How Hackers Bypass Outlook Spam Filters: Hidden ISO Malware Threat

Hoplon InfoSec
25 Feb, 2025
A recently uncovered technique has revealed a significant vulnerability in Microsoft Outlook’s spam filtering system. This method enables attackers to deliver malicious ISO files through seemingly benign email links. Cybercriminals can bypass Outlook’s spam filters by disguising harmful content behind innocuous-looking text, leading to potentially dangerous phishing and malware attacks. In this article, we explore the details of this bypass technique, discuss its potential implications, and provide comprehensive mitigation strategies to help organizations protect themselves from these evolving threats.
The Emergence of Hyperlink Obfuscation in Email Threats
Hyperlink obfuscation is not entirely new to cyber attackers; however, the sophistication of this technique has grown in recent years. By embedding a malicious URL beneath a text that appears safe, attackers exploit a systemic weakness in email security systems—namely, the focus on the visible link text rather than the actual destination URL.
How Bypass Outlook Spam Filters Works
Microsoft Outlook’s spam filtering system traditionally flags emails containing direct links to dangerous file extensions, such as .iso or .exe. For example, an email containing a visible link like https://afine.com/update.iso would typically be identified as potentially harmful and moved to the junk folder. However, cybercriminals have developed a technique where the malicious URL is hidden behind a seemingly harmless text.
This method works by:
- Email Crafting: Attackers create emails that include hyperlinks with embedded dangerous URLs.
- Filter Evasion: The spam filter inspects only the visible text of the link, not the underlying href attribute, which contains the actual destination.
- User Interaction: Once users click on the seemingly safe link, they inadvertently download an ISO file that bypasses additional security checks.
This clever evasion strategy allows the harmful payload to slip past Outlook’s spam filtering, potentially leading to widespread compromise within organizations.
Historical Parallels and Context
The recent vulnerability mirrors historical incidents, such as the flaw identified as CVE-2020-0696. In that instance, improper hyperlink parsing in Outlook for Mac allowed attackers to bypass security controls using similar techniques. These recurring patterns underscore the importance of addressing vulnerabilities that arise from reliance on surface-level analysis of URLs in emails.
Detailed Mechanism of the Bypass Technique
Understanding the mechanism behind this bypass is crucial for developing effective defences. The process can be broken down into three primary steps: email crafting, filter evasion, and user interaction.
Email Crafting: Laying the Foundation for Attack
Cyber attackers begin by constructing an email that appears to originate from a legitimate source. The email contains a hyperlink that, at first glance, looks completely ordinary. However, behind the scenes, the link’s destination is a malicious website hosting an ISO file. Once downloaded and executed, this file can unleash malware that exploits vulnerabilities in the system.
The attackers rely on social engineering tactics to persuade the recipient that the email is safe and the link should be clicked. Often, the email will be styled to mimic trusted sources, making it even more likely that the target will engage with the content.
Filter Evasion: Exploiting the Limits of Outlook’s Inspection
Outlook’s spam filtering system is designed to scan emails for known malicious patterns. It focuses on the visible text of hyperlinks rather than the underlying href attribute that specifies the URL destination. By embedding a dangerous URL beneath a benign text, attackers effectively hide the threat from automated scanners.
For instance, the email may display a link with the text “Download the latest update here,” which, if clicked, leads the user to a page hosting the malicious ISO file. Since the filter only “sees” the text and not the proper destination, the harmful content is delivered to the user’s inbox without raising red flags.
User Interaction: The Final Step in the Attack
The final link in the chain is the unsuspecting user. When recipients click on the seemingly harmless link, they are redirected to download the ISO file. These ISO files often contain executables designed to bypass further security measures, such as SmartScreen protections, by exploiting vulnerabilities like the Mark-of-the-Web (MOTW) bypass.
Once the file is downloaded, if executed, it can compromise the user’s system, leading to further propagation of malware, credential theft, or even ransomware deployment. This three-step process—careful email crafting, exploiting filter weaknesses, and manipulating user behaviour—illustrates how a simple tactic can have profound security implications.
