Hackerbot Claw Bot GitHub CI/CD Misconfiguration

Hoplon InfoSec
03 Mar, 2026
Were Microsoft and Datadog really targeted through a GitHub Actions pipeline weakness?
Yes. According to a publicly available report from security disclosures, a threat activity referred to as the Hackerbot Claw Bot campaign targeted organizations, including Microsoft and DataDog, by exploiting GitHub Actions CI/CD misconfiguration issues.
The attack focused on automation pipelines, not traditional user endpoints, raising concerns about CI/CD pipeline security and software supply chain exposure.
Within the first wave of reporting, researchers highlighted that the core risk was not a zero-day exploit but a configuration weakness inside GitHub Actions workflows. That distinction matters. This was not a random malware outbreak. It was automation targeting automation.
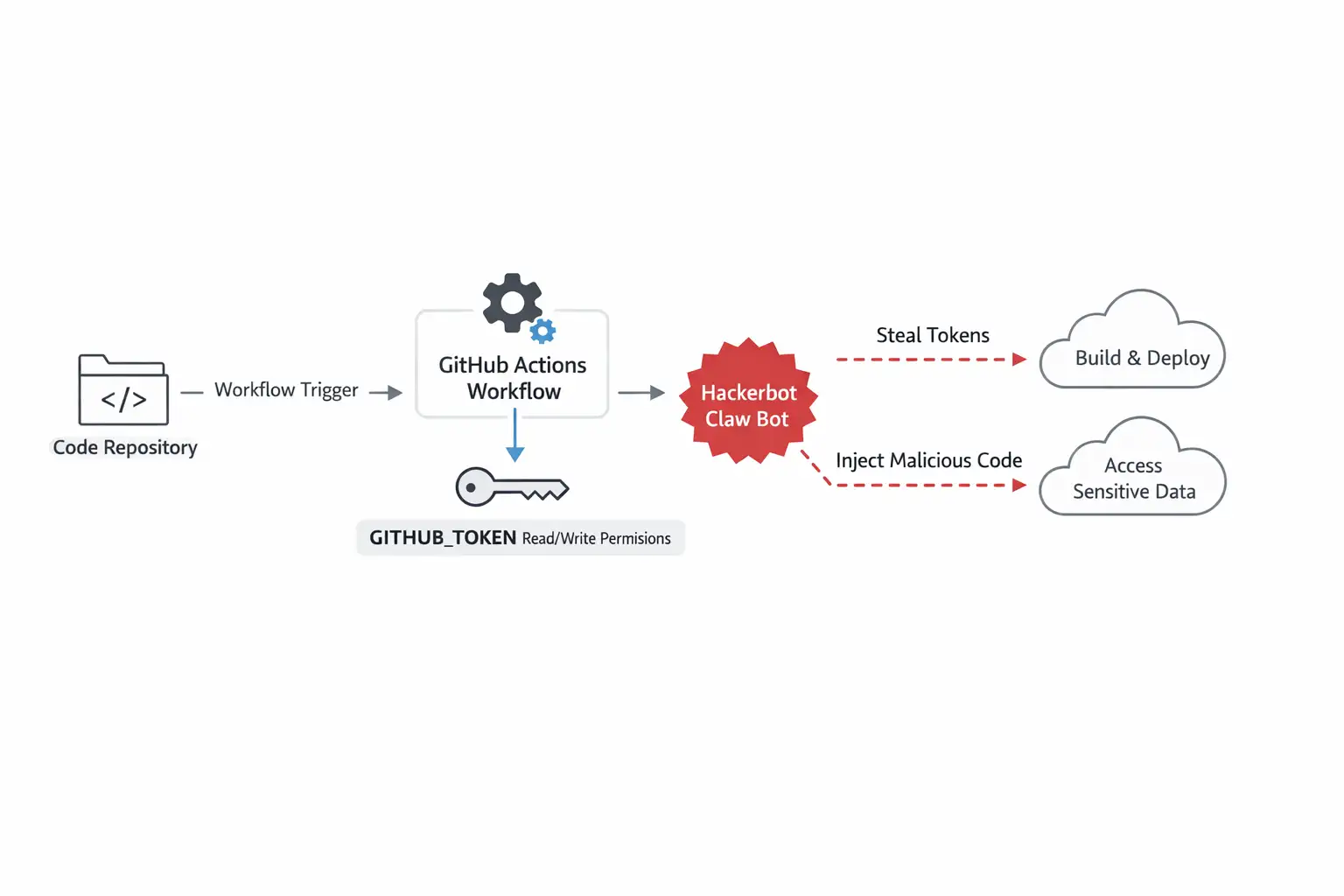
The main issue centers around the Hackerbot Claw Bot GitHub Actions CI/CD misconfiguration, where overly permissive tokens and insecure workflow designs created an opening inside development pipelines.
