WebDAV RAT Attacks: Windows RAT Sneak Attack!

Hoplon InfoSec
01 Mar, 2026
Cybercriminals have recently started to use an old but still useful part of Windows File Explorer called WebDAV in ongoing WebDAV RAT attacks.This method lets them put Remote Access Trojans, or RATs, into company networks without anyone noticing. Cofense was the first to notice the activity.
Cofense and Proofpoint say that more than 2,500 Active Threat Reports (ATRs) have mentioned this specific technique as of the first quarter of 2026. About 89% of these attacks used a RAT to get in. XWorm made up 45% of those cases, AsyncRAT made up 28%, and DcRAT made up 16%.
Various cybersecurity reports indicate that 58% of these attacks were originally aimed at Europe, but there has been a rise of almost 15% in Asia during 2026.
( Image source: confence)
Why is WebDAV Still Dangerous in Windows 10, 11, and Server 2022?
WebDAV was first used in 1999 to help people work together on files online. Microsoft said in late 2023 that they were no longer going to include the WebClient service in Windows Explorer, but it is still turned on by default in Windows 10, 11, and Server 2022.
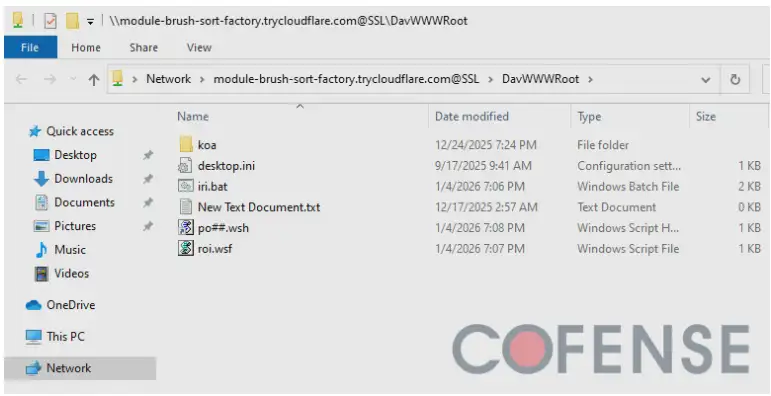
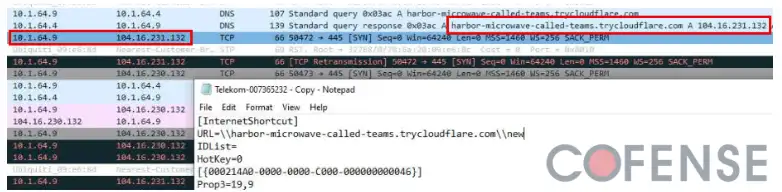
Because of this, it is still a very good way to attack. Ports 80 or 443 are usually used by WebDAV. This makes the bad traffic look like normal web browsing. When you test links like file://trycloudflare.com/DavWWWRoot in the real world, Windows Explorer mounts remote folders as if they were local drives.
Windows Defender doesn't always send out alerts. Proofpoint says that attackers were able to get around security layers in about 37% of the cases they looked at. Cofense's simulations show that 82% of users just ignore security warnings. That number goes up to 91% in the finance sector.
Common WebDAV Attack Methods Used to Spread Remote Access Trojans (RATs)
In addition to the basic method, there are now several different ways to do it:
• Direct File URIs: Clicking a link gives WebDAV remote root access.
• URL Paths: Just looking at a file can start a connection to the attacker in the background.
• PowerShell Scripts: These download bad code from a command server without following normal execution rules.
• OneDrive Lures: Attackers use fake domains like https://www.google.com/search?q=ms-onedrive-shared.com to trick people. About 22% of the 2026 campaigns used this method.
• ISO Files: WebDAV hosts malicious ISO files that are automatically mounted and run.
The bait messages were invoices in German, English, and French. A lot of the time, AI was used to make this content in more than one language. At its busiest, about 15,000 emails were sent out in one day.
( Image source: confence)
WebDAV RAT Payloads and Targeted Regions in 2026
Once attackers get in with a RAT, they usually steal credentials or go deeper into the network. 62% of the victims were European banks, but more and more organizations in Bangladesh and India are being targeted.
There has been a noticeable rise in localized invoice spoofing and the misuse of bank-themed domains. Attackers usually change the servers they use every 1 to 72 hours. In the past, it took 8 hours to find these threats, but now it takes less than 4 hours on average.
