Featured Blogs
Recent Blogs
A Quiet War in the ShadowsSuppose that, a group of hackers, backed by a powerful nation, silently...
Are you aware of Adidas Data Breach? On May 23, 2025, Adidas, the iconic German sportswear brand...
Imagine you’re sitting in your home office, sipping tea, when you get a simple email from what looks...
In the ever-evolving landscape of cybersecurity threats, a new player has emerged, leveraging modern...
Imagine you are waking one morning and heading to your favorite coffee shop, only to find out you...
In an era dominated by online shopping and digital interactions, cybersecurity is more critical than...
“Imagine waking up one morning to find the most sensitive data from nine federal ministries and even...
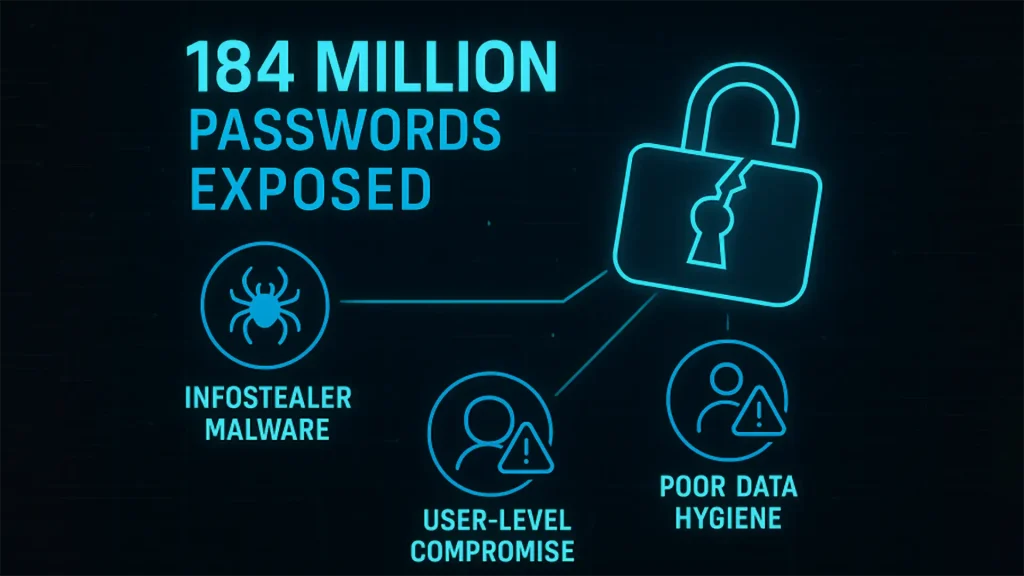
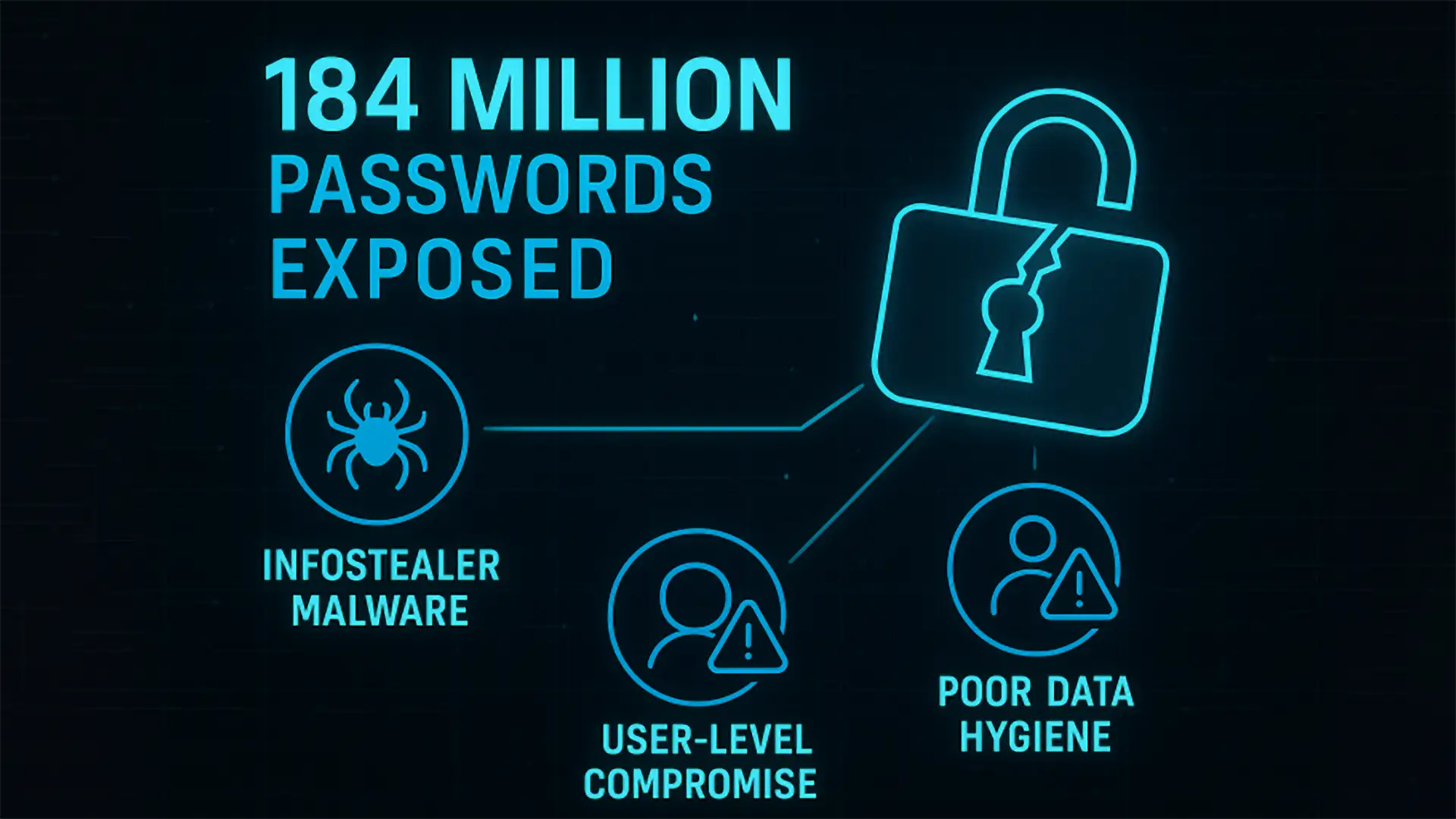
In May 2025, cybersecurity researcher Jeremiah Fowler uncovered a significant breach: an unprotected...
Imagine you roll onto your jobsite at sunrise, coffee in hand, only to find crews scrambling to...
Recent Blogs
We’re Here to Secure Your Hard Work
Protect your system from cyber attacks by utilizing our comprehensive range of services. Safeguard your data and network infrastructure with our advanced security measures, tailored to meet your specific needs. With our expertise and cutting-edge technology, you can rest assured.