Mobile Payment Security Solutions in 2026: Key Updates

Hoplon InfoSec
07 Feb, 2026
Are mobile payment security solutions enough to keep everyday tap-to-pay and wallet apps safe right now, on February 4, 2026?
Yes, for most people, mobile wallets can be very safe when they rely on tokenization, strong device security, and good bank controls. But scams that trick people into approving wallet setup, plus malware-driven NFC relay fraud, have become a very real problem. That is why the “best security” today is not just encryption. It is stopping the card from being added to the wrong device in the first place.
What happened recently and why it matters
Over the past year, one problem has kept showing up in fraud reports and consumer stories: criminals do not always “hack” the wallet app. They often trick a person into handing over a code or approving a prompt, then use that to add the victim’s card to a different phone’s wallet. A January 4, 2026, report described how this kind of digital wallet fraud works in real life, including victims being socially engineered into approving a code or notification that enables the wallet enrollment.
That’s the uncomfortable truth about mobile wallet security in 2026. The strongest cryptography in the world cannot save you if you are tricked into authorizing the wrong action. The “front door” is often the enrollment step, not the tap.
Now layer on a second trend: NFC relay threats moving from theory into real malware tooling. Security researchers have documented Android malware that combines remote control, credential theft, and NFC relay-style capabilities, which raises the stakes for secure mobile payments on compromised phones.
How mobile payments are supposed to stay safe
Let’s make the mechanics simple.
Tokenization: your real card number stays backstage.
In many wallet systems, the real card number is replaced by a token, and that token is what merchants see. EMVCo describes this model as EMV Payment Tokenization, designed to reduce exposure of valuable card data.
Think of it like giving a valet a claim ticket instead of handing them your house keys. The claim ticket is useful inside that system, but it is not your actual key ring.
Secure element and dynamic codes: the “one-time stamp” effect
Apple explains that a device-specific number is stored in a Secure Element, and transactions use a dynamic security code that changes per purchase. That means even if a merchant’s systems are breached, the stolen data is far less useful than traditional card data.
This is why many security professionals still prefer wallet tap to pay over mag stripe swipes. The data is just less reusable.
Device lock and “verify it’s you”
Google Wallet requires device security controls like a screen lock and user verification for tap to pay. This is not “extra friction for fun.” It is meant to prevent someone who picks up your phone from spending freely.
This is also why turning off your lock screen “because it’s annoying” is like taking the front door off your house because keys are inconvenient.

The threats that actually hit people in 2026
Here’s a practical rundown, based on what has been publicly documented.
1) Wallet enrollment scams and OTP trapping
A common pattern is phishing plus urgency. The criminal already has some of your details. Then they call pretending to be the bank or a merchant. They push you to share a code or approve a notification. That action can be the final step needed to add your card to their wallet.
This is where the article-writing internet sometimes gets sloppy. You will see dramatic claims like “Apple Pay got hacked.” In many cases, that framing is wrong.
This appears to be unverified or misleading information, and no official sources confirm its authenticity.
The more accurate explanation is often “the wallet enrollment flow was abused through social engineering.”
2) NFC relay fraud and “ghost tap” style abuse
NFC relay attacks are a category of fraud where communication is relayed between devices to make a transaction look legitimate. Kaspersky has described direct and reverse relay patterns, including how these capabilities can show up inside malware chains.
ThreatFabric documented Rat. On as a malware family combining remote control with NFC relay and automated transfer behaviors. That is a serious evolution, because it blends “phone compromise” with payment misuse.
3) Account takeover and SIM swap pressure
Not every wallet attack touches NFC. Sometimes the target is your email, your bank login, or your phone number. If an attacker can take over an account, they can often reset access, intercept codes, or initiate card provisioning steps.
This is why risk-based authentication matters. It is not just “Do you have the password?” It is “Does this login look like you, on your usual device, behaving normally?”
4) Merchant-side issues: weak controls and noisy alerts
Merchants sometimes assume wallet payments are “handled by Apple or Google.” That is not fully true. Merchants still need good terminal security, fraud monitoring, refund controls, and staff training.
