Overcoming Android Spyware That Demands a Password for Uninstallation

Hoplon InfoSec
04 Apr, 2025
A new type of Android spyware has emerged that is particularly troublesome for users. This malicious application not only invades privacy by monitoring sensitive information but also employs a cunning method to prevent its removal. By requiring a password during the uninstallation process, this Android Spyware poses a serious threat to victims’ control over their own devices. In this blog, we delve into how the spyware operates, the implications for security, methods for bypassing its protection, and recommendations for preventive measures.
Overview of the Android Spyware Threat
Android devices have become essential tools in daily life, storing everything from personal communications to sensitive financial data. Unfortunately, these devices are also prime targets for cybercriminals. The spyware in question exploits the Android operating system’s features to hide itself and resist removal. Once installed, the malicious app embeds itself so deeply into the system that even the standard removal procedures through device settings become ineffective without the proper password.
This spyware leverages Android’s “overlay” feature—a functionality designed to enhance user experience by allowing apps to display content on top of other applications. However, in the hands of malicious developers, this feature is repurposed to create an unyielding password prompt that appears whenever a user attempts to uninstall or disable the application. The implications are significant: without the correct password, victims are unable to remove the spyware, leaving their devices continuously exposed to surveillance.
How the Android SpywareOperates
Installation and Activation
The spyware is typically installed by an individual with physical access to the target device. This could occur in situations ranging from a domestic dispute to corporate espionage. Once on the device, the app covertly requests and is granted device administrator privileges—a critical step that allows the application to override standard security measures and perform actions that are normally restricted.
After activation, the Android Spyware cleverly removes its icon from the home screen, thereby reducing the likelihood of accidental discovery by the user. This invisibility is a hallmark of sophisticated mobile malware, as it minimizes the chance of the app being noticed during routine checks.
Exploiting the Overlay Feature
The key mechanism behind this Android Spyware’s resilience is the exploitation of the overlay feature. Android’s overlay functionality permits an app to display its interface over other apps. The malicious software uses this to its advantage by constantly monitoring for any attempt to access the uninstallation option. Once it detects such an attempt, it immediately triggers a password prompt on top of the screen.
This overlay prevents the user from interacting with the underlying settings. Since the prompt is enforced by the spyware, it effectively locks out the user from accessing the uninstallation options. In doing so, the application guarantees its persistence on the device. The password required for removal is set by the installer of the spyware, not the victim, making it nearly impossible to remove without specific knowledge.
Continuous Surveillance
Once installed, the Android Spyware continues to operate in the background. It monitors various aspects of the victim’s device, including messages, photos, location data, and other sensitive information. This constant surveillance creates a comprehensive digital profile of the user. For cybercriminals, the potential for espionage—whether for personal, financial, or political gain—is immense. In many cases, the spyware is marketed under the guise of legitimate parental control or employee monitoring software, further complicating its identification and removal.
Security Risks and Implications
The presence of such spyware on Android devices raises several significant concerns. First, it highlights vulnerabilities in the operating system that allow legitimate features to be repurposed for malicious intents. Second, the installation and persistence of the spyware reveal the potential consequences of physical access to a device, even if it is temporarily unattended.
Privacy Invasion and Data Breach
The Android Spyware is capable of collecting vast amounts of personal data, which can lead to severe privacy invasions. From private messages to geolocation data, the information gathered can be used to track the victim’s movements, monitor their behavior, and even compromise their personal safety. This kind of surveillance can be particularly harmful in scenarios involving domestic abuse or corporate spying.
Trust Erosion in Android’s Security
Android, being an open-source platform, is prized for its flexibility and customizability. However, the open nature of the operating system also makes it a target for exploitation. The emergence of spyware that can lock itself in place not only undermines user trust but also exposes systemic weaknesses that may be exploited by other forms of malware in the future. As these threats evolve, users and developers alike must remain vigilant in addressing and mitigating potential vulnerabilities.
Methods to Bypass the Android Spyware
Fortunately, security researchers have identified a viable method for removing this stubborn spyware from infected devices. By booting the device into “safe mode,” users can disable third-party applications, including the malicious Android Spyware that employs the password prompt.
Safe Mode: A Strategic Advantage
Safe mode is a diagnostic tool built into Android devices that allows the system to operate with only the essential, pre-installed applications running. This environment prevents third-party apps from launching automatically. In safe mode, the Android Spyware’s ability to trigger the overlay password prompt is neutralized because it does not load into memory along with the other apps.
