Canvas Cyberattack Locks Students Out During Finals Week

Hoplon InfoSec
11 May, 2026
Canvas Cyberattack Locks Students Out During Finals Week
"I'm locked out of my exam."
That was the message a student posted on X on May 7, 2026, as the Canvas cyberattack finals week crisis unfolded across North America. It was not a single frustrated post. Within hours, thousands of students were saying the exact same thing.
This article covers the full story, what happened, who did it, what data was stolen, which schools were hit, and what you should do right now if you are a student or faculty member.
What Exactly Happened? The Canvas Cyberattack Finals Week Breakdown
Here is the short answer first, because you deserve it fast.
On May 7, 2026, a ransomware group called ShinyHunters took down Canvas by Instructure, the learning management system used by more than 30 million students across 9,000+ schools worldwide. The attack happened at the worst possible time: the middle of finals week, when students needed access to exams, grade submissions, and course materials the most.
The group claimed to have stolen 3.65 terabytes of data, including well over 275 million private messages from students and faculty. They defaced Canvas login pages with a ransom note and gave schools a deadline of May 12, 2026, to contact them privately or face a full data leak.
This was not just a technical outage. This was targeted, timed, and deliberate.
Canvas Cyberattack Timeline: May 1 to May 9, 2026
Understanding the sequence of events matters. A lot happened before students ever saw that ransom note on their screens.
May 1 - The First Sign
Instructure, the company behind Canvas, quietly detected what it called "a cybersecurity incident perpetrated by a criminal threat actor." At this point, no public announcement went out. The company began investigating.
May 2 - Partial Disclosure
Instructure told institutions that the situation appeared to be "contained." In the same statement, the company acknowledged that names, email addresses, student ID numbers, course enrollment information, and internal messages could have been accessed. No passwords. No financial data. That was the official line.
May 3 - ShinyHunters Goes Public
The group posted Instructure on its dark web leak site. Their claim: 3.65TB of data stolen, including 275 million personal messages. They sent a ransom note with a May 6 deadline. Schools that did not respond would have their data leaked publicly.
May 6 - Deadline Passes, Platform Gets Hit
Instructure did not respond publicly. ShinyHunters followed through on its warning. Hackers defaced Canvas login pages at universities nationwide with the ransom note. Students logging in to review for finals instead saw a message from hackers telling their school to "negotiate a settlement."
On May 7 (Thursday), there was a full outage that caused widespread panic.
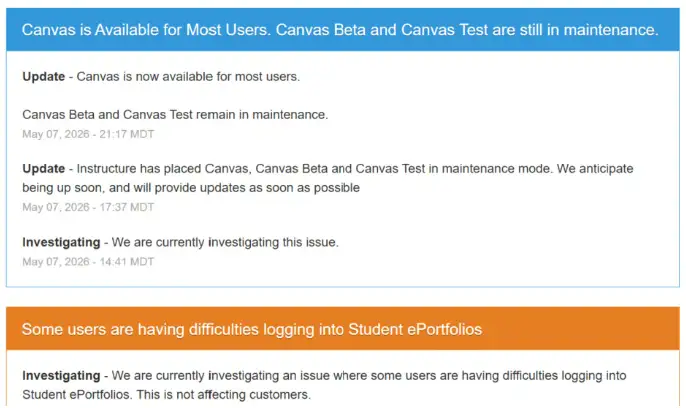
Canvas went offline, officially "for maintenance." The reality was a full-scale shutdown. Downdetector spiked with more than 2,870 reports from users across North America. Students flooded social media with panic posts. At 9:17 PM Mountain Time, Instructure posted that "Canvas was available for most users," but Canvas Beta and Canvas Test remained down.
May 8 (Friday) - Schools Start Canceling Exams
Boise State University announced it was canceling all finals. No rescheduling. No grade penalties. Students simply would not take those exams. Meanwhile, ShinyHunters issued a new extortion threat, this time targeting individual schools rather than just Instructure itself.
Then, in what can only be described as audacious, ShinyHunters posted a "press statement" on its leak site explaining that it was "not commenting" on what it called a "global incident." They were receiving so many press inquiries that they issued a statement specifically to say they had no comment.
Who is ShinyHunters? Understanding the Group Behind the Canvas Breach
If this name sounds familiar, it should. ShinyHunters is one of the most active and destructive ransomware groups operating today.
