Stryker Cyber Attack: Hackers Claim System Breach and Device Wipe
Hoplon InfoSec
13 Mar, 2026
Was there really a Stryker cyber attack?
A lot of people are asking the same thing right now: Did hackers really attack Stryker and erase systems?
There are reports online that say a Stryker cyber attack may have exposed internal systems and that hackers tried to wipe devices that were connected to the network. The information was posted on forums and security monitoring sites that deal with cybercrime. At the time of writing, though, Stryker and regulatory bodies have not officially confirmed the full extent of the alleged incident.
The story is important because Stryker is one of the biggest medical tech companies in the world. People in dozens of countries use its products in hospitals, surgical centers, and emergency rooms. Any possible breach of healthcare systems raises concerns about patient safety, the security of medical devices, and the increasing risk of cyber attacks on healthcare infrastructure.
Cybersecurity monitoring sites say that hackers said they had gotten into internal systems and threatened to make data public. But security researchers have also said that claims made on underground forums should be taken with a grain of salt until they are proven.
Why the Claim About the Stryker Cyber Attack Is Getting Attention
Cybersecurity problems in healthcare often cause immediate worry because hospitals depend on connected devices. A possible Stryker cyber attack could affect not only business networks but also medical equipment used during surgeries and to keep an eye on patients.
There are thousands of connected systems in modern healthcare settings. Some of these are imaging machines, surgical navigation platforms, implant management databases, and software for remote monitoring. A lot of these tools connect to hospital networks, which makes them easy targets for cybercriminals.
If hackers say they've broken into a major healthcare technology provider, the possible effects could be huge. Hospitals that depend on those systems need to quickly check to see if their networks or devices are at risk.
Cybersecurity researchers often find that healthcare organizations are among the most targeted sectors in the world. It's not easy for hospitals to stop working, which makes them vulnerable to ransomware attacks and data extortion campaigns.
What Hackers Said About the Stryker Systems
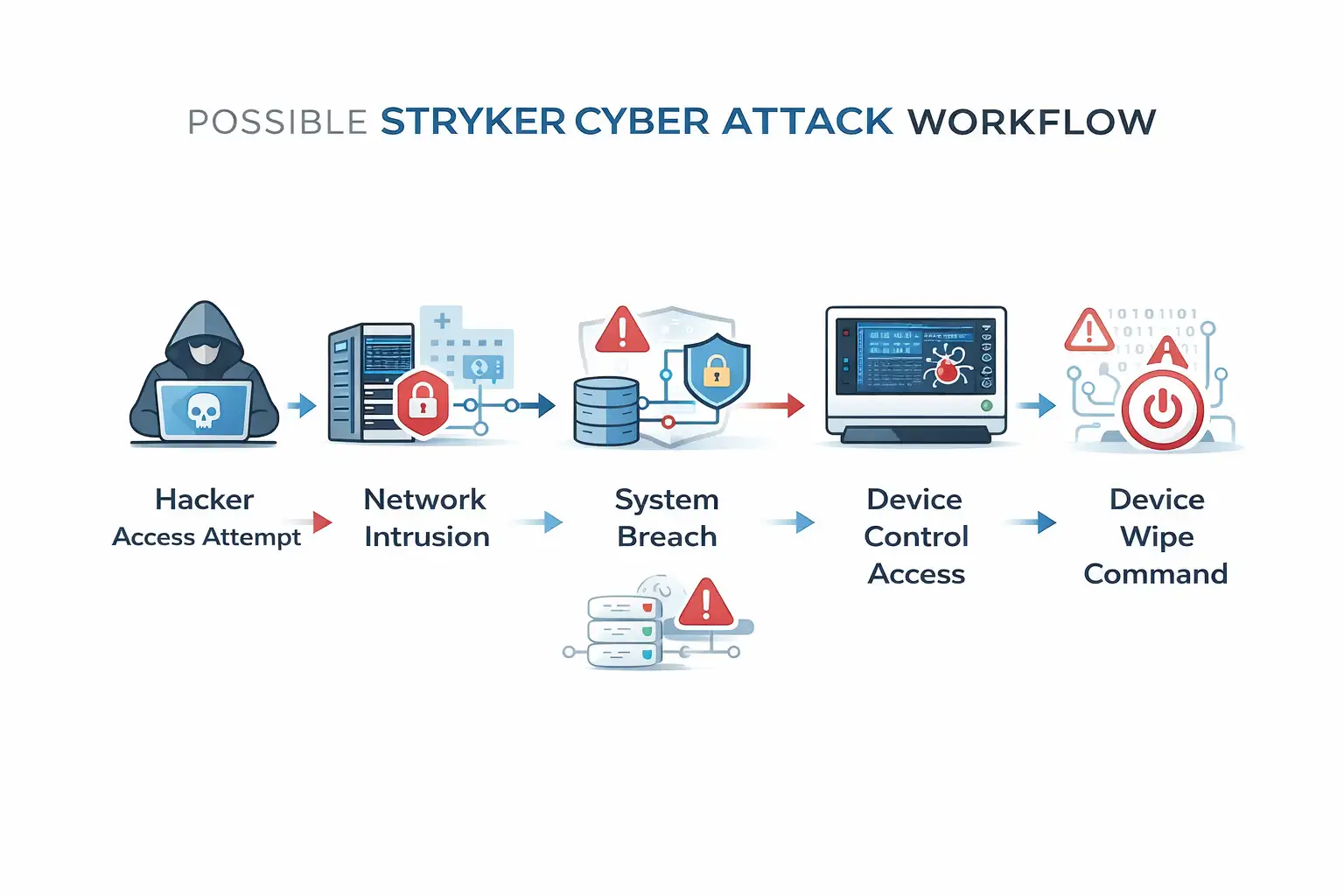
Early reports on cybercrime monitoring sites say that the people who are said to have attacked Stryker claimed they had gotten into internal infrastructure that was connected to Stryker's environment.
According to reports, the people behind the threat said they could get into some internal systems and erase devices that were connected to the network. Hackers often make these kinds of claims on underground forums to try to get companies to negotiate or to get attention for what they're doing.
Cybersecurity experts, on the other hand, say that these claims are often overblown. Some attackers post partial information or screenshots that don't always show that the whole system has been compromised.
