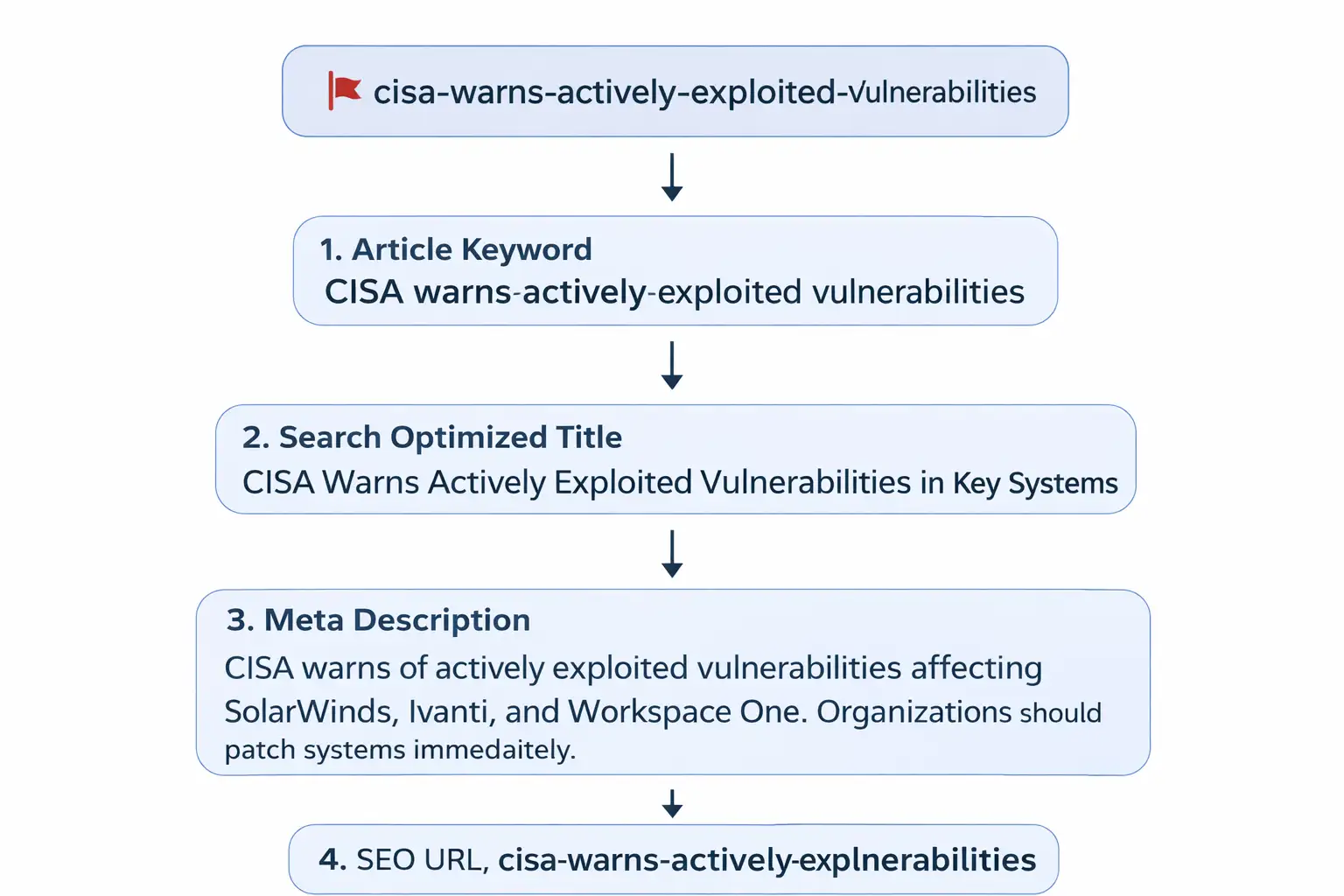
CISA Warns Actively Exploited Vulnerabilities in Key Systems

Hoplon InfoSec
10 Mar, 2026
CISA Warns of Actively Exploited Vulnerabilities
Author: Security Research Team
Source references: CISA KEV Catalog, Microsoft Threat Intelligence, Huntress, GreyNoise
Topic: CISA warns of actively exploited vulnerabilities
What does the latest CISA security alert mean for organizations?