Their past targets include Tokopedia, AT&T, and Ticketmaster. They are known for targeting high-value data platforms and then running a two-stage extortion model: hit the company first, then go after individual customers or clients when the company does not cooperate.
What is particularly notable here is the language they used against Instructure: "ShinyHunters has breached Instructure (again). " That word "again" suggests the breach was not their first time inside the system. They accused Instructure of ignoring their earlier contact and simply applying "security patches" instead of taking the threat seriously.
Their communication method of choice for negotiation is TOX, an encrypted peer-to-peer messaging application. Schools were told to reach out through TOX by May 12 or face complete data exposure.
The extortion playbook here is textbook:
Breach the platform and sit quietly on the data
Issue a private ransom demand
When ignored, go public and escalate
Deface the platform to create chaos and media pressure
Move to extort individual institutions directly
Use a hard deadline to force rushed, panicked decisions.
It is calculated. It works. And education is the preferred hunting ground right now.
What Data Was Actually Stolen in the Canvas Hack?
This is the question every student and professor is asking, so here is the clear breakdown based on what Instructure has officially confirmed versus what ShinyHunters has claimed.
Confirmed Exposed (per Instructure)
Full names
Email addresses
Student identification numbers
Course enrollment information
Internal messages between users
NOT Confirmed Exposed (per Instructure)
Passwords
Dates of birth
Government-issued identification numbers
Financial information
Instructure stated: "If that changes, we will notify any impacted institutions."
ShinyHunters, on the other hand, claims the haul includes 275 million personal messages and 3.65TB of raw data. The gap between what the company confirms and what the hackers claim is wide. Until an independent forensic investigation concludes, the full scope remains uncertain.
Our interpretation: The company carefully chooses its language when it states "no evidence of financial data exposure" immediately after an attack. It does not mean the data is safe. It means they have not yet found proof it was accessed. Those are completely unique statements.
Which Universities Were Affected?
The Canvas LMS hacked 2026 event touched institutions across the United States, Canada, and the international community. Below is what we know:
All 8 Ivy League Schools
Harvard, Yale, Princeton, Columbia, UPenn, Cornell, Dartmouth, and Brown were all on the list of affected institutions. Students at these schools reported being unable to access exams, coursework, and submission portals.
Other Major US Universities
Duke, UCLA, University of Nebraska, UCF, Georgetown, Rutgers, MIT, Kent State, UTSA, James Madison University, and Boise State all experienced the attack. UTSA and JMU pushed back Friday exams. Boise State canceled them entirely.
K-12 Systems
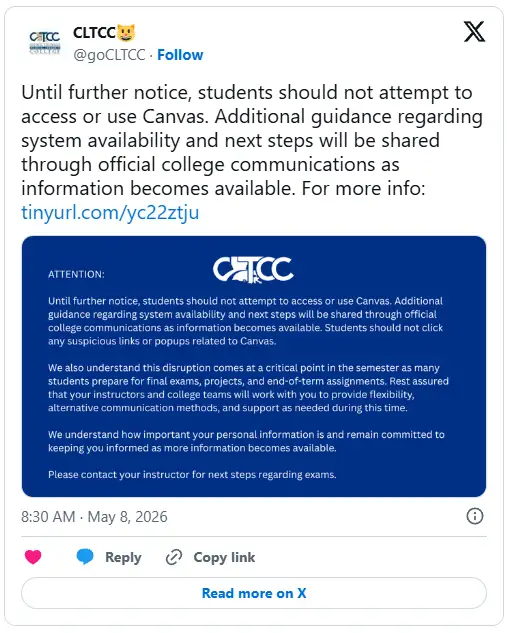
Several K-12 school districts in Florida were affected. The Central Louisiana Technical Community College (CLTCC) told students and faculty across all its social media pages: "Until further notice, students should not attempt to access or use Canvas." They also warned users not to click any suspicious links or popups related to the platform.
Canada
The University of British Columbia and Simon Fraser University sent alerts to students and staff about the possibility of targeted phishing attacks tied to the incident, according to a CBC report.
International
Oxford University appeared on the affected school list. ShinyHunters asserted that the breach data included over 9,000 institutions worldwide.
