Cybersecurity vs Information Security: 7 Key Differences
Hoplon InfoSec
17 Apr, 2026
Is cybersecurity vs. information security just a wording difference in 2026?
No. As of April 2026, trusted sources such as NIST and CISA
still support a meaningful distinction: information security
protects information in any form, while cybersecurity focuses
on protecting digital systems, networks, devices, and the information they
process from cyber threats.
People mix these terms up because they overlap all the time. The same company may use a data classification policy, badge access, email encryption, MFA, EDR, and cloud monitoring to protect one business process.
Some of those controls sit under information security. Some sit under cybersecurity. In the real world, they meet in the middle.
Our team looks at this distinction the way a security program should look at it: by following the asset.
Where does the information live? Who can access it? What can go wrong? What control reduces the risk fastest?
That approach makes this topic far easier to understand than the usual “bigger umbrella” explanation.
Quick answer
Information security protects information in all forms. That includes digital files, paper records, verbal communication, internal documents, intellectual property, and the systems that store or move that information.
NIST’s glossary ties this directly to confidentiality, integrity, and availability, the core security objectives often called the CIA triad.
Cybersecurity protects digital environments. Think networks, cloud platforms, laptops, servers, endpoints, SaaS apps, mobile devices, and the data processed inside them.
CISA describes cybersecurity around understanding cyber risk and defending against cyberattacks, while NIST’s CSF 2.0 frames it as a risk-based practice for managing cybersecurity outcomes across the organization.
So yes, information security vs cybersecurity is a real distinction. One is broader. One is more digitally focused. Mature organizations need both.
Cybersecurity vs Information Security
|
Aspect |
Cyber Security |
Information Security |
|
Definition |
The practice of protecting systems, networks, devices, and digital data from cyber attacks. |
The practice of protecting information from unauthorized access, use, disclosure, modification, or destruction. |
|
Main Focus |
Protecting assets in cyberspace and digital environments. |
Protecting information itself, regardless of its form or location. |
|
Scope |
Limited mainly to digital and online environments. |
Broader scope covering both digital and physical information. |
|
Objective |
To defend against cyber attacks and ensure safe use of cyberspace. |
To ensure confidentiality, integrity, and availability of information. |
|
Type of Threats |
Hacking, malware, phishing, cyber fraud, cybercrime, APTs, and other online attacks. |
Unauthorized access, disclosure, alteration, disruption, insider threats, espionage, human error, and physical theft. |
|
Realm of Protection |
Focuses only on the cyber realm. |
Applies to all information assets, whether digital, paper-based, or verbal. |
|
Security Approach |
Concentrates on protecting systems, networks, applications, and online accounts. |
