Underground Ransomware Gangs Enter a New Era

Hoplon InfoSec
30 Aug, 2025
Underground ransomware gang new tactics
Don’t believe that ransomware is a threat from the past. An underground ransomware gang has surfaced in the past year with new strategies that make previous attacks appear nearly inexperienced. When odd patterns started to appear across multiple continents, security researchers initially became aware of them.
Files were no longer simply locked. The victims reported public humiliation, coordinated online harassment, and threats to release private information. It was a growing wave rather than a single instance. That was the clue that organized crime had changed.
Seeing the new tactics used by the underground ransomware gang is like watching a professional pickpocket turn into a full-fledged bank robber. Little, inconspicuous encroachments have developed into major disturbances. The rules of the game had changed, and organizations that had previously depended on conventional defenses suddenly found themselves in a tight spot.
Why These Gangs Continue to Modify Their Strategy
Every successful defense makes the attacker more intelligent. That is the cybersecurity cycle. Because adaptation is ingrained in their DNA, ransomware gangs thrive by adapting. Gangs began erasing shadow copies when businesses upgraded their backups. Gangs switched to fileless attacks as antivirus software improved. Layering multiple threats at once is the new tactic used by this underground ransomware gang.
They are motivated by more than just money. It’s rivalry among the criminal community. Victims stop paying if one group becomes predictable. Therefore, even if an innovation appears frightening to opposing defenders, the underground world rewards those who innovate.
Initial Contacts: How Security Teams Learned About the Change
Businesses in Asia and the Middle East reported the first confirmed incidents. Unusual activity was observed by security analysts: intrusions that started with credentials that were stolen and ended with quick encryption of vital servers. Not only was the encryption remarkable, but so was the accuracy. The most valuable systems were carefully chosen by the attackers rather than saturating the entire network.
One expert likened it to burglars who enter your home, pass through each room, and take only the jewelry box beneath your bed. Organizations realized this underground ransomware gang’s new tactics playbook was more strategic than brute force because of its accuracy.
Global Reach: From Regional Intruders to Worldwide Initiatives
Reports by the middle of 2025 indicated that the incidents had occurred from South Korea to the United Arab Emirates, with traces also found in North America and Europe. A local criminal syndicate was not responsible for this. It bore the marks of a well-run business with affiliates all over the world.
Greater risks are associated with global reach. A hospital in Germany and a small IT company in Dubai might not seem connected, but when the same ransomware notes show up, they do. This link indicates that the new tactics used by the underground ransomware gang are franchised, akin to a fast-food chain but specifically tailored to cybercrime.
The Ransomware Industry’s Hidden Economy
There is a market behind the attacks. Underground forums promote pre-made ransomware kits, tools, and stolen data. Groups even use “Ransomware-as-a-Service” to rent their malicious software. Affiliates sign up, launch attacks, and split the earnings with the developers. This economic system explains why gangs spread so quickly throughout the world.
The professionalism is new. These days, some forums provide criminals with customer support. Do you need to know how to get past a firewall? You have a coach waiting for you. This underground marketplace, where crime is traded like any other commodity, is a major component of the new tactics wave used by this underground ransomware gang.
New Strategies of the Underground Ransomware Gang: Technical Dissection
The attacks are technically a combination of new layers and old tricks. They frequently start with credentials that were stolen from the dark web or phishing emails. Once inside, attackers use commands like vssadmin delete shadows to disable recovery tools. Next is encryption using a combination of the RSA and AES algorithms.
However, sequencing is where the true innovation lies. Attackers map the network, locate crown-jewel assets, and exfiltrate data before locking everything at once. They start encryption only after that. The new strategy playbook of the underground ransomware gang focuses on maximizing leverage by simultaneously threatening exposure, stealing, and encrypting.
Deletion, Encryption, and Beyond: The Developing Toolkit
Encrypting files and deleting backups are outdated practices. These gangs add pressure points today. Some have begun attacking victims’ websites with DDoS attacks. Others send threatening emails to staff members’ inboxes. Hackers have even called people posing as insiders with evidence of stolen data in a few instances.
The way the underground ransomware gang’s new tactics strategy is developing is reflected in this multi-layered approach. Overwhelming victims from all sides until they give in is the goal, not just one approach.
+
Double extortion and psychological pressure
Ransomware has evolved into a mental game. The danger extends beyond data loss to include public humiliation. These days, victims are listed on dark web leak sites like trophies, complete with countdown timers that indicate when stolen files will become public.
Negotiations are painful because of this underground ransomware gang’s new tactics. The issue between a business and its attackers is no longer a private one. Executives are forced to balance the reputation of their brand against demands for ransom when it turns into a public scandal.
Automation and AI in the Hands of Criminals
The use of artificial intelligence tools by these gangs is among the most concerning changes. AI is capable of writing persuasive emails, automating phishing campaigns, and even negotiating ransom demands. According to some reports, gangs have used AI chatbots to interact with victims while they are negotiating.
Automated network reconnaissance, quicker password cracking, and real-time learning from unsuccessful attempts are now all part of the underground ransomware gang’s new playbook. Defenders must contend with adversaries that are always changing, much like a never-tired chess machine.
Sectors Under Attack: Who Is Targeted First?
Not every victim is created equal. Important sectors like manufacturing, healthcare, and finance continue to be prime targets. Because downtime can endanger lives, hospitals are particularly vulnerable. Recently, a European clinic refused to pay and was denied access to patient records for days.
