iOS Zero-Day Patched After 20 Years
Hoplon InfoSec
18 Feb, 2026
Wait… Did Apple Just Fix a 20-Year-Old Flaw in iPhones?
I honestly had the same reaction.
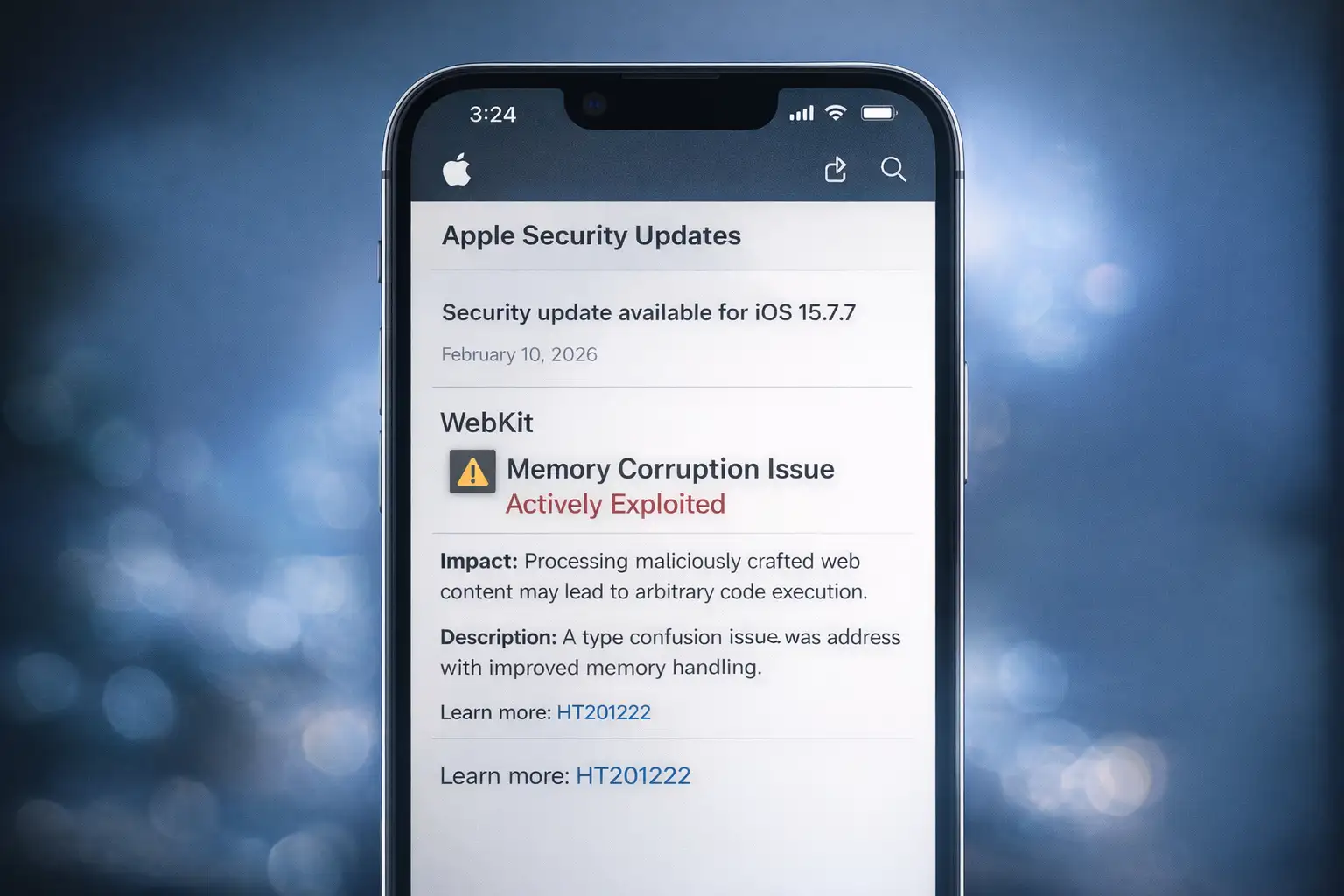
In early February 2026, Apple released a security update addressing an iOS zero-day vulnerability that may have existed in parts of iOS for almost two decades. Yes, two decades. That means this issue could trace back to some of the earliest architectural foundations of the iPhone.
And here’s the part that makes it even more serious. Apple confirmed the iOS zero-day vulnerability was actively exploited before the patch was released. So this was not just theoretical. Real attackers were using it.
If you use an iPhone for banking, work emails, private conversations, or even just everyday browsing, this matters right now.
