Organizations can no longer assume that threats only originate from outside their network. Cybercriminals, malware, and insider threats can emerge from any direction—even within what was once considered a “safe zone.” As a result, many organizations are turning to Zero Trust Architecture (ZTA), a bold and holistic security approach that is based on the principle of “never trust, always verify.” This blog explores the concept of Zero Trust Architecture in depth. It is written for anyone—from general readers and students to business leaders and IT professionals—who wants to understand how this model is shaping the future of cybersecurity.
What is Zero Trust Architecture?
Zero Trust Architecture is a cybersecurity model that assumes no actor, system, or network is trustworthy by default, regardless of whether it is inside or outside the organizational perimeter. Rather than relying on a single security checkpoint, ZTA requires continuous verification of identity, device posture, access permissions, and contextual factors before granting access to resources. The concept, coined by John Kindervag in 2010 while at Forrester Research, has gained significant momentum due to the rise of cloud services, mobile workforces, and increasingly sophisticated cyberattacks. The key takeaway is that trust is not a given and must be earned through rigorous verification.
The Flaws of Traditional Perimeter-Based Security
Traditional network security models have long relied on perimeter defences such as firewalls, VPNs, and intrusion detection systems to protect assets. Once a user or device is inside the network, it is often assumed to be trustworthy. This approach is analogous to a castle with a moat—while the outer defences may be robust, there is little protection once inside. This model is particularly vulnerable in today’s environment where remote work, BYOD (Bring Your Own Device), cloud computing, hybrid environments, advanced persistent threats, credential theft, and insider threats are on the rise.
A prime example is the infamous Target breach of 2013, where attackers gained access through a third-party HVAC vendor. Once inside the network, they moved laterally and accessed sensitive payment data, highlighting the dangers of implicit trust.
Core Principles of Zero Trust
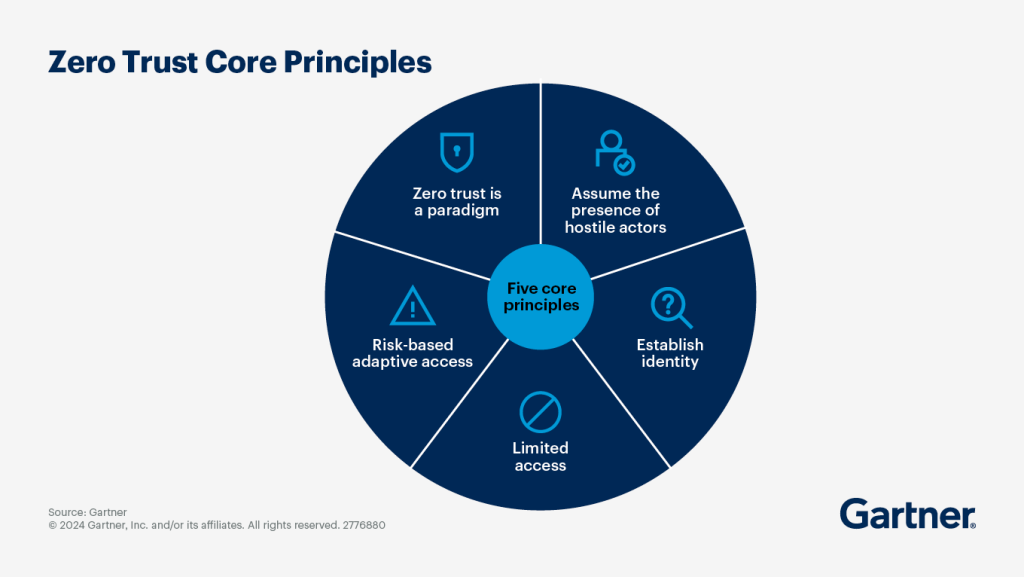
Verify Explicitly
The Zero Trust philosophy is built on the foundational principle that every user and device must be authenticated and authorized using multiple data points such as identity, location, device health, and behaviour before access is granted. This approach ensures that trust is continually reassessed rather than assumed.
Least Privilege Access
In a zero-trust model, users are granted only the minimum level of access required to perform their job functions. This principle limits potential damage in the event of compromised accounts, as only the essential permissions are provided.
Assume Breach
Zero Trust Architecture operates under the assumption that a breach is inevitable. Systems are designed with the expectation of compromise, which encourages continuous monitoring, alerting, and the implementation of micro-segmentation to limit the impact of any potential breach.