Concentrates on protecting data, documents, intellectual property, trade secrets, and confidential records. |
|
Role in Defense |
Often acts as the first line of defense against digital attacks. |
Provides the overall framework for securing information before, during, and after incidents. |
|
Professional Responsibility |
Professionals focus on preventing, detecting, and responding to active cyber threats. |
Professionals focus on policies, processes, governance, compliance, and access management. |
|
Tools and Technologies |
Firewalls, antivirus software, IDS/IPS, SIEM, endpoint protection, and threat monitoring tools. |
Encryption, access controls, data loss prevention, backup controls, classification systems, and audit controls. |
|
Skills Required |
Knowledge of computer systems, networks, programming, and cyber defense techniques. |
Knowledge of risk management, compliance, legal/regulatory issues, governance, and technical controls. |
|
Threat Environment |
Deals with fast-changing and evolving cyber threats. |
Deals with a wide range of threats including digital, physical, and human-related risks. |
|
Relationship |
Considered a subset of Information Security. |
Considered the broader field that includes Cyber Security. |
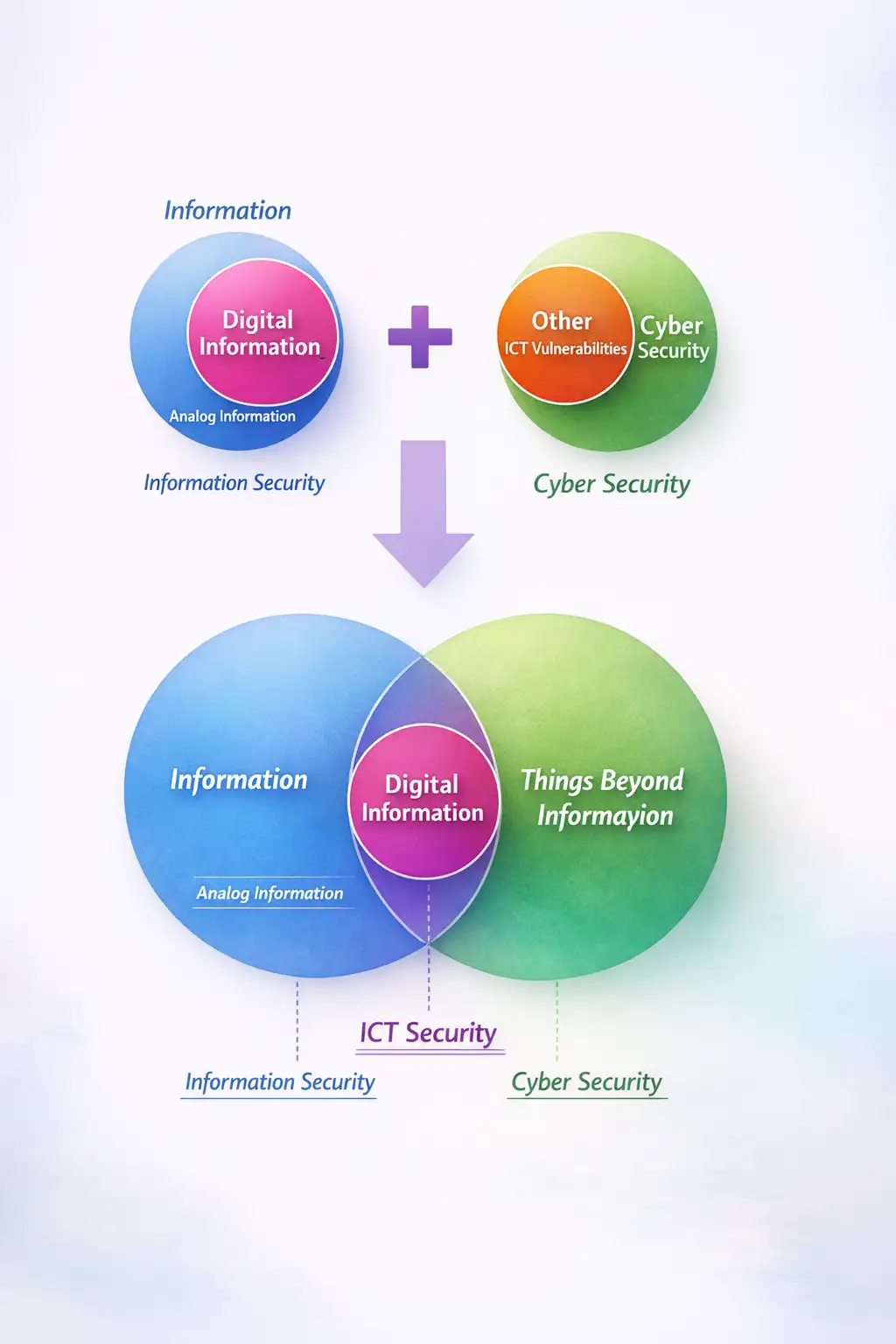
What information security covers
Information security starts with the value of the information itself. It does not care whether the asset sits in SharePoint, a printed invoice, a contract folder, a voice memo, or a whiteboard photo sent over chat. If the information matters to the business, it falls into scope.
That is why the difference between cybersecurity and information security is not just technical. Information security includes administrative controls and physical safeguards that never show up in a SOC dashboard.
A locked file room, records retention policy, NDA process, clean desk rule, classification label, and approved destruction workflow all sit comfortably inside an information security program.
NIST’s definition supports that broader frame because the objective is to preserve confidentiality, integrity, and availability across information and systems.
In our practical work, this is where many teams underestimate risk. They secure the cloud tenant but forget the exported report. They protect the inbox but not the printed board packet. They deploy encryption but skip data handling policy. Then an incident starts with something boring, not something cinematic.
What cybersecurity covers
Cybersecurity is narrower in scope and deeper in technical defense. It deals with hostile activity in digital environments: phishing, credential theft, ransomware, exploitation of internet-facing devices, malicious scripts, abuse of remote access, and compromised third-party software.
CISA’s public guidance focuses heavily on those operational risks, and NIST CSF 2.0 is structured around managing cyber outcomes rather than just writing policy.
This is the side of security that usually owns tools such as MFA, EDR, SIEM, vulnerability management, email security, cloud logging, identity monitoring, and incident response.
If an attacker is trying to break into the system, persist, move laterally, or encrypt production data, cybersecurity is in the hot seat.
