Weekly Cybersecurity Recap: Updates, Risks & Threats

Hoplon InfoSec
13 Mar, 2026
What happed in the cybersecurity world this week, and why should businesses watch?
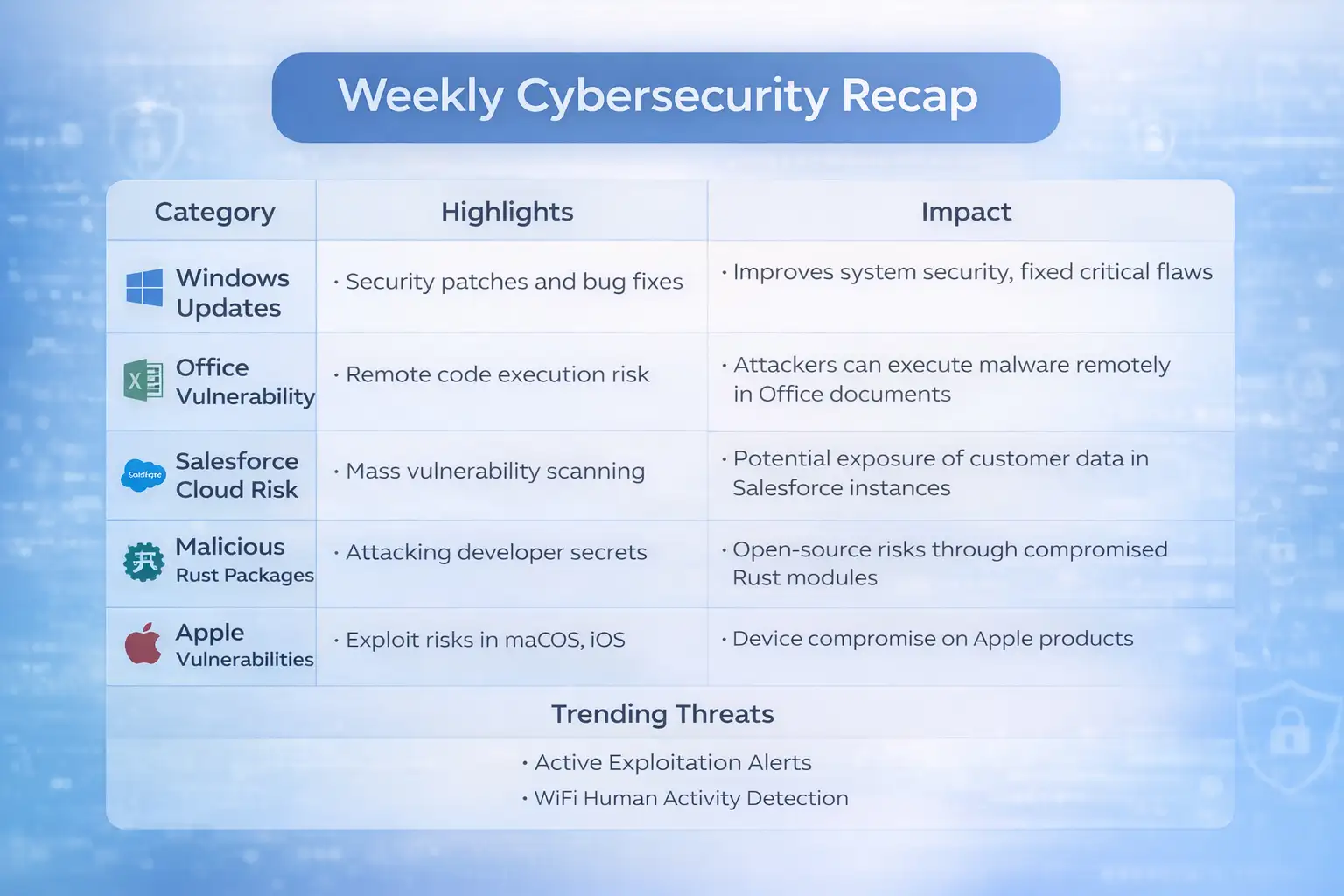
This daily cybersecurity recap highlights recently bared vulnerabilities, software security updates, force-chain pitfalls, and arising exploration that affects enterprise systems, pall platforms, and everyday bias. Several merchandisers released security patches while experimenters uncovered attacks targeting development tools, enterprise pall platforms, and operating systems.
The big shift looks like this.
Old approach Organizations replied to incidents after damage passed.
New approach Security brigades cover vulnerability exposures and patch cycles continuously.
Result Faster mitigation, reduced attack face, and smaller large-scale breaches.
