Claude Mythos Firefox Vulnerabilities: 271 Bugs Found

Hoplon InfoSec
23 Apr, 2026
Did Claude Mythos really help uncover 271 Firefox security issues?
Yes. Mozilla says Anthropic’s Mythos Preview helped identify and fix 271 vulnerabilities in Firefox 150, and multiple reputable reports support that core claim.
The caution is in the label. Some headlines lean on “zero-day,” but the strongest sourced version is that 271 vulnerabilities were found and addressed, not that all 271 were confirmed to be exploited in the wild.
That difference matters. A lot. If you are a regular Firefox user, the immediate lesson is simple: update the browser.
If you run security for a business, the lesson is bigger: AI found Firefox vulnerabilities at a pace that forces defenders to rethink how code review, triage, and patching work.
Technical Overview
|
Item |
What is confirmed |
What is still uncertain |
|
Model involved |
Anthropic Mythos Preview |
Full internal methodology is not public |
|
Vendor affected |
Mozilla Firefox |
Exact full list of all bug classes is not public |
|
Reported count |
271 vulnerabilities |
Public per-bug breakdown is not complete |
|
Product version cited |
Firefox 150 |
Whether every report maps neatly to one release branch |
|
Earlier related finding |
Claude Opus 4.6 found 22 Firefox vulnerabilities in February 2026 |
How much workflow changed between Opus and Mythos |
|
Zero-day claim |
Mythos is described by Anthropic as capable of finding and exploiting serious zero-days across major browsers and OSes |
Public reporting does not confirm all 271 were live exploited zero-days in Firefox |
What Happened
Mozilla’s side of the story is the anchor here. Its engineers describe receiving bug reports from Anthropic’s frontier red team that included minimal test cases, which made verification faster and more credible than the usual flood of low-quality AI-generated security submissions.
That is a critical detail because Mozilla Firefox AI vulnerability detection only matters if maintainers can reproduce the problem and ship a fix.
The broad media version is simpler: Anthropic Mythos Firefox became headline news because Mozilla said 271 vulnerabilities were identified and addressed in Firefox 150. That number is large enough to reframe the conversation.
We are no longer talking about a novelty demo. We are talking about industrial-scale vulnerability discovery against a mature browser codebase.
Why this is bigger than a routine browser update
- Firefox is not a neglected codebase
- Browser engines already receive heavy scrutiny
- Coordinated disclosure and patching worked here
- The discovery rate still shocked the industry
What is Claude Mythos?
Claude Mythos is not being described as a normal chatbot. Anthropic’s own security material frames Mythos Preview as a cyber-capable model able to identify and exploit serious zero-day vulnerabilities across major operating systems and major browsers when instructed to do so. That is why access has been tightly restricted.
This is where Claude Mythos cybersecurity moves from marketing phrase to policy problem. If a model can generate research-grade findings at speed, access control becomes part of product safety.
The same reporting cycle also included scrutiny over unauthorized access concerns around Mythos, which adds another layer of urgency to the story.
What makes Mythos different
- It is positioned as a frontier cyber model
- It is not broadly released
- It is tested for offensive and defensive cyber capability
- Its risk profile is part of the public story, not just its performance
How Claude Mythos Found 271 Firefox Vulnerabilities
The exact internals are not public, but the workflow is easier to understand than the hype makes it sound. Anthropic’s earlier collaboration notes show that models can scan for subtle bug patterns, propose proofs of concept, and generate reports that engineers can verify. Mozilla then decides what warrants a valid bug, what can be reproduced, and what gets patched.
That is why the best framing is not “AI replaces researchers.” The stronger framing is this: AI found Firefox vulnerabilities faster than a human-only process likely could, but human engineers still handled validation, patch quality, prioritization, and release management. In other words, Claude Mythos security bugs became useful because the receiving team had the discipline to process them.
Likely workflow behind the finding surge
- Large-scale code inspection
- Pattern matching on dangerous logic paths
- Reproducible test case generation
- Human review and bug triage
- Patch development and release integration
That hybrid model is probably the real story behind how Claude Mythos found 271 Firefox vulnerabilities.
Were These Really Zero-Day Vulnerabilities?
This is the part most articles blur. A zero-day is generally a vulnerability unknown to the vendor before disclosure. An actively exploited zero-day is narrower. It means attackers are already using it in the wild. Public coverage here supports the first category more strongly than the second.
So when readers ask, did Claude Mythos find zero-day bugs in Firefox, the careful answer is: very likely some of the findings fit zero-day logic before disclosure, and Anthropic clearly says Mythos can identify and exploit serious zero-days. But public reporting does not establish that all Firefox 271 vulnerabilities were active real-world exploit cases before Mozilla fixed them.