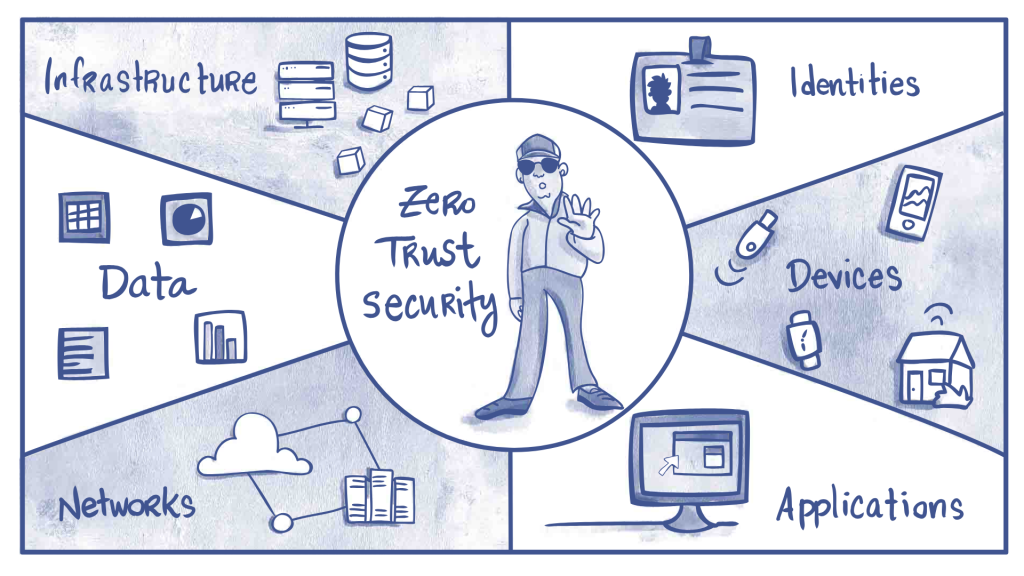
Pillars and Components of Zero Trust
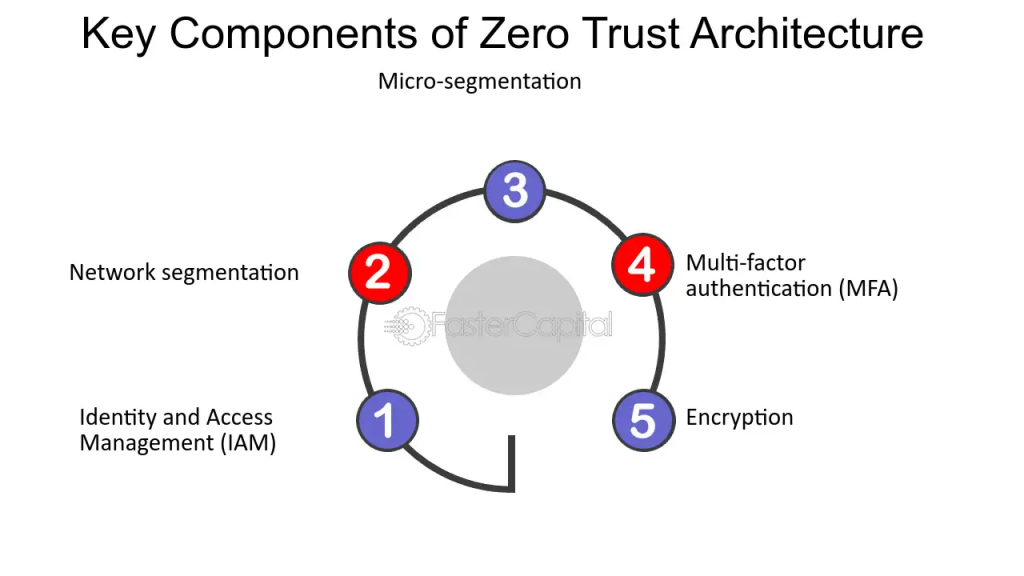
Identity and Access Management (IAM)
Effective identity and access management is crucial in a zero-trust model. Organizations implement multi-factor authentication (MFA), role-based access control (RBAC), and context-aware access policies to ensure that only verified and authorized users can access resources.
Device Security
A robust Zero Trust strategy includes rigorous device security measures. This involves conducting device posture checks, deploying endpoint detection and response (EDR) systems, and utilizing mobile device management (MDM) to ensure that all devices meet security standards before accessing the network.
Network Segmentation
Network segmentation is essential to minimize lateral movement within a network. Techniques such as micro-segmentation, software-defined perimeters (SDPs), and secure tunnelling with encrypted traffic help create isolated segments, thereby limiting the impact of a breach.
Application Security
Securing applications is another critical component of Zero Trust Architecture. Organizations adopt secure coding practices, deploy Web Application Firewalls (WAFs), and implement robust API security to protect applications from vulnerabilities and attacks.
