Cisco SD-WAN Zero-Day Exploit: Critical Patch Guide
Hoplon InfoSec
26 Feb, 2026
Imagine waking up to find that a stranger has been living in your house for years, quietly changing the address of your mail and watching everything you do. The Cisco SD-WAN zero-day exploit is a nightmare for thousands of businesses right now. A serious flaw, known as CVE-2026-20127, lets attackers get past authentication and dig deep into SD-WAN controllers.
This isn't a threat that will happen in the future. It has been active since at least 2023, and it has hit businesses that use Cisco's networking equipment to connect data centers, branches, and clouds. You should care because if you're using Cisco Catalyst SD-WAN, your network may already be at risk, putting sensitive data and operations in the hands of bad actors and giving them root-level access. It's time to move quickly.
Cisco SD-WAN makes it possible to connect securely and quickly across distributed setups. But this zero-day exploit changes the game. Attackers make sneaky requests to get around peering checks and log in as users with high privileges. Then, they use NETCONF to change the settings and add fake devices that look real.
According to CISA, federal agencies have a patch deadline coming up soon, but private companies can't wait. Why now? Five Eyes allies just sent out warnings, telling people to harden up right away.
What is the Cisco SD-WAN Zero-Day Exploit?
SD-WAN is like a smart traffic cop for all of your company's offices that are far apart. It sends data over the internet safely and at a lower cost than old MPLS lines. But the main problem is that CVE-2026-20127 is in the peering authentication system. That part checks to see if a new device that joins the network is a friend or an enemy. It doesn't work at all.
An attacker sends the controller requests that are made just for them. Boom. They sign in as a powerful internal account that isn't the root account. No need for a password. This lets you use NETCONF, the tool that controls the entire SD-WAN fabric. It's like giving someone the keys to your whole highway system. They can lie about routes, get traffic to go their way, or do worse.
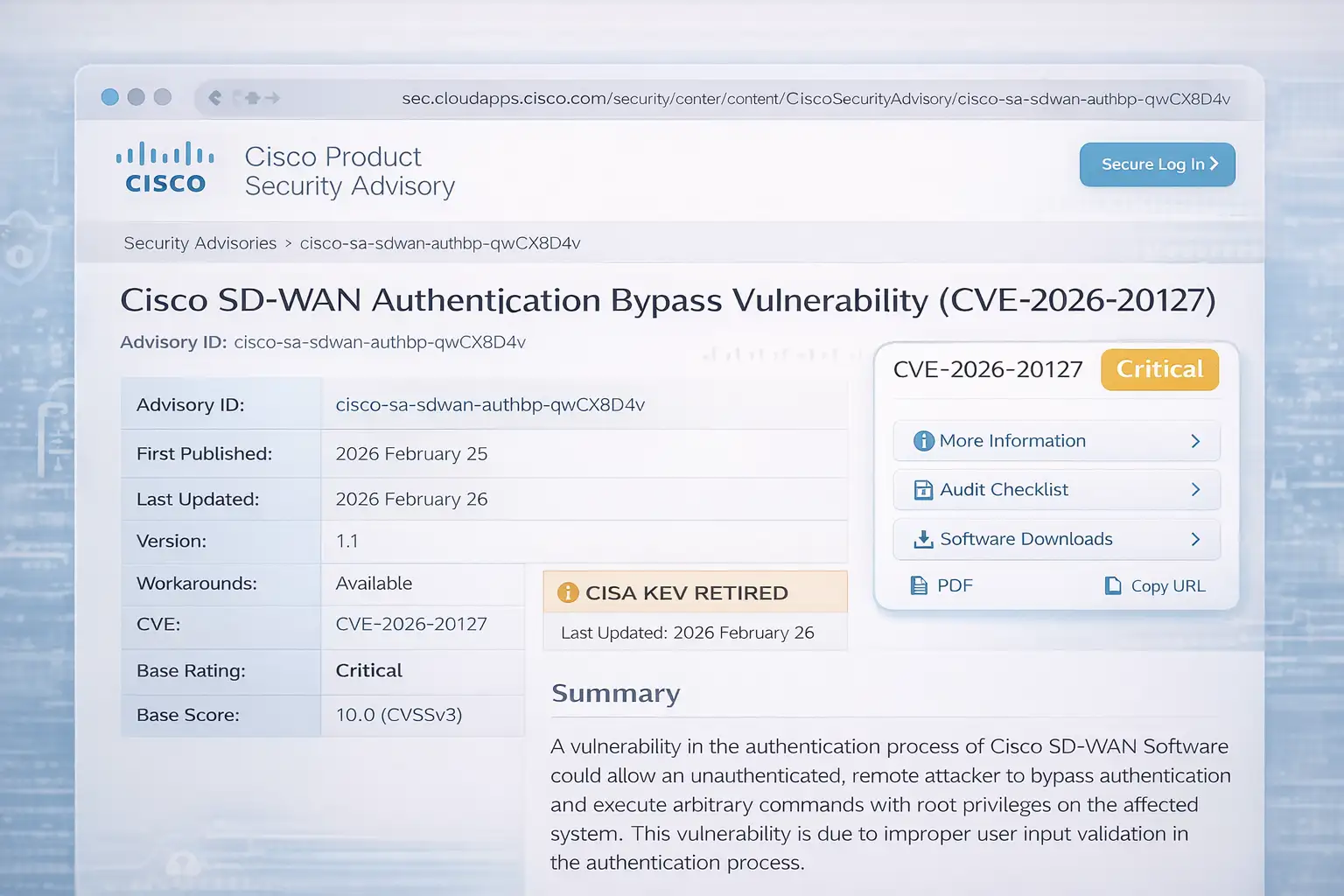
Things get complicated very quickly. The CVSS gives the vuln a perfect 10.0 score. Cisco's warning says that the problem is with the wrong checks in the authentication flow. Talos, Cisco's intelligence arm, connects it to "UAT-8616," a dangerous group. They've been doing it for years without anyone knowing.
