersecurity is vital to maintaining your digital defenses.
Following Trusted Sources
Identify reputable sources of cybersecurity news and advice. Following industry experts, cybersecurity blogs, and official advisories from technology companies can help you stay ahead of emerging threats. Engaging in online forums and communities where cybersecurity is discussed can also provide insights and practical tips from fellow users.
Continuous Learning
Investing time in cybersecurity education is another essential habit. Many online courses, webinars, and workshops are available to help you understand the complexities of digital security. Whether you’re a novice or a seasoned tech user, continuous learning ensures that you are aware of the risks and know how to mitigate them effectively.
The Psychological Aspect of Cyber Hygiene

Good cyber hygiene is as much about mindset as it is about technology. Cultivating a cautious, informed, and proactive approach to online activities can significantly reduce your risk of exposure to cyber threats. This psychological preparedness involves being aware of potential risks and maintaining a healthy skepticism about unsolicited messages or too-good-to-be-true offers.
Building a Security Mindset
A security mindset means thinking ahead about what could go wrong and taking preventive measures before an incident occurs. It involves understanding that cyber threats are not just abstract concepts but real risks that can affect your daily life. By internalizing the importance of cyber hygiene, you are more likely to adopt habits that prioritize your digital security.
Reducing Complacency
One of the biggest challenges in maintaining good cyber hygiene is overcoming complacency. When you haven’t experienced a cyber incident, it’s easy to assume that “it won’t happen to me.” However, cyber attackers target vulnerabilities without discrimination. Regularly reminding yourself of the potential consequences of a breach can help maintain vigilance and encourage you to stick to your daily security routines.
Practical Daily Routines for Enhanced Cyber Security
Integrating cyber hygiene into your daily life does not have to be burdensome. Simple routines, when practiced consistently, build a strong foundation for digital security. Consider setting aside a few minutes each day to review your digital security practices. Whether it’s checking for software updates, reviewing your security settings, or simply scanning your emails for suspicious activity, these actions contribute to a safer online experience.
Morning Security Checks
Starting your day with a quick review of your devices can set the tone for a secure day. Check that your antivirus software is active and that any scheduled updates have been completed. Use this time to glance over any security notifications that may have appeared overnight, such as warnings from your email provider or alerts from your banking app.
Evening Routine and Reflection
Consider a brief review of your online activities. Did you click on any unfamiliar links? Were there any unexpected login attempts on your accounts? Reflecting on your daily usage can help identify areas where you might improve your security practices. This routine not only reinforces your vigilance but also helps you recognize patterns that could indicate emerging threats.
Balancing Convenience and Security
In the quest for digital security, it is common to encounter the tension between convenience and robust protection. Many security measures, such as complex passwords and multi-factor authentication, seem cumbersome in the fast-paced digital world. However, the slight inconvenience is a small price to pay for the significant protection these practices provide.
Striking the Right Balance
Finding a balance between security and usability is an ongoing challenge. It is important to evaluate the potential risks of taking shortcuts in your cyber hygiene routines. For instance, while it may be tempting to save passwords in an unsecured document or browser, the risks far outweigh the benefits. Investing in a secure password manager and taking the time to set up proper authentication processes can streamline your daily operations without sacrificing security.
Accepting Minor Inconveniences
Accepting that some security measures may slow you down is a key part of maintaining good cyber hygiene. Remember that cyber threats are constantly evolving, and what might seem like a minor inconvenience today could prevent a major security breach tomorrow. Over time, as these practices become habitual, the perceived inconvenience will diminish, replaced by the confidence that you are protecting your digital life effectively.
Looking Ahead: The Future of Cyber Hygiene
As technology continues to advance, so too will the methods and strategies of cyber attackers. The future of cyber hygiene will likely involve even more sophisticated tools and practices designed to protect our data. Innovations such as artificial intelligence and machine learning are already being integrated into cybersecurity tools, allowing for faster threat detection and more robust defenses.
Emerging Technologies and Their Impact
Artificial intelligence is playing a growing role in cybersecurity by analyzing patterns and predicting potential threats before they can cause damage. Machine learning algorithms are being developed to recognize anomalies in network traffic and user behavior, which can signal a cyber attack in its early stages. As these technologies become more widespread, staying informed about their capabilities and limitations will be essential for maintaining good cyber hygiene.
The Need for Adaptability
The dynamic nature of technology means that cyber hygiene practices must be adaptable. What works today may not be sufficient tomorrow. Continuous education, regular updates to security protocols, and an open mindset toward emerging technologies are crucial. As you plan your long-term digital security strategy, be prepared to evolve your practices alongside technological advancements.
Conclusion
Maintaining strong cyber hygiene is a daily commitment that requires attention to detail, an informed mindset, and the willingness to adapt. By establishing habits such as creating strong passwords, enabling multi-factor authentication, keeping your software updated, practicing safe browsing and email habits, securing your devices and home network, and regularly backing up your data, you build a robust defense against cyber threats.
Moreover, understanding the importance of managing your digital footprint and staying informed about the latest cybersecurity trends will empower you to navigate the digital landscape with confidence. Cyber hygiene is not merely a technical set of tasks; it is a lifestyle that reinforces the idea that every small, daily action contributes to your overall safety and the protection of your personal information.