How Canvas Login Pages Were Defaced
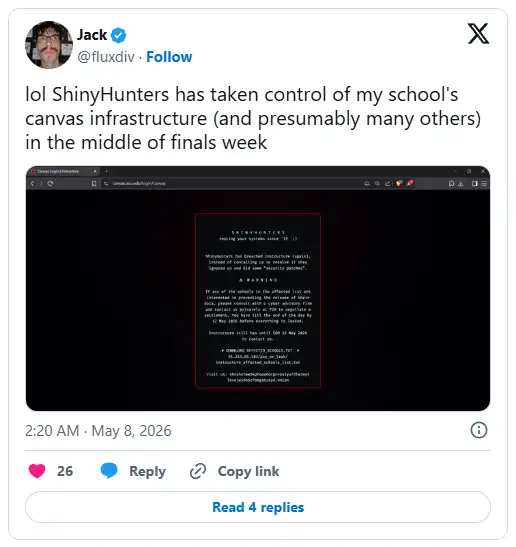
On May 6 and 7, students logging into Canvas did not see their dashboards. They saw a ransom note.
The University of Pennsylvania was among the confirmed schools where the Canvas platform was visibly defaced. The Daily Pennsylvanian, UPenn's student newspaper, reported that the full ShinyHunters extortion message appeared on the school's Canvas login page. The note urged impacted schools to "negotiate a settlement" and listed a contact method.
At approximately 4:20 PM on May 7, a Canvas-branded notice replaced the ShinyHunters message, indicating that the platform was undergoing "scheduled maintenance." That cover story did not hold for long. Students had already taken screenshots.
One student posted, "Lol, ShinyHunters has taken control of my school's Canvas infrastructure (and presumably many others) in the middle of finals week."
Finals Week Chaos: How Students and Professors Responded
The human cost of the Canvas cyberattack finals week is not measured in terabytes. It is measured in the stress of students who had studied for months and could not access their exams.
Social media filled up fast. A few reactions that spread widely:
"Canvas has been down for 6 hours, and it's freaking me out. Like is the FBI on this?"
"I still can't take my exam; the Honorlock access code is no longer working. I might be cooked."
On Downdetector, one user posted: "The irony that I need to submit my cybersecurity final." That comment had 2,870 others alongside it.
Professors were not spared either. At MIT, faculty scrambled to find student email addresses after losing access to the Canvas announcements feature. They had no other way to reach students directly.
Kent State said it was "very concerned" and confirmed that the disruption also hit tuition billing and financial aid processing. They activated contingency planning across multiple departments.
Schools handled the crisis differently:
|
School |
Response |
|
Boise State University |
Canceled all finals. No rescheduling. No grade penalties. |
|
UTSA |
Pushed back Friday exams |
|
James Madison University |
Moved some exams to Wednesday |
|
Kent State |
Contingency planning, monitoring |
|
MIT |
Faculty reached students via personal email |
|
Princeton, Harvard |
Posted Canvas status updates on X |
|
CLTCC |
Told students not to use Canvas at all |
Is Canvas Safe to Use Right Now?
use it with caution and change your password immediately.
Instructure posted on its status page at 9:17 PM MT on May 7 that Canvas was "available for most users." Canvas Beta and Canvas Test remained in maintenance mode. However, users continued reporting outages through Friday evening, hours after the official restoration announcement.
The May 12 deadline is the immediate concern. If schools do not contact ShinyHunters through TOX by the end of that day, the group says it will release all stolen data publicly. That would expose the names, email addresses, student IDs, and messages of millions of students to the open internet.
This Has Happened Before: Canvas 2026 vs. PowerSchool 2024
The Canvas LMS hacked 2026 situation has a direct predecessor. In December 2024, PowerSchool, a K-12 software provider, suffered a ransomware attack that hit more than 60 million students across 15,000 schools in North America.
PowerSchool paid the ransom. They believed the hackers would delete the data. They were wrong.
After collecting the payment, the unnamed group began extorting individual schools directly, threatening to leak data the hackers had never actually deleted.
The person responsible? A 19-year-old college student from Massachusetts, now serving four years in federal prison and ordered to pay more than $14 million in restitution.
The Canvas attack follows the same pattern almost exactly:
|
Canvas 2026 |
PowerSchool 2024 |
|
|
Platform type |
Higher Ed LMS |
K-12 SIS |
|
Users affected |
30M+ |
60M+ |
|
Schools affected |
9,000+ |
15,000+ |
|
Data claimed |
3.65TB, 275M messages |
Undisclosed volume |
|
Threat actor |
ShinyHunters |
Unnamed group |
|
Ransom paid |
Unknown (as of May 9) |
Yes |
|
Outcome after payment |
Pending |
Data still leaked |
The lesson from PowerSchool is clear. Paying does not guarantee deletion. The Canvas cyberattack finals week situation may play out the same way.