Keep these distinctions clear
- Vulnerability: a security weakness
- Security bug: often used loosely for a vulnerability
- Zero-day: unknown to the vendor at discovery time
- Exploited zero-day: already used by attackers in the wild
That nuance is essential when discussing Claude Mythos zero-day vulnerabilities and zero-day vulnerabilities in Firefox.
Why This Matters
For regular users, this story is about patching. Update Firefox and move on. For organizations, it is about volume. A security team can survive one serious browser bug. Hundreds of findings discovered in compressed time create a triage and staffing problem. That is a different class of pressure.
For open source, the warning is even sharper. Wired’s reporting highlighted the uncomfortable truth: large vendors may be able to absorb AI-scale vulnerability discovery, but many smaller maintainers cannot. That means AI vulnerability hunting in Firefox is not just a Firefox story. It is a preview of what happens when advanced offensive-quality discovery collides with underfunded defensive capacity.
Why businesses should care
- Browser flaws can become entry points for phishing and credential theft
- Large batches of findings overwhelm patch cycles
- AI-assisted discovery changes attacker and defender economics
- Third-party software risk becomes harder to model
Claude Mythos vs Human Security Researchers
The public quote that Mythos is comparable to elite security researchers gets attention, but the operational comparison is more useful. Humans still win on judgment, context, and knowing when a “clever” path is actually noise. Models win on scale, fatigue resistance, and repeated inspection.
That makes Claude Mythos vs human security researchers the wrong battle. The real question is which team can validate, remediate, and ship fixes faster when models keep surfacing more issues than staff can absorb.
|
Factor |
Claude Mythos |
Human Researchers |
|
Speed |
Very high |
Moderate |
|
Scale |
Massive |
Limited by time |
|
Novel pattern detection |
Strong |
Strong but slower |
|
Context judgment |
Limited |
Strong |
|
Patch validation |
Needs humans |
Strong |
This is why Anthropic AI Firefox bugs should worry defenders less as a headline and more as a workflow challenge.
Mozilla and Anthropic Timeline
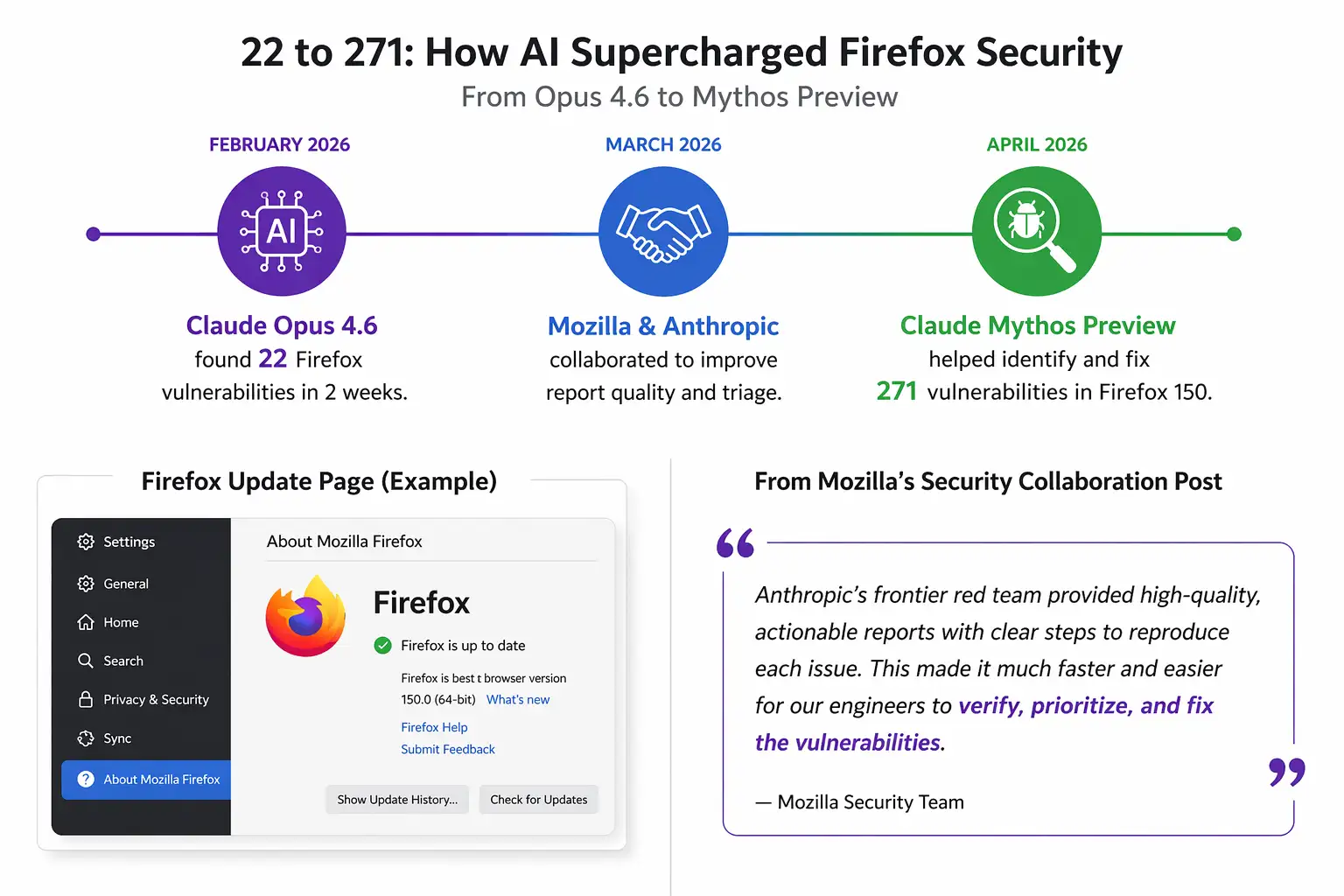
The 271 count did not appear from nowhere. Anthropic reported last month that Claude Opus 4.6 found 22 Firefox vulnerabilities in February 2026, more than were reported in any single month in 2025. Mozilla’s own blog confirms that earlier collaboration and explains why the report quality mattered.