At the time of publication, there is no public technical evidence that medical devices were affected. There is no public record of any confirmed vulnerabilities or exploit chains related to the alleged Stryker cyber attack.
How Healthcare Companies Get Targeted
Over the past ten years, cyber criminals have targeted the healthcare industry more than any other. The reasons are pretty clear.
First, healthcare systems keep very important information. Medical records have private information, insurance information, and private health history. This information is worth a lot of money on the black market.
Second, hospitals are always under a lot of time pressure. When systems go down, patient care can be affected. That sense of urgency makes organizations sometimes have to act quickly when ransomware asks for money.
Third, a lot of healthcare settings still use old systems. Some devices keep working for years and aren't always easy to update. That leaves holes in security coverage.
Because Stryker makes medical equipment that is used all over the world, any report of a Stryker cyber attack gets a lot of attention from security researchers, regulators, and healthcare providers right away.
Explaining the Risks of Medical Device Security
In modern healthcare, more and more medical devices are connected to the internet. Surgical navigation systems, orthopedic implants tracking platforms, and robotic surgery tools all need software and a network connection to work.
That connection makes patient care better in a lot of ways. Doctors can get real-time data, keep an eye on systems from afar, and do more complicated procedures with more accuracy.
But being connected also comes with new risks.
If hackers get into a network that has medical technology systems on it, they might try to change data, break software, or stop devices from working. That's why organizations like the FDA and international cybersecurity agencies now put a lot of stress on medical device security standards.
In the case of the alleged Stryker cyber attack, there is no evidence that implanted devices or surgical tools were damaged. Experts say that problems with corporate networks don't often lead to direct manipulation of devices.
The Part Ransomware Plays in Cyber Attacks on Healthcare
A lot of recent events involving healthcare companies have followed the same pattern. Hackers break into a network, steal private information, and then threaten to make it public unless they get paid.
People often call this model "double extortion." Even if systems are restored from backups, the victim organization can still be pressured with stolen information.
Attackers often go after healthcare organizations because they think hospitals will act quickly to avoid problems with their operations.
If the reported Stryker cyber attack included stealing data or using ransomware, investigators would probably look at a number of technical signs, such as:
• strange traffic on the network
• accounts for administrators that aren't authorized
• ways for malware to stay around
• data transfers that look suspicious
Right now, none of these facts have been confirmed by the public.