Not every setup gets this. Only some versions of Catalyst SD-WAN Manager (formerly known as vManage) work. But if you're on one of the affected releases, you should assume that you are.
I remember talking to a friend who works in network administration last year. For months, his team looked for strange peering logs. It turned out to be exactly like this. No patch then. Just angry.
What is the reason for this Cisco SD-WAN zero-day?
These kinds of bugs don't just show up out of nowhere. Companies stopped using rigid hardware and started using software overlays, which led to a boom in SD-WAN technology. Cisco is the biggest player in the enterprise and government markets. But flaws come from complexity.
Shared secrets or certs are what make peering auth work. In this case, the code doesn't check requests correctly, so junk requests get through. Set the stage for past problems. Cisco has seen other zero-day flaws before, like those in IOS XE. Attackers learn.
UAT-8616 got clever and used older holes like CVE-2022-20775 to get root access by downgrading software and then upgrading it again. Cunning. It gets past most scans. Why do you keep going? SD-WAN controllers are often left out in the open, managing overlays without strong segmentation.
Late notice for regulators. Five Eyes (the US, UK, Australia, New Zealand, and Canada) put out a joint guide. CISA added it to the list of Known Exploited Vulnerabilities, which means that federal patches must be made by the end of February 2026.
What is the background? Cloud shifts happened quickly and left holes. Orgs chased flexibility instead of lockdown. As a result, Cisco SD-WAN zero-day exploits will have a perfect storm.
One analyst I follow called it "the price of software-defined everything." He is correct. Speed wins, but security loses if it's not given enough attention.
What is the Cisco SD-WAN Zero-Day Exploit, and how does it work?
Let's break it down into steps. No jargon overload. I'll keep it simple, like talking to that friend over coffee.
First, the entrance. Attackers used scouts to find controllers. Many people use the internet to manage things from afar. They shoot crafted packets at the peering endpoint. Check for auth? Falls without making a sound. They go in as "internal" users with high permissions.
Next, let's talk about escalation. That account is NETCONF. It uses XML and controls overlays. The attacker adds a bad peer: their own box, which is now trusted. It connects to the network, encrypts tunnels, and draws in traffic.
Persistence sets in. Did someone mess with the logs? Check. Root by downgrading? Talos says it's possible.