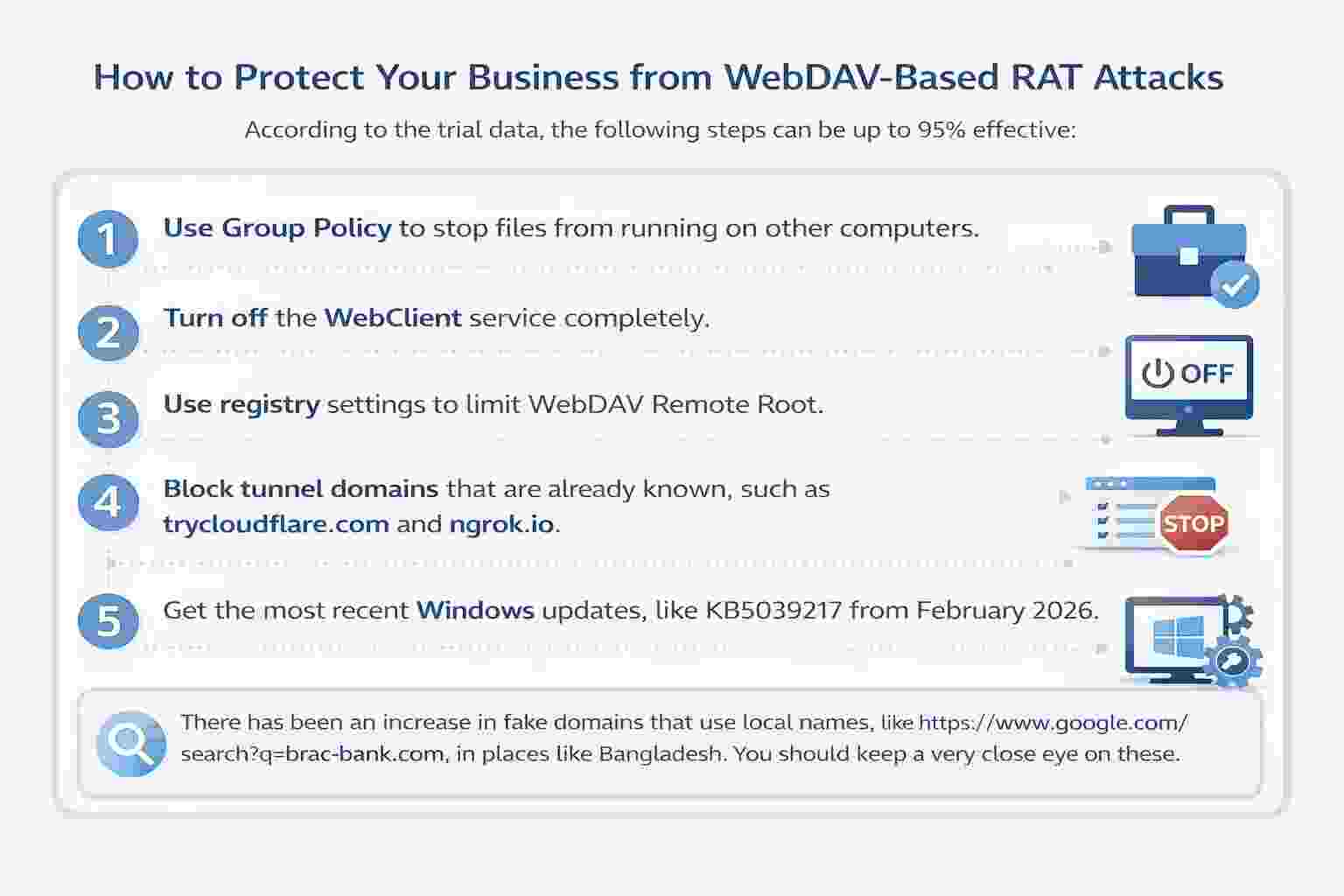
How to Protect Your Business from WebDAV-Based RAT Attacks
According to the trial data, the following steps can be up to 95% effective:
Use Group Policy to stop files from running on other computers.
Turn off the WebClient service completely.
Use registry settings to limit WebDAV Remote Root.
Block tunnel domains that are already known, such as trycloudflare.com and ngrok.io.
Get the most recent Windows updates, like KB5039217 from February 2026.
There has been an increase in fake domains that use local names, like https://www.google.com/search?q=brac-bank.com, in places like Bangladesh. You should keep a very close eye on these.
The Future of WebDAV Exploitation and AI-Generated Cyber Attacks
Experts say that AI-generated content is now involved in about 30% of attacks. People are also worried that Android's mobile WebDAV features could be the next target.
These attacks are thought to cost the world economy $1.2 billion a year. WebDAV is an old technology, but it is being used very well today. Improving user awareness is still the most important line of defense, along with technical controls.
A few short questions and answers about WebDAV RAT attacks
What does WebDAV mean?
Windows 10, 11, and Server 2022 still have a file-sharing protocol from 1999 turned on by default. This lets attackers mount malicious remote folders as local drives over ports 80 and 443.
Why do hackers use it to make RATs?
It looks like normal web traffic, gets past Defender (37% of the time), and 82% of users ignore warnings, spreading RATs like XWorm (45% of the time).
What are the best RATs for attacks in 2026?
XWorm (45%), AsyncRAT (28%), and DcRAT (16%) were the most common RATs used in 2,500+ reports.
Main targets and lures?
58% of the attacks came from Europe (banks), 15% from Asia (Bangladesh/India), and 22% from OneDrive. The attackers used fake invoices in German, English, and French, as well as ISO files.
How do attacks get around?
Direct file URIs, URL paths, PowerShell scripts, and up to 15,000 emails a day with AI-generated multilingual bait.
What are the main defenses?
Turn off WebClient, block trycloudflare.com/ngrok.io, and install the KB5039217 update. This works 95% of the time with Group Policy and training.
For more latest updates like this, visit our homepage.
Was this article helpful?
React to this post and see the live totals.
Share this :