Cisco Secure Firewall Management RCE Vulnerability Exposed

Hoplon InfoSec
05 Mar, 2026
Introduction
RCE Vulnerability in Cisco Secure Firewall Management For a long time, many companies thought of firewall management platforms as internal systems that didn't need to be watched closely very often.
In the past, firewall management consoles were used internally and were trusted by default. New reality: attackers can run commands from a distance if management software has security holes. Result: one flaw can make the system that is supposed to protect a network useless.
The Cisco Secure Firewall Management RCE Vulnerability is an example of why management infrastructure is now a big target for hackers. Attackers who get into firewall management systems may be able to set their own network security rules.
Cisco Secure Firewall Management RCE Vulnerability
What transpired Security researchers found a serious problem with the Cisco Secure Firewall Management Center software. Later, Cisco confirmed the vulnerability in an official advisory.
The flaw lets attackers send specially crafted requests that could let them run commands on affected systems from afar. The problem is known as CVE-2025-20265, and it has a CVSS score of 10.0, which is the highest possible severity rating.
That score means something important. This is not a small bug. It means that the whole system is at risk of being hacked.
About Firewall Management Center
About the Firewall Management Center The Cisco Secure Firewall Management Center (FMC) is a single place where you can manage all of your Cisco firewalls in your business. Administrators can manage security policies from one console instead of setting up each firewall separately.
Some common functions are:
• Managing firewall policies
• setting up intrusion detection
• watching traffic
• combining threat intelligence
FMC is very important for enterprise network security because it controls many firewall devices.
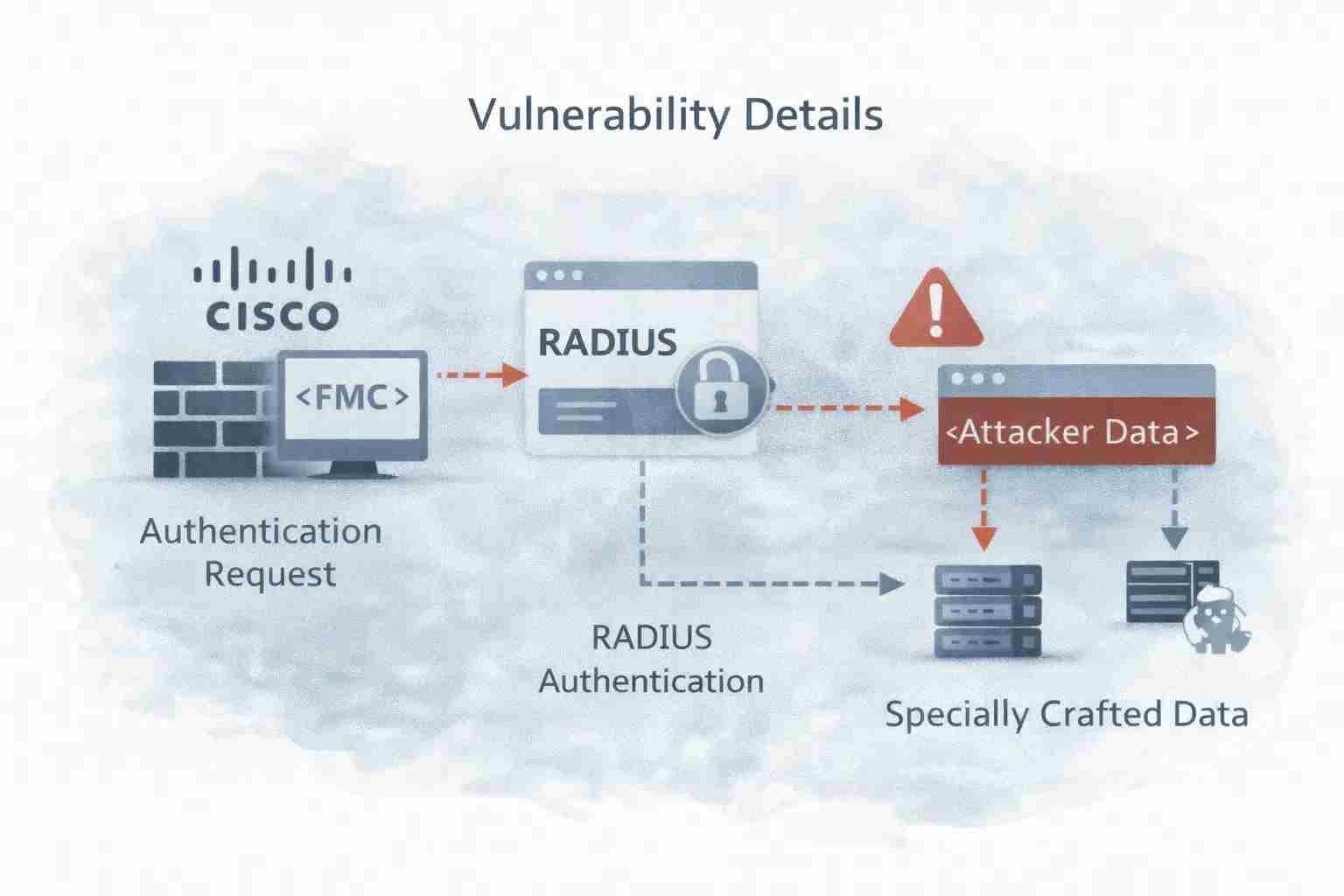
Vulnerability Details
Information about the vulnerability The RADIUS authentication subsystem has the Cisco Secure Firewall Management RCE vulnerability. In business settings, RADIUS is often used for centralized login authentication.
