LexisNexis Data Breach Know How to Stay Protected

Hoplon InfoSec
04 Mar, 2026
Did a big data broker really say that a security breach happened in June 2026, when files that were stolen were put online?
Of course. LexisNexis data breach disclosures confirmed that someone had access to the data without permission and that the stolen data was later posted online.
LexisNexis has a lot of personal and business information that it uses for identity verification, risk analysis, and compliance services. This is why this situation is so important.
This isn't just another tale of a company that was hacked. When a big data broker gets hacked, it can hurt banks, insurance companies, and even regular people. The LexisNexis data breach quickly became a hot topic in the security world because of this.
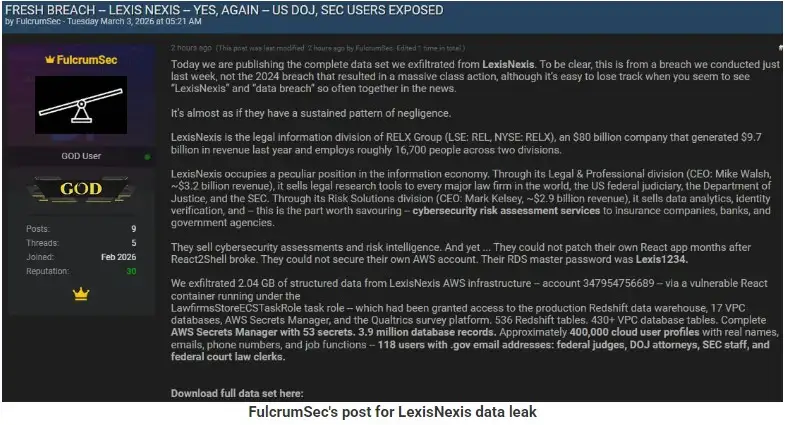
(Image Source: bleepingcomputer)
What Really Happened in the LexisNexis Data Breach?
The confirmed LexisNexis data breach involved unauthorized access to internal systems, and it is said that stolen files were then leaked online. The company said in a public statement that the breach was found after they noticed something strange happening. After that, the company started looking into how big the exposure was.
At this point, some technical details are still unclear. Public reports have not named any specific malware, CVE IDs, or threat actors. Regulatory filings or security updates would usually include any new forensic evidence that comes to light. It is important not to guess about anything that hasn't been confirmed yet.
We do know that data that was leaked showed up online, which means that attackers not only got to the information but also took it. Copying sensitive files out of a system is what data exfiltration means. That is often worse than a short-term problem with the system.

What Makes This Event Feel Different?
Data brokers are not like regular businesses. They gather, combine, and study data from a lot of different places. This includes information about public records, finances, and risk assessments. When this kind of organization has a breach, it raises concerns that go beyond just one customer database.
Businesses use LexisNexis data services to check identities, stop fraud, and make sure they are following the rules. This is why the data breach is important. If any of that information gets out, it could cause problems in other fields as well.
It's important to remember that no official source has said that large-scale identity theft has happened as a direct result. If this kind of abuse were proven, regulators would probably give more advice. It looks like investigations are still going on for now.
What kind of data might have been made public?
Public reports show that some internal files were accessed and leaked. But full lists of the exact data categories have not yet been made public.
When data brokers are involved, the information that is leaked can include personal identifiers, contact information, and analytical datasets. We are still looking into whether that applies fully in this case. Readers should only trust official news and not rumors that are spread online.
When there is a LexisNexis data breach, it is very important to know what types of data are involved. Companies usually let people know if they have to under breach notification laws.
A Timeline of Events
According to reports from the public:
Activity that looks suspicious has been found.
An investigation has begun.
Confirmed unauthorized access
Files that were stolen were seen online.
Issued a public confirmation
There are still some technical details that haven't been made public. This happens a lot in active investigations because giving out too much information too soon can mess up forensic analysis.
The company has said it is working to figure out how big the problem is and how to lessen its effects. Some questions may not be answered until the forensic investigation is over.
How Data Exfiltration Usually Happens
To get a better idea of the big picture, it's helpful to explain what data exfiltration is. Phishing, stolen credentials, or taking advantage of weaknesses are common ways for attackers to get in. Once they get in, they move across systems to find valuable information.