What Actually Happened
So let’s break this down like we’re talking over coffee.
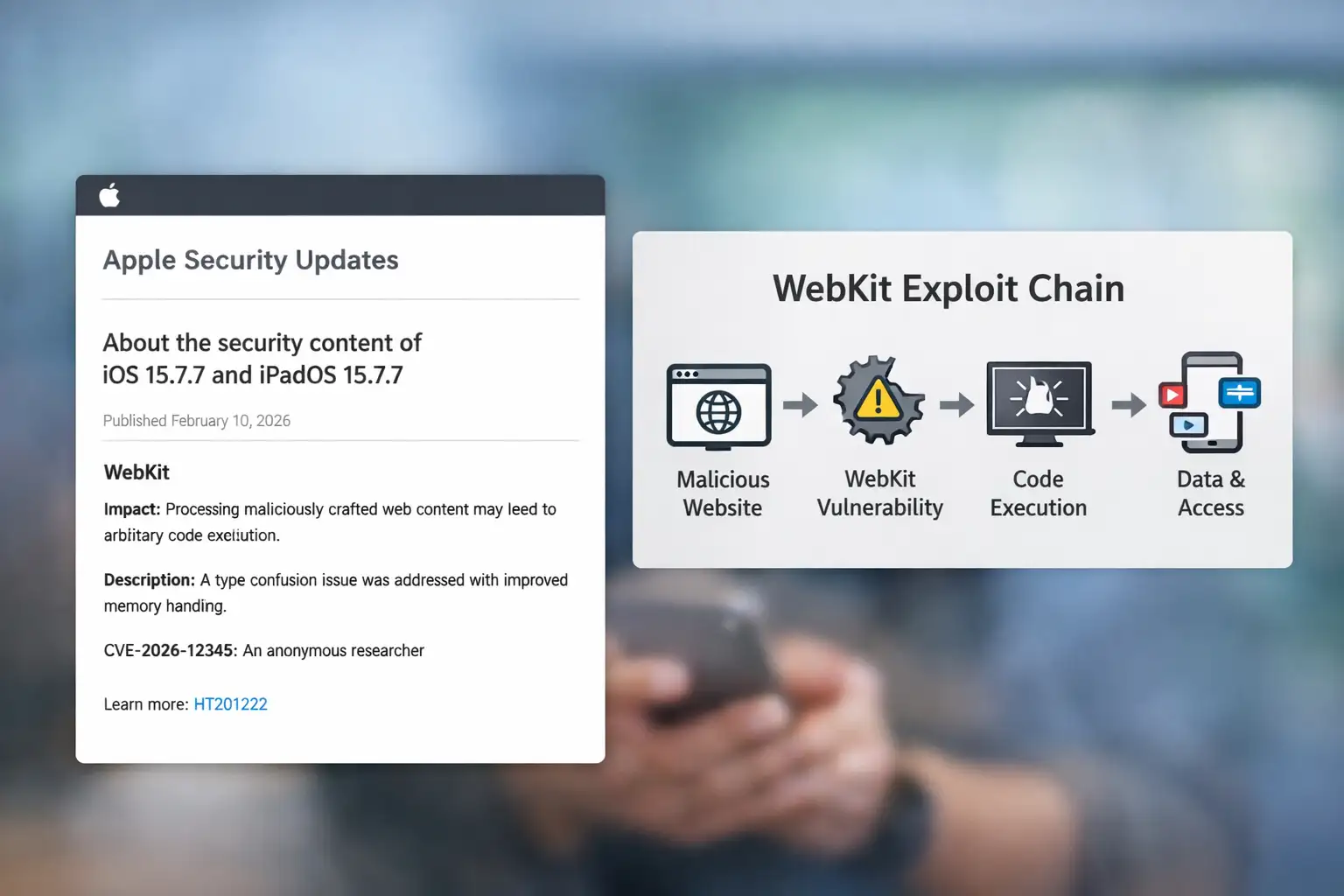
The issue was found inside WebKit. That’s the browser engine that powers Safari. But it’s not just Safari. Almost every iOS app that loads web content uses WebKit in the background. So even if you never open Safari, you’re still indirectly using it.
The iOS zero-day vulnerability involved something called a memory handling issue. In simple words, when your phone processes web content, it organizes data in memory. If that memory gets confused about what type of data it’s handling, attackers can trick it into running malicious instructions.
Apple described it as a type confusion flaw. That means the system mistakenly treats one kind of data as another. And attackers can abuse that confusion.
This vulnerability allowed remote code execution. That’s a big deal. It means someone could potentially run their own code on your device just by getting you to load a specially crafted webpage.