When administrators try to log in, the system sends requests for authentication to a RADIUS server. Researchers, on the other hand, found that the system doesn't properly clean up some inputs during this process. Because of that mistake, specially crafted data can get into the backend system without being checked.
Root Cause
The root cause The main reason for the vulnerability is not checking the input correctly. Before the system can process user input, it must always be cleaned up. In this case, bad input can get to the parts of the operating system that run commands.
Once the input reaches that level, it may be interpreted as executable commands. This changes a simple request for authentication into a command injection attack. Command injection vulnerabilities frequently result in direct remote code execution.
Affected Systems
Systems that are affected Cisco confirmed that some versions of its Secure Firewall Management Center software are vulnerable. Versions that are affected are
• Version 7.0.7 of FMC
• Version 7.7.0 of FMC
But exploitation needs a certain setup. When RADIUS authentication is turned on for management access, the vulnerability can be used. The attack path might not be reachable if RADIUS authentication is not turned on.
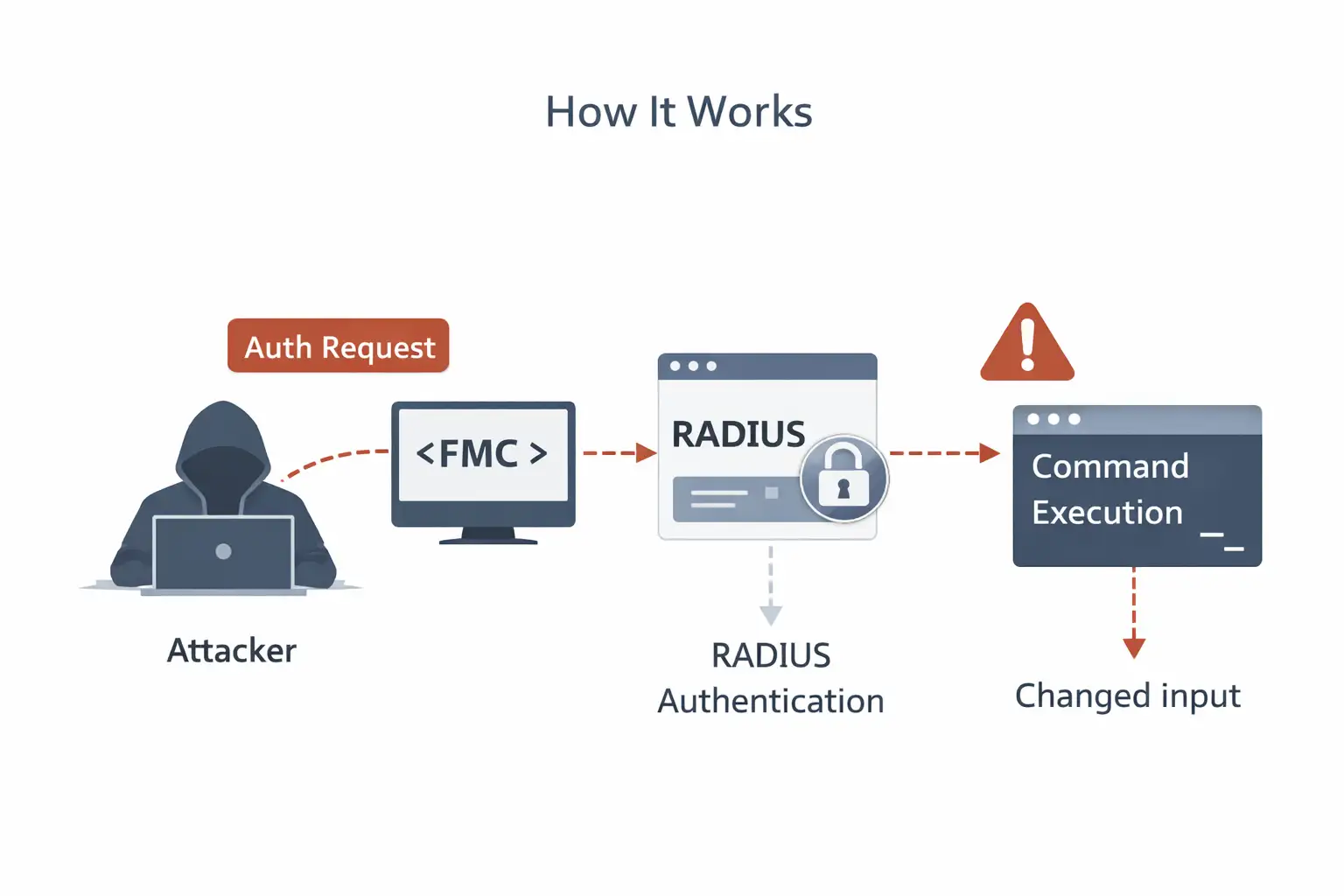
How the Exploit Works
How the exploit works There are a few steps in the attack process. To start, an attacker sends a specially made authentication request to the interface for managing the firewall. The request then goes through the RADIUS authentication system.
Third, the system doesn't handle the input correctly. Finally, the harmful input is run as a command by the system. This series of events lets attackers run any command they want on the affected device.
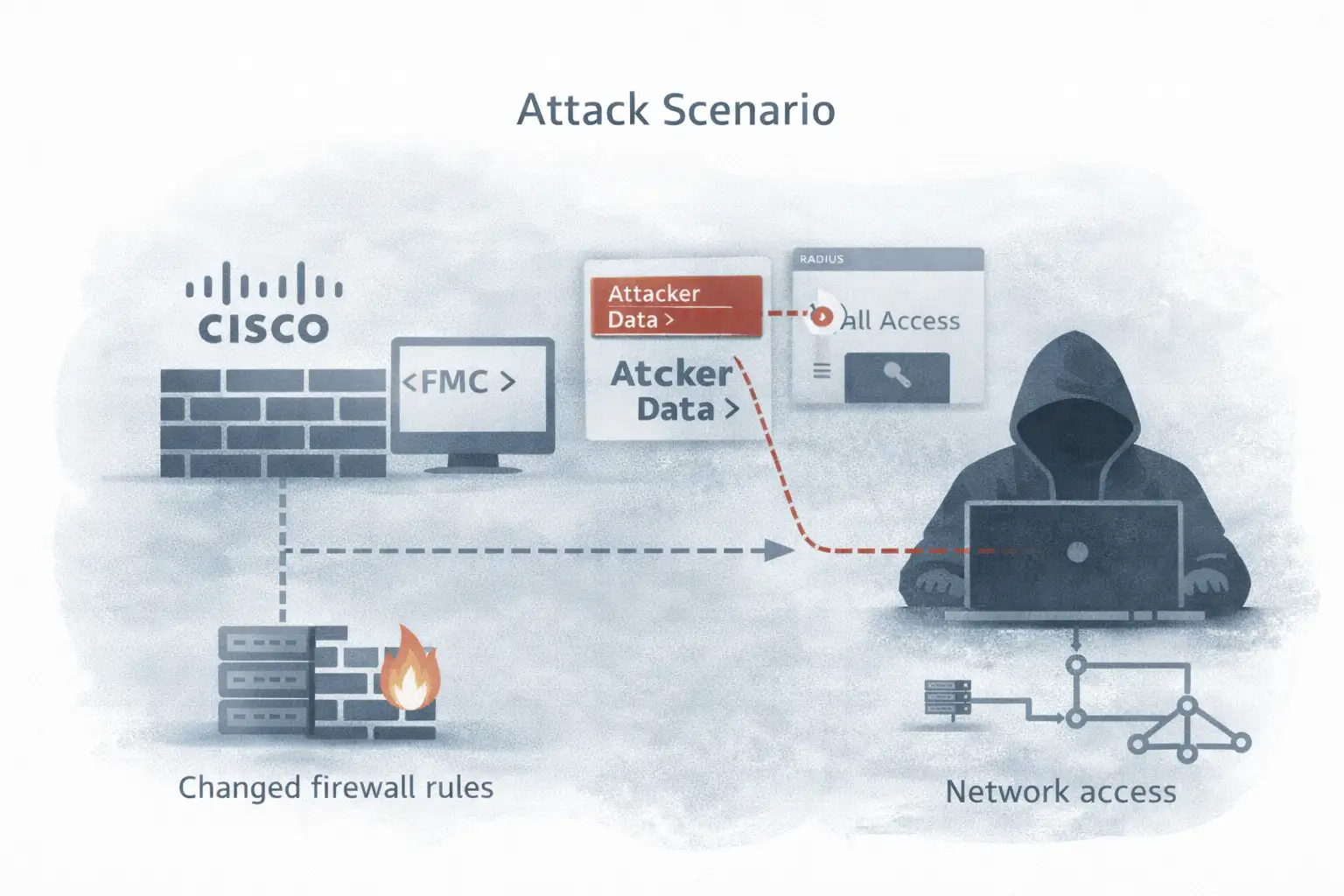
Attack Scenario
Scenario for an Attack Picture an attacker looking for open firewall management interfaces on a business's network. If the attacker finds an FMC instance that uses RADIUS authentication, they might try to take advantage of the security hole.