A lot of readers searching "What is cybersecurity vs. information security?" are really asking a career question in disguise.
They want to know whether they are walking into policy and risk work or into hands-on defense. That is a fair question, and the answer becomes clearer once you look at the seven differences below.
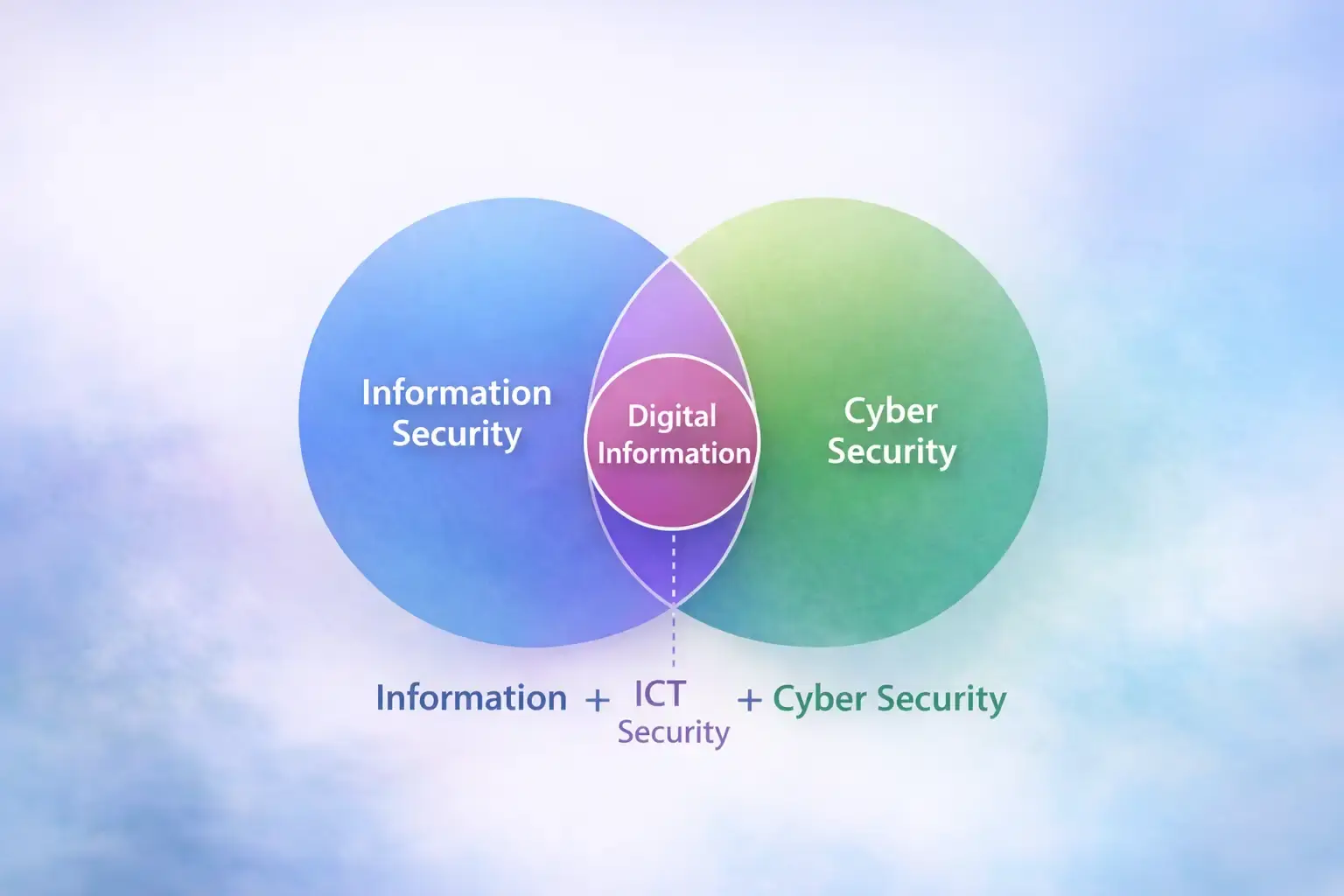
The biggest difference
Information security protects information wherever it exists. Cybersecurity protects the digital environments where that information is processed, stored, and attacked.
That one line clears up most of the confusion. It also explains why cybersecurity and information security overlap so often in modern organizations.
Most valuable information now touches a digital system at some point, even when it also exists in paper or verbal form.
