macOS and iOS Vulnerabilities Exploited in Attacks

Hoplon InfoSec
09 Mar, 2026
The phrase macOS and iOS vulnerabilities exploited in attacks refers to a set of Apple security flaws that have been confirmed as actively abused by threat actors. The Cybersecurity and Infrastructure Security Agency (CISA) recently warned that several vulnerabilities affecting Apple operating systems are already being used in real-world attacks.
These issues affect multiple Apple platforms including macOS, iOS, iPadOS, Safari, and other components across the Apple ecosystem.
The warning matters for a simple reason. When a vulnerability is added to CISA’s Known Exploited Vulnerabilities catalog, it means security teams have confirmed that attackers are already using it. This moves the issue from theoretical risk to real operational threat.
Organizations, government networks, and everyday Apple users are therefore being urged to apply security updates immediately.

Apple Security Alert Impact
Security teams once treated Apple ecosystems as relatively insulated compared with other platforms.
That assumption is gradually shifting.
The old way of managing Apple device security often relied on periodic updates and general antivirus protection. Many organizations assumed the threat landscape was smaller.
The new reality looks different. Vulnerabilities affecting Apple devices are increasingly discovered and quickly weaponized by attackers.
The result is clear. Organizations must monitor Apple security advisories with the same urgency they apply to other platforms.
When vulnerabilities move into the “exploited in the wild” category, patching becomes a time-critical task rather than routine maintenance.
This is precisely why the warning about macOS and iOS vulnerabilities exploited in attacks has drawn attention across the cybersecurity community.
What Exactly Did CISA Warn About?
CISA warned that several Apple vulnerabilities affecting macOS, iOS, and other Apple platforms are actively exploited by attackers. The flaws involve memory management errors and integer overflow issues that can allow malicious code execution or elevated system access.
Detailed Explanation
CISA added three Apple vulnerabilities to its Known Exploited Vulnerabilities catalog, a public list used by security teams to track flaws that attackers are actively abusing.
Once vulnerabilities appear in this catalog, organizations are expected to treat them as urgent patching priorities.
The identified vulnerabilities affect several Apple technologies including:
macOS operating systems
iOS devices such as iPhones
iPadOS devices
Safari web browser
Apple TV operating system
watchOS components
This broad scope means the issue is not confined to a single Apple product line. Instead, it touches multiple layers of the Apple ecosystem.
In practical terms, this expands the attack surface significantly.
Apple Vulnerabilities Explained
The vulnerabilities linked to macOS and iOS vulnerabilities exploited in attacks fall into two technical categories.
These categories are well known in software security and often appear in serious exploitation cases.
Use-After-Free Memory Vulnerabilities
Two of the vulnerabilities belong to a class called Use-After-Free.
Security professionals categorize these under CWE-416.
In simple terms, this happens when software continues to use a piece of memory after it has already been released or reassigned. The pointer remains active even though the memory location is no longer safe to access.
Attackers can manipulate this condition to introduce malicious instructions.
If the exploitation succeeds, the system may begin executing code supplied by the attacker rather than legitimate software operations.
This type of flaw is especially dangerous because it can lead to memory corruption and unpredictable behavior across the operating system.