For business leaders and IT brigades, the assignment is simple. Cyber threat changes every week. Keeping track of vindicated security updates and vulnerabilities helps associations avoid expensive incidents and functional dislocations.
What happed This Week in Cybersecurity
Multiple Security Updates and Vulnerabilities Bared
This daily cybersecurity recap covers several verified security events reported by merchandisers, security experimenters, and government agencies.
The major themes include:
Security patches for Windows operating systems
Vulnerabilities affecting enterprise platforms similar as Salesforce Experience pall
Remote law prosecution pitfalls in productivity software
Force-chain pitfalls targeting open-source packages
Active exploitation warnings from government agencies
Security exploration on WiFi-grounded mortal exertion discovery
Each content represents a different attack face. Operating systems, pall platforms, inventor tools, and wireless networks all face different types of pitfalls.
For associations running large digital surroundings, that diversity makes monitoring indeed more important.

Windows Security Updates and Patch Activity
Windows accretive updates and system fixes
Security updates remain one of the most common motifs in any daily cybersecurity recap.
Microsoft released accretive updates affecting several Windows performances. These updates generally include:
Security patches
Bug fixes
Performance advancements
System trustability updates
According to Microsoft attestation, accretive updates are designed to rush multiple fixes into one installation package. This approach reduces the complexity of patch operation for associations.
For illustration, updates affecting Windows recovery factors addressed issues that could impact recovery surroundings.
Why accretive updates count
Numerous cyber attacks begin with outdated software.
Bushwhackers frequently search the internet for bias running aged performances of operating systems. Once they identify unpatched systems, they can exploit known vulnerabilities.
That's why merchandisers encourage associations to emplace updates snappily. Patch operation remains one of the most effective protective strategies available.
Microsoft Office Remote Code prosecution threat
What the vulnerability involves
Another crucial highlight in this daily cybersecurity recap involves a vulnerability affecting Microsoft Office.
A remote law prosecution vulnerability generally allows bushwhackers to run vicious law on a victim system after opening a especially drafted train.
Security advisories frequently describe the threat in simple terms.
Still, bushwhackers may be suitable to execute commands on the system with the same warrants as the stoner, if a stoner opens a vicious document.
Why bushwhackers target productivity software
Office software is extensively used in business surroundings.
Documents are changed daily between:
Workers
Guests
Mates
Merchandisers
Because druggies trust these documents, bushwhackers constantly use document-grounded exploits in phishing juggernauts.
This is why numerous security brigades emplace dispatch filtering, sandbox analysis, and endpoint protection tools.
Salesforce Experience pall Vulnerability and Scanning exertion
What experimenters observed
Security experimenters reported surveying exertion targeting a vulnerability affecting Salesforce Experience pall surroundings.
Experience pall allows associations to make client doors and mate access systems on top of Salesforce structure.
Experimenters noted automated scanning exertion trying to identify exposed cases.
Why pall platform vulnerabilities count
Cloud platforms power numerous client-facing services.
A vulnerability in these systems could expose:
Client information
Internal data
Authentication commemoratives
Configuration files
For businesses that calculate heavily on CRM platforms, security monitoring and configuration operation come essential.
Force Chain threat vicious Rust Packages
Inventor ecosystems under attack
This daily cybersecurity recap also highlights force-chain pitfalls affecting open-source ecosystems.
Security experimenters linked vicious Rust packages that tried to steal inventor secrets in CI/CD surroundings.
Nonstop integration systems frequently store sensitive data similar as:
API keys
Authentication commemoratives
Deployment credentials
Still, they may gain access to product systems or software depositories, if bushwhackers access these secrets.
Why force-chain attacks are adding
Open-source ecosystems power ultramodern software development.
Numerous operations calculate on hundreds of external packages.
While this improves development speed, it also introduces threat. A single compromised reliance can affect numerous systems.
That's why associations decreasingly overlook dependences and corroborate package integrity before deployment.
Government Warning laboriously Exploited Vulnerabilities
CISA premonitory highlights
Government cybersecurity agencies occasionally advise associations when vulnerabilities are being laboriously exploited.
In this case, the U.S. Cybersecurity and structure Security Agency issued cautions about vulnerabilities observed in real-world attacks.
These advisories generally prompt associations to:
Apply security patches incontinently
Review system logs
Apply monitoring controls
When vulnerabilities appear in active attack juggernauts, the urgency increases significantly.
macOS and iOS Security Vulnerabilities
Mobile and desktop ecosystems also affected
Apple platforms also appeared in this daily cybersecurity recap due to recently bared vulnerabilities.
Security advisories noted issues affecting macOS and iOS systems that could potentially be exploited in targeted attacks.