Our Analysis
When we analyzed the ShinyHunters breach claim against Instructure's disclosed response timeline, several things stood out.
Instructure said the incident was "contained" by May 2, yet the platform did not suffer its major outage until May 7. That five-day gap is significant. It suggests the initial breach containment was either incomplete, or ShinyHunters maintained persistent access through a secondary vector that the May 2 patch did not address.
The group's own language confirms thithis conclusionhey accused Instructure of applying "security patches" rather than engaging with them. That implies ShinyHunters was aware of Instructure's response in near real time, which typically indicates they still had read access to internal communications or system logs after the supposed containment.
The defacement of individual school Canvas subdomains, rather than a single central page, also suggests the group had access at the institutional tenant level, not just the Instructure parent infrastructure. That level of access would explain why 9,000+ schools each saw the ransom note on their own Canvas pages simultaneously.
This was not a smash-and-grab. It was a long-game operation.
-20260511110849.webp) Canvas cyberattack timeline May 2026
Canvas cyberattack timeline May 2026What Should Students and Staff Do Right Now?
This is the most important section. Take these steps today.
Step 1: Change Your Canvas Password Immediately Do not wait for your school to tell you. Go directly to your institutional account settings and update it. Use a strong, unique password you have not used elsewhere. This matters because your email address and student ID are likely already in the stolen data.
Step 2: Enable Two-Factor Authentication (2FA) If your institution supports 2FA on Canvas or your student email, turn it on now. This single step dramatically reduces the risk of unauthorized login even if your credentials are exposed.
Step 3: Do Not Click Suspicious Canvas-Related Links CLTCC issued this warning explicitly, and it applies to everyone. Phishing emails impersonating Canvas, Instructure, or your university IT department will start circulating using the stolen student name and email combinations. If a link asks you to "verify your Canvas account," do not click it.
Step 4: Watch for Targeted Phishing Attacks UBC and Simon Fraser University warned their students specifically about thithese threatsttackers now have your name, your email, and your student ID. They can craft convincing messages that appear to come from your university. Be skeptical of anything urgent-sounding in your inbox right now.
Step 5: Contact Your Institution's IT Security Team If you notice anything unusual with your accounts, like any unexpected login notifications or password reset emails you did not request, report it immediately. Your school's IT department is actively monitoring the situation.
Step 6: Monitor for Identity Theft Student ID numbers were in the exposed data. Those numbers, combined with your name and email, can be used in targeted fraud attempts. Check your financial accounts and university billing portal for anything suspicious.
Step 7: Email Your Professor Directly If you cannot access your exam, assignment, or submission portal, do not wait for Canvas to come back. Email your professor directly using your institutional email address. Document everything. Schools are actively accommodating students affected by this outage.
Why Universities Are the #1 Target for Ransomware Groups
Is it surprising that Canvas was attacked during finals weeweek,ecifically? Not to anyone watching the threat landscape.
Universities are not random targets. They are chosen with purpose.
Data richness. A single learning management system holds student IDs, grades, financial aid records, health office communications, course schedules, and years of private messages. That is more actionable personal data than most corporate systems hold.
Timing leverage. Attack during finals, and the pressure to pay becomes immediate. Schools cannot afford two weeks of back-and-forth negotiations when students need exam access tomorrow morning. ShinyHunters understood this perfectly.
Underfunded security. Most universities run IT security departments that are dramatically underfunded relative to the attack surface they defend. A system serving 30 million users with the security budget of a mid-sized company is a structural vulnerability, not a human failure.
Single-vendor dependency. Canvas is not just a portal. At many institutions, it is the only system connecting professors to students outside of physical class. Email lists, grade books, announcements, exam distribution, assignment submission, and lecture recordings all run through one vendor. One successful attack paralyzes an entire campus.
According to advisories from CISA (Cybersecurity and Infrastructure Security Agency), the education sector has been the second most targeted critical infrastructure sector for ransomware in the United States for three consecutive years. This is not a trend that is reversing.
Common Mistakes Students and Schools Make After a Breach
Mistake 1: Waiting for official confirmation before acting Instructure said the breach was "contained" on May 2. It was not. Do not wait for reassurance to change your passwords. Act on the possibility, not the certainty.