Industries with a low threshold for disruption are frequently given priority in the underground ransomware gang’s new tactics framework. The likelihood of the ransom being paid is increased by that leverage.
Case Study: A Manufacturing Company Captured
Think about a mid-sized South Korean manufacturing business. Before employees noticed machines halting one by one, everything appeared to be normal. Digital control systems were locked in a matter of hours. Using a VPN credential that had been stolen, the attackers gained access.
In addition to demanding millions, the ransom note threatened to leak confidential supplier contracts if it was ignored. Operations stalled, backups were tainted, and leadership wavered. This story demonstrates how the new tactics used by the underground ransomware gang involve operational sabotage in addition to digital theft.
Insights from Previous Vulnerabilities and Current Events
Patterns can be seen in history. The fear of data loss was the foundation of early ransomware. Data leaks followed, followed by DDoS attacks, and now pressure from AI. Defenders learn something new from every wave. Layered security and a rapid response culture were common traits of companies that survived attacks.
The new strategies used by the underground ransomware gang serve as a reminder that cybersecurity is a continuous process. Today’s flaw is yesterday’s fix.
Strategies for Defense That Are Still Effective Against the New Wave
Defenders are not helpless in spite of the sophistication. Offline backups, network segmentation, and multi-factor authentication are still functional. It is still crucial to train employees to recognize phishing. Because they restrict an attacker’s ability to move around a network, zero trust models are becoming more popular.
Businesses that make proactive monitoring investments frequently detect the intrusion before encryption starts. Speed of detection is crucial when dealing with new tactics used by underground ransomware gangs.
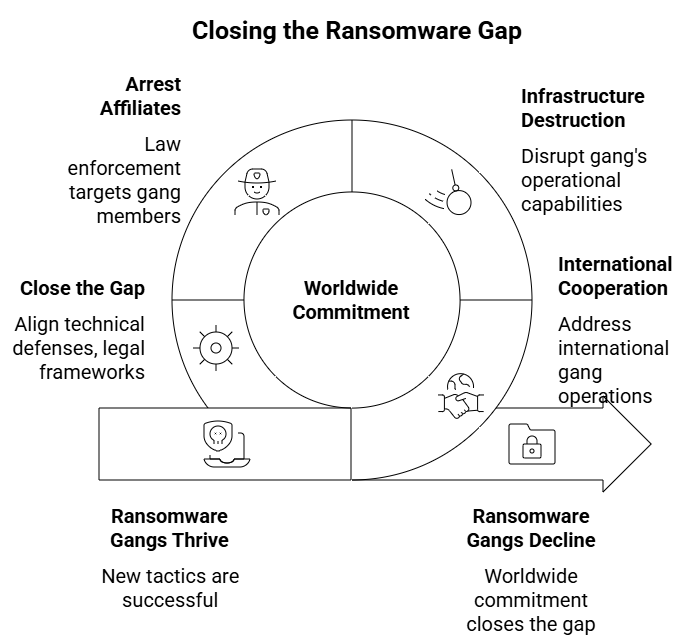
The Function of Law Enforcement and Governments
Though progress is uneven, governments are increasing their efforts. Gangs operate internationally, making international cooperation challenging. Nevertheless, well-planned infrastructure destructions yield outcomes. In recent years, law enforcement has arrested affiliates and taken down a number of leak sites.
But when one gang goes down, another one comes up. The discrepancy between technical defenses and legal frameworks contributes to the success of the underground ransomware gang’s new tactics. It will require worldwide commitment to close that gap.
Getting Ready for the Future: What Businesses Need to Do Right Now
What does this leave us with, then? The wave of new tactics used by underground ransomware gangs is not abating. Businesses need to think of themselves as targets rather than exceptions. This entails incorporating resilience into every stratum, including crisis communication strategies, technical defenses, and even psychological preparedness for public coercion.
Ultimately, the battle is about more than firewalls and backups. It has to do with attitude. Businesses that view security as a one-time expense are already falling behind. There is a chance for those who view it as a continuous struggle. And that opportunity is crucial in the current digital environment.
FAQs
What distinguishes the latest strategies used by the underground ransomware gang from previous ransomware attacks?
The primary goal of older ransomware was to encrypt files and demand money. These days, the underground ransomware gang uses a variety of tactics, including DDoS attacks, public humiliation, data theft, and even AI-powered tools. This multi-layered strategy complicates defense and puts more strain on victims.
Which sectors are most vulnerable to the latest strategies used by underground ransomware gangs?
The primary targets are sectors like manufacturing, healthcare, and finance that cannot afford downtime. These companies are more likely to pay ransoms since they risk having their operations shut down if they don’t comply with demands.
How can companies protect themselves from new strategies used by underground ransomware gangs?
Network segmentation, offline backups, multi-factor authentication, and ongoing monitoring are the best defenses. Given that many attacks start with phishing, employee awareness training is also crucial. Organizations can remain resilient against these changing threats by implementing proactive security planning.
Strong endpoint protection is essential given the new tactics used by underground ransomware gangs. Hoplon Infosec’s Endpoint Security protects devices, identifies threats instantly, and halts the spread of ransomware. This guarantees that businesses remain safe from constantly changing threats.
Follow us on X (Twitter) and LinkedIn for more cybersecurity news and updates. Stay connected on YouTube, Facebook, and Instagram as well. At Hoplon Infosec, we’re committed to securing your digital world.
Was this article helpful?
React to this post and see the live totals.
Share this :