Lastly, lateral play. Rogue peers snoop, reroute, and exfil. Or puts malware on your computer. All of this while looking normal.
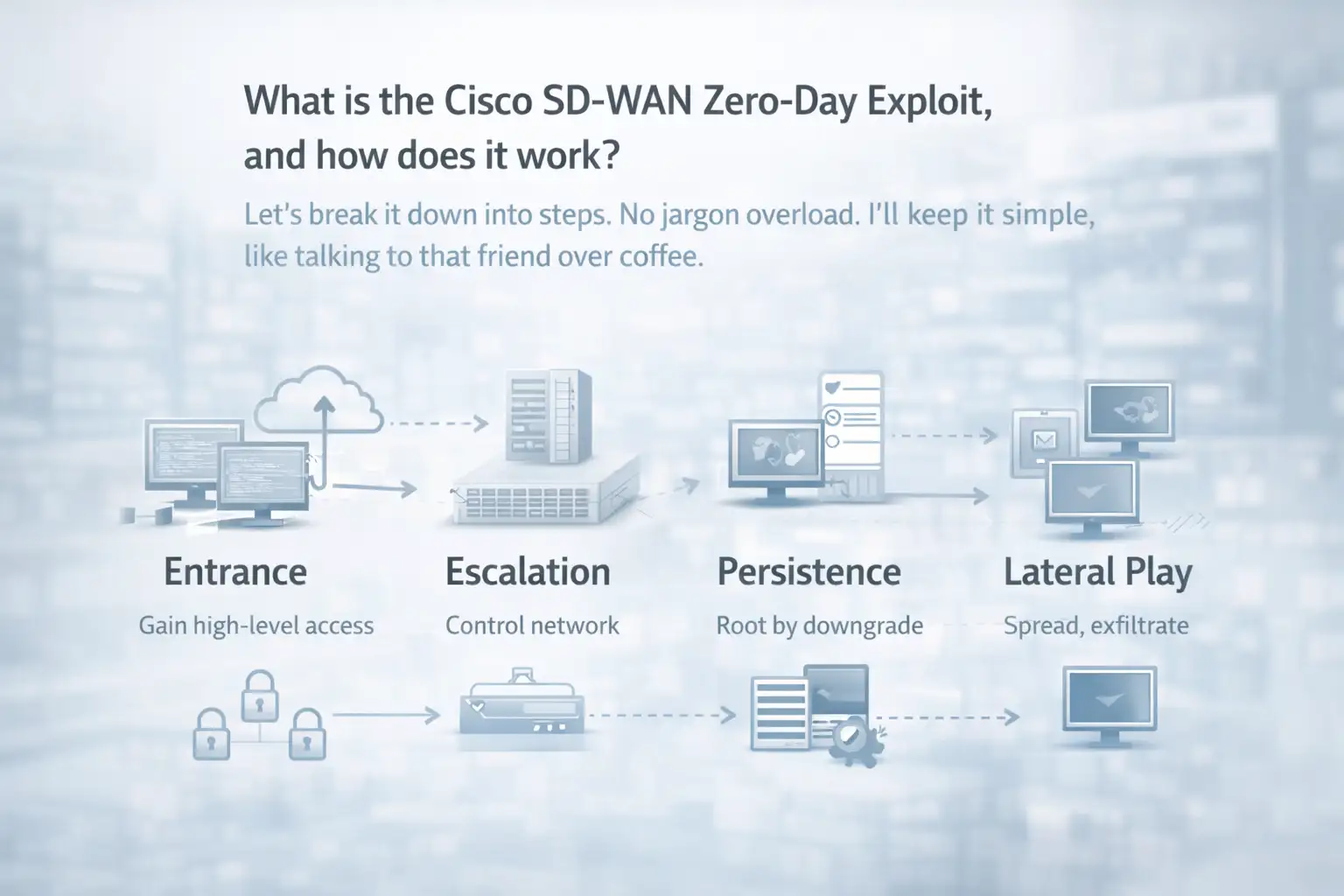
It feels like it takes a long time to happen. Not a crash. Calm compromise. That's the fear.