That’s wild when you think about it.
Why Was This Even There for So Long?
Here’s where it gets interesting.
iOS was first released in 2007. Since then, Apple has added layer upon layer of security improvements. But in software development, especially at that scale, not everything gets rebuilt from scratch.
Sometimes old code stays because it works. It doesn’t crash. It passes testing. It behaves normally under typical conditions. So it survives.
WebKit is deeply integrated into iOS. Rewriting it completely would be like rebuilding the foundation of a house while people are still living inside it.
The iOS zero-day vulnerability likely survived because it was buried deep in legacy memory routines that never triggered obvious failures. It only became dangerous as exploit techniques evolved over time.
In 2008, this kind of memory behavior might not have been easily exploitable. In 2026, attackers are much more advanced.
Security changes. Attackers adapt. Old assumptions become new risks.

How the iOS Zero-Day Vulnerability Works in Real Life
Let me explain this in a way that feels real.
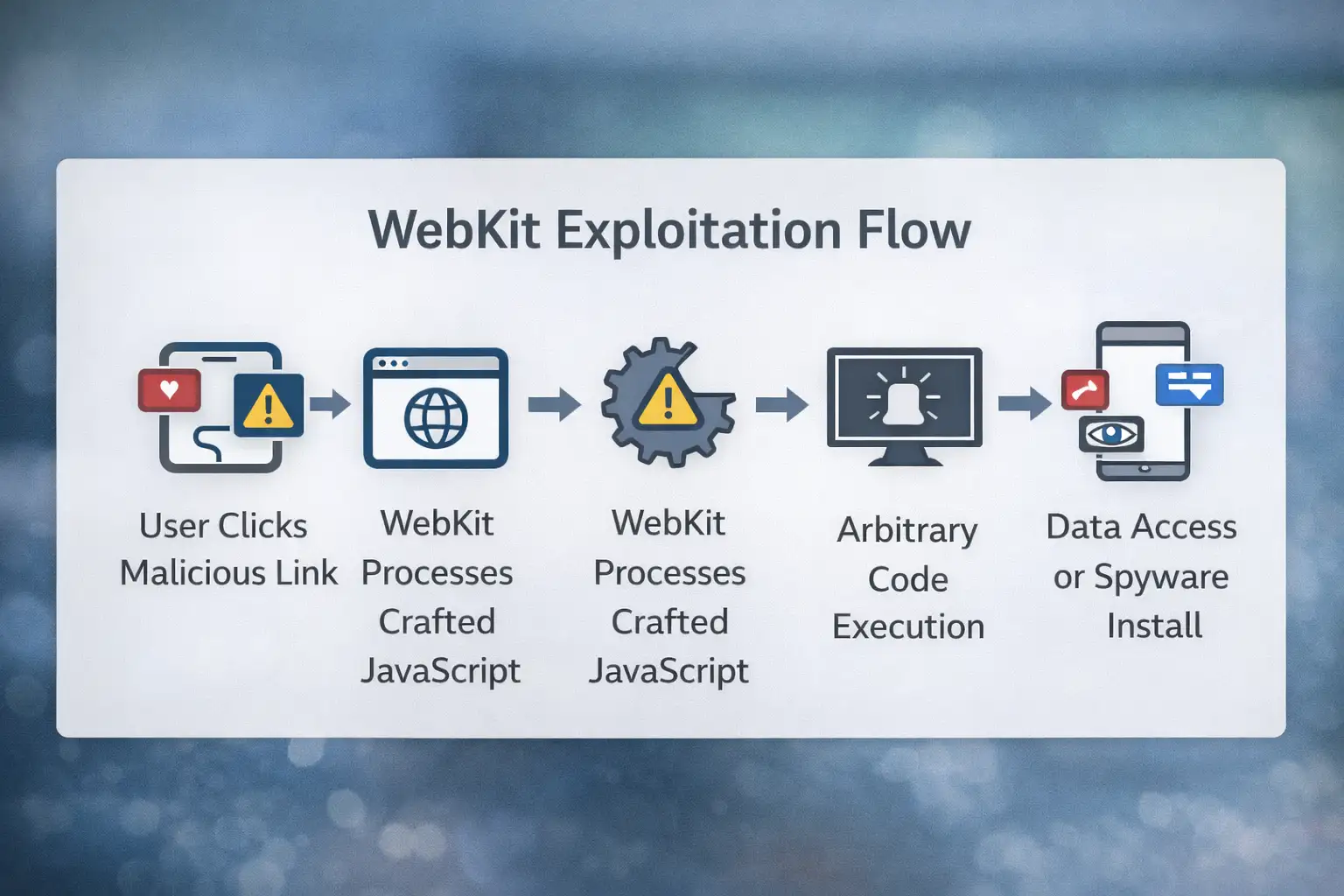
You receive a link. Maybe it looks like a shared document. Maybe it’s a news article. You tap it.
