AI-Assisted FortiGate Device Compromise: 600+ Hit

Hoplon InfoSec
22 Feb, 2026
What exactly is the recent large-scale AI-assisted cyberattack on FortiGate devices, and how far does it affect things?
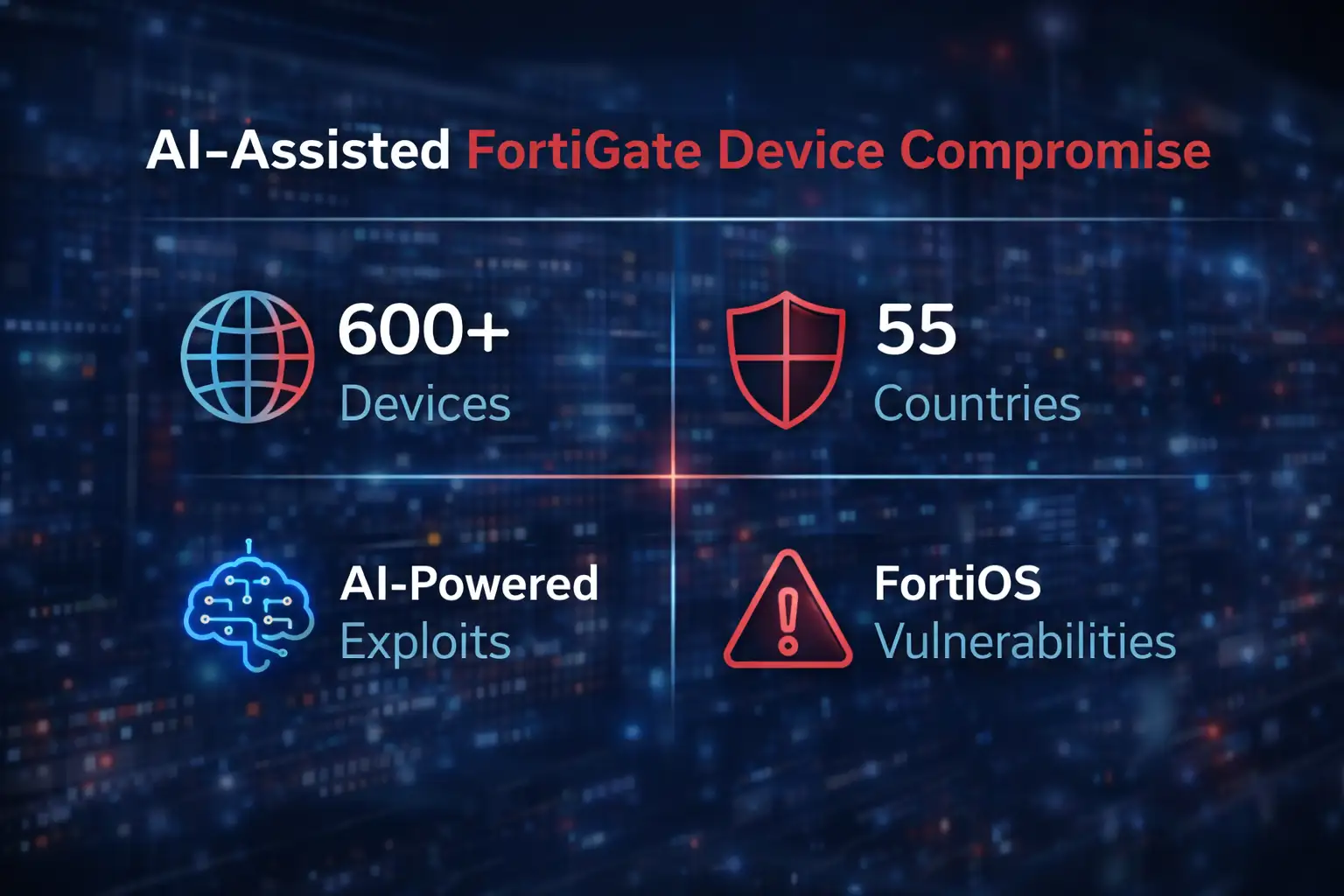
This is a very advanced cyber campaign in which hackers used AI tools to break into at least 600 FortiGate firewall devices in 55 countries. In the middle to late 2024, this operation got a lot of attention. This is a great example of an AI-assisted FortiGate device compromise, according to security researchers.