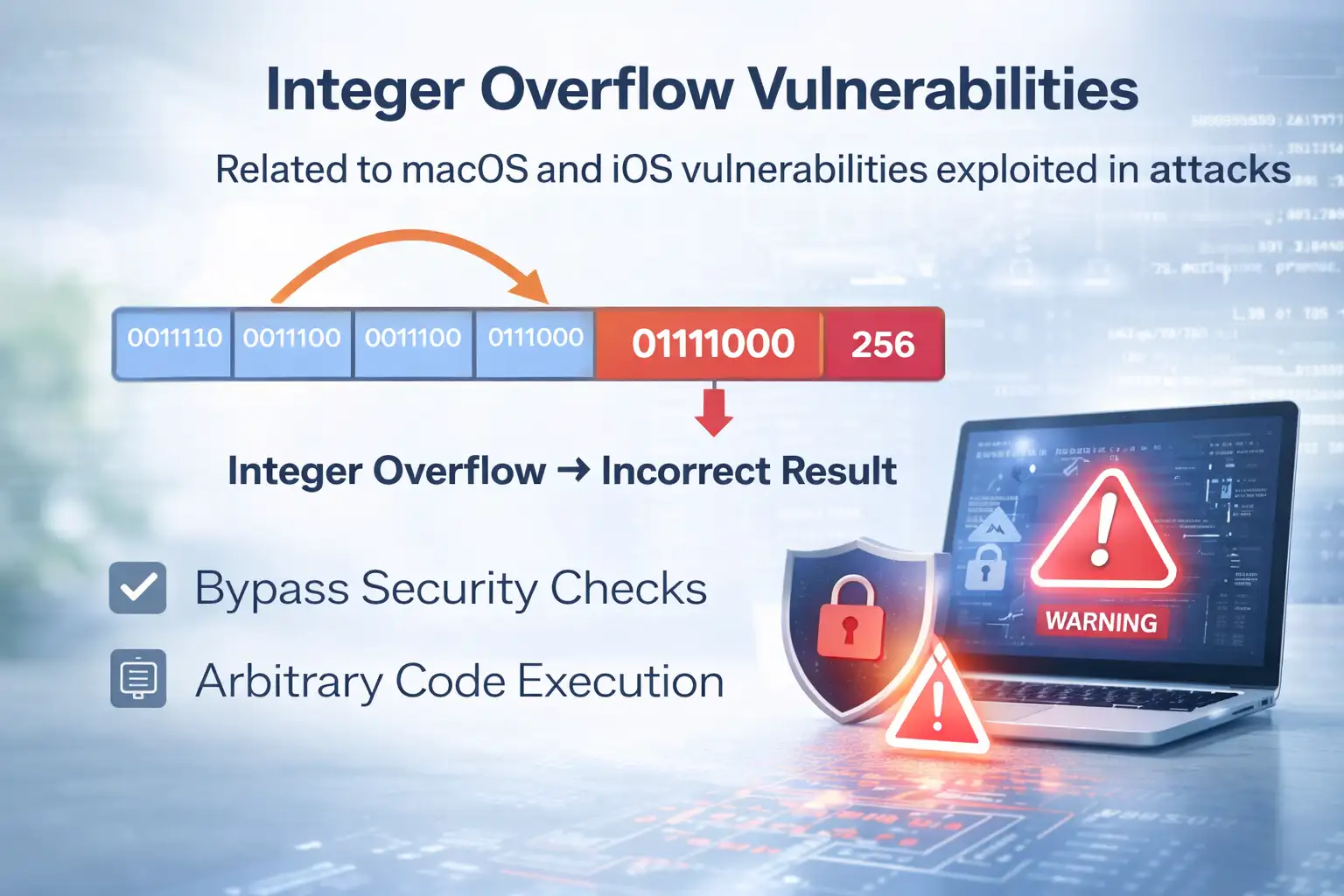
Integer Overflow Vulnerabilities
Another vulnerability connected to the macOS and iOS vulnerabilities exploited in attacks warning involves integer overflow, categorized as CWE-190.
This occurs when a calculation generates a number larger than the system can store in the assigned memory space.
When that limit is exceeded, the value “wraps around” and creates incorrect results.
In secure systems this should be prevented through input validation and memory controls. However, when protections fail, attackers can use the overflow condition to bypass security checks or alter system logic.
In certain situations this enables arbitrary code execution, which allows attackers to run their own software instructions inside the target system.
Key CVE Vulnerabilities
The advisory references three vulnerabilities that are part of the macOS and iOS vulnerabilities exploited in attacks situation.
Each vulnerability has a different scope and risk profile.
CVE-2023-43000
This vulnerability affects several Apple platforms including:
macOS
iOS
iPadOS
Safari version 16.6
The vulnerability involves a Use-After-Free memory condition.
When exploited, it may lead to memory corruption. Memory corruption often becomes the foundation for further exploitation techniques.
In real attack scenarios, memory corruption can allow attackers to manipulate program execution flow.
CVE-2023-41974
This vulnerability impacts:
iOS
iPadOS
The risk associated with this flaw is particularly serious.
If exploited successfully, a malicious application could execute code with kernel-level privileges.
Kernel privileges represent the deepest level of system access within an operating system. Once an attacker reaches that level, they may gain control over system processes, hardware communication, and security enforcement layers.
CVE-2021-30952
This vulnerability affects a broader set of Apple products, including:
tvOS
macOS
Safari
iPadOS
watchOS
The vulnerability involves integer overflow conditions.
Successful exploitation may allow attackers to execute arbitrary code.