Data Protection
In the realm of data protection, Zero Trust advocates for comprehensive measures, including data classification and tagging, encryption both at rest and in transit, and the use of Data Loss Prevention (DLP) systems. These practices ensure that sensitive information remains secure even if a breach occurs.
Visibility and Analytics
Continuous visibility and real-time analytics form the backbone of an effective zero-trust strategy. Organizations deploy systems for monitoring and logging, utilize User and Entity Behavior Analytics (UEBA), and implement Security Information and Event Management (SIEM) to detect and respond to anomalies promptly.
Real-World Applications and Case Studies
Google’s BeyondCorp
Following a significant cyberattack in 2009, Google introduced BeyondCorp—a Zero Trust model that eliminates the need for VPNs and enables secure work from any location. This initiative highlights the practical benefits of a Zero Trust approach in enhancing overall security.
U.S. Federal Government
In 2021, an executive order mandated that federal agencies adopt Zero Trust practices. Prominent agencies, including the Department of Defense and NASA, are actively integrating Zero Trust Architecture into their cybersecurity frameworks to bolster their defences against modern threats.
Capital One
After experiencing a cloud breach, Capital One adopted Zero Trust principles by implementing behaviour-based authentication and micro-segmentation to protect customer data better. This case study underscores how Zero Trust can mitigate risks even for large financial institutions.
Steps to Implement Zero Trust Architecture
Organizations looking to transition to a zero-trust model should begin with a thorough assessment of their assets, users, data flows, and existing security posture. The next step is to secure identity first by implementing strong IAM tools, enforcing MFA, utilizing just-in-time access, and auditing identity workflows. Strengthening device security is equally important; organizations must ensure that all devices are patched, monitored, and compliant before granting them network access.
Network segmentation, achieved through micro-segmentation, is crucial to isolating workloads and applications, thereby limiting lateral movement in case of a breach. Adaptive access policies should then be enforced to ensure that access is granted contextually, based on risk levels, device trustworthiness, location, and user behaviour. Continuous monitoring through SIEM, UEBA, and threat intelligence is essential to detect anomalies. Finally, educating and training employees is critical, as human error often represents the weakest link in cybersecurity.
Benefits of Zero Trust
Adopting Zero Trust Architecture enhances an organization’s security posture by reducing its attack surface and improving threat detection capabilities. It enables secure access from any location, making it an ideal solution for remote work scenarios. The approach also aligns well with compliance frameworks such as NIST 800-207, GDPR, and HIPAA, ensuring that organizations remain audit-ready. Additionally, by implementing the principle of least privilege and continuous monitoring, organizations can significantly minimize the risks associated with insider threats. Centralized logging and analytics further contribute to improved visibility, enabling organizations to respond to incidents more effectively.
Common Challenges and How to Overcome Them
Implementing a Zero Trust model is not without its challenges. Legacy infrastructure may lack the integration capabilities required for Zero Trust, so organizations should consider phased upgrades or segmentation strategies to bridge the gap. The complexity and cost associated with deploying multiple tools and configurations can be daunting, but using managed services or Zero Trust Network Access (ZTNA) solutions can help mitigate these issues.
User friction is another common challenge, as multi-factor authentication and new access policies can sometimes frustrate users. Balancing security with a seamless user experience through adaptive authentication is key. Moreover, overcoming cultural resistance requires clear communication of the benefits of Zero Trust and early stakeholder engagement to secure buy-in.
Future Trends in Zero Trust
The future of Zero Trust is set to be shaped by several emerging trends. Integration of artificial intelligence and machine learning will enhance threat detection and policy enforcement, making security systems even more responsive. Zero Trust principles will also extend to the Internet of Things (IoT) and Operational Technology (OT) devices, necessitating robust identity and access controls in industrial and smart device environments. Additionally, the convergence of Zero Trust with Secure Access Service Edge (SASE) solutions promises to create scalable and agile security infrastructures. Finally, automation and orchestration will streamline policy enforcement and incident response, reducing the need for manual intervention and accelerating reaction times.
Final Thoughts
Zero Trust Architecture is not a one-size-fits-all solution but rather a comprehensive approach to building resilient, adaptive, and secure digital environments. In an age where cyberattacks are no longer a question of “if” but “when,” Zero Trust provides a practical framework to minimize risk and ensure business continuity. The future of enterprise security lies in questioning every access attempt, segmenting systems, protecting data at all levels, and continuously monitoring for threats. Although adopting Zero Trust is a journey that requires commitment and strategic planning, it is undoubtedly a journey worth taking.