Systems running certain SolarWinds, Ivanti, and Workspace One product may already be targeted by attackers.
Security researchers and the U.S. Cybersecurity and Infrastructure Security Agency confirmed that several weaknesses in widely used enterprise software are being actively abused. These weaknesses were serious enough to be added to the Known Exploited Vulnerabilities catalog, a list reserved for security flaws that attackers are already using in real environments.
When CISA warns of actively exploited vulnerabilities, it usually signals something urgent. Organizations are expected to patch quickly because attackers rarely wait.
For business leaders and IT teams, the shift is clear.
Old approach
Wait for internal testing before patching.
New reality
Patch immediately when exploitation is confirmed.
Result
Lower risk of ransomware intrusion and credential theft.
That change in mindset often determines whether a company becomes a victim or stays secure.
Why the Latest CISA Alert Matters
The CISA alert highlights three software vulnerabilities that attackers are already exploiting in real networks. These flaws affect SolarWinds Web Help Desk, Ivanti Endpoint Manager, and Omnissa Workspace One UEM.
The vulnerabilities are tracked as
• CVE-2025-26399 (CVSS score: 9.8) - SolarWinds Web Help Desk
• CVE-2026-1603 (CVSS score: 8.6) - Ivanti Endpoint Manager
• CVE-2021-22054 (CVSS score: 7.5) - Omnissa Workspace One UEM
The weaknesses could allow attackers to access systems, run commands, or expose sensitive credentials.
Security warnings appear regularly, but only a fraction make it into the Known Exploited Vulnerabilities catalog. That catalog is maintained specifically for issues that have credible evidence of exploitation.
In other words, these are not theoretical risks.
Attackers have already attempted to use them in real attacks.
This is why cybersecurity teams take these alerts seriously. Federal agencies are required to patch vulnerabilities listed in the KEV catalog within strict timelines.
Private companies often follow the same practice.
Understanding the Three Vulnerabilities Flagged by CISA
When CISA warns of actively exploited vulnerabilities, the agency usually provides detailed identifiers. Each vulnerability has a CVE number that allows security teams to track patches and risk levels.
Below is a breakdown of the confirmed issues.
SolarWinds Web Help Desk Command Execution Vulnerability
CVE-2025-26399 (CVSS score: 9.8)
The most severe vulnerability in this group affects SolarWinds Web Help Desk.
It carries a CVSS severity score of 9.8, which places it in the critical category.
Security researchers identified the issue in the AjaxProxy component of the application.
The SolarWinds vulnerability allows attackers to run commands on the affected system if they exploit unsafe data deserialization inside the AjaxProxy component.
The vulnerability occurs when software processes untrusted input as if it were safe data. Attackers can craft malicious data that tricks the system into executing commands.
Once successful, attackers may gain control over the host system.
Reports from Microsoft and the security firm Huntress suggest that threat actors are already attempting to exploit the flaw to gain initial access to networks.
Investigators believe some of the activity may be linked to a ransomware group known as Warlock.
Ransomware crews often search for entry points that allow them to move inside corporate networks. Vulnerabilities in help desk platforms can be attractive because those tools often connect with multiple systems.
Ivanti Endpoint Manager Authentication Bypass
CVE-2026-1603 (CVSS score
The second vulnerability affects Ivanti Endpoint Manager.
This weakness involves an authentication bypass through an alternate path or channel.
The Ivanti vulnerability could allow a remote attacker who is not authenticated to access stored credential data under certain conditions.
Why this matters
Endpoint management tools control devices across enterprise environments. They manage updates, policies, and credentials.
If attackers gain access to those systems, they may uncover sensitive authentication data.
That information could potentially help them move deeper into a network.
Interestingly, public information about active exploitation methods remains limited.
Security analysts have not yet disclosed how attackers are weaponizing the vulnerability. Ivanti’s public security bulletin also had not been updated to reflect exploitation status at the time of reporting.