From a security perspective, arbitrary code execution is often the turning point in an attack chain because it allows threat actors to run their own payloads on a compromised device.
How Attackers Trigger
Attackers exploit these vulnerabilities by tricking users into interacting with malicious web content or software. Specially crafted data can trigger memory errors or arithmetic faults that allow malicious code to run.
Detailed Explanation
The attack scenario typically begins with user interaction.
A victim may encounter malicious web content designed to trigger the vulnerability inside the browser or operating system component.
This content could be delivered through:
compromised websites
malicious advertising networks
phishing links
manipulated application packages
Once the vulnerable component processes the malicious data, the memory error or overflow condition activates.
At that point the attacker can attempt to inject code into the running process.
If the exploit chain succeeds, the attacker may gain elevated access or control over parts of the system.

Business Risk Explained
Many organizations now rely heavily on Apple devices.
MacBooks are widely used in development teams. iPhones are standard issue in many enterprise environments. Tablets often support field operations and executive workflows.
The presence of macOS and iOS vulnerabilities exploited in attacks therefore creates real operational risk.
Attackers may attempt to:
access corporate data
capture authentication credentials
deploy surveillance tools
pivot deeper into corporate networks
A compromised device can sometimes become the initial entry point for broader network attacks.
Security teams therefore treat exploited vulnerabilities as urgent patching priorities.
Government Response & Deadline
CISA operates under a policy framework known as Binding Operational Directive 22-01.
This directive requires federal civilian agencies to remediate vulnerabilities listed in the Known Exploited Vulnerabilities catalog within a specific timeframe.
For the Apple vulnerabilities recently added, agencies were instructed to secure their networks before the established remediation deadline.
While this requirement applies directly to government systems, the guidance extends far beyond federal infrastructure.
CISA explicitly encourages private sector organizations to treat these vulnerabilities with the same urgency.
From a risk management perspective, organizations that delay patching increase the likelihood of exploitation.
Patch Impact Scenario
Imagine a corporate employee browsing the web on a company-issued MacBook.
Before patching, the system still contains one of the vulnerabilities associated with macOS and iOS vulnerabilities exploited in attacks.
The employee clicks a link that leads to a malicious page. The page contains specially crafted content designed to trigger the memory vulnerability.
Within seconds, the attacker’s exploit runs.
Now compare that scenario with a patched system.
The operating system update fixes the vulnerable code path. The malicious content is processed safely, and the exploit fails.
The difference between those two outcomes often comes down to one simple factor. Timely updates.
Affected Users
The impact of macOS and iOS vulnerabilities exploited in attacks varies depending on the type of user.
Individual Apple Users
Everyday iPhone and Mac users could be exposed if their devices run vulnerable software versions.
Most attacks rely on interaction with malicious content. That means users browsing the web or installing apps may encounter exploitation attempts.
Keeping devices updated dramatically reduces this risk.
Businesses and Enterprise Environments
Organizations that manage hundreds or thousands of Apple devices face greater complexity.
Enterprise IT teams must ensure that:
patches deploy quickly
vulnerable devices are identified
endpoint monitoring is active
A delay in patch deployment can leave corporate networks exposed.
Government Infrastructure
Government networks follow strict remediation timelines under federal directives.
The presence of vulnerabilities in the KEV catalog triggers mandatory mitigation actions.
Apple Security Update Impact
Security updates remain the most effective defense against macOS and iOS vulnerabilities exploited in attacks.
Benefits
Timely patching closes the vulnerable code path before attackers can use it.
In most cases, Apple security updates address the flaw at the operating system level. Once installed, the exploit condition no longer exists.
This drastically reduces the attack surface.
Limitations
Patching alone does not eliminate all risk.
Several factors can delay remediation:
large device fleets
remote employees
unmanaged personal devices
Organizations must therefore combine patching with monitoring, endpoint detection, and security awareness programs.
