What is an MFA Fatigue Attack? Stop Clicking Allow Now!

Hoplon InfoSec
23 Mar, 2026
Why Are People Suddenly Getting Repeated Login Alerts, and Why is This Dangerous?
A lot of people get repeated authentication notifications on their phones or email and think it's a problem with the technology. In fact, those alerts could be a sign of an MFA Fatigue Attack, a known social engineering technique in which attackers keep sending login approval requests until the victim finally clicks "approve."
Cybersecurity organizations like CISA and NIST say that attackers use people's behavior instead of technical flaws. Instead of going around security, they keep asking the user for permission until they get so frustrated or confused that they give in.
The outcome is simple but serious: if the request is approved, the attacker can get into the account legally.
What is an MFA Fatigue Attack?
An MFA Fatigue Attack is a type of social engineering attack in which attackers keep sending multi-factor authentication approval requests to a victim's device until the victim either accidentally or intentionally approves one. Once approved, the attacker can get into the account even though MFA is turned on.
When using multi-factor authentication, users usually have to prove who they are using more than one method. A password by itself isn't enough. The user must also give their permission for a push notification, enter a code, or check biometric data.
This extra step is meant to stop attackers even if they get the password.
But MFA Fatigue attacks change the game. Instead of breaking the system, attackers put pressure on the person who runs it.