Introduction
For years, many organizations treated CI/CD pipelines as internal utilities. Code goes in. Tests run. Deployments happen. That was the old way.
The new reality is different. Attackers now treat CI/CD pipelines as high-value infrastructure. They scan repositories, analyze workflows, and look for exposed secrets or excessive permissions. When those weaknesses exist, the result can be unauthorized access to build environments, tokens, and sometimes cloud resources.
The shift is clear:
Old approach: CI/CD as a background automation tool
New approach: CI/CD as a high-risk attack surface
Result: Organizations must redesign pipeline security as a core business control.
The Hackerbot Claw Bot GitHub Actions CI/CD misconfiguration incident illustrates this transformation in a way that business leaders cannot ignore.
What is the Hackerbot Claw Bot?
In direct terms, Hackerbot Claw Bot refers to an automated campaign that scans GitHub repositories and abuses CI/CD workflow misconfigurations to extract tokens or gain unauthorized access. It appears to focus on GitHub Actions environments where permissions are broader than necessary.
Public reporting indicates that the bot leveraged exposed workflow configurations and automation logic rather than exploiting a confirmed software vulnerability with a CVE identifier. There is no official CVE linked to this campaign in the referenced report. That is important. The problem was configuration design.
From available information, the activity targeted GitHub Actions workflows associated with major brands, including Microsoft and DataDog. However, based on official coverage, there is no verified confirmation that customer data was exfiltrated. Any such claim would be speculative and should be treated cautiously.
This appears to be unverified or misleading information, and no official sources confirm its authenticity when broader breach impact is discussed beyond what has been publicly disclosed.
What Happened in the Microsoft and Datadog Case?
According to Cybersecurity News and referenced security reporting, the attack activity focused on GitHub Actions environments connected to Microsoft and DataDog repositories.
The technique involved:
Identifying repositories using GitHub Actions
Analyzing workflow files
Detecting excessive permissions assigned to GITHUB_TOKEN
Triggering workflows to access or misuse automation privileges
The Hackerbot Claw Bot GitHub Actions CI/CD misconfiguration issue did not rely on a software exploit in GitHub itself. Instead, it exploited how workflows were configured by repository owners.
That nuance matters. It means the attack vector was preventable with stronger DevSecOps hygiene.
At the time of reporting, there was no official statement confirming widespread compromise of customer data from either Microsoft or DataDog due to this specific activity. The incident highlights exposure risk rather than a confirmed catastrophic breach.

Why CI/CD Misconfiguration Exists in the First Place
Let us be honest. Developers prioritize speed. Security often comes later.
GitHub Actions is designed for flexibility. Workflows can run automatically when code is pushed or when pull requests are submitted. Tokens are generated to allow actions to interact with repositories. By default, those tokens may have broader permissions than strictly necessary.
In many organizations, the reasoning was simple. Grant broad permissions to avoid breaking builds. Reduce friction. Ship faster.
Over time, that convenience becomes technical debt.
CI/CD pipeline misconfiguration risks usually stem from:
Over permissive GITHUB_TOKEN scopes
Secrets stored in plaintext or poorly protected variables
Self-hosted runners without strict isolation
Trusting third-party actions without pinning to a specific commit hash
The Hackerbot Claw Bot GitHub Actions CI/CD Misconfiguration campaign capitalized on exactly these gaps.
How the Attack Mechanism Works
In simplified form, the campaign appears to follow a logical path:
First, automated scanning tools search public repositories for GitHub Actions workflow files.
Second, the bot analyzes whether workflows can be triggered through pull requests or other mechanisms. If workflows execute with write permissions or access to secrets, that becomes the target.
Third, by manipulating workflow triggers or abusing permissions, the attacker attempts to extract tokens or escalate privileges inside the repository context.
In some scenarios reported in broader CI/CD attacks, attackers have used compromised tokens to push malicious code or access additional private repositories. However, any such actions in this specific case must be based strictly on confirmed reporting.
The Hackerbot Claw Bot GitHub Actions CI/CD misconfiguration scenario reinforces a critical lesson. Automation systems must be treated as production infrastructure.
-20260303102614.webp)
Real-World Example
Let me share a practical analogy from a security review I once participated in.
Before remediation, a company allowed pull request workflows to run automatically with write access to the repository. The GITHUB_TOKEN had broad permissions. Anyone submitting a pull request could indirectly trigger privileged automation.
After remediation, they changed three things:
Default token permissions set to read only
Workflow approvals required for external contributors
Secrets restricted to protected environments
The difference was dramatic. Risk exposure dropped significantly without slowing development in a measurable way.