7 key differences
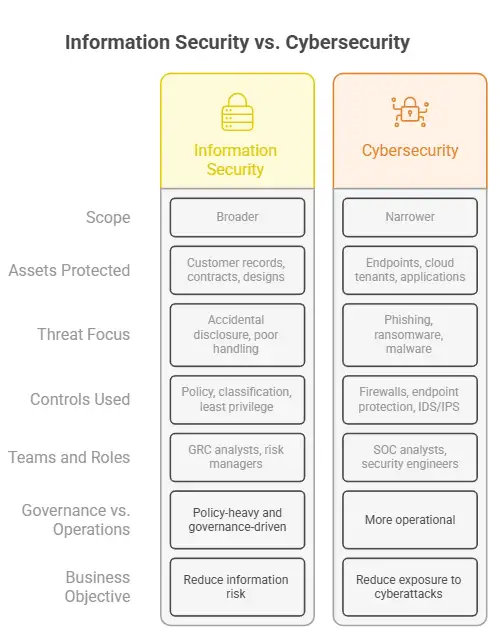
1. Scope
Information security is broader. It covers digital, physical, and administrative protection of information.
Cybersecurity is narrower. It focuses on digital assets and cyber threats. That is the heart of information security vs. cybersecurity scope.
2. Assets protected
Information security protects customer records, contracts, designs, emails, source documents, recordings, and intellectual property in any form.
Cybersecurity protects endpoints, cloud tenants, applications, servers, networks, and identity systems. That is the real cybersecurity and information security difference in practice.
3. Threat focus
Information security worries about accidental disclosure, poor handling, over-permissioning, physical theft, insider misuse, and governance failures.
Cybersecurity is built for phishing, ransomware, malware, zero-day exploitation, credential abuse, and attacker behavior on systems.
Verizon’s 2025 DBIR says exploitation of vulnerabilities increased 34%, ransomware appeared in 44% of breaches, and human involvement remained high.
4. Controls used
Information security leans on policy, classification, least privilege, retention, encryption, training, and audit.
Cybersecurity leans on firewalls, endpoint protection, IDS/IPS, patching, email filtering, logging, and incident response workflows.
5. Teams and roles
Information security roles often include GRC analysts, risk managers, auditors, privacy teams, and security managers.
Cybersecurity roles often include SOC analysts, security engineers, incident responders, threat hunters, and penetration testers.
BLS groups information security analysts under one of the faster-growing occupations in the U.S., with 29% projected growth from 2024 to 2034.
6. Governance vs. operations
Information security is often policy-heavy and governance-driven.
Cybersecurity is more operational. It has to detect, block, contain, and recover. One writes rules. The other fights fires. Both matter.
7. Business objective
Information security tries to reduce information risk across the whole organization.
Cybersecurity tries to reduce exposure to cyberattacks and improve the resilience of digital operations.
Where they overlap
This part matters more than the difference.
Both disciplines protect confidentiality, integrity, and availability. Both use access control, encryption, monitoring, and training.
Both support enterprise risk management, compliance, and continuity planning. NIST’s definitions and CSF materials reinforce that these are not competing ideas. They are connected layers of the same security program.
When we ran internal reviews on client environments, the most common pattern was not “bad cybersecurity” alone. It was a mismatch. Strong tools, weak governance. Or strong policy, weak enforcement.
A board-approved classification scheme means little if every SaaS app is over-permissioned. The reverse is also true. A great EDR will not save you from sensitive reports being sent to personal email.
Is cybersecurity part of information security?
Usually, yes.
Most educational and professional resources treat cybersecurity as a subset or specialized branch of information security. Forbes, Coursera, University of Phoenix, and the NIST/CISA framing all point in that direction, even if organizations use the terms loosely in job titles and internal org charts.
A simple hierarchy looks like this:
· Information Security
o Cybersecurity
o Physical security
o Administrative controls
o Data governance
o Compliance and audit
That answers another common search: is cybersecurity part of information security? In most contexts, yes.
Real-world examples
Take employee records. A locked HR cabinet, a records retention rule, and an access approval workflow belong to information security. The HR portal’s MFA, access logs, and endpoint protection belong to cybersecurity.
Take a customer database. The classification rule that defines what is sensitive is information security. The database firewall, secrets management, and monitoring stack are cybersecurity.
Take email compromise seriously. The acceptable use policy and role-based access model are part of information security. Anti-phishing controls, conditional access, and mailbox anomaly detection are cybersecurity measures.
Take a printed contract left in a meeting room. That is information security. It may have nothing to do with cybersecurity at all. This is where information security vs. cybersecurity examples become useful, because the distinction stops feeling abstract.