The attacker sends harmful authentication data that is meant to start command execution. If the attack works, the attacker can get shell access to the system. From there, they can change the rules for the firewall or make it possible to always access the network.
Real World Impact
Effect on the Real World If someone takes advantage of the Cisco Secure Firewall Management RCE Vulnerability, the results could be very bad. If attackers get control of a firewall management platform, they might be able to change security policies for the whole network.
Some possible effects are:
• changing the rules for the firewall
• turning off security features
• Getting data about how the network is set up.
• Making new accounts for administrators
A compromise could affect a lot of a network because FMC controls more than one firewall.
Who is Affected
Who is Affected? The weakness affects many kinds of businesses. Large companies are at risk because they often manage their firewalls from one place. Managed security service providers might also be affected because they handle infrastructure for more than one client.
Another group that often uses centralized firewall management platforms is government agencies and operators of critical infrastructure. For these groups, a breach of management systems could have serious effects.
Cisco Response
Cisco's Answer Cisco's answer was to put out an official security advisory that explained the flaw. The advisory gives information about the products that are affected, how bad the problem is, and how to fix it. Cisco said that there are software updates that can fix the problem.
Cisco said that at the time of the advisory, there was no proof that the vulnerability was being actively used in the wild. But because the severity score is so high, businesses should quickly apply patches.
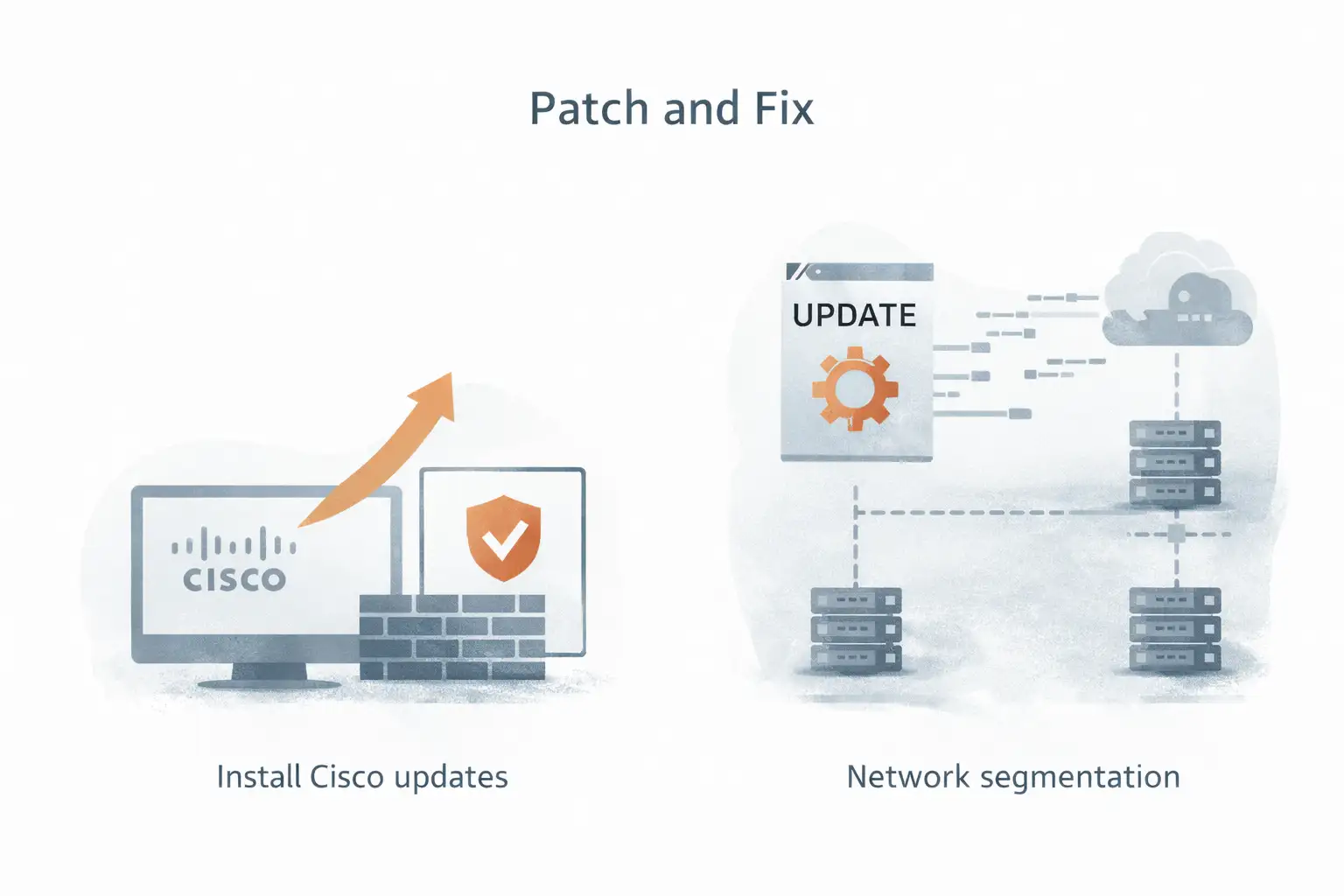
Patch and Fix
Fix and Patch Installing the most recent software updates from Cisco is the best way to fix the problem. These updates fix the flaw in the authentication processing that lets command injection happen. Updating any FMC deployments that are vulnerable should be the top priority for security teams.
If patching right away isn't possible, administrators should limit access to the management interface. Until updates are installed, network segmentation can help keep things safe.
Security Risks
Risks to Security Vulnerabilities that let remote code execution happen are some of the most serious threats to cybersecurity. RCE flaws are different from most other vulnerabilities because they let attackers run commands directly on the target system. That ability can lead to a complete breach of the system.
Firewall management platforms control the security infrastructure of the network, so the effects may go beyond just one device.
Detection Tips