In this case, machine learning made traditional hacking methods much more powerful, allowing them to scan, find, and take advantage of weaknesses on a scale never seen before.
Picture this: you put a very expensive, high-quality deadbolt on your front door. You sleep well, believing you are safe. But then a burglar comes along with a "magic" device that can quickly look at the pins inside your lock and make a master key in 3D right there.
That's what is going on in the digital world right now. We think FortiGate firewalls are the best way to protect our networks, but hackers are now getting around them with the help of artificial intelligence.

What Really Happened: The Gritty Details
Cybersecurity experts were shocked when they first heard about this huge breach. It wasn't just the number of victims; it was also how well the attack worked. The hackers didn't just pick one country or company to pick on. Instead, they set up a global dragnet to find flaws in FortiGate devices.
Using AI, they could scan tens of thousands of devices in the same amount of time that it used to take a person to scan a dozen. This AI-assisted FortiGate device compromise let them attack more than 600 high-value targets, including both government agencies and private businesses.
The attackers mostly took advantage of known weaknesses in FortiOS, the operating system that runs these firewalls. You might be wondering, "Aren't there fixes for old bugs?" Yes, that's right. But these AI tools are made to find "low-hanging fruit." These are devices that belong to groups that, for some reason, haven't updated their systems.
Once inside, the hackers have full control over the system, which makes it easy to steal data or install ransomware. This isn't just a hit-and-run; it's a silent occupation where the attackers can stay in a network for months without being seen.
Why is AI the hacker's best friend?
It's pretty clear why the bad guys have turned to AI. In the past, a hacker had to check IP addresses by hand to see if a door was open. It was boring, took a long time, and made it more likely that a watchful sysadmin would catch you. AI bots and scripts can do things a thousand times faster than people can do them.
They can find a weakness on their own and then quickly create a "payload," which is the exact piece of bad code needed to get in. The main reason the AI-Assisted FortiGate Device Compromise spread so quickly is because of this speed.
There are FortiGate devices all over the place. You can find them in the server rooms of almost every business, from small startups to Fortune 500 companies. Hackers know that if they can get into the gateway, they can get into everything behind it.
