Featured Blogs
Recent Blogs
Do you heard about the recent Volkswagen Data Breach Exposes 800,000 Electric Car Owners Data? In a...
In an era where digital security has become paramount, a significant cybercrime case involving a...
A new critical Apache MINA Vulnerability, CVE-2024-52046, has been discovered in Apache MINA, a...
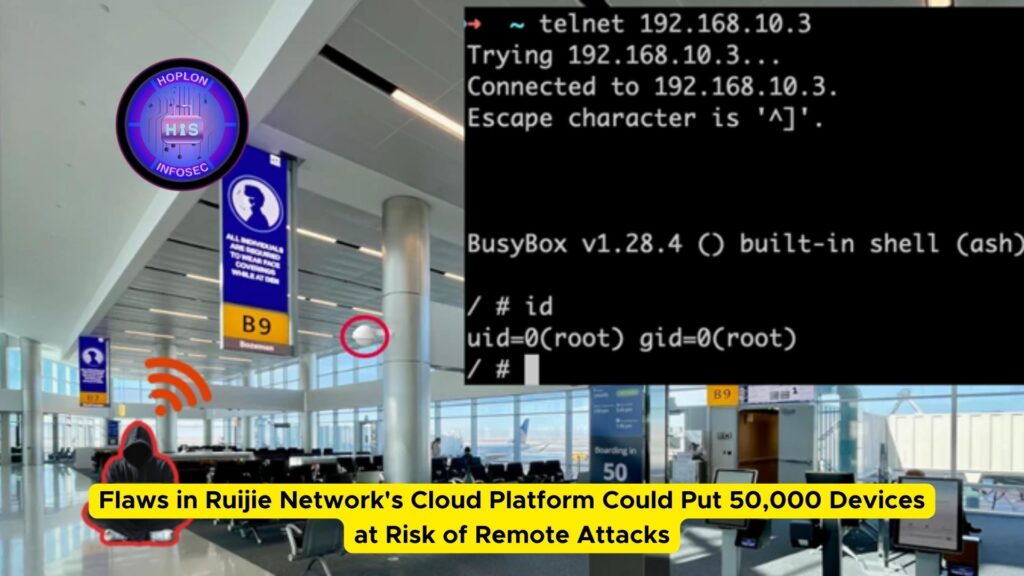
In a recent revelation, cybersecurity researchers have uncovered significant vulnerabilities in the...
Are you aware of Postman Data Leak? In recent years, the widespread adoption of Application...
Recent disclosures have unveiled two significant vulnerabilities affecting widely used software...
It’s that time of the year again when we reflect on the past 12 months in cybersecurity and...
In today’s digital age, organizations rely heavily on cloud-based productivity suites like Microsoft...
Are you aware of IBM Cognos Vulnerability? In today’s digital landscape, security remains a...
Recent Blogs
We’re Here to Secure Your Hard Work
Protect your system from cyber attacks by utilizing our comprehensive range of services. Safeguard your data and network infrastructure with our advanced security measures, tailored to meet your specific needs. With our expertise and cutting-edge technology, you can rest assured.