Step-by-Step Removal Process
The process to remove the spyware in safe mode is straightforward yet requires precision:
- Booting into Safe Mode:
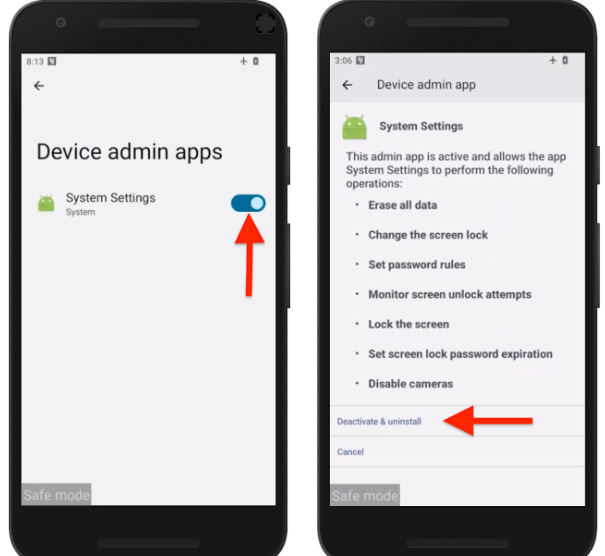
To initiate safe mode, the user must press and hold the power button. Once the power options appear, a long press on the “Power off” option will prompt the device to restart in safe mode. The screen will display a “Safe Mode” label, indicating that only system apps are active. - Navigating to Security Settings:
While in safe mode, the user should navigate to the device’s Settings. Here, they must locate the section labeled “Security” or “Device administration.” In this section, a list of apps with administrative privileges will be displayed. - Revoking Administrator Privileges:
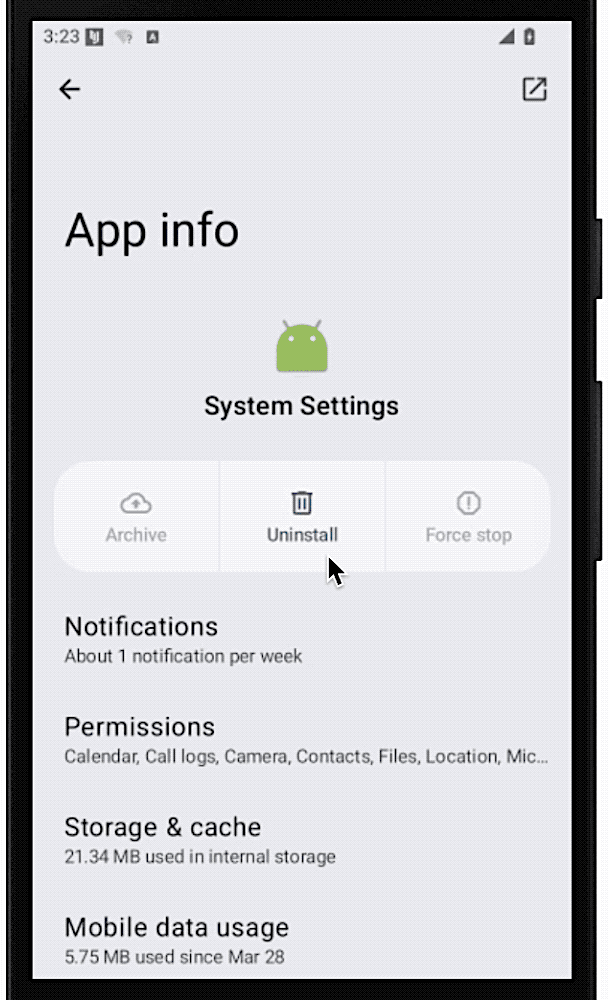
The next step involves identifying the suspicious application from the list of device administrator apps. Once found, the user can deactivate its administrative privileges. This action is crucial as it removes the app’s ability to enforce its password protection and other elevated functions. - Uninstalling the Application:
With the administrative privileges revoked, the user can now proceed to the application management section in the settings. The Android Spyware should now be listed among the installed applications. Selecting the app and choosing the uninstall option will remove it from the device.
These steps provide an effective workaround to bypass the spyware’s protective mechanisms, thereby restoring control to the device owner.
Preventive Measures and Recommendations
Given the potential risks associated with such spyware, it is imperative for Android users to take preventive measures. Security experts recommend a series of steps to safeguard devices from similar threats.
Keeping Google Play Protect Enabled
Google Play Protect is a built-in security feature designed to scan and monitor applications for suspicious behavior. Users should ensure that this feature is activated at all times. Regular scans help in identifying potentially harmful apps before they can cause significant damage.
Vigilance with Device Administrator Apps
Regularly reviewing the list of apps with device administrator privileges is a proactive measure. This allows users to quickly spot any unfamiliar or suspicious applications. If an unknown app is found, especially one that the user did not install intentionally, its privileges should be revoked immediately.