A Real-Life Example of the Impact of Cisco SD-WAN Zero-Day
For example, a medium-sized bank. Branches all over the country are connected by Cisco SD-WAN. Saves millions of dollars a year on WAN costs. One day, peering logs go up. A device that isn't known joins. IT shrugs and thinks it's a glitch.
Before: Smooth operations. Customers use the internet to bank, and ATMs hum. Secure overlays keep data safe.
After the exploit, a rogue peer steals transaction logs. Attackers map the internet and hit servers higher up. Time off? Not right away. But the average cost of a breach is $4 million per incident, according to IBM data (not specific here, but typical). The feds require clean installs if the root is owned.
My finance contact saw echoes. "We patched blind," he said. "Hunted logs for weeks." Shift before and after? From trusting blindly to locking down with no trust.
Another point of view: healthcare. Patient portals over SD-WAN. Exploit helps ransomware spread. One chain of clinics had problems and was about to get HIPAA fines.
Lesson learned: Keep a record of everything outside. These stories really hit home. If they knock, you're not paranoid.
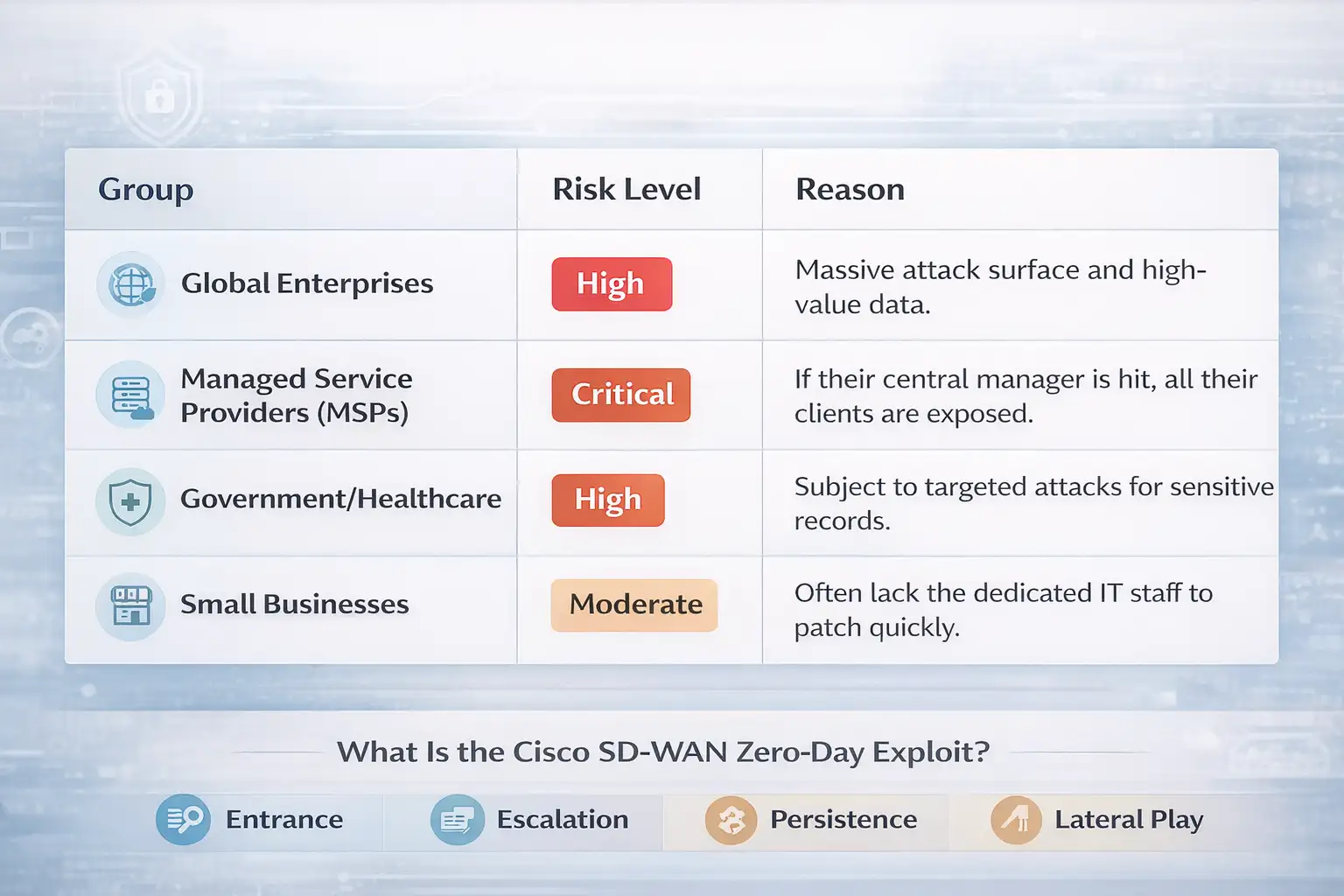
Who Gets Hit by This Cisco SD-WAN Zero-Day?