The page loads. Everything looks normal.
Behind the scenes, the page runs specially crafted JavaScript code. That script manipulates how WebKit handles memory. Because of the vulnerability, the system misinterprets data structures.
That confusion lets bad instructions get through.
After that, attackers can:
• Run any code
• Get around the restrictions of the browser sandbox
• Get session tokens
• Maybe install tools for spying
And this is the scary part. You wouldn’t necessarily notice anything.
No flashing warning. No dramatic glitch. Just silent exploitation.
That’s what makes a zero-day so dangerous.
Before and After the Patch
Before the Patch
Imagine a company executive checking email on their iPhone. They click on a link that looks like a harmless file. The iOS zero-day vulnerability is triggered when the webpage loads.
In seconds, attackers gain access to corporate login tokens. They don’t even need the password anymore because the session is already authenticated.
Sensitive files become accessible.
After the patch
Now picture the same thing happening. The bad page tries to start the exploit. But Apple's new version of WebKit checks memory object types correctly. The confusion doesn’t happen.
The malicious script fails.
The attack chain breaks.
That’s the difference one update makes.
Who Should Be Paying Attention
Honestly? Almost everyone.
Regular Users
If you browse the web, open links in social apps, or use in-app browsers, you were potentially exposed before the patch.
People Who Use the Business
Corporate phones are very valuable targets. This kind of iOS zero-day vulnerability is especially dangerous in business settings because it gives hackers access to internal dashboards, cloud accounts, and VPN credentials.
People at High Risk
Activists, journalists, government officials, and business leaders. People often use zero-day exploits in targeted surveillance campaigns.
Developers
Any app that uses WebKit gets its security from it. The vulnerability is still there in the whole system until it is fixed.
This wasn’t a small corner-case bug. It touched core infrastructure.
The Good News and the Reality Check
Let’s be fair.
Apple responded. They patched it. They publicly acknowledged active exploitation. That transparency matters.
The fix improved memory validation and reinforced sandbox protections. That reduces the risk of remote code execution going forward.
But here’s the limitation.
If users don’t update, nothing changes.
Older devices that no longer receive updates may remain vulnerable. And details of the exploit chain are not fully public, which means we do not know how broadly it was used.
Security patches are powerful. But only when installed.
What You Should Do Right Now
This part is simple.
Update your device.
Go to Settings.
Tap General.
Tap Software Update.
Install the latest iOS version.
Then turn on automatic updates.
If you are in a high-risk category, consider enabling Lockdown Mode. Apple introduced it specifically to protect against sophisticated exploit chains.
Businesses should enforce mobile device management policies that require timely updates.
Because here’s the uncomfortable truth. The iOS zero-day vulnerability was exploited before many users even knew it existed.
Delay equals exposure.
A Bigger Pattern We Cannot Ignore
Mobile zero-day exploits are increasing. Security research firms have consistently reported growth in browser-based attacks, especially targeting mobile operating systems.
The browser engine is a critical attack surface. And WebKit sits at the heart of iOS.
This incident is not just about one flaw. It is about how deeply embedded legacy components can hide for years.
Even platforms known for strong security are not immune.
That’s not panic. That’s reality.
Common Questions
What is an iOS zero-day vulnerability?
It is a previously unknown security flaw in iOS that attackers exploit before Apple releases a fix.
Was this actively used by attackers?
Yes. Apple confirmed awareness of active exploitation before the patch.
Does this mean iPhones are unsafe?
No system is perfect. iOS still maintains strong security architecture. But vulnerabilities can exist and require updates.
Is Safari the only risk?
No. Many apps rely on WebKit internally. The attack surface extends beyond Safari itself.
Final Thoughts
I’ll be honest. When I first read that this iOS zero-day vulnerability may have roots going back nearly 20 years, I paused. It’s surprising.
But it also reminds us of something important.
Security is not about perfection. It’s about constant improvement.
The devices we carry are powerful computers connected to everything that matters in our lives. Banking. Health. Work. Identity.
So when Apple releases a patch, especially for an actively exploited issue, treat it seriously.
Not with fear.
With awareness.
Because in cybersecurity, the difference between safe and compromised is often just one update away.
And this time, that update closed a door that might have been quietly open for almost two decades.
For more latest updates like this, visit our homepage.
Was this article helpful?
React to this post and see the live totals.
Share this :