The Impact on Organizations
The implications of this vulnerability are significant, especially for organizations that rely heavily on Microsoft Outlook for communication. The ability of threat actors to bypass standard security measures means that even well-established security protocols can be rendered ineffective against this kind of attack.
Increased Risk of Phishing and Malware Distribution
Bypassing Outlook’s spam filter allows threat actors to conduct targeted phishing campaigns with higher success rates. Since the malicious ISO files are delivered directly to the inbox, users are likelier to click on the embedded links, assuming they are legitimate. Once the ISO file is downloaded and executed, the door is opened for malware to infiltrate the organization’s network.
Challenges for Endpoint Security Systems
Even if an organization employs robust endpoint security measures, the initial bypass during email delivery can allow malware to gain a foothold before these systems respond. Many endpoint security tools are designed to detect malicious content after it has been executed, but in this case, the ISO file may slip through the initial email filter undetected.
Targeting High-Value Entities
Organizations that rely exclusively on Outlook’s native spam filtering, particularly those without layered defence strategies, are at acute risk. High-value targets such as financial institutions, government agencies, and large enterprises may be more attractive to cybercriminals looking for opportunities to deploy ransomware, steal sensitive information, or conduct widespread espionage.
Mitigation Strategies to Counter Hyperlink Obfuscation
Given the seriousness of this threat, organizations need to adopt a multi-layered defence approach. Here are several strategies that can be implemented to mitigate the risks posed by hyperlink obfuscation attacks:
Advanced Email Security Solutions
Investing in advanced email security tools can make a significant difference. These solutions are designed to resolve shortened or obfuscated URLs and inspect the final destination before delivering the email to the user’s inbox. By analyzing the entire link, these tools can identify and block emails that contain hidden malicious URLs.
For example, some modern email security systems integrate machine learning algorithms to detect unusual patterns in URL structures. They can flag links that deviate from typical formatting, adding an extra scrutiny layer beyond simple text matching.
User Awareness and Training
Despite technological advancements, user vigilance remains a critical component of cybersecurity. Regular training sessions should be conducted to educate employees about the risks associated with hyperlink obfuscation. Users should be advised to constantly hover over links to view the URL before clicking, especially if the email is unsolicited or appears out of character for the sender.
Employees can be taught to recognize common red flags such as:
- Unsolicited emails that request urgent action.
- Links using generic text like “Click here” or “Download now” without clearly indicating the destination.
- There are slight misspellings or unusual domain names in the URL when inspected.
Organizations can reduce the likelihood of successful phishing attempts by fostering a culture of scepticism and awareness.
Combining Email Filtering with Endpoint Detection and Response (EDR)
While advanced email filtering can catch many malicious emails, it is essential to integrate these systems with robust endpoint detection and response (EDR) tools. EDR systems provide real-time monitoring of network activities and can quickly identify abnormal behaviours, such as the unauthorized execution of downloaded ISO files.
This combination ensures that even if a malicious file slips past the initial email filter, it is still subject to thorough inspection once it reaches the endpoint. In the event of a breach, EDR solutions can help contain the spread of malware by isolating affected systems and initiating incident response protocols.
Restricting ISO File Execution
Another effective mitigation strategy is to impose strict controls on the execution of ISO files. Organizations can minimize the risk associated with accidental downloads by restricting the ability to run these files to only approved directories or applications. Monitoring abnormal file access patterns and implementing allowlisting policies for trusted executables further strengthen this defensive measure.
