Managed Endpoint Security Services Explained for Modern Enterprises
Hoplon InfoSec
08 Feb, 2026
Are managed endpoint security services still enough to protect modern businesses in 2026?
Managed endpoint security services are no longer a “nice to have” IT add-on. They have become one of the most critical layers of defense for organizations that rely on laptops, phones, cloud workloads, and remote access to function daily. The problem is not whether endpoint security matters. The problem is whether internal teams can realistically manage it alone.
According to CISA and NIST publications, endpoints remain one of the most common initial access points in confirmed cyber incidents, especially through phishing, stolen credentials, and unpatched devices. That reality explains why more companies are moving endpoint protection into managed, continuously monitored environments rather than handling it piecemeal.
What managed endpoint security services actually mean today
Managed endpoint security services refer to the continuous monitoring, protection, and response of devices by a specialized external security team. These services go beyond installing antivirus software or pushing updates. They include threat detection, behavioral analysis, incident response, and compliance reporting, all handled remotely.
In practical terms, this means a business hands over the day-to-day responsibility of endpoint defense to a managed security service provider. The provider uses a combination of endpoint detection and response tools, security analysts, and predefined playbooks to catch threats early.
What many articles miss is that modern endpoints are no longer just laptops. They include mobile devices, cloud-hosted virtual machines, point-of-sale systems, and even developer endpoints accessing sensitive code repositories. Managing all of that internally is difficult even for mature IT teams.
Why endpoint threats keep slipping past internal teams

Most breaches do not happen because companies ignore security. They happen because security teams are stretched thin.
Endpoints are noisy. They generate alerts constantly. False positives, software updates, user behavior anomalies, and legitimate admin activity all look suspicious at first glance. Internal teams often lack the time to investigate each alert deeply.
IBM’s Cost of a Data Breach Report consistently shows that detection and containment speed has a direct impact on breach cost. Delays of even a few days increase financial and operational damage significantly. This is one of the strongest arguments for managed endpoint security services, because response time matters more than tools alone.
How managed endpoint security services work in real life
The process usually starts with visibility. Every endpoint is enrolled into a centralized platform that tracks device health, user activity, and threat signals. This is not surveillance. It is pattern recognition.
Once visibility is established, behavioral monitoring takes over. Instead of relying only on signatures, the system looks for unusual activity such as credential dumping attempts, suspicious PowerShell usage, or unauthorized remote access sessions.
When something looks wrong, the managed team steps in. They validate the alert, isolate the affected endpoint if necessary, and guide remediation. In many cases, the end user never even realizes a threat was stopped.
This human-in-the-loop model is what separates managed endpoint security services from basic endpoint software.
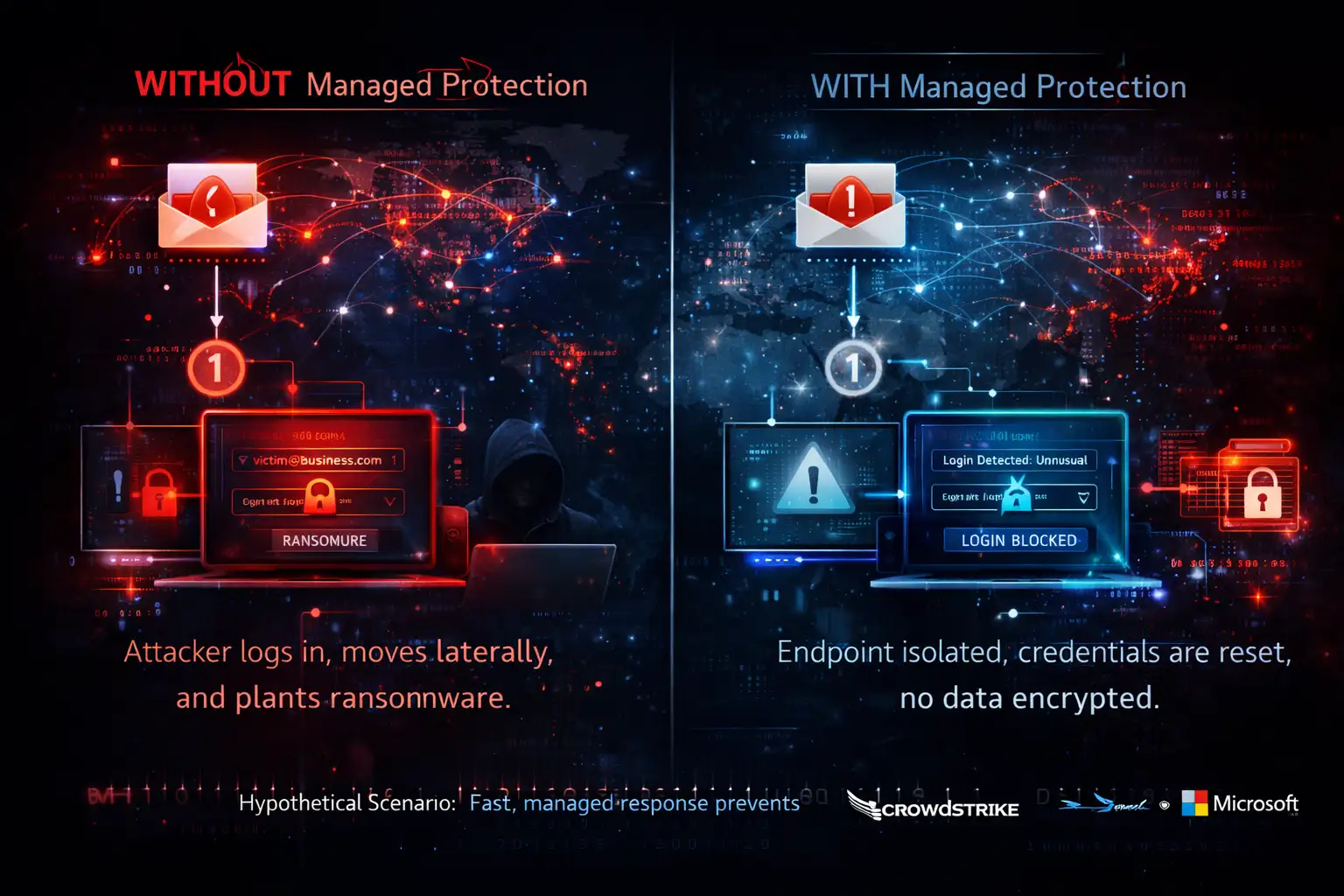
A realistic example most businesses recognize
Consider a mid-sized marketing firm with remote employees across three countries. One employee receives a phishing email that looks like a shared document request. They click it. Credentials are harvested.
Without managed protection, the attacker logs in, moves laterally, and plants ransomware overnight.