Attackers can compress and export large datasets if encryption tools or endpoint monitoring don't catch unusual file transfers. You might find those files later on dark web forums or leak sites.
Leaked files from the LexisNexis data breach show that data was stolen. The exact way of getting in has not been made public.
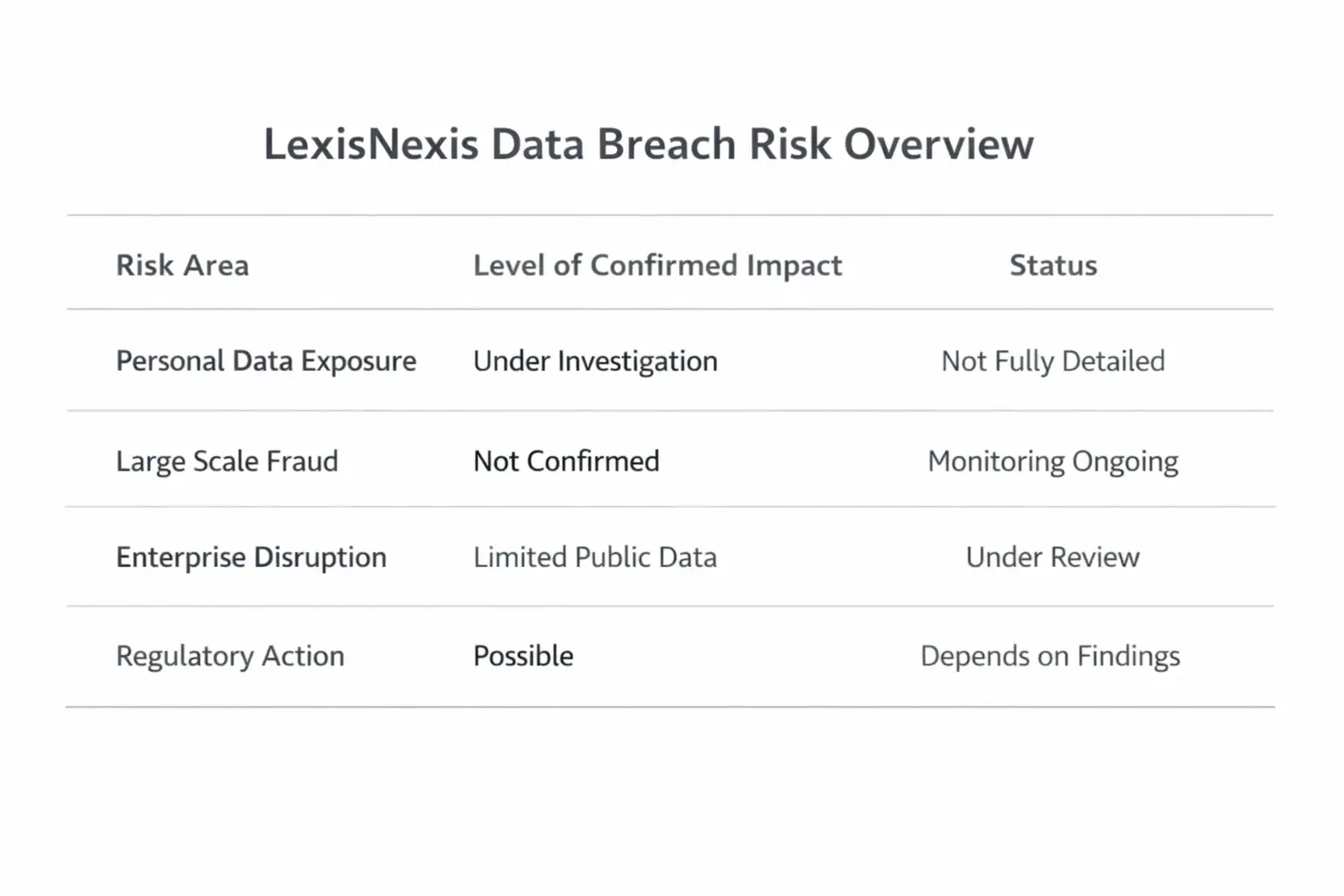
Effect on Businesses and Customers
Indirect exposure is the biggest worry for businesses that depend on LexisNexis services. If analytical or risk datasets were hacked, it could change how companies look at identity or compliance risk.