This lack of detail sometimes happens during early investigation phases.
Security teams often release limited information until patches are widely deployed.
Workspace One UEM Server-Side Request Forgery Vulnerability
CVE-2021-22054 (CVSS score: 7.5)
The third vulnerability affects Omnissa Workspace One UEM, previously known as VMware Workspace One UEM.
The weakness is categorized as a server-side request forgery vulnerability.
The vulnerability allows an attacker with network access to send unauthorized requests to the Workspace One UEM server and potentially retrieve sensitive data.
How SSRF vulnerabilities work
Server-side request forgery occurs when an attacker tricks a server into making requests on their behalf.
The attacker does not directly contact the internal resource.
Instead, the vulnerable server becomes the messenger.
This technique can expose internal services, metadata endpoints, or sensitive information that would normally be inaccessible.
Security firm GreyNoise reported that this vulnerability had been exploited alongside other SSRF issues in a coordinated campaign targeting multiple products.
The activity highlights a growing trend.
Attackers increasingly combine vulnerabilities across products to gain stronger access to networks.
Why These Vulnerabilities Were Added to the KEV Catalog
CISA adds vulnerabilities to the KEV catalog when credible evidence confirms active exploitation in the wild.
Background context
The Known Exploited Vulnerabilities catalog exists for a specific reason.
Many security flaws are published every year. Some are theoretical. Others are rarely used.
But a smaller group becomes part of real attacks.
Those are the vulnerabilities that matter most.
When CISA warns of actively exploited vulnerabilities, the agency requires federal agencies to patch them within defined deadlines.
Federal Civilian Executive Branch agencies have been ordered to apply the fix for SolarWinds Web Help Desk (CVE-2025-26399) by March 12, 2026, and the remaining vulnerabilities (CVE-2026-1603 and CVE-2021-22054) by March 23, 2026.
The objective is simple.
Reduce the window of opportunity for attackers.
How Attackers Are Exploiting These Vulnerabilities
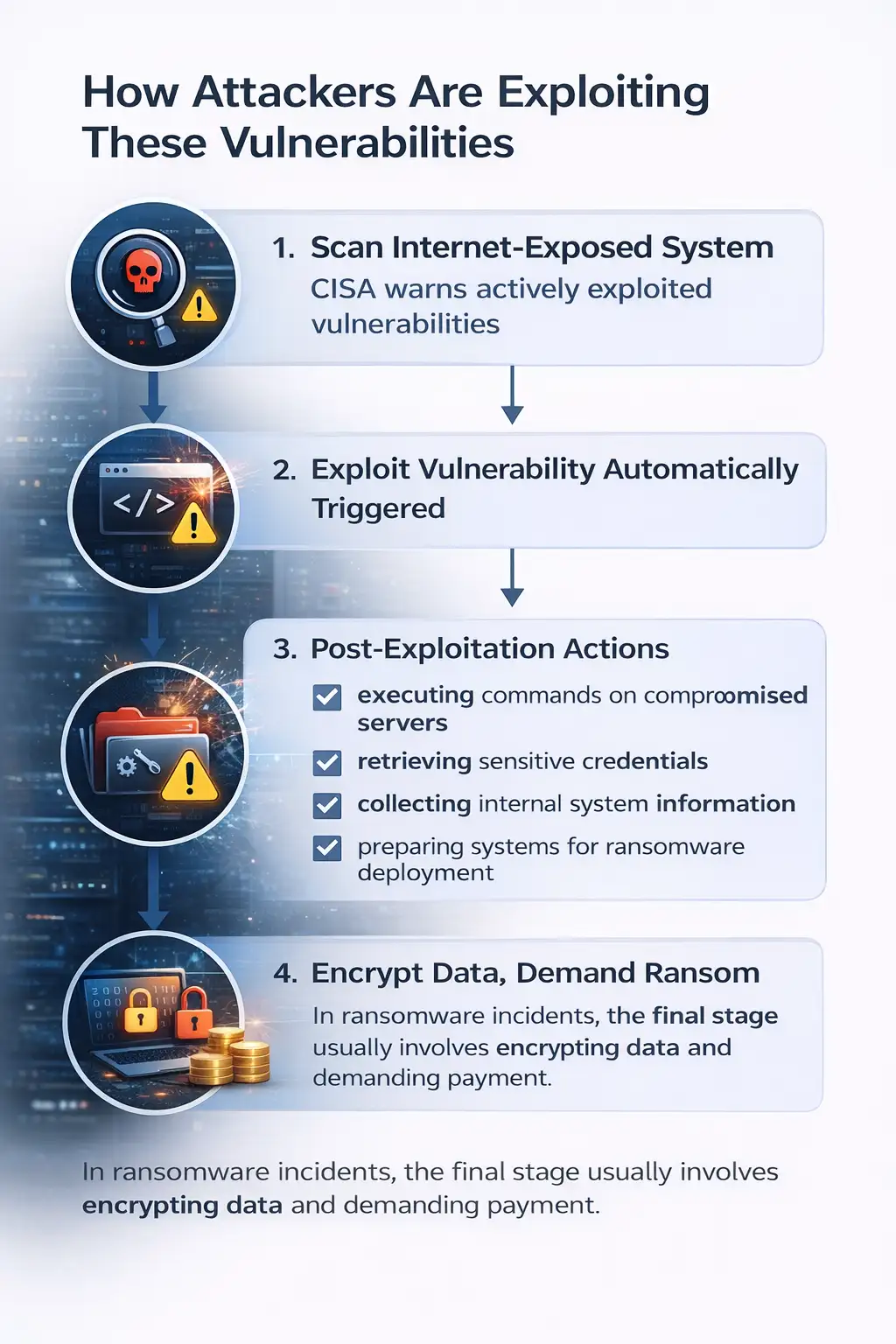
When analyzing incidents tied to these products, security researchers observed several common attack patterns.
Attackers often begin with an initial foothold. They scan internet-exposed systems searching for outdated versions of software.