Then came the step change. By April, the discussion shifted to Anthropic Mythos Firefox 150 vulnerabilities and the 271 total associated with Firefox 150. That is the moment the industry stopped treating this as an experimental curiosity and started treating it as a production security event.
Timeline at a glance
- February 2026: Opus 4.6 finds 22 Firefox vulnerabilities over two weeks.
- March 2026: Mozilla publicly discusses the collaboration and quality of reports.
- April 2026: Multiple outlets report that Mythos Preview helped identify and fix 271 vulnerabilities in Firefox 150.
How to Protect Your System
If you are reading this because Firefox zero-day vulnerabilities AI sounds alarming, here is the practical part.
For home users
- Update Firefox immediately from the browser’s update menu
- Restart the browser after updating
- Remove old or unused extensions
- Turn on automatic updates for the browser and OS
- Review saved passwords and enable MFA on important accounts
For IT and security teams
- Confirm your estate is on the latest Firefox release
- Use endpoint management to enforce browser updates
- Review browser extension allowlists
- Watch for browser child-process abuse in endpoint telemetry
- Re-test web apps that depend on older browser behavior
- Revisit vulnerability intake workflows for AI-generated reports
For Linux endpoints
- On Debian or Ubuntu:
- sudo apt update
- sudo apt upgrade firefox
- On Fedora:
- sudo dnf upgrade firefox
- On systems using Snap:
- sudo snap refresh firefox
Users should also refer to official advisories from Mozilla, CISA, and other vendor channels when patch guidance is published or updated.
Field Notes
When we reviewed the available reports side by side, one pattern stood out immediately: Mozilla was willing to describe the incoming reports as useful because they were reproducible. That might sound small. It is not. In real-world security operations, reproducibility is the line between signal and noise.
In our practical reading of this case, the bigger lesson is not simply that Claude Mythos Preview Firefox bugs exist. The lesson is that mature teams will soon need dedicated intake pipelines for machine-generated vulnerability research. Without that, even true positives become operational clutter.
Common pitfalls
- Assuming all 271 bugs were exploited in the wild
- Reading “AI found Firefox vulnerabilities” as “humans are obsolete”
- Ignoring browser updates because the issue sounds abstract
- Forgetting that open source maintainers may not have enterprise-grade response capacity
What This Means for Browser Security
What does what Claude Mythos means for browser security actually look like in practice?
- Browser makers will need faster validation pipelines
- Red-team AI workflows will become normal
- Smaller projects may struggle unless funding follows the risk
- Disclosure policy will need to adapt to machine-scale discovery
The earlier Mozilla collaboration already hinted at this. The 271 figure simply made it impossible to ignore.
Our recommendation
- Treat this as a defense operations story, not just an AI story
- Build a process for handling high-volume machine-generated findings
- Prioritize browser hygiene in endpoint hardening
- Watch the open source funding question closely
Research note
A useful external benchmark for the broader risk conversation is the Cloud
Security Alliance research note discussing Mythos and autonomous offensive
capability, though that document itself states it was AI-assisted and
unofficial, so it should be treated as context, not primary proof.
Security Checklist
- Update Firefox now on every managed and unmanaged endpoint.
- Audit browser extensions and remove anything unneeded.
- Review your vulnerability workflow because AI-assisted discovery volume is now a real operational risk.
Published: April 23, 2026
Last updated: April 23, 2026
Author: Radia | Senior Cybersecurity Analyst & Breach Reporter.Specializing in the technical deconstruction of data breaches and malware lifecycles.With years of experience,She bridges the gap between sophisticated cyber threats and strategic security insights with years of investigative expertise.
Frequently Asked Questions
Was this article helpful?
React to this post and see the live totals.
Share this :