FortiGate has had security problems in the past, but this campaign is different because the attackers are using technology to make their operations "scalable." They've figured out that mixing human creativity with machine speed gives them a success rate that was only a dream ten years ago.
How the Attack Works Behind the Scenes
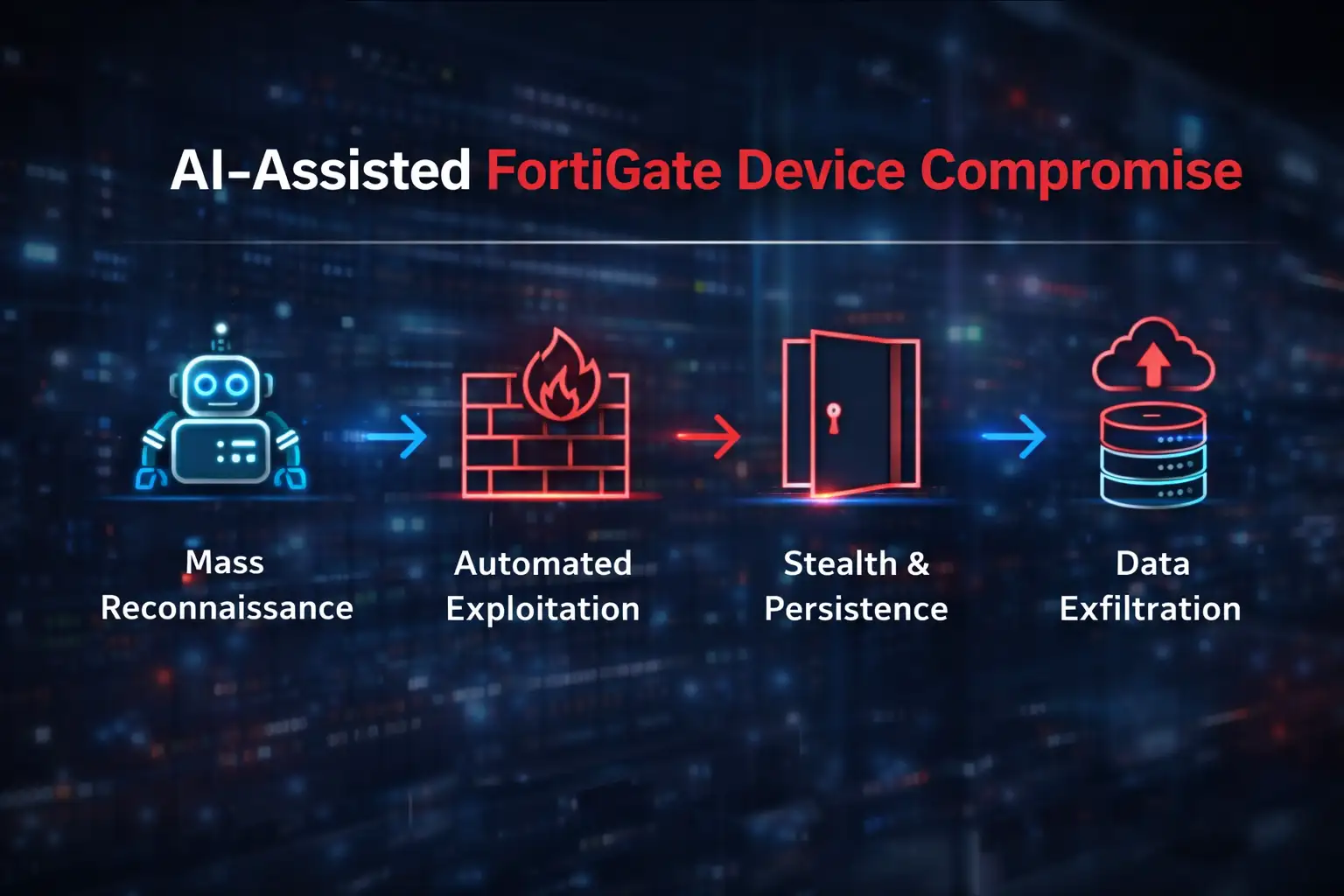
If we look closely, this process makes a lot of sense. It goes through a number of different stages:
Mass Reconnaissance: AI-powered botnets crawl the public internet and find every FortiGate device that is visible. These bots are set up to find the exact "digital fingerprint" of FortiOS versions that are weak.
Automated Exploitation: The AI picks the right exploit code once a target is marked. This often looks for weaknesses like CVE-2023-27997 or other heap-based buffer overflows.
Stealth and Persistence: Once inside, the attackers set up "backdoors." This means that even if you change your admin password, they can still get in through a secret door they made.
Exfiltration: The last step is to send sensitive data to the hackers' servers while also deleting system logs so that no one can see that they were there.
This AI-assisted FortiGate device compromise may sound like something out of a movie, but the code behind it is very real and very dangerous. Hackers aren't just "guessing" anymore; they are using data science to make sure their attacks hit their targets with deadly accuracy.
A Real-World Example
Before and After Let's say there is a company called "Global Logistics Inc." "They used a FortiGate firewall to keep track of all their client data and shipping manifests. The IT manager was busy and thought, "The firewall is working fine; I'll update the firmware next month." That was the mistake that cost him his life. An AI script found their old firewall at 3:00 AM on a Tuesday.
Before the Attack: The network was calm. The firewall was keeping out normal "dumb" bot attacks, and employee data was safe.
After the Attack: The AI had mapped the whole internal network within two hours of the first breach. At 9:00 AM, when the IT team sat down for coffee, 600 GB of sensitive manifests had already been uploaded to a server in a country that doesn't extradite people. A note asking for money showed up on every screen.
This wasn't a manual hack; it was a disaster that happened on its own. The business lost millions of dollars in sales and, more importantly, the trust of its partners around the world.
Who Is Being Hit?