How to Find Things Security teams should keep an eye on authentication logs for strange behavior. Unexpected authentication attempts or strange command execution could be signs of possible exploitation.
You can also use network monitoring tools to find strange access to management interfaces. Regularly looking at logs helps security teams find possible attacks before they happen.
Mitigation Steps
Steps to Reduce Risk To lower risk, businesses should do a number of things.
• Install Cisco software updates right away.
• Check the settings for authentication.
• Limit who can use management interfaces.
• Keep an eye on authentication logs.
• do assessments of vulnerabilities
These steps help lower the chances of being taken advantage of.

Best Practices
Best Ways to Do Things This event shows how important it is to have good security measures in place. Management systems should never be connected to public networks.
Only trusted internal networks or VPN connections should be able to access it. Security teams should also regularly check for security holes and keep their patches up to date. These steps lower the chances of similar weaknesses happening in the future.
Security Lessons
Lessons in Security The Cisco Secure Firewall Management RCE Vulnerability is a good reminder. The security infrastructure itself can be a target for attacks.
Companies often put their main focus on keeping servers, applications, and endpoints safe. But attackers are more and more going after management systems that control security tools. Making sure those systems are safe should be a top priority.
Conclusion
In conclusion, The Cisco Secure Firewall Management RCE Vulnerability shows how a problem with how authentication is handled can put important network infrastructure at risk. Exploitation could have serious effects because firewall management platforms control security policies on many devices.
Companies that use Cisco Secure Firewall Management Center should check their deployments and install the most recent updates from Cisco. To keep business infrastructure safe, proactive patching, monitoring, and network segmentation are still very important.
FAQ
What is the Cisco Secure Firewall Management RCE security hole?
This is a serious security hole that lets attackers run commands from a distance on Cisco Secure Firewall Management Center systems that are not protected.
What Cisco products are affected?
When RADIUS authentication is turned on, the vulnerability only affects certain versions of Cisco Secure Firewall Management Center software.
How can attackers take advantage of the flaw?
Attackers can send authentication requests that are made to take advantage of the RADIUS authentication subsystem's lack of proper input validation.
How can companies fix the problem?
Installing the most recent security updates from Cisco is the main way to fix the problem.
For more latest updates like this, visit our homepage.
Was this article helpful?
React to this post and see the live totals.
Share this :