TransUnion Hack Exposes 4M Customers: A Warning to Stay Protected

Hoplon InfoSec
29 Aug, 2025
TransUnion hack exposes 4 million customers
I remember getting the first alert. It was like getting a text from a friend who never lies. One of the Big Three credit reporting companies said that a vendor system connected to customer support had been hacked. Headlines moved quickly. The phrase “TransUnion hack exposes 4 million customers” started to show up everywhere, and for many people, it felt like it was about them. If a bureau that grades our lives like a report card can be hacked, what does that mean for the rest of us?
The story moved along quickly. Early reports to state regulators said that a third-party app was involved. It was a small relief in a week full of bad news that the reports made it clear that credit files were not accessed. Names, birth dates, and Social Security numbers are still the keys to many doors.
What happened in simple terms?
Let’s keep it simple. The weak link was a tool that helped U.S. customers. Attackers got in, stole personal information on millions of people, and set off mandatory alerts. The headline “TransUnion hack exposes 4 million customers” became the shorthand because that number is big enough to shock even those who aren’t interested.
It’s like having an extra key hidden under the doormat of a busy building. The door in front looks tough. Security guards pay attention. Someone, though, finds the key that was meant to be used only for maintenance. That’s how most modern breaches happen, and that’s why “vendor governance” is the word of the year.
Where the breach started and why a third party is important
The filings point to a third-party app that helped customers do business. Third-party doesn’t mean small or messy. It means that the software stack is made up of layers, and there is a trusted helper between the company and the customer. When that helper is hacked, the main brand suffers. Reports and filings make it clear that this helper app was the way in for the attack. This is exactly how the TransUnion hack that affected 4 million customers became a national news story.
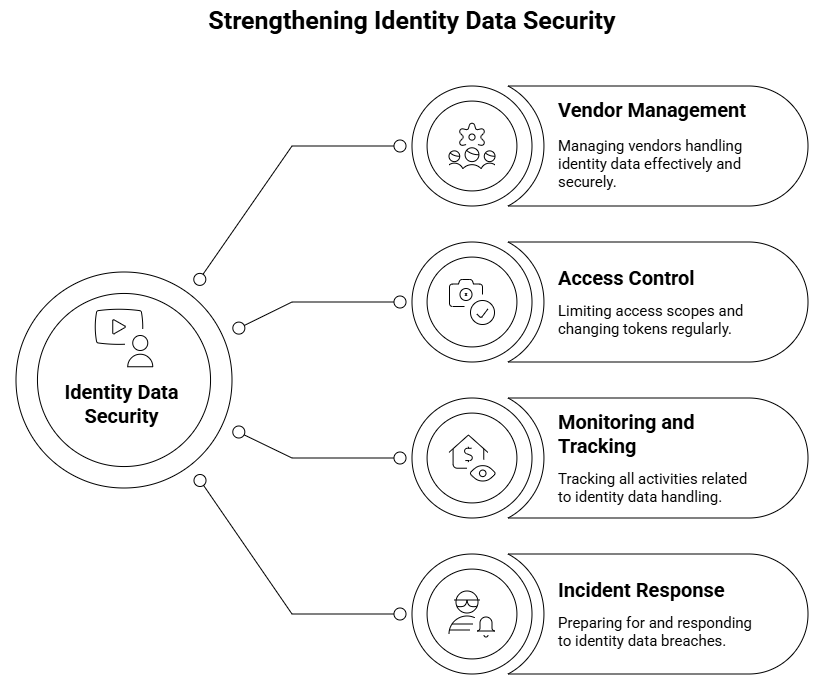
This is the hard part for security teams. You can lock up your own stuff. You can make rules. But you still need partners, and each one makes your attack surface bigger. Good contracts and audits can help, but they don’t get rid of the risk.
What information was made public and what wasn’t?
Reports from several sources say that the data set has names, birth dates, and Social Security numbers. That is enough for people to try to make fake identities, commit tax fraud, and take over accounts. TransUnion also says that credit information was not accessed, which makes the blast radius a little smaller. The line “TransUnion hack exposes 4 million customers” still gets across how serious it is because core identifiers are strong on their own.
If you’re wondering why criminals want Social Security numbers instead of credit files, think about how new accounts are opened. Those three things are what lenders need to get things going. With them, an attacker can push on the edges until something breaks.