Not everyone. Targets specific.
First things first: businesses. Companies that use Catalyst SD-WAN Manager, versions before fixes. Retail chains, branches, and manufacturers. 70% of the Fortune 500 companies use Cisco networking, and many of them use SD-WAN.
Next up, the pros of government. The order from CISA is binding on the feds. Energy and transportation are critical infrastructure. Five Eyes tells all of its allies to be careful.
Do you use it often? Not as much. Home setups don't use enterprise SD-WAN. But what about MSPs who run client networks? Very risky. The people who work in IT ops and NOC teams are the most stressed.
It depends on the configuration. Controllers that connect to the Internet amplify.
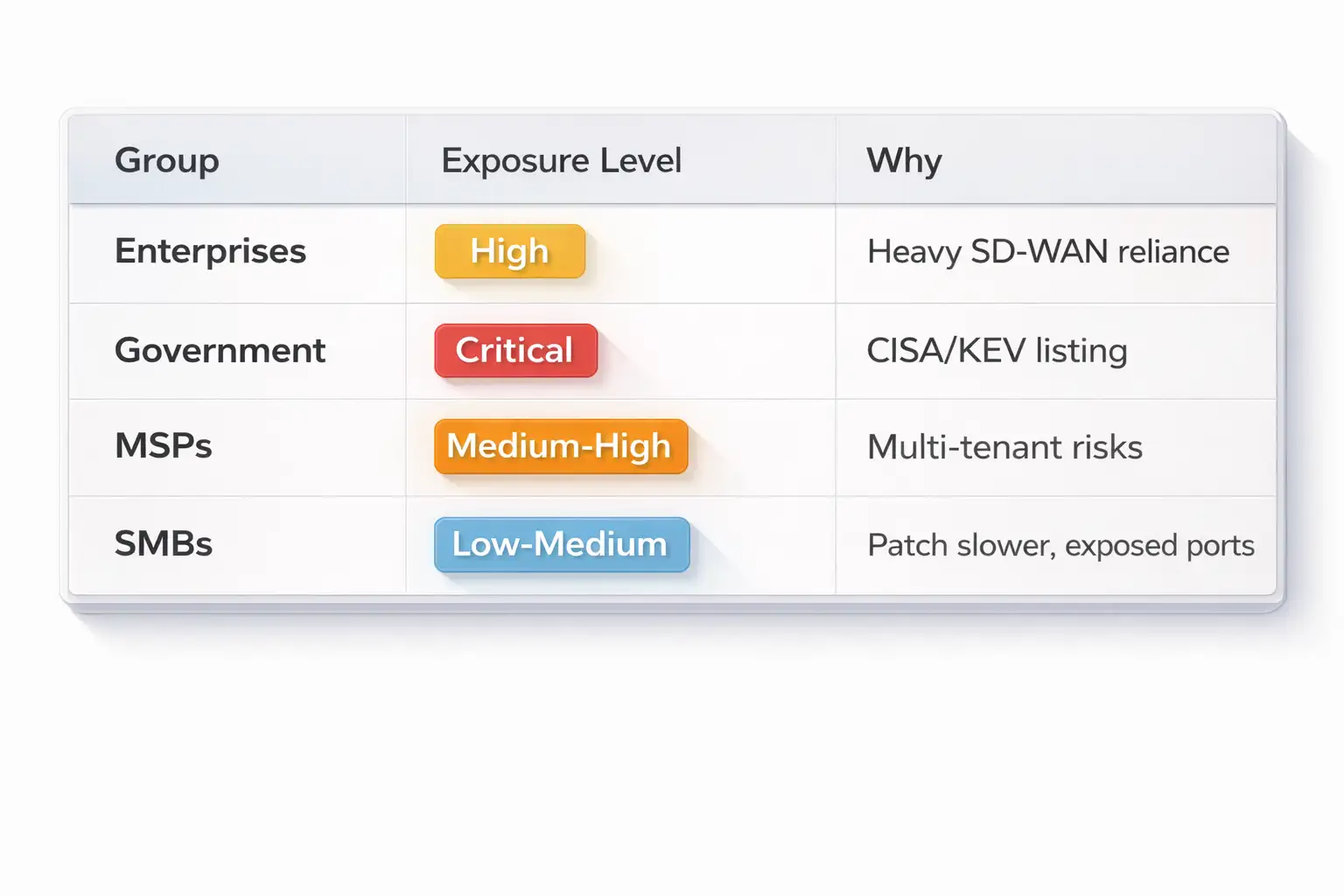
I've seen SMBs ignore until they break. Don't.
Pros and cons of patching now
Patching kills the zero-day in Cisco SD-WAN. Updates were made available by Cisco. Upgrade, no more problems.
Benefits: Persistence is blocked. No bad peers. Networks belong to you.
But downtime is coming. Upgrades are needed all the time. Try it out first. According to Cisco, some people say they have 99.9% uptime after the patch.
Measurable: In similar cases, the risk of a breach went down by 90% (industry average).
What are the limits? No full solution. Firewalls help, but not enough. Logs could already be gone. Think like a breach.
Patch wins: balanced. Delay loses. One company was able to cut incident response time by 40% with quick fixes.
Trade-offs are real. Put them on a scale.
Do these things right away
This is how.
Look at the exposure. Use Cisco's version scanner. Are you affected? Patch to fixed release.
Hunt for signs. Strange peers? Strange things with the controller? Look into it. Send logs to SIEM.
Harden. Ports for managing firewalls. Keep controllers apart. Read the Cisco guide.
If hacked, do fresh installs. Wipe and rebuild. If necessary, report to NCSC/CISA.
