Cyber Attack Alert: New IoT Botnet Hijacking TP-Link Archer Routers

Hoplon InfoSec
14 Mar, 2025
A newly discovered IoT botnet targets TP-Link Archer routers, posing a significant security risk to thousands of users worldwide. This botnet exploits vulnerabilities in these routers to take control of them, adding them to a network of infected devices that can be used for cyberattacks such as Distributed Denial of Service (DDoS) attacks, data theft, and unauthorized access to private networks.
As IoT devices become increasingly integrated into homes and businesses, ensuring the security of routers and network infrastructure is more critical than ever. This blog explores how the botnet operates, the vulnerabilities it exploits, its potential impact, and what users can do to protect themselves.
Understanding IoT Botnets and Their Threats
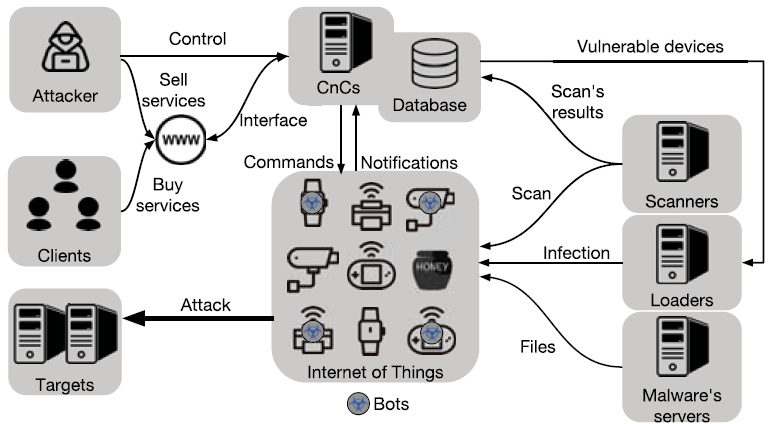
IoT botnets are networks of compromised internet-connected devices that hackers remotely control to carry out cyberattacks. These botnets have been responsible for some of the most devastating cyber incidents in history, including the infamous Mirai botnet, which exploited weak passwords in IoT devices and launched massive DDoS attacks, and the Mozi botnet, which targeted IoT devices to execute malware payloads.
The botnet affecting TP-Link Archer routers follows a similar pattern but appears more sophisticated. It takes advantage of security loopholes in these routers to gain control, turning them into part of a massive cybercriminal infrastructure.
How the New IoT Botnet Targets TP-Link Archer Routers
Attack Methodology: Exploiting TP-Link Vulnerabilities
The botnet’s success relies on exploiting security weaknesses in TP-Link Archer routers. Researchers have identified multiple vulnerabilities that attackers use to compromise these devices. Among the most concerning are remote code execution (RCE) vulnerabilities, which allow attackers to execute commands remotely, and authentication bypass flaws, which let hackers access the router’s settings without needing login credentials.
Another significant issue is the misconfigured Universal Plug and Play (UPnP) setting, which exposes routers to attacks by allowing external devices to communicate directly. Many users also fail to change default credentials, making it easier for attackers to gain access using automated brute-force techniques.
Stages of Infection
The botnet infection process begins with attackers scanning the internet for vulnerable TP-Link Archer routers. Once a weak router is identified, the hacker exploits its vulnerabilities to gain control. Malicious code is then deployed to establish persistence on the device by modifying system settings and disabling security features. Once the router is fully compromised, it becomes part of the botnet, allowing attackers to use it for large-scale cyberattacks.
Impact of the TP-Link Router Botnet
The consequences of this botnet are far-reaching. Compromised routers can be used to launch DDoS attacks against websites, crippling online services and causing financial losses. Home and business networks connected to infected routers are at risk of data theft, where attackers intercept sensitive information such as banking details and login credentials.
Privacy is another primary concern. Cybercriminals controlling these routers can monitor internet traffic, potentially gaining access to confidential communications. In addition, infected devices can be weaponized for cryptocurrency mining, consuming bandwidth and electricity without the user’s knowledge.
The most alarming impact is the use of these botnets in cyber warfare and espionage. Large-scale botnets can target financial institutions, government websites, and infrastructure services, leading to widespread disruptions.
How to Protect Your TP-Link Archer Router from the Botnet

To defend against this botnet, users must immediately secure their routers. The most effective way to prevent infection is to update the router’s firmware regularly. TP-Link releases security patches to fix vulnerabilities, but users often neglect these updates, exposing their devices.
Changing default passwords is another critical step. Factory-set credentials are easy targets for attackers, so setting up a strong, unique password for the router’s admin panel reduces the risk of unauthorized access.
Turning off remote management is also advisable. Many users enable remote administration features for convenience, but this opens the router to external threats. This feature should be turned off unless necessary to prevent attackers from exploiting it.
Configuring the firewall and security settings on the router adds an extra layer of protection. Disabling UPnP and using strong Wi-Fi encryption (WPA3 or WPA2) ensures that unauthorized devices cannot easily access the network.
Monitoring network activity regularly can help detect unusual behavior. If unknown devices appear in the router’s admin panel or network traffic spikes unexpectedly, it could indicate a security breach. In cases where a router is suspected to be compromised, performing a factory reset and reinstalling the latest firmware is the best course of action.
Using a VPN (Virtual Private Network) can further enhance security by encrypting internet traffic, making it difficult for attackers to intercept sensitive data. Additionally, installing endpoint security software on connected devices can help detect and block threats before they cause significant damage.
Conclusion
The emergence of an IoT botnet targeting TP-Link Archer routers underscores the growing threats posed by cybercriminals exploiting unsecured network infrastructure. As botnets become more sophisticated, users must stay informed and take proactive steps to protect their devices.
By keeping firmware up to date, securing routers with strong passwords, disabling unnecessary remote access features, and monitoring network activity, users can significantly reduce their risk of being victims of these attacks.
Cybersecurity is an ongoing battle, and staying vigilant is the best defense against threats like this. If you own a TP-Link Archer router, now is the time to act—secure your device and prevent it from becoming part of a cybercriminal’s botnet army.
Was this article helpful?
React to this post and see the live totals.
Share this :