The attacker keeps trying to log in with stolen credentials. Every time someone tries, the victim's device gets another notification. Some users just tap "Approve" to stop the noise after dozens of alerts go off during the day or night.
That approval is valid from the system's point of view. The attacker is now in.
Why MFA Fatigue Attacks Happen
MFA Fatigue attacks happen because a lot of authentication systems use simple approval prompts that don't require much interaction from the user. Attackers take advantage of this ease by sending login requests to victims until the user accidentally accepts one.
Background and Context
To cut down on password-based breaches, multi-factor authentication became very popular. Phishing campaigns, data leaks, and credential marketplaces on the dark web made it too easy to steal passwords.
To make it easier for users, tech companies made MFA easier to use. Push notifications took the place of hard-to-understand code entry. A user could confirm their identity with just one tap.
Convenience made it easier to use. It also made a new weak spot.
Attackers figured out how to use notification fatigue as a weapon.
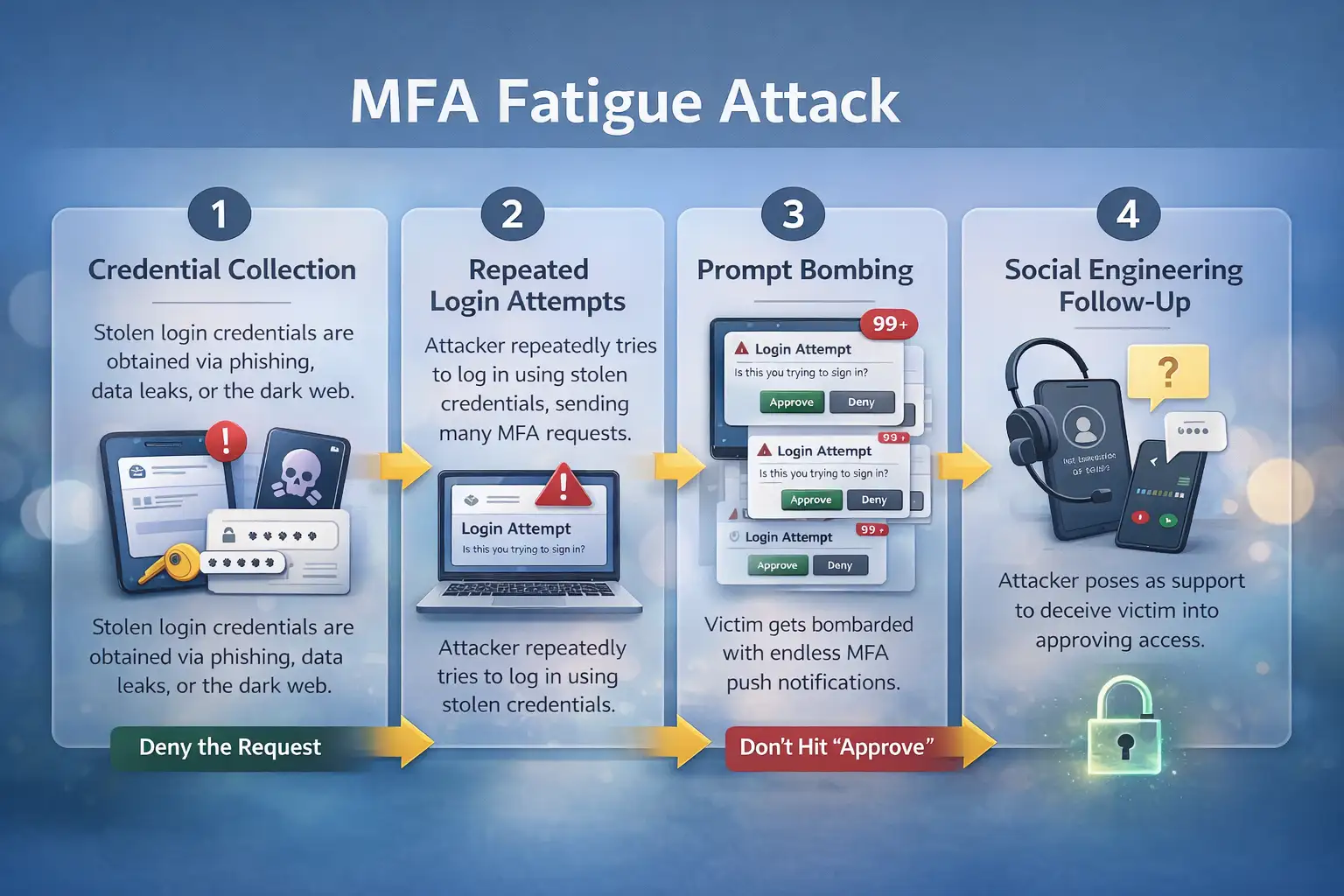
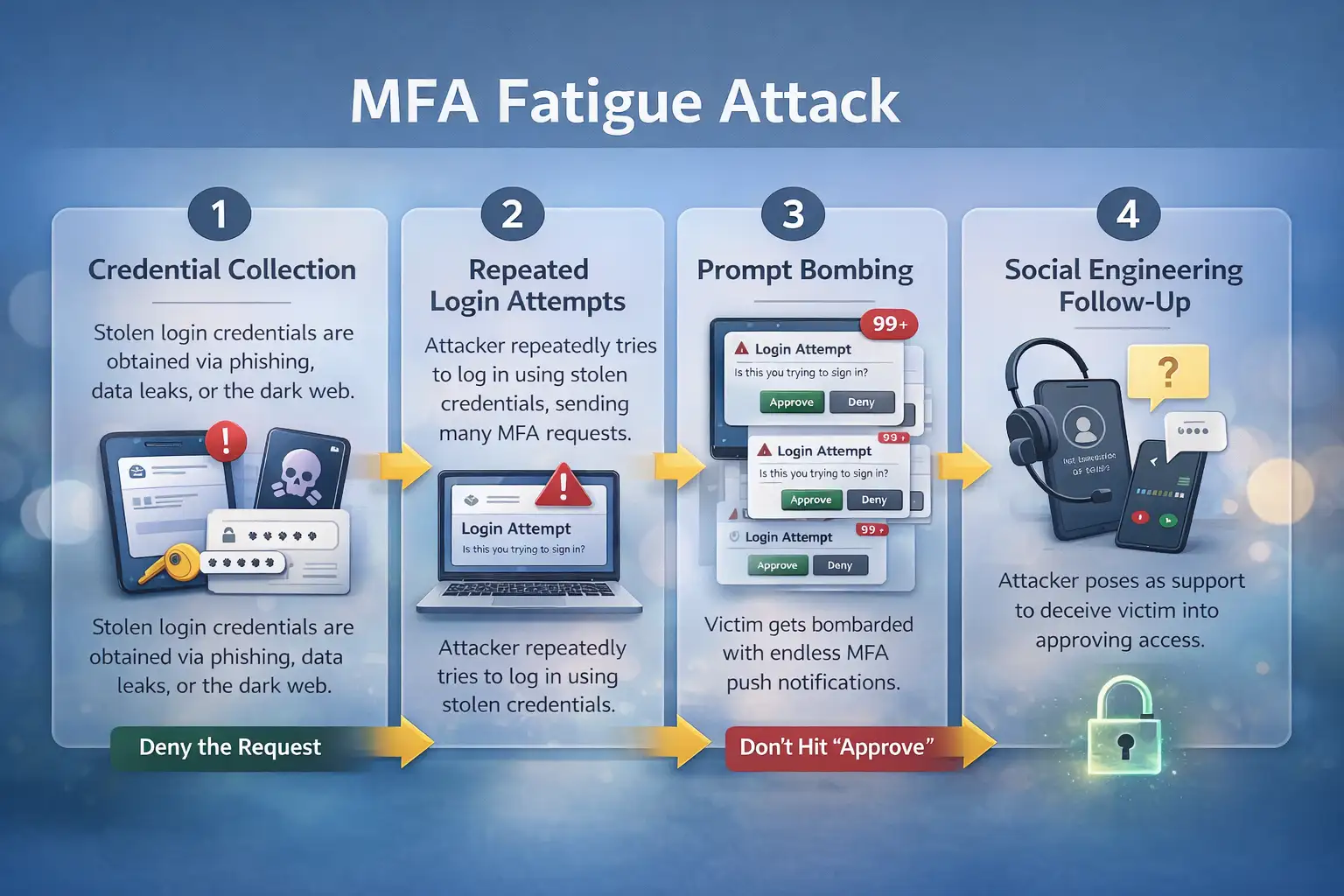
How an MFA Fatigue Attack Works
Stolen credentials are usually the first step in an MFA Fatigue Attack. The attacker keeps trying to log in with those credentials, which sends push authentication notifications. The victim gets dozens of requests for approval. In the end, the user agrees to one request, which lets the attacker into the account.