Apple generally addresses similar issues through software updates.
Associations using Apple bias frequently emplace mobile device operation (MDM) results to apply patch installation and security programs.
Exploration limelight WiFi Signals Detecting mortal exertion
What experimenters discovered
Security experimenters published studies demonstrating that WiFi signals can occasionally descry mortal movement through walls.
The conception is known as WiFi-grounded mortal exertion recognition.
Wireless signals bounce off objects and people. By assaying signal changes, algorithms may descry stir patterns.
Why this exploration matters
While the technology has licit uses similar as smart home monitoring or exigency response systems, it also raises sequestration questions.
Experimenters emphasize that the technology remains experimental and depends heavily on controlled surroundings.
No wide marketable exploitation has been officially proved.
AI and inventor Tools Security Around Code Generation
Security discussion around AI rendering tools
AI rendering tools similar as automated programming sidekicks continue to attract attention from security experimenters.
The main concern involves how generated law might include vulnerabilities if inventors calculate on it without proper review.
Security experts recommend treating AI-generated law the same way as mortal-written law.
That means applying:
Law reviews
Vulnerability scanning
Security testing
Responsible development practices remain essential anyhow of how the law was created.
Patch Delay vs Immediate Response
Consider a typical enterprise script.
Before bettered patch operation
A company detainments operating system updates for months because of comity enterprises.
During that time, bushwhackers exploit a known vulnerability affecting unpatched systems. The breach leads to data loss and functional time-out.
After espousing visionary security monitoring
The association tracks security advisories and applies critical patches within days. Vulnerabilities are addressed before bushwhackers can exploit them.
The difference is n't just specialized. It directly affects business durability and character.
Who's utmost Affected by These Security Developments
Businesses and Enterprises
Companies running pall platforms, enterprise software, and development channels face the topmost exposure.
Security brigades must cover vulnerabilities across operating systems, operations, and pall services contemporaneously.
Software Developers
Developers counting on open-source packages must corroborate dependences precisely.
Force-chain attacks decreasingly target development ecosystems.
Individual druggies
Consumers using operating systems, mobile bias, and productivity software should keep their bias streamlined.
Indeed particular computers can come entry points for phishing or malware attacks.
Benefits and Limitations of Security Advisories
Benefits
Early warning about vulnerabilities
Seller-handed mitigation steps
Translucency around security pitfalls
Faster patch deployment
Limitations
Not every vulnerability is discovered incontinently
Some exploits appear before patches are available
Associations may delay updates due to functional constraints
Security advisories help associations respond snappily, but they can not exclude threat entirely.
What Organizations Should Do Now
Security professionals frequently recommend several practical conduct after reviewing updates in a daily cybersecurity recap.
Immediate conduct
Apply operating system updates instantly
Patch productivity software vulnerabilities
Examiner pall platform configurations
Review CI/CD security practices
Strategic conduct
Apply automated patch operation
Emplace vulnerability scanning tools
Borrow zero-trust security models
Maintain incident response plans
Cybersecurity is infrequently answered by one tool or one policy. It requires nonstop monitoring and adaption.
Constantly Asked Questions
What's a daily cybersecurity recap?
A daily cybersecurity recap summarizes important security updates, vulnerabilities, and trouble intelligence reported during the week. It helps associations understand arising pitfalls and apply mitigation strategies snappily.
Why are software updates important for cybersecurity?
Software updates fix vulnerabilities discovered by experimenters or vendors. However, bushwhackers may exploit those sins, if associations delay installing them.
What are force chain attacks in software?
Force chain attacks target third-party factors similar as open-source libraries. Bushwhackers fit vicious law into dependences used by numerous operations.
Are WiFi exertion discovery technologies extensively used?
WiFi-grounded stir discovery is still primarily a exploration conception. While it has implicit operations, there's limited substantiation of wide real-world deployment.
How can businesses stay informed about security pitfalls?
Associations generally follow seller security advisories, government cybersecurity cautions, and trouble intelligence reports published by security experimenters.
Summary
This daily cybersecurity recap highlights several vindicated developments across the security geography, including operating system updates, software vulnerabilities, pall platform pitfalls, and force-chain pitfalls.
The main benefit for associations is mindfulness. By tracking vulnerabilities beforehand, businesses can apply patches and reduce exposure before bushwhackers exploit sins.
The broader capability lies in erecting a visionary security culture. Organizations that cover vulnerability exposures, update systems regularly, and secure development surroundings are far more set for evolving pitfalls.
Cybersecurity changes constantly. Staying informed each week remains one of the simplest yet most important protective strategies.
References
Was this article helpful?
React to this post and see the live totals.
Share this :