The worry for consumers is that their personal data could be used in the wrong way. That could mean trying to steal your information through phishing. No one has officially reported a large-scale fraud campaign that is directly linked to this event yet.
The LexisNexis data breach, on the other hand, shows how connected the data economy has become. One breach can have effects in many different fields.
A Real-Life Example of Data Broker Risk
A few years ago, another big data aggregator had a breach that let millions of records get out. Afterward, there were regulatory fines, class action lawsuits, and damage to the company's reputation that would last for a long time.
This example is important because data brokers keep a lot of information together. Even if one record isn't very sensitive on its own, when you put a lot of them together, you can make detailed profiles. That's why any LexisNexis data breach is so worrisome.
What Users Should Do Now
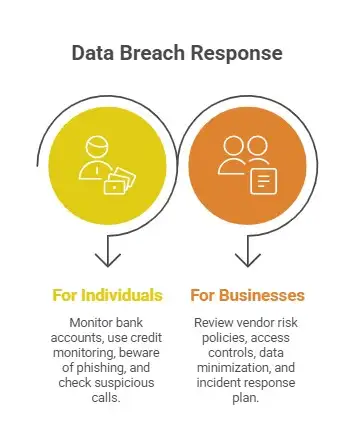
If You Are a Person:
• Keep an eye on your bank accounts.
• Think about using credit monitoring services.
• Be careful with phishing emails.
• Check out calls that seem suspicious and claim to be about leaked data.
If You Work for a Business:
• Look over the policies for managing vendor risk.
• Look over the access controls for third parties again.
• Make sure that data minimization is being used.
• Make sure your plan for responding to incidents is up to date.
The LexisNexis data breach is a reminder that vendor risk is real and never ends.
Lessons in Vendor Risk and Enterprise Response
Companies often put a lot of effort into protecting their own systems but forget about third-party exposure. Not just yearly audits, but also ongoing monitoring is needed for vendor risk management.
The LexisNexis data breach shows how important it is to review supply chain security. Companies should check with their partners to make sure they are following the right encryption standards, access logging, and breach notification procedures.
A good vendor contract should clearly spell out the responsibilities for protecting data and the time frames for responding to incidents.
Questions that are often asked
What went wrong with the LexisNexis data breach?
Someone got into the system without permission and stole files that were then made public. The investigation is still going on to find out how big it is.
Was private information that was sensitive made public?
Not all of the details about certain categories have been made public. If this is true, the people who are affected are usually told according to the law.
Is this breach connected to ransomware?
Public statements have not confirmed that ransomware was involved. No one has officially named a specific family of malware.
What can businesses do to lower the risk of vendor breaches?
Regular security checks, limiting the amount of data collected, having controls in place in contracts, and being ready to respond to incidents are all very important.
The Hoplon Insight Box
Useful Suggestions:
Do risk assessments of third parties every three months.
Make sure that strict least privilege access rules are followed.
Set up log monitoring that happens all the time.
Check twice a year to see if you are ready to respond to an incident.
Set up clear ways to talk about breaches.
These steps lessen the effects, even when incidents happen outside of your company.
Last Thoughts on the LexisNexis Data Breach
The LexisNexis data breach shows that collecting data gives you power and responsibility. When big data brokers have security problems, the effects go beyond just one business.
At this point, the only confirmed facts are that there was unauthorized access and files were leaked. There is no official record of widespread confirmed exploitation If additional evidence comes to light during the investigations, that might alter.
For now, the best thing to do is keep calm and wait. Check for updates, verify information using trustworthy sources, and make vendor risk management better. The tale isn't over yet, and it's better to behave appropriately than to guess.
People will undoubtedly keep an eye on the LexisNexis data leak until the investigations are over. Now is a good time for both organizations and people to review their plans for protecting their data and make sure they are ready for any difficulties that may come up in the future.
For more latest updates like this, visit our homepage.
Was this article helpful?
React to this post and see the live totals.
Share this :