How Security Researchers Check Claims of Breaches
When hackers say they've broken into a system online, security researchers start to check it out.
They usually look at:
• files that got out
• pictures of internal systems
• claims of domain access
• dumps of credentials
Attackers sometimes make their access seem bigger than it really is. In other cases, they might only have a small amount of data that doesn't show a full system breach.
Cybersecurity experts have told people to be careful about the alleged Stryker cyber attack. The claims are still unproven until forensic evidence or official statements come out.
When it comes to cybersecurity, responsible reporting means telling the difference between confirmed incidents and unproven claims.
Possible Effects on Hospitals and Healthcare Providers
If a major healthcare technology provider were to be breached, hospitals would have to look at a number of risk areas.
First, they would look at how the network connects to the vendor's systems. Hospitals often use vendor software as part of their own systems.
Second, they would check to see if any credentials or access tokens related to vendor services had been made public.
Third, they would keep an eye on how the device works to look for problems. Medical equipment usually keeps track of operational events that can help find suspicious behavior.
Even rumors of a Stryker cyber attack can make healthcare organizations that use its products take extra steps to protect themselves.
In the healthcare field, this kind of response is normal for cybersecurity.
Why there are more cyber attacks on healthcare systems
In the last ten years, cyber attacks on healthcare systems have grown a lot. There are a few trends that explain this change.
Healthcare organizations are quickly moving their work online. Today, electronic health records, cloud platforms, and medical devices that are connected to the internet are all important parts of medicine.
A lot of hospitals, on the other hand, have very tight budgets and not enough staff to protect their computers. This can make it harder to find threats or keep an eye on systems.
Criminal organizations are aware of these problems. They often see healthcare networks as good places to steal data and extort money.
The growing interest in the supposed Stryker cyber attack shows a bigger truth. Now, medical technology companies are fighting on the global cybersecurity battlefield.

What Users and Hospitals Should Do
Security experts suggest taking a number of safety measures even if a cyber incident has not been confirmed.
Hospitals that use connected medical devices should keep their software and firmware up to date whenever they can. Vendors often put out security patches to fix holes in their software.
It's also important to segment your network. Medical equipment should work on separate network segments that are not connected to administrative systems.