If your cashier happily accepts a rushed, suspicious tap plus a weird story, no amount of encryption helps. Humans are part of the payment system, whether we like it or not.
The most effective mobile payment security solutions in 2026
Let’s talk solutions like a builder, not like a brochure.
1) Strong wallet provisioning controls (banks and issuers)
If I ran a bank program today, I would treat wallet provisioning like opening a new door to an account. Because that’s what it is.
Practical controls that work:
device binding so the token is tied to a known device identity
step-up checks for “new device + new location + unusual spend”
limits on how many devices can provision the same card quickly
Near real-time alerts that clearly say, “A card is being added to a wallet.”
A big gap in many “top 5” articles is that they do not emphasize this. They focus on transaction security, not enrollment security.
This is one of the most important mobile payment security solutions banks can deploy right now because it directly targets the scam pattern being reported.
2) Better authentication: not just SMS codes
SMS codes are better than nothing, but they are also phished, forwarded, or intercepted in SIM swap scenarios.
Better options include
App-based approvals that show what you are approving
passkeys or strong app authentication
Multi-factor authentication that does not depend on a single channel
PCI Security Standards Council guidance explains the general idea behind MFA: use at least two different factors before granting access. While PCI documents are aimed at card data environments, the principle maps well to wallet enrollment risk.
3) On-device security that people actually follow
This is the “boring” advice that saves people.
Use a real screen lock.
Keep OS updates on.
Avoid installing random apps.
Do not enable risky permissions unless you understand them.
Google Wallet explicitly ties tap to pay to having device security like screen lock verification. That is not optional if you want secure mobile payments.
4) Biometric checks, done carefully
Biometric authentication is great for convenience, and it can make fraud harder, but it is not magic.
Samsung’s official announcement in India highlights PIN-free biometric payment experiences in Samsung Wallet, aimed at making onboarding and payments smoother. It is a reminder that major brands are pushing “fast and secure,” not “slow and secure.”
The best implementations combine biometrics with device integrity checks and back-end monitoring, so one stolen face photo does not become a payment key.
5) Tokenization plus secure hardware for transaction protection
This is still a foundation. I would not remove it. I would just stop pretending it solves every problem.
Apple documents device-specific numbers and dynamic security codes, stored in secure hardware. These are key parts of modern mobile payment security solutions for tap transactions.
EMVCo’s payment tokenization framework exists for a reason: to reduce the value of intercepted card data.
6) Real-time fraud detection that understands contactless patterns
The new fraud patterns are not always “big obvious theft.” They can be rapid small purchases, unusual merchant categories, or sudden high-value retail spending right after provisioning.
This is where modern fraud platforms talk about
velocity rules
device intelligence
behavioral analytics
merchant pattern scoring
If you want a market signal that fraud pressure is not going away, Juniper Research forecasted global fraud costs rising sharply over the next several years, with a large increase projected by 2030.
(Their press release also frames it as a major surge trend, which is the key takeaway.)
7) Merchant and employee controls
For merchants, mobile payment security solutions for merchants are often less about cryptography and more about operations:
Keep terminals patched and monitored.
restrict refunds and gift-card cash-out patterns
train staff on social engineering scripts
Enable transaction alerts and reconciliation.
I have seen small businesses lose money not because someone “hacked NFC,” but because someone talked a staff member into doing a refund to a different card. The payment system did exactly what it was told to do.

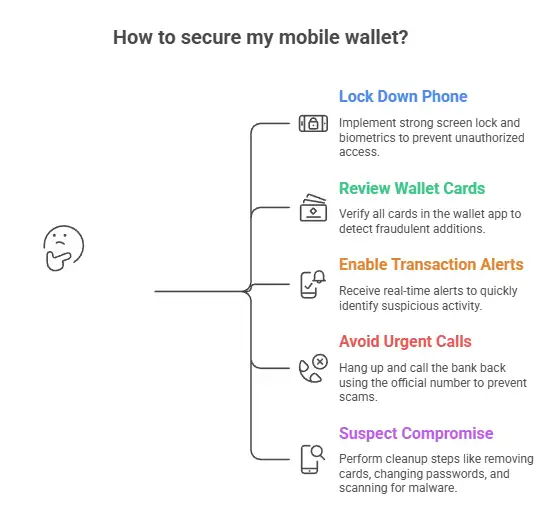
Step-by-step: what users should do next
Here is a realistic checklist you can follow in 10 to 20 minutes.