With managed endpoint security services in place, the unusual login behavior is flagged within minutes. The endpoint is isolated. Credentials are reset. No data is encrypted. No headline is written.
This scenario is not hypothetical. Variations of it appear repeatedly in incident response case studies published by CrowdStrike and Microsoft. What changes the outcome is speed and expertise.
The impact on businesses beyond security alone
One overlooked benefit of managed endpoint security services is operational clarity. IT teams regain time. They stop chasing alerts and start focusing on strategic improvements.
Finance teams gain predictability. Security costs become operational expenses rather than emergency breach spending. Leadership gains clearer reporting on risk posture and compliance status.
There is also a cultural shift. Employees become less afraid of making mistakes because incidents are handled calmly and professionally. That matters more than most executives realize.
Where many providers fall short
Not all managed endpoint security services are equal. Some providers oversell automation and underdeliver on human analysis. Others flood clients with reports that look impressive but offer little actionable insight.
Gartner repeatedly warns organizations to evaluate managed security providers based on response capability, not tool count. A dashboard does not stop an attack. People do.
The future of managed endpoint security services
The future is already forming around three ideas.
First is identity-centric security. Endpoints are no longer trusted by default. Every action is verified, aligning closely with zero trust models described by NIST.
Second is tighter integration with cloud and SaaS platforms. Endpoints do not exist in isolation anymore, and security providers must understand application behavior as well as device behavior.
Third is transparency. Buyers are demanding clearer explanations, not buzzwords. Providers who cannot explain what they do in plain language will lose trust.
Based on current industry reporting, these trends are confirmed, although exact timelines vary by region and industry.
What businesses should realistically do next
If you are evaluating managed endpoint security services, start by asking simple questions.
Who responds when an alert fires at 3 a.m.?
How fast is isolation performed?
What happens after containment?
How is success measured?
Avoid vendors who promise perfection. No system is perfect. Look for honesty, clear processes, and documented response procedures.
Hoplon Insight Box
At Hoplon Infosec, the focus is not on tools alone but on outcomes. Their approach to managed endpoint security services emphasizes clear response playbooks, continuous monitoring, and real human analysis. This helps organizations reduce dwell time and regain control over endpoint risk without overwhelming internal teams.
Frequently Asked Questions
What are managed endpoint security services?
They are services that use both technology and people to keep an eye on, find, and deal with threats on laptops, servers, and mobile devices.
Are managed endpoint security services suitable for small businesses?
Yes. In fact, smaller teams often benefit the most because they lack dedicated security staff.
Do managed endpoint services replace internal IT teams?
No. While the rest of the staff works on operations, they help IT teams by keeping an eye on security.
How quickly do managed providers respond to threats?
Response times vary by provider. Reputable services publish response SLAs and escalation processes.
Final takeaway
Managed endpoint security services are not about fear or compliance theater. They are about realism. Endpoints are messy, humans make mistakes, and attackers move fast. Businesses that accept this reality and plan accordingly tend to recover faster and suffer less damage.
The real question is not whether you need managed protection. It is whether you are prepared to handle endpoint threats alone.
Was this article helpful?
React to this post and see the live totals.
Share this :