The list of victims is long and includes a lot of different people. The attackers don't care who they get; they just want someone with a weak perimeter.
Government Agencies: A lot of departments still use "legacy" hardware that doesn't get updated as often as it should. These are great places for the government to steal data.
Mid-to-large businesses: Any company with a huge customer database is a gold mine. This is the majority of the more than 600 organizations that were affected in 55 countries.
Managed Service Providers (MSPs): This is the most frightening part. If a hacker gets into an MSP's network through a FortiGate device, they might be able to get into the networks of all the MSP's clients.
Critical Infrastructure: Energy and water utility companies often use these devices to connect their office networks to their operational technology.

A Balanced View of the Pros and Cons
We have to be fair here. AI is a great tool for hackers, but it's not a god.
Hackers get a lot of work done quickly, which is a big plus for them. With a small staff, they can handle hundreds of attacks at the same time. The "benefit" is a huge wake-up call for the industry. Fortinet and other vendors are having to adapt and add stronger, AI-resistant security features because of this.
But the "limitation" is that AI is still mostly predictable. It follows a pattern. The AI scripts often get confused when a network administrator uses settings that aren't standard or puts out "honey pots" (fake servers meant to catch hackers). When things don't go according to plan, AI doesn't have the "gut feeling" or creative problem-solving skills of a human hacker.
What You Need to Do Now
I know this is a lot to take in, but don't worry. When you panic, you make mistakes. If you are in charge of a network, here is your plan of attack:
Check Your Firmware: Right away, check the version of FortiOS you have. If you're behind on patches, stop everything and update right away. This is the best way to stop the AI-assisted FortiGate device compromise.
Turn on Multi-Factor Authentication (MFA): Even if an AI gets your password, it can't easily copy your physical MFA token or biometric scan.
Geo-Blocking: If your business doesn't do business in some parts of the world, block all traffic from those areas at the firewall level.
Offline Backups: Store your most important data on a drive that isn't connected to the internet. You should have a lifeboat ready in case the ship goes down.
People Also Ask
1. How can I tell if someone has hacked my FortiGate device?
Check for strange spikes in outgoing traffic, the creation of unauthorized admin accounts, or the sudden deletion of system logs. Another big red flag is if your firewall keeps restarting on its own.
2. Is this a problem only for people who use FortiGate?
No. This campaign was aimed at Fortinet, but other AI tools are being made to attack devices from Cisco, Palo Alto, and Check Point. No brand is safe.
3. Can antivirus software stop an attack that uses AI?
Standard antivirus usually protects your laptop, but it won't stop a breach at the firewall level. For that, you need Network Detection and Response (NDR) tools.
4. What makes 55 countries such an important number?
This shows that the attack was done by a computer and didn't care where it happened. The AI didn't care about borders; it only cared about finding the weak spot.
The Digital Arms Race in the Future
The compromise of more than 600 FortiGate devices is a turning point. It means that we are now officially in the age of AI vs. AI war. It's not just about who has the better firewall anymore; it's also about who has the smarter algorithms. The hackers have made their move, and they've done it with the help of machines.
To stay safe in the future, you need to move at the same speed as the threat. We can't fight AI in the 21st century with the same maintenance habits we used in the 20th century. Stay alert, keep your systems up to date, and never think, "It won't happen to us."
We suggest using a "Zero Trust" architecture in the Hoplon Insight Box. Even if a device or user is on your network, you shouldn't trust them by default. If you use FortiGate, we recommend turning off the "SSL-VPN" feature unless you really need it. This is because it has been a major way for these exploits to get in in the past.
This analysis is based on recent threat intelligence reports from FortiGuard Labs' official security advisories.
Are you ready to protect your perimeter? Don't wait for the AI to find you first if you're not sure about how things are set up right now. Call Hoplon Infosec today for a full network audit, and we'll help you build a defense that is smarter than the threat. Let's work together to keep the bad guys out.
Author's Note: I write about cybersecurity and think that the best way to protect yourself is to know what you're doing. I've seen these attacks happen in real time, and I want to make sure you're not the next news story.
For more latest updates like this, visit our homepage.
Was this article helpful?
React to this post and see the live totals.
Share this :