Step-by-Step Breakdown
1. Credential Collection
The notification itself is not usually the start of the attack. First, the attacker needs to know how to log in.
These credentials usually come from:
• Emails that try to trick you into giving them your personal information
• passwords that have been leaked before
• databases of credentials going around on the internet
• attempts at social engineering
Once the attacker has the username and password, they can make authentication prompts pop up.
2. Repeated Login Attempts
Then, the hacker keeps logging in with the stolen credentials.
Every time you try, you get a new authentication request. The notification may look like this, depending on the system:
• a push notification on a mobile device
• an alert from an authentication app
• a text message to confirm
• a request to verify your email login
Because modern MFA systems let you try multiple times in a short amount of time, attackers can set off dozens of prompts in just a few minutes.
3. Prompt Bombing
At this point, the victim gets alerts all the time.
The phones keep vibrating. Every few seconds, notifications show up. Some people get them at night.
The goal is clear. Wear the user out.
Someone who is angry might agree to the request just to stop the alerts.
4. Social Engineering Follow-Up
In some cases that have been recorded, attackers go even further.
They call the victim and act like they're tech support. The attacker might say that the notification is part of a maintenance update or a way to check your login.
If the victim believes the explanation, they agree to the request.
How Multi-Factor Authentication Works
To prove someone's identity, multi-factor authentication needs two or more separate authentication factors. Usually, these factors are something the user knows, something the user owns, or something that is part of the user, like their fingerprints.
The Authentication Process
When you log into a system that uses MFA, the process of verifying your identity usually happens in steps.
The user first gives a main credential. Most of the time, this is a combination of a username and password.
The system checks those credentials and then asks for another piece of information to confirm identity. This could be a mobile notification, a hardware token, or a check of your fingerprints.
The system only lets you access the resource after both factors have been confirmed.
Types of Authentication Factors
Knowing what authentication factors are helps us understand why MFA usually works and why attackers try to get around it by using social engineering.
Knowledge Factors
These are things that only the user should know.
Some examples are passwords, PIN codes, and answers to security questions. Knowledge factors are common, but they are also weak because passwords can be stolen or used again across services.
Possession Factors
Possession factors need a real device.
Authentication apps, security keys, and mobile devices that get login alerts are some examples. A lot of modern MFA systems depend on possession factors.
Inherence Factors
Inherence factors depend on physical characteristics.
These are things like recognizing fingerprints, faces, voices, or irises. Biometric verification is safer because it is directly linked to the user's body.
MFA Fatigue Attack Example: Before and After
Think about a typical worker who works from home.
Before the Attack
The employee gets a login message once or twice when they try to get into company systems. They approve it quickly and go back to work. They get used to approving these requests without much thought over time.
During an MFA Fatigue Attack
All of a sudden, their phone starts buzzing all the time. Every minute, notifications pop up. The worker thinks something is broken.
They tap "approve" after a few breaks.
The attacker can get into internal systems in a matter of seconds.
The attacker was hoping for this exact result.
Who is Most Affected by MFA Fatigue Attacks?
Different groups face different risks.
Individual Users
Regular users are at risk because they might not know why they keep getting authentication notifications.
They often think the alerts are system errors instead of active attacks._
Businesses
Organizations are more at risk because employee accounts often let people into internal networks, company data, and operational systems.
Once an attacker gets in through a hacked account, they might try to move around the network.
IT and Security Teams
Security experts need to be able to quickly spot strange authentication patterns.
When there are a lot of authentication prompts in a short amount of time, it usually means that someone is trying to abuse their credentials or is tired of using MFA.
Benefits and Limitations of Multi-Factor Authentication
MFA is still one of the best ways to protect your security.
But it can still be changed.