Who is affected, and how to find out your status
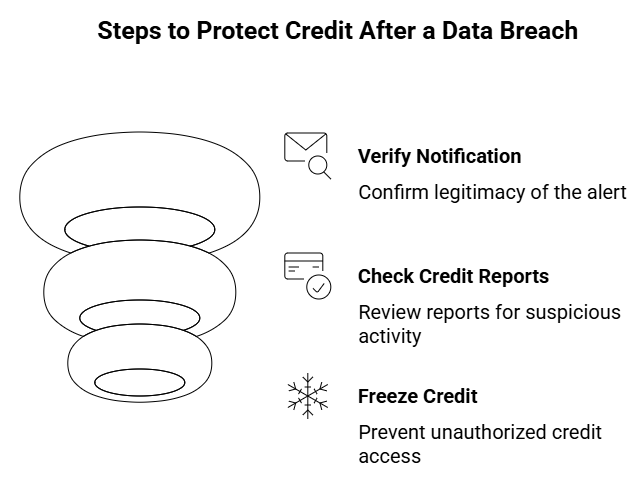
According to news wires and regulatory letters, the count is just over four million. You should get a formal notice if your information is in the set. Look for real letters about remediation in your mailbox and inbox. If the subject line says “TransUnion hack exposes 4 million customers and offers free monitoring,” don’t click right away. Check with official sources and your state’s attorney general’s list of breach notices to be sure.
You can also look at your credit reports from all three bureaus and put a free credit freeze on them if you see anything strange. A freeze stops new creditors from getting your file, which makes it harder for someone to open.
The short time between the event and the disclosure
The papers show that the event happened on July 28 and was found on July 30. That is a short time frame, which probably cut down on dwell time. Notifications came after the scope became clearer. Within days, the phrase “TransUnion hack exposes 4 million customers” showed up in major news outlets, which suggests that the company was working with regulators and the media to make the news public.
This is a matter of speed. Faster discovery usually means that fewer systems are affected and there are fewer chances for data to be staged and sold again. It also shows that the monitoring controls were able to quickly find something strange.
How attackers usually switch between vendor tools
When you connect service platforms, you give them permissions, tokens, and sometimes even full access to sensitive workflows. Attackers search for those tokens like they are gold. They can pretend to be trusted software if they get one. That’s how a phrase like “TransUnion hack exposes 4 million customers” goes from the tech world to the evening news. The mechanics are quiet, but the effect is loud.
Think of a valet who has a ring with keys to a lot of cars on it. If someone steals the ring, they don’t have to break into anything. They just walk to the lot and get in their cars.
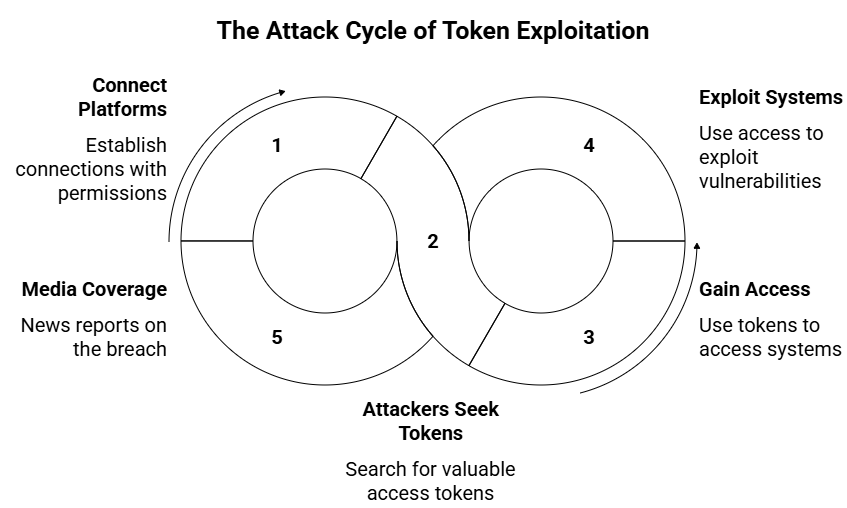
A possible connection to a bigger campaign
A lot of reports talk about a bigger campaign that has to do with cloud and CRM ecosystems. A group that is known has taken responsibility for it in other places. Attribution always takes time, but the pattern fits how criminals use one foothold to get to many high-value targets. This is one reason why the TransUnion hack that exposed 4 million customers kept getting attention. It seemed like a piece of a bigger picture instead of a one-time thing.
Investigators will keep looking into the links between these events. It’s easy for readers to get the point. Shared platforms are efficient, and that efficiency works both ways when attackers find a way in.