Once a vulnerable system is discovered, exploitation scripts may attempt to trigger the weakness automatically.
After gaining access, attackers may attempt actions such as
• executing commands on compromised servers
• retrieving sensitive credentials
• collecting internal system information
• preparing systems for ransomware deployment
Each step helps attackers expand their control.
In ransomware incidents, the final stage usually involves encrypting data and demanding payment.
Before vs. After a Patch
Consider a mid-sized company running an internal help desk system.
Before patching
The organization continues operating normally.
However, the SolarWinds Web Help Desk vulnerability remains exposed.
An attacker scans the internet and discovers the outdated instance.
Within minutes, they exploit the deserialization weakness and gain system access.
From there they attempt to move across the network.
After patching
The vulnerability is removed.
The attacker attempts the same exploit but fails because the patched system rejects the malicious request.
The difference between those two outcomes often depends on how quickly organizations respond to alerts where CISA warns of actively exploited vulnerabilities.
Who is Most Affected by These Security Issues?
The impact varies across different groups.
Enterprise organizations
Large companies using SolarWinds help desk tools or endpoint management platforms may face operational disruption if attackers gain access.
Government agencies
Federal civilian agencies must follow strict patching deadlines when vulnerabilities enter the KEV catalog.
Managed service providers
MSPs manage infrastructure for multiple clients. A compromised management tool could affect several organizations simultaneously.
Security professionals
Incident responders and threat analysts must monitor these vulnerabilities closely because they can indicate early stages of an attack.
Benefits and Limitations of the KEV Alert System
The KEV catalog plays an important role in improving cybersecurity response.
Benefits
• Provides a prioritized list of vulnerabilities already exploited by attackers
• Helps organizations focus patching resources where they matter most
• Improves coordination between government and private sector security teams
However, the system also has limitations.
Not every exploited vulnerability is immediately discovered. Some campaigns operate quietly for months.
That means security teams must still rely on broader monitoring, not only the KEV list.