Script audits that are useful. I check NETCONF logs once a week.
Do this. Get more sleep.
Questions that come up a lot
What sets off the Cisco SD-WAN zero-day exploit?
Made requests for peering auth. No action is needed from the user. Controllers that are exposed are weak.
Is there a way to get around CVE-2026-20127?
No. Patches are the only full fix. Interim: Limit access and keep an eye on peers.
How long have people been taking advantage of this Cisco SD-WAN zero-day?
Telemetry shows from 2023 onward. UAT-8616 has been active for years.
Does patching mess up my network?
Not often. Test in the lab. Cisco says that it works perfectly for most people.
Who keeps an eye on this threat actor?
Cisco Talos calls it UAT-8616. Very advanced.
In conclusion, stay ahead of the shadows
This zero-day exploit for Cisco SD-WAN is a good reminder that networks change and threats follow. For years, it was quiet. Now it's in the spotlight. Hunt, patch, and harden.
What about the future? As SD-WAN grows, there will probably be more zero-days. But being proactive wins. You are safe as long as your eyes are open.
Old reactive patching slows down breaches. New zero-trust and automation find bad guys quickly. As a result, networks that fight back save millions of dollars in downtime.
Hoplon Infosec does a great job here. Their threat hunting is different from regular audits because it uses both AI and human intelligence to find things that regular tools miss. According to case studies, companies can find things 60% faster.
Are you ready to lock up?
Box of Hoplon Insight
• Do a full SD-WAN audit today.
• Add logging from outside sources.
• Partner for managed detection.
Study Quote
"This isn't a case of patching and praying. Assume compromise." - Cyber Security Center of Australia
Was this article helpful?
React to this post and see the live totals.
Share this :