The Role of Microsoft Safe Links and Its Limitations
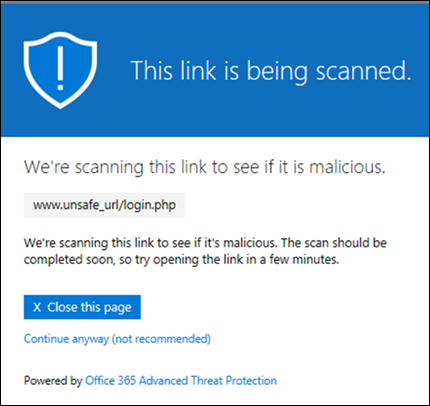
Microsoft’s Safe Links feature, part of its Advanced Threat Protection (ATP) suite, offers a robust solution by rewriting URLs in emails to scan them in real time. This service is designed to analyze the destination of links before a user clicks on them, thereby providing an additional safety net against malicious URLs.
How Safe Links Works
Safe Links functions by intercepting the URL when a user clicks on it and then evaluating its safety against a database of known malicious sites. If the URL is deemed unsafe, the user is redirected to a warning page instead of the malicious site. This process helps prevent the execution of harmful files that could compromise the system.
Limitations and Inconsistencies
Despite its potential, the Safe Links feature has shown inconsistent performance across different Outlook clients and third-party email integrations. The variability in implementation can leave gaps in protection, meaning that some emails with obfuscated hyperlinks may still reach the recipient’s inbox. Organizations that rely solely on Safe Links without additional layers of security may find themselves exposed to risk.
Recommendations for a Proactive Defense
In light of the vulnerability and the sophisticated methods threat actors use, organizations must take a proactive approach to cybersecurity. Here are some key recommendations to bolster defences against hyperlink obfuscation attacks:
Layered Security Architecture
Relying on a single security solution is no longer sufficient. Organizations should implement a layered security architecture that includes:
- Email Security Solutions: Tools that examine the visible text and underlying URLs in emails.
- Endpoint Detection and Response (EDR): Systems that continuously monitor endpoints for suspicious behaviour.
- Network Security Measures: Firewalls, intrusion detection systems, and regular network scans to detect and isolate threats.
- User Training Programs: Regular sessions to educate employees on recognizing and responding to suspicious emails.
A layered approach ensures that if one defence fails, additional measures are in place to stop the threat from propagating.
Regular Security Audits and Penetration Testing
Conducting periodic security audits and penetration testing is critical to identifying and addressing vulnerabilities. These exercises help organizations understand their current security posture and provide actionable insights into areas that need improvement. By simulating phishing attacks and other common threat scenarios, security teams can assess how well existing defences perform under real-world conditions.
Encouraging Vendor Transparency
Cybersecurity professionals should also advocate for greater transparency and timely vulnerability management from software vendors. When vendors like Microsoft classify a vulnerability as low risk and delay patching, organizations that depend on their native security features remain exposed. By pushing for more rigorous vulnerability management practices, the cybersecurity community can help drive improvements in security protocols and reduce the exposure window for newly discovered threats.
Conclusion
The discovery of this bypass technique—where threat actors use hyperlink obfuscation to deliver malicious ISO files via Microsoft Outlook—is a stark reminder of the evolving nature of cyber threats. Although Outlook’s spam filtering system is designed to protect users by scanning visible link text, failing to inspect the underlying URL opens a significant vulnerability. Attackers can exploit this weakness to deliver malware, evade endpoint protections, and target organizations that rely solely on native email security measures.
To counter these threats, organizations must adopt a multi-layered defence strategy. This includes investing in advanced email security tools, integrating endpoint detection and response systems, and training employees to recognize suspicious links. Additionally, while Microsoft’s Safe Links feature provides some protection, its limitations mean that relying exclusively on it is insufficient. A proactive and comprehensive approach—encompassing technology and user education—is essential to staying ahead of cybercriminals.
Ultimately, the responsibility for cybersecurity is shared across the organization. By combining technical solutions with robust policies and continuous education, companies can mitigate the risks associated with hyperlink obfuscation attacks and build a resilient defence against future threats.
For more:
https://cybersecuritynews.com/hackers-bypassing-outlook-spam-filter/
Was this article helpful?
React to this post and see the live totals.
Share this :