Featured Blogs
Recent Blogs
Apple CVE-2025-43300 zero-day patch Imagine waking up and checking your iPhone only to find a...
Apache Tika PDF parser XXE exploit mitigation Imagine this: you have a cup of coffee while Apache...
Contemporary enterprises are powered by web apps such as e-commerce management tools to medical...
GPT-5 Access Plan Think about this. You have a half-empty cup of coffee and a lot of unopened emails...
Wake up, make some coffee, and look at the cameras in your house. The screen won’t work. You...
Cyber threats are growing every day. Hackers no longer only target big companies, they go after any...
Cyber threats are becoming more intelligent, quicker, and difficult to detect today. Hackers do not...
Novel 5G attack bypassing base station The Day I Found Out My Phone Wasn’t Alone ,I remember...
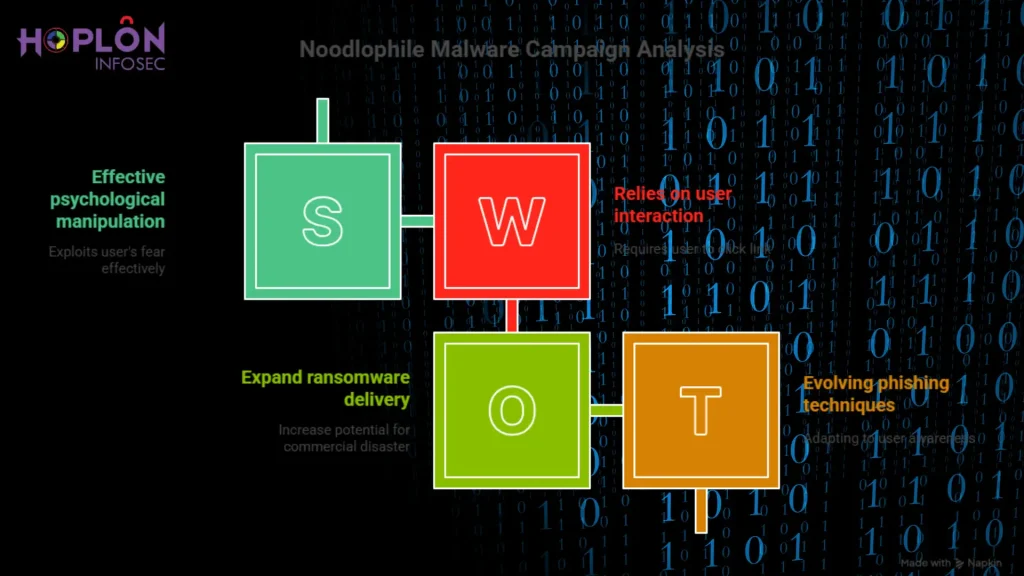
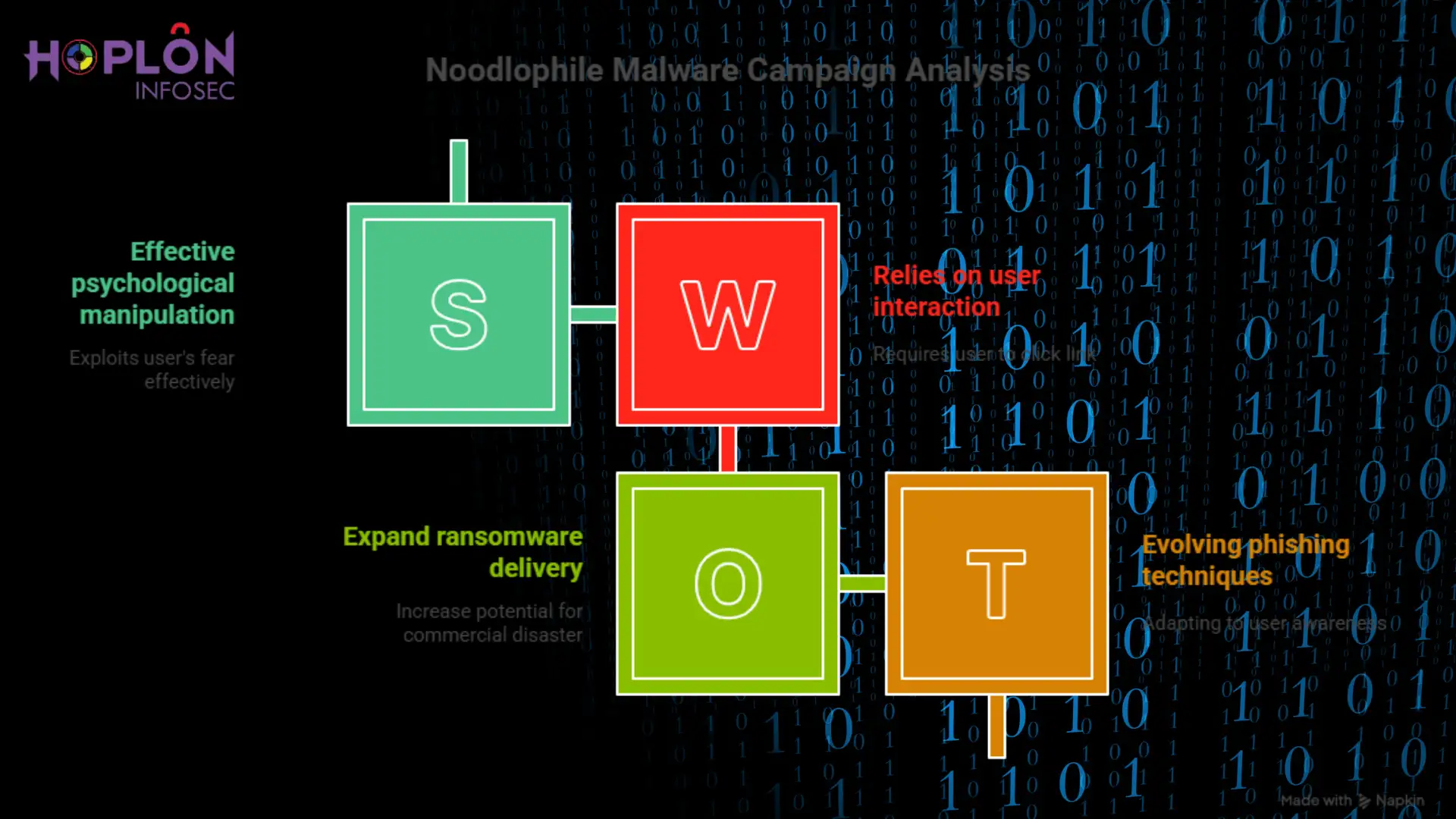
The Noodlophile Malware Campaign’s Growing Shadow On a quiet Tuesday afternoon, an IT manager...
Recent Blogs
We’re Here to Secure Your Hard Work
Protect your system from cyber attacks by utilizing our comprehensive range of services. Safeguard your data and network infrastructure with our advanced security measures, tailored to meet your specific needs. With our expertise and cutting-edge technology, you can rest assured.