Step 1: Lock down the phone.
Turn on a strong screen lock and biometrics if you use them. If your phone is older and no longer receives updates, consider that a risk factor for mobile payment security.
Step 2: Review wallet cards and recent transactions.
Open your wallet app and confirm every card belongs to you. If you see a card you did not add, treat it as urgent.
Step 3: Turn on transaction alerts at the bank.
Real-time alerts are not glamorous. They are effective. They shorten the time between fraud and response.
Step 4: Be allergic to “urgent” calls about your wallet.
If someone calls claiming you must approve a wallet action right now, stop. Hang up. Call the bank back using the official number you already trust.
That simple habit blocks a shocking percentage of wallet enrollment scams described in reporting.
Step 5: If you suspect compromise, do the boring cleanup.
remove the card from the wallet
Call the issuer and ask about wallet provisioning history.
change passwords and enable stronger authentication
Scan for malware or reset the device if needed.
If malware is involved, especially NFC relay-capable malware, the safest path may be a full reset after backing up essentials. Threat research shows how these families can chain capabilities.
For businesses: the “beat the Top 5 results” playbook
Most top-ranking posts give generic advice. Here is what tends to be missing and what you can do.
Gap 1: Businesses ignore wallet provisioning as a fraud event.
If you issue cards or run a wallet program, treat provisioning like account opening. Use risk-based authentication and step-up verification when signals look wrong.
Gap 2: Businesses focus on PCI but forget the customer journey.
PCI matters, but modern fraud often happens outside the classic cardholder data environment. The fraud happens in calls, texts, fake links, and manipulated approvals.
Gap 3: No one explains NFC relay in plain language.
An NFC relay attack is basically “extending the tap.” The terminal thinks the phone is present, but the communication is being relayed.
If you run a fraud team, build detection around odd contactless behavior patterns, not just chargeback volume.
Gap 4: Businesses underinvest in customer messaging.
When a bank sends a code, the message should say what the code is for. Google Wallet’s documentation repeatedly reinforces verification context and the idea that codes come from the bank, not Google. That distinction matters when fighting impersonation scams.
FAQs
Is Apple Pay safer than a physical card?
In many cases, yes, because the merchant does not receive your actual card number, and each transaction uses a dynamic code tied to the device’s secure hardware. That reduces the value of stolen payment data from breaches.
How do criminals add my card to their phone?
Commonly through social engineering. They trick you into sharing a code or approving a prompt that is actually authorizing wallet enrollment. Reporting has highlighted this exact pattern.
What is an NFC relay attack, and can it happen to me?
An NFC relay attack relays contactless communication so a payment can be made without the legitimate device being physically at the terminal. It is more likely if a device is compromised by malware or if criminals are using specialized tooling.
What should I do if I see a wallet I didn’t set up?
Remove the payment method, contact your bank immediately, ask whether a new wallet token was provisioned, review recent transactions, and secure your accounts and device. If you suspect malware, consider a full device reset after proper backup.
practical recommendations
If you want a simple “do this, not that” approach to mobile payment security solutions, here’s my honest shortlist:
Treat wallet enrollment alerts like smoke alarms. Do not ignore them.
Use device lock and keep your phone updated. Convenience is not worth it.
3. Find out how your bank checks the wallet's provisioning. If SMS is the only option, ask for better ones if they exist.
For businesses, focus on provisioning risk scoring and rapid detection of unusual contactless patterns. That is where modern fraud is moving.
Takeaway: the safest wallet is the one that is hard to enroll, easy to monitor, and quick to shut down.
In 2026, mobile payment security solutions are not just about making tap to pay “encrypted.” They are about preventing the wrong device from getting a valid token and catching fraud fast when a human gets tricked.
If you do the basics well, wallet payments can still be a strong option. But the industry needs to keep tightening enrollment checks, and users need to stop treating verification codes like harmless spam.
Was this article helpful?
React to this post and see the live totals.
Share this :