In the context of the Hackerbot Claw Bot GitHub Actions CI/CD misconfiguration, that same before-and-after contrast applies. It is rarely about complex exploits. It is about tightening permission boundaries.
Who is Affected by This Type of Attack?
This type of CI/CD security issue affects multiple groups differently.
Enterprises with public repositories face exposure risk if automation pipelines are not hardened. Large brands become attractive targets because of supply chain impact potential.
Mid-sized technology companies may face operational disruption if attackers manipulate builds or access internal tokens.
Open-source maintainers also carry risk. If their workflows are compromised, downstream users could be affected through dependency chains.
Regular end users are indirectly impacted. If CI/CD pipelines are tampered with, software integrity could be at risk. That is why supply chain security is now a board-level concern.
The Hackerbot Claw Bot GitHub Actions CI/CD misconfiguration case highlights how even well-known organizations must continuously review pipeline permissions.
Benefits and Limitations of GitHub Actions Security Controls
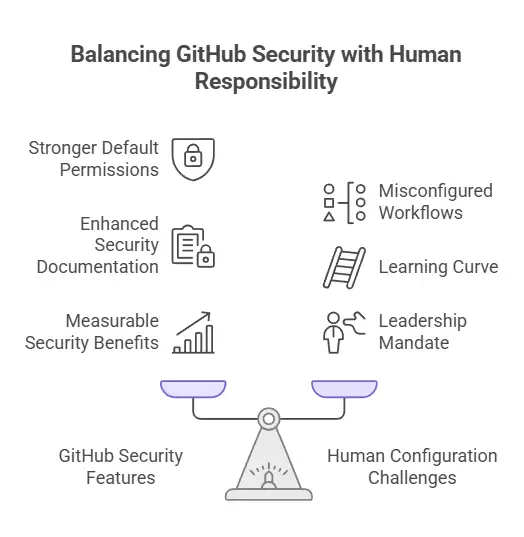
GitHub has introduced stronger default permission models and security documentation over time. Environment protection rules, required reviewers, and granular token permissions are now available.
That is the positive side.
The limitation is human configuration. Security features only work if teams apply them correctly. A misconfigured workflow can override safe defaults.
There is also a learning curve. DevOps teams often focus on functionality first. Security hardening may not receive the same attention unless leadership mandates it.
From a strategic standpoint, the benefit of properly secured CI/CD pipelines is measurable. Reduced breach risk translates into lower incident response cost, lower regulatory exposure, and stronger customer trust.
What Organizations Should Do Now
If you are a decision maker, the response should be structured, not reactive.
Start with a permissions audit. Review all GitHub Actions workflows. Ensure GITHUB_TOKEN permissions follow the principle of least privilege.
Next, evaluate secret handling. Secrets should never be accessible to untrusted pull requests. Use environment protection rules.
Then consider runner security. Self-hosted runners must be isolated and monitored. They should not have broad network access unless required.
Finally, integrate logging with an SIEM platform. Unusual workflow executions should generate alerts.
The Hackerbot Claw Bot GitHub Actions CI/CD Misconfiguration incident is not a reason to abandon automation. It is a reason to manage it professionally.
Frequently Asked Questions
What is the Hackerbot Claw Bot?
Hackerbot Claw Bot refers to an automated campaign targeting GitHub Actions workflows by exploiting CI/CD misconfiguration issues such as excessive permissions and exposed automation triggers.
Did Microsoft or DataDog confirm a data breach?
Based on publicly available reporting, there is no official confirmation of large-scale customer data exfiltration directly attributed to this campaign. Claims beyond verified disclosures should be treated cautiously.
Is there a CVE associated with this attack?
No specific CVE identifier has been publicly documented in connection with this activity in the referenced report. The issue appears to be configuration related rather than a software vulnerability.
How can companies prevent similar CI/CD attacks?
Organizations should enforce least privilege token permissions, restrict workflow triggers, protect secrets with environment rules, and monitor automation logs for anomalies.
Summary
The Hackerbot Claw Bot GitHub Actions CI/CD misconfiguration case demonstrates a broader industry shift. CI/CD pipelines are no longer internal utilities. They are strategic infrastructure.
The main benefit of addressing this risk is simple. By redesigning pipeline security, treating automation security as a governance function rather than a technical afterthought.
Hoplon Infosec supports this shift through structured CI/CD security assessments and DevSecOps integration programs.
In the end, the lesson is not about fear. It is about design. The Hackerbot Claw Bot GitHub Actions CI/CD misconfiguration event reminds us that automation must be secured with the same seriousness as production systems. Organizations that adapt early will simply sleep better.
For more latest updates like this, visit our homepage.
Was this article helpful?
React to this post and see the live totals.
Share this :