Urgent Security Steps
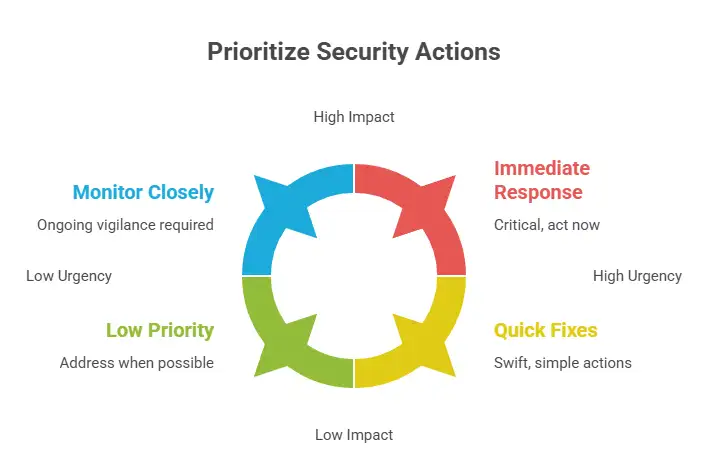
Security teams should treat the presence of macOS and iOS vulnerabilities exploited in attacks as a priority incident response task.
Key actions include:
Apply all Apple security updates following official vendor guidance
Identify devices running vulnerable versions
Monitor endpoints for suspicious behavior
Remove unsupported software versions when mitigation is unavailable
Organizations that cannot deploy patches quickly may need to restrict access to vulnerable systems temporarily.
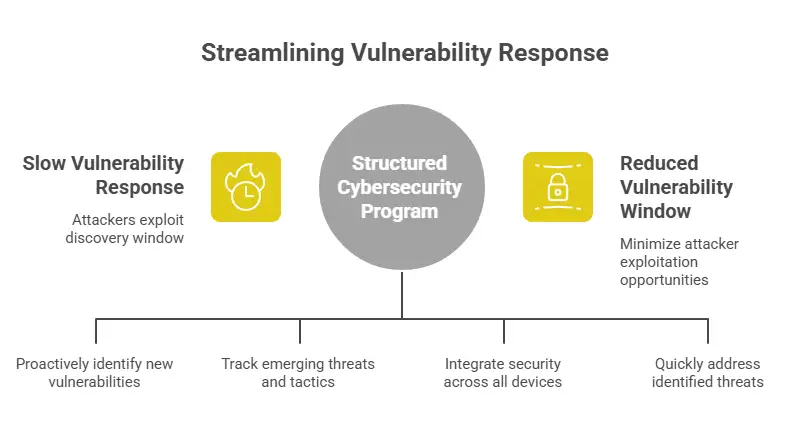
Apple Security Strategy
Security leaders often struggle with the speed required to respond to newly exploited vulnerabilities.
This is where a structured cybersecurity program becomes essential.
Hoplon Infosec works with organizations to strengthen vulnerability management practices, particularly in environments where multiple operating systems coexist.
Rather than focusing only on reactive patching, effective security programs combine:
continuous vulnerability monitoring
threat intelligence tracking
endpoint protection integration
rapid incident response
The goal is simple. Reduce the window between vulnerability discovery and mitigation.
In practice, that window is often where attackers succeed.
Frequently Asked Questions
What does it mean when vulnerabilities are “exploited in the wild”?
It means security researchers or government agencies have confirmed that attackers are actively using the vulnerability in real attacks.
Which Apple systems are affected by the vulnerabilities?
The vulnerabilities affect macOS, iOS, iPadOS, Safari, tvOS, and watchOS components depending on the specific CVE.
Can attackers gain full control of a device?
Some vulnerabilities may allow arbitrary code execution or kernel-level privileges, which could lead to deep system access.
Are these vulnerabilities linked to ransomware attacks?
According to available reports, there is currently no confirmed evidence linking these specific vulnerabilities to ransomware campaigns.
How can users protect themselves?
The most effective step is installing the latest Apple security updates and avoiding suspicious web content or untrusted applications.
Summary
The discovery of macOS and iOS vulnerabilities exploited in attacks highlights an important shift in the cybersecurity landscape.
Apple ecosystems are increasingly targeted. Once vulnerabilities appear in CISA’s Known Exploited Vulnerabilities catalog, they move from theoretical risk to confirmed threat.
Organizations that respond quickly reduce exposure significantly.
The broader lesson is simple. Security today requires continuous monitoring, rapid patch deployment, and structured vulnerability management.
Companies working with experienced security partners such as Hoplon Infosec can build programs that detect and mitigate these threats faster.
And in cybersecurity, speed often makes the difference between prevention and breach.
Trusted References
CISA Known Exploited Vulnerabilities Catalog
For more latest updates like this, visit our homepage.
Was this article helpful?
React to this post and see the live totals.
Share this :