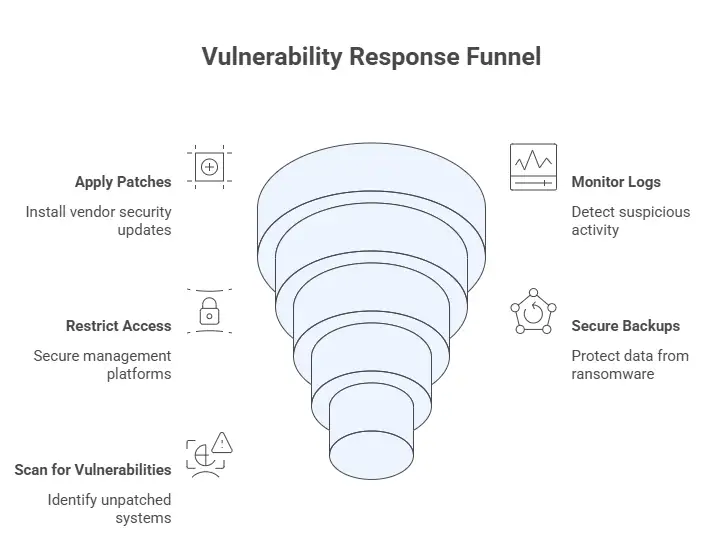
What Organizations Should Do Right Now
Security teams often ask the same question when CISA warns of actively exploited vulnerabilities.
What should we do immediately?
Here are practical steps based on official recommendations.
• Apply vendor security patches for affected products
• Monitor logs for suspicious activity related to the vulnerabilities
• Restrict network access to sensitive management platforms
• Ensure backup systems are secure in case ransomware attacks occur.
• Implement vulnerability scanning to detect unpatched systems
These actions reduce risk significantly.
How Modern Security Programs Are Changing
Traditional security programs relied heavily on periodic updates.
That approach worked when attack cycles were slower.
Today threats move faster.
A vulnerability may be exploited within hours of public disclosure.
Organizations increasingly rely on threat intelligence monitoring and automated patch management.
Security teams also use endpoint detection tools to identify abnormal behavior after an intrusion attempt.
Solutions like those implemented by Hoplon Infosec help organizations monitor vulnerability alerts, identify affected systems quickly, and coordinate remediation efforts.
The focus is not only on patching but also on early detection.
Frequently Asked Questions
What does it mean when CISA warns of actively exploited vulnerabilities?
It means security researchers have confirmed attackers are using the vulnerability in real attacks. These issues are added to the Known Exploited Vulnerabilities catalog and require rapid patching.
Which products are affected in the latest alert?
The vulnerabilities involve SolarWinds Web Help Desk, Ivanti Endpoint Manager, and Omnissa Workspace One UEM.
Are attackers already exploiting these vulnerabilities?
Yes. Evidence from security researchers and threat intelligence sources indicates active exploitation in some cases.
Why are KEV catalog vulnerabilities important?
They represent security flaws that attackers have already weaponized. Organizations should treat them as high-priority patching tasks.
Can small businesses be affected?
Yes. Any organization running the vulnerable software may be at risk if patches are not applied.
Summary
The latest alert, where CISA warns of actively exploited vulnerabilities, highlights three serious weaknesses affecting SolarWinds, Ivanti, and Workspace One systems.
These vulnerabilities are not theoretical. Security researchers have observed real exploitation attempts, which is why they were added to the Known Exploited Vulnerabilities catalog.
Organizations that patch quickly reduce the risk of ransomware attacks and credential theft.
Security providers such as Hoplon Infosec support organizations by monitoring threat intelligence, identifying vulnerable assets, and coordinating response strategies that help businesses stay ahead of evolving threats.
Organizations often discover vulnerabilities only after attackers attempt exploitation. A proactive security program changes that.
Recommended approach:
• Continuous vulnerability monitoring
• Rapid patch deployment workflows
• Threat intelligence integration
• Endpoint activity monitoring
Hoplon Infosec helps security teams identify vulnerabilities earlier and respond faster before attackers gain a foothold.
For more latest updates like this, visit our homepage.
Sources
CISA Known Exploited Vulnerabilities Catalog
Microsoft Threat Intelligence Reports
GreyNoise Threat Intelligence
Was this article helpful?
React to this post and see the live totals.
Share this :