Security teams should also keep an eye on authentication logs for any strange behavior. Unauthorized access attempts can be a sign that a breach has already happened.
Even though the alleged Stryker cyber attack has not been fully confirmed, these practices help lower risk in all healthcare settings.
Visual Data: Cyber Attacks on Healthcare
Cyber Incidents in Healthcare (Recent Years)
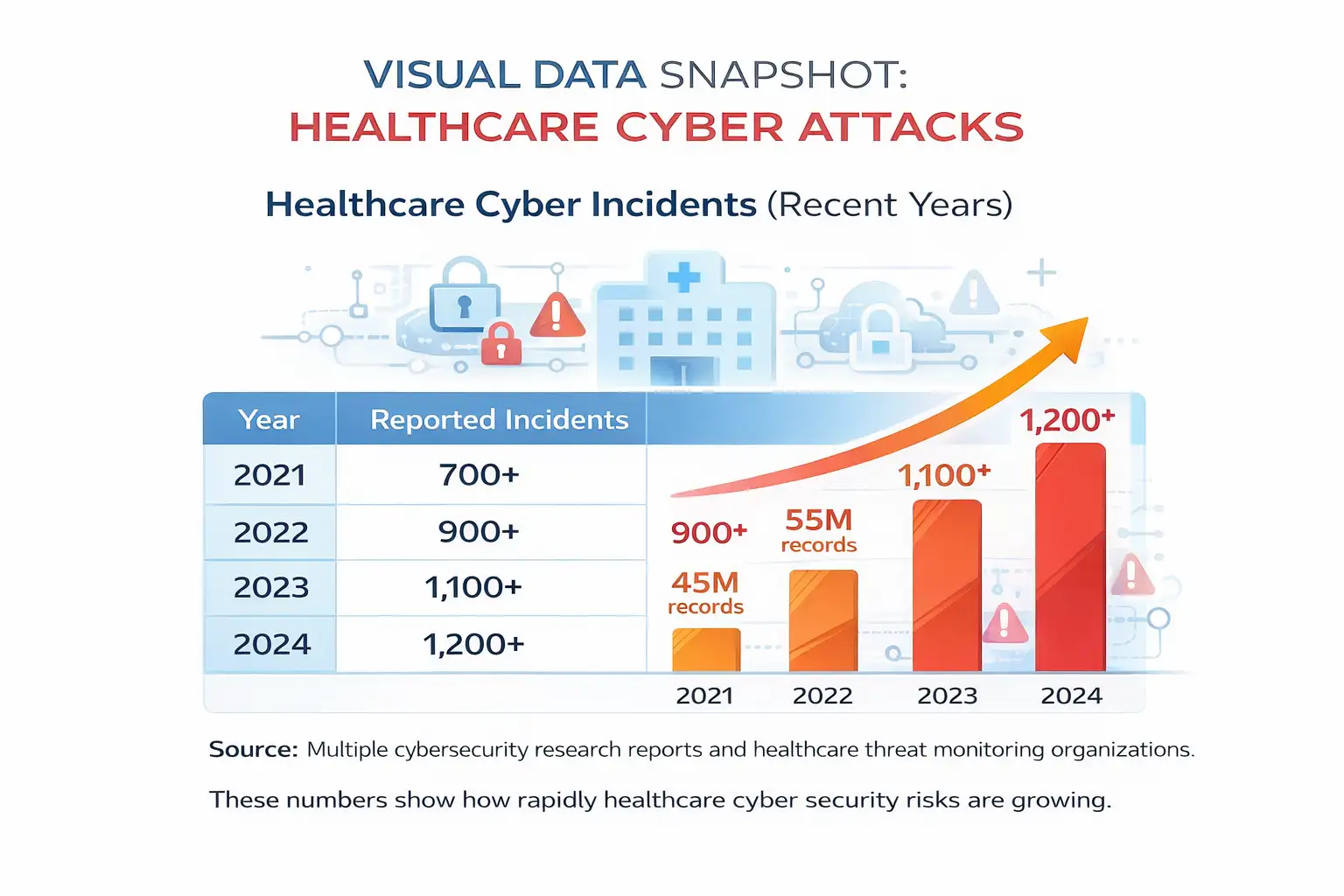
Source: A number of cybersecurity research reports and groups that keep an eye on healthcare threats.
These numbers show how quickly the risks to healthcare cybersecurity are growing.
Security researchers' expert point of view
A number of cybersecurity research groups have said that claims of public breaches should always be looked into carefully.
Security experts say that underground forums often have claims that are too big. Attackers might try to get attention or pressure businesses before talks start.
When there is a Stryker cyber attack, the most reliable information usually comes from official reports, regulatory filings, or confirmed forensic investigations.
Researchers don't consider early claims to be confirmed events until those sources provide proof.
People Also Ask: Did someone hack Stryker?
Some hackers said they got into Stryker's systems and deleted devices. But so far, there has been no public proof that a full breach has happened.
What does Stryker do?
Stryker is a global medical technology company that makes surgical tools, orthopedic implants, hospital beds, and other medical devices for use in healthcare settings.
Could a cyber attack hurt medical devices?
In theory, compromised networks could have an effect on systems that are connected to them. Most modern medical devices, on the other hand, have safety controls and separate environments that lower risk.
Why do hackers go after healthcare companies?
Healthcare organizations keep private patient information and run important systems that can't be turned off easily. This makes them easy targets for groups of cybercriminals.
Important Point
The news stories about the Stryker cyber attack show how vulnerable healthcare infrastructure has become in the digital age. Even a claim of a breach that hasn't been verified can cause problems for hospitals, security teams, and medical technology companies.
Right now, the most important thing is to double-check everything. Cybersecurity incidents should be assessed through evidence, not speculation.
Healthcare systems need to keep making security controls stronger, keeping an eye on networks, and working closely with vendors to lower the risks that could happen.
Cybersecurity will continue to be a major concern for hospitals, device makers, and regulators around the world as medical technology becomes more connected.
For more latest updates like this, visit our homepage.
Trusted Source
Cybersecurity News
Was this article helpful?
React to this post and see the live totals.
Share this :