Benefits
• Lowers the chance of breaches that only use passwords
• Adds more layers of verification
• Keeps sensitive systems and user identities safe
Security groups strongly suggest using MFA because it greatly lowers the number of unauthorized access attempts when done right
Limitations
• Users can approve requests without checking them first
• Users have to make decisions for push notification systems to work.
• Attackers can use people's anger against them.
These limits show an important truth. User awareness is more important than security technology alone.
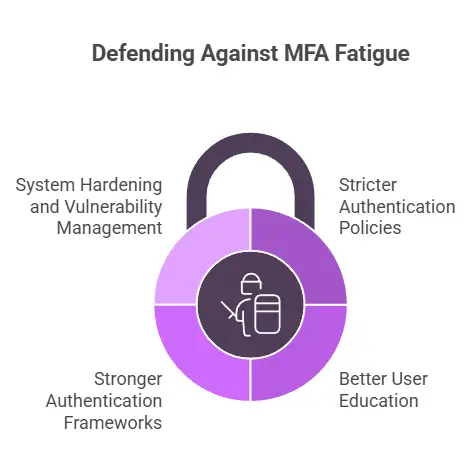
How Companies Protect Themselves from MFA Fatigue Attacks
More and more, security teams use a number of defensive strategies.
Stricter Authentication Policies
Companies often limit the number of times people can try to log in within a certain amount of time. Limiting the number of attempts makes it harder for the attacker to flood a user with prompts.
When there are multiple failed attempts to log in, security systems may also send out alerts.
Better User Education
User awareness programs are still one of the best ways to protect yourself.
Employees should know that getting repeated login notifications could mean an attack instead of a technical problem.
Training helps users spot strange behavior and report problems right away.
Stronger Authentication Frameworks
Some companies use more advanced authentication models that don't rely as much on passwords.
For instance, security frameworks like Zero Trust architecture need to check your identity all the time before letting you use resources. When deciding whether to authenticate someone, they look at the device's identity, location, and behavior.
System Hardening and Vulnerability Management
Security teams also make the infrastructure of the system stronger.
Regularly updating software, managing patches, and scanning for vulnerabilities lower the chances that attackers will get credentials in the first place.
It also helps to look at authentication logs to find strange login patterns.
What Users Should Do Right Away
If you keep getting authentication notifications that you didn't ask for, be careful.
Take these useful steps into account.
• Don't approve login requests that come out of the blue
• Right away, change the password for your account
• Tell the service provider or IT team about the activity
• look over recent activity on your account
If the notifications keep coming after you change your password, security experts suggest turning on extra verification methods or getting in touch with support.
Common Mistakes That Make MFA Fatigue Attacks Work
Many successful attacks happen because users don't know they're helping the attacker.
Common mistakes are:
• allowing notifications without checking login activity
• thinking that alerts are just technical problems
• Not paying attention to repeated login requests
• giving authentication codes to people you don't know
These actions may seem harmless, but they give attackers chances.
Frequently Asked Questions About MFA Fatigue
What does MFA fatigue mean?
MFA Fatigue is a type of social engineering attack in which attackers keep sending authentication requests to a victim until the victim finally approves one, giving the attacker access to the account.
Is MFA still safe?
Yes. One of the best ways to keep people from getting into your account without permission is to use multi-factor authentication. Users, on the other hand, need to carefully check each authentication request.
Why do attackers send repeated login alerts?
Attackers depend on how people act. Notifications that keep coming in can be annoying or confusing, which makes it more likely that the victim will approve a login request without checking it.
What should I do if I get login approvals that I didn't expect?
Don't give them permission. Right away, change your password and check the security settings for your account. Let the security team know if the account is part of a work system.
Can MFA Fatigue attacks hurt personal accounts?
Yes. If attackers get the username and password for an account that uses push notification authentication, they could target that account.
In Short
Users can spot suspicious authentication notifications before approving them if they know how MFA Fatigue attacks work.
The strategy doesn't just rely on technical defenses; it also combines authentication security with user awareness.
Companies that teach users, make authentication rules stricter, and keep an eye on login behavior make it much less likely that hackers will be able to use MFA fatigue techniques.
Useful Suggestions
A simple rule is what security teams suggest.
Never approve the notification if you didn't start the login request.
If you keep getting asked to log in, don't think it's a bug in the system; it's a warning sign. Reporting strange behavior right away can stop attackers from getting in.
Final Thought
Every year, security tools get better. People who attack know that. So they go after something easier more and more.
People.
Most of the time, just knowing what causes MFA Fatigue is enough to stop the attack before it works.
To learn more, visit our blog page.
Sources
Was this article helpful?
React to this post and see the live totals.
Share this :