What TransUnion has said and done up to this point
The business says that the problem came from a third party and that credit files were not affected. It is letting people who are affected know and working with law enforcement and regulators. Newsrooms kept saying the same thing over and over again, but they also talked about how urgent it was that the TransUnion hack exposed 4 million customers because personal information is sensitive even without credit data. Over time, you should get more information. The root cause is not often mentioned in early statements. Mature incident response focuses first on containing the problem and getting the word out, and then on fixing it and making it stronger.
What lawyers and regulators are doing
The notices started showing up on attorney general portals. Class action lawyers are already looking into the facts and asking people who are affected to talk about their options. That’s a common rhythm in U.S. breach law. It also keeps the TransUnion hack that exposed 4 million customers in the news because legal filings keep the story going for more than a week.
Regulators will check to see if vendor management and access controls were good enough. They will also look at how clear and timely the notifications are. The result will affect how everyone deals with third-party risk next quarter.
Real risks to customers in the coming months
Attackers are patient. They usually wait until the noise stops. The phrase “TransUnion hack exposes 4 million customers” may not show up in your feed for long, but the data doesn’t lose value quickly. People who commit new account fraud, SIM swap fraud, and tax refund fraud are the most likely to do so. Keep an eye on all of them.
Setting calendar reminders to check your credit freeze status and multifactor authentication settings every three months is a good idea. Make it boring and normal. You win this game by being boring.
Things you can do right now to lower your risk
Start by freezing your credit at all three bureaus. If you need to keep limited access open for lending, think about setting up a fraud alert. If free monitoring is available, sign up for it, but don’t stop there. The number of breaches in the TransUnion hack that affects 4 million customers is not the only thing that matters. It is the fact that core identifiers are permanent. You can’t change your birthday. You can choose who can see your file.
To lower the risk of SIM swapping, update your password manager, change any credentials you use more than once, and lock down your carrier accounts with a PIN. Before tax season, check the status of your IRS account. If you don’t have one yet, make one online.
What businesses that deal with sensitive records can learn
This is a case study for businesses. Make a list of all the vendors that handle identity data. Limit scopes, change tokens, and keep track of everything. Assume that the most appealing target is a helper with a lot of support permissions. If the TransUnion hack that exposed 4 million customers can happen in a highly regulated environment, it can happen anywhere less controlled.
Do tabletop exercises that make it seem like an upstream vendor has been hacked. Make sure your legal and communications teams can keep up with your responders. The best incident is one that your customers hardly notice because you were ready for it.
How does this compare to other problems with credit bureaus?
People who have been in the business for a long time will remember past bureau events that lasted for a long time. Here, the filings stress that there is no access to the credit file, a smaller scope, and a short detection window. Even so, the phrase “TransUnion hack exposes 4 million customers” keeps the focus on the main harm. It’s not just about the numbers. It’s about what kind of data was exchanged.
Every event changes how lenders, insurers, and regulators think about risk. Each time, the standards for vendor oversight get a little higher.
FAQ 1: What information was stolen in the TransUnion hack?
Hackers got into this case and stole personal information like names, birth dates, and Social Security numbers. TransUnion said that credit files were not hacked, but these identifiers are still very sensitive because they can be used to steal someone’s identity and commit fraud.
FAQ 2: What can I do to keep myself safe now that the TransUnion hack has revealed the information of 4 million customers?
People who were affected should keep a close eye on their credit reports, put a free credit freeze on all three major bureaus, and turn on fraud alerts when they can. Adding another layer of protection is to set up multifactor authentication on your bank and mobile accounts and use a password manager.
FAQ 3: Will TransUnion help customers who have been affected?
Yes. TransUnion has told the people who were affected and is giving them free credit monitoring and identity protection services. If you get a notice, always check it out through official channels to avoid phishing scams that may use the breach as bait. 15) What to watch next and a calm path forward
What to watch next and a calm path forward
In the next few weeks, state and federal agencies will give you more technical information, longer lists of affected data fields, and more help. People will keep seeing the phrase “TransUnion hack exposes 4 million customers” in notices and summaries, but the real story will move on to fixing things and making them stronger.
If you were affected, do what you need to do today and set reminders to do it again later. If you weren’t, you might want to do the same. The internet brought us all together, and good habits in the neighborhood can make a difference.
After hacks like the one at TransUnion, stolen data often shows up on secret forums. Hoplon Infosec’s Deep and Dark Web Monitoring service keeps an eye on these threats in real time, which helps businesses find leaked information quickly and take action before criminals can use it.
Was this article helpful?
React to this post and see the live totals.
Share this :