Cautious Physical Access
Many Android Spyware installations require physical access to the device. Users should take steps to secure their devices, such as using strong lock-screen passwords and ensuring that their phones are never left unattended in public places. For those in sensitive environments, additional security measures such as biometric locks can further reduce the risk.
Utilizing Reputable Antivirus Software
The use of reliable antivirus and anti-spyware applications can provide an extra layer of security. Programs like Malwarebytes and Norton are frequently recommended by experts. These tools are capable of scanning for known threats, including stalkerware, and alerting users to potential infections. Regular updates to these antivirus programs ensure that they can detect the latest forms of malware.
Awareness of Unusual Device Behavior
Users should be alert to any signs that their device may be compromised. Indicators such as the phone running warmer than usual, experiencing a noticeable slowdown, or exhibiting unexplained increases in data usage may be signals of an ongoing infection. Early detection of such symptoms is crucial for prompt removal of the Android Spyware before it can extract more data.
Expert Perspectives on the Evolving Threat Landscape
Insights from Mobile Security Experts
Security experts have voiced growing concerns about the increasing sophistication of Android Spyware targeting mobile devices. One mobile security expert from McAfee emphasized that the ability of these apps to hide their presence while continuously monitoring user activities represents a significant leap in surveillance technology. The expert noted that while consumer-grade spyware is often marketed as a tool for parental control or employee monitoring, its potential for abuse is vast.
Analysis from Tech Publications
Tech publications such as TechCrunch have highlighted the dangers of exploiting legitimate system features for malicious purposes. The use of the overlay feature to enforce password protection is a prime example of how benign functionalities can be twisted to serve nefarious ends. These reports serve as a wake-up call for both users and developers, underscoring the need for enhanced security protocols and continuous monitoring of system vulnerabilities.
The Broader Impact on Privacy and Corporate Security
Privacy Invasion in Personal Life
The invasive nature of this Android Spyware is particularly alarming when considering its implications for personal privacy. With access to private messages, photographs, and even location data, the spyware can create a detailed digital profile of the victim. This profile may be exploited for various malicious purposes, including identity theft, blackmail, or targeted harassment. The psychological impact of knowing that one’s private life is being monitored without consent cannot be overstated.
Corporate Espionage and Employee Monitoring
In a corporate context, similar Android Spyware can be used to monitor employees under the guise of productivity or security. While some companies justify the use of monitoring software for ensuring the integrity of corporate data, the misuse of such tools can lead to significant breaches of privacy and trust. Employees may find themselves under constant surveillance, leading to a workplace environment where personal freedoms are severely restricted. The ethical implications of such practices have sparked debates about the balance between security and privacy in the modern workplace.
Future Concerns and Evolving Trends
Continuous Innovation by Cybercriminals
The development of Android Spyware that requires a password for uninstallation is just one example of the continuous innovation in the cybercriminal landscape. As security measures evolve, so too do the methods employed by attackers. Cybercriminals are constantly exploring new techniques to bypass existing safeguards and maintain persistent access to target devices. This cat-and-mouse game between developers of malicious software and security professionals means that users must remain vigilant and proactive in protecting their devices.
Potential Regulatory and Legal Implications
The increasing prevalence of such Android Spyware raises important questions about regulation and legal oversight. In many regions, the unauthorized installation and use of surveillance software can have severe legal repercussions. However, enforcement can be challenging, particularly when the spyware is disguised as legitimate monitoring software. Future regulatory measures may need to focus on stricter controls over the distribution and use of such applications, as well as more robust penalties for those found guilty of installing spyware without consent.
Conclusion
The emergence of Android spyware that employs a password to prevent its removal is a stark reminder of the evolving challenges in mobile security. This malicious software not only invades personal privacy but also leverages legitimate system features in harmful ways. By exploiting the overlay functionality, the Android Spyware can effectively block users from regaining control over their devices, leaving them vulnerable to continuous surveillance.
Understanding how this Android Spyware operates is the first step in mitigating its impact. By recognizing the importance of safe mode as a method to bypass the password protection, users can take proactive steps to remove the malware from their devices. Additionally, maintaining robust security measures—such as keeping Google Play Protect enabled, regularly reviewing device administrator privileges, and using reputable antivirus software—can significantly reduce the risk of infection.
Looking forward, it is essential for both individuals and organizations to stay informed about emerging threats. Cybersecurity is a rapidly evolving field, and the techniques used by malicious actors are constantly advancing. Through increased awareness, vigilance, and the implementation of effective security protocols, users can safeguard their devices and personal data against these invasive threats.
Source: Cybersecurity News, Kaspersky
Was this article helpful?
React to this post and see the live totals.
Share this :