Why this matters
A lot of businesses overspend on tools and underspend on discipline. Then they act surprised when the breach starts with a human mistake, a third party, or data that moved outside the monitored environment.
IBM’s 2024 research put the average global data breach cost at $4.88 million. That number is not just a technology story. It is also a governance story.
Our view is simple. If you frame every security problem as a cyber problem, you will miss non-digital exposures. If you frame every problem as policy, you will move too slowly when attackers are active. The real win comes from choosing the right lens at the right moment.
In one tabletop exercise we ran, the initial scenario was a phishing email. Nothing unusual there. The technical team focused on blocking the sender, checking mailbox rules, and reviewing endpoint telemetry. All valid. But the bigger weakness turned out to be outside the tool stack.
A finance user had exported sensitive payment data to a spreadsheet, saved it locally, printed a copy for review, and shared a screenshot over an unapproved channel. The cyber controls caught the inbox threat. The information security gaps created the business risk. That is why cybersecurity vs. information security is not a cosmetic debate. It changes where you look first.
We also noticed a pattern during access reviews. Teams were good at detecting malicious sign-ins but poor at asking a basic question: should this person have access at all? Cybersecurity can catch abuse. Information security helps prevent unnecessary exposure before the abuse starts.
Business use cases
Small businesses usually need a lightweight but disciplined mix. Secure email, MFA, endpoint protection, backups, and patching handle the cyber side. Basic policies for file sharing, retention, access approvals, and document handling cover the information side.
Enterprises need a more formal split of responsibilities. Cyber teams run detection, response, architecture, and threat reduction.
Information security leaders shape classification, governance, audit, risk acceptance, vendor controls, and policy.
In regulated sectors such as healthcare and finance, that balance becomes even more important because the risk includes privacy failures, legal exposure, and operational disruption.
Startups often lean too hard in one direction. Some build fast and skip governance. Others produce policies nobody can operationalize.
The better path is simple: protect the highest-value information first, then map the digital attack paths around it.
Careers, skills, and certifications
If you like governance, compliance, risk, privacy, and business process design, information security may fit better.
Roles can include Information Security Analyst, GRC Analyst, Risk Analyst, Compliance Manager, and Security Auditor.
If you like systems, detection, incident response, hardening, and troubleshooting under pressure, cybersecurity may fit better.
Roles can include SOC Analyst, Security Engineer, Incident Responder, Penetration Tester, and Cloud Security Engineer. That covers the usual interest around cybersecurity vs. information security careers and information security vs. cybersecurity jobs.
The strongest shared skills are risk assessment, IAM, networking fundamentals, security awareness, encryption, vulnerability management, and incident response thinking.
On certifications, the governance side often values CISSP, CISM, CRISC, and ISO 27001 knowledge, while the cyber side often values Security+, CySA+, GIAC, and platform-specific cloud security certifications.
These are common market signals, though hiring managers still care heavily about actual experience.
Common pitfalls
One mistake shows up everywhere: treating policy as paperwork. Policy is only useful when it changes behavior. Another is buying tools before classifying data. That almost always creates blind spots.
A third pitfall is assuming cyber incidents start and end inside security tooling. Ask yourself: Where else does the information travel? Who exports it? Who stores it offline? Who shares it with vendors? Those questions often reveal the gap faster than another dashboard.
Recommendation 1: Classify your top 10 sensitive
information assets before buying another tool.
Recommendation 2: Map each asset to both an information
security control and a cybersecurity control.
Recommendation 3: Review whether your current program is too
policy-heavy or too tool-heavy. Most weak security programs are unbalanced, not
empty.
Security Checklist
1. List one sensitive information asset your team uses every day.
2. Name one information security control and one cybersecurity control protecting it right now.
3. Check one weak point in under 5 minutes: shared links, stale access, missing MFA, or exported files sitting on unmanaged devices.
Trusted source: NIST glossary and CSF 2.0 are the best places to verify the core definitions and the risk-management framing used in this article. (NIST Computer Security Resource Center)
Research firm benchmark: IBM’s 2024 Cost of a Data Breach research found the global average breach cost reached $4.88 million. That is the business reason this distinction matters. (IBM Newsroom)
Published: April 19, 2026
Last updated: April 19, 2026
Author: Senior Cybersecurity Analyst
Understanding the difference between cybersecurity and information security helps businesses reduce risk by protecting both digital threats and broader information exposures.
Frequently Asked Questions
Was this article helpful?
React to this post and see the live totals.
Share this :