Mistake 2: Assuming old passwords are safe because they were not "confirmed" stolen. "No evidence of password exposure" is not the same as "passwords are safe." Until a full forensic audit is completed and published, treat your credentials as potentially compromised.
Mistake 3: Ignoring phishing warnings The stolen data combination of name plus email plus student ID is exactly what attackers use to build convincing impersonation emails. Reading an email from what appears to be your university registrar is not proof it is real.
Mistake 4: Paying the ransom without legal counsel For school administrators reading thithese emails,e PowerSchool case proved that paying does not guarantee data deletion. Before your institution contacts ShinyHunters, consult a cybersecurity legal advisory firm. The FBI has also issued guidance that paying ransomware demands often funds further attacks and does not guarantee data security.
Pro Tips: What Cybersecurity Analysts Actually Recommend
Use a password manager. If you have used the same password for Canvas and three other accounts, all three are now at risk. A password manager like Bitwarden or 1Password generates unique passwords for every account automatically.
Set up Google Alerts for your name plus student ID. It sounds unusual, but it is a fast way to catch if your data surfaces on public leak sites or news reports after May 12th.
Check haveibeenpwned.com. This free tool from security researcher Troy Hunt shows you whether your email address has appeared in known data breaches. Bookmark it and check it monthly.
Read official advisories, not just social media posts. CISA publishes real-time alerts on education sector threats at cisa.gov. Your university's IT security page will post verified guidance. Rely on those before acting on anything you see on Reddit or X.
Student Security Checklist: Do This Today
Change Canvas password to a strong, unique one
Enable 2FA on your Canvas and student email account
Do not click any suspicious Canvas-related emails or links.
Check your student email for unexpected login or password reset notices.
Email your professor directly if you cannot access your exam or submission.
Check HaveIBeenPwned.com for your email address.
Report anything suspicious to your university IT security team.
Review your financial aid and billing portal for unexpected activity.
Turn on login notifications for your institutional accounts if available.
Frequently Asked Questions
Who hacked Canvas in May 2026?
ShinyHunters, a well-known ransomware group, claimed responsibility for the hacked Canvas LMS 2026 incident. They say they stole 3.65 TB of data, including 275 million private messages from more than 9,000 schools, and set a May 12 deadline for schools to contact them or face a public data leak.
What student data was actually stolen from Canvas?
nstructure confirmed that full names, email addresses, student IDs, course enrollment information, and internal messages were potentially exposed. The company stated that passwords, dates of birth, government IDs, and financial data were NOT confirmed stolen as of May 9, 2026.
Which schools had finals canceled because of the Canvas cyberattack?
Boise State University canceled all finals on FriSaturday, May 9ith no rescheduling and no grade penalties for students. UTSA and James Madison University also pushed back exams. All 8 Ivy League schools, Duke, UCLA, MIT, Oxford, and more than 9,000 other institutions worldwide were affected by the outage.
Is Canvas safe to use now?
Instructure says Canvas is restored for most users as of May 8, 2026. However, users continued reporting outages through Friday evening. Canvas Beta and Canvas Test remained in maintenance mode. The May 12 deadline from ShinyHunters remains active, and the full data leak threat has not been resolved. Use Canvas with caution and change your password before logging back in.
The Bigger Picture
The Canvas cyberattack finals week is not just a story about one platform going down. It is a warning about how deeply embedded single-vendor platforms have become in academic life and how catastrophically exposed that makes students when those platforms fail.
MIT students could not reach their professors. Kent State students could not access financial aid information. Hundreds of thousands of students had months of academic work hanging in the balance because one company's security posture was not strong enough to stop a group that, by their own admission, had been inside the system before.
Ransomware groups are not going to stop targeting education. The data is too valuable, the security too weak, and the timing leverage too powerful.
What students can do is refuse to be passive about thetheirta security. Change the passwords. Turn on 2FA. Stop reusing credentials. These are not technical steps. They are habits. And right now, after the Canvas cyberattack finals week crisis, there has never been a better moment to build them.
Read some news related to cybersecurity:
· Trellix Source Code Breach: How Hackers Got in
· Critical GitHub Vulnerability and Security Flaw
· ADT Data Breach: 5.5 Million Customers Affected
· Spain Shuts Down Major Manga Piracy Site
· 2FA vs MFA
Published: May 11, 2026
Last Updated:May 11, 2026
Author: Radia, Cybersecurity Content Analyst
Was this article helpful?
React to this post and see the live totals.
Share this :