How Hackers Hack Accounts: 10 Tricks They Use to Break In
Hoplon InfoSec
21 Mar, 2026
A lot of people used to think that one password was enough to keep their online accounts safe. You made a password, logged in, and didn't think about security again for a long time.That way of doing things doesn't work anymore.
As more services go online, cybercrime has gone up a lot. Multiple cybersecurity reports say that data breaches happen every year and expose millions of user credentials. It's no longer just hard to make passwords.
The real problem is knowing how hackers break into accounts and what tools they use to do it.It's much easier to protect yourself once you know how attackers work. You can spot warning signs early and lower your risk of common attack methods instead of waiting until after a breach has happened.
This guide tells you the real ways that attackers get into your account, how to tell if your account has already been hacked, and what you and your organization can do to stay safe.
Account Hacking Basics
It's helpful to know the basic idea before talking about defense strategies.When people ask how hackers get into accounts, they mean the steps that attackers take to get into online services like email, banking, cloud tools, and social media accounts without permission.This usually happens when someone steals your login information.
Sometimes hackers get passwords by leaking data. In some cases, they get users to give them their credentials directly.The outcome is the same. Once an attacker gets in, they can pretend to be the victim, steal information, commit fraud, or spread bad links.Security researchers often call this "credential compromise," which is one of the most common types of cyber incidents reported by businesses around the world.
Why Hackers Target Accounts
Access to an account is very important.People don't always know that a hacked account can give them access to a lot more information. For instance, email accounts are often used to recover other services.
If hackers get into your email, they can change the passwords for other accounts.There are a number of reasons why these attacks happen.One of the most common reasons is to make money.
Attackers could get into payment services, banking platforms, or cryptocurrency wallets. People who steal credentials can also sell them on secret forums where other criminals buy access.In some cases, attackers use hacked accounts to trick people. A hacker could control a social media profile and send messages to friends asking for money or sharing bad links.
Sometimes all you want to do is collect data. Corporate accounts may let you see private files, internal communications, or customer databases.These reasons help us understand why hackers break into accounts so often. The rewards could be big, and a lot of users still use weak security measures.

Signs Your Password Was Stolen
Most people don't realize right away that their credentials have been stolen. The signs of danger can be hard to see.But there are a few signs that security experts often talk about.
Account Lockouts
Not being able to log into an account you used to have no trouble with is a common sign. When attackers get in, they often change passwords, which keeps the real owner from logging in.
Slow Device Performance
Malicious software on a device can make it noticeably slower. There are many reasons why devices might not work right, but security experts often look for malware when they do.
Weird Messages
Another warning sign is when people say they got strange messages from your account. These messages could have links, scams about investments, or requests for money.
Unexpected Security Alerts
If you get verification codes, password reset messages, or login alerts that you didn't ask for, it could mean that someone else is trying to get into your account.
Suspicious Transactions
One of the worst signs is when transactions happen without permission. Attackers sometimes act quickly after getting into an account, especially when money is involved.
Unknown Apps
If you see new software on your computer or phone out of the blue, it could be a sign of bad behavior. Some attackers put in tools that keep an eye on activity or get login information.
Security Tools Disabled
If your antivirus software or device's security settings suddenly stop working, it could mean that the device has been hacked.
These signs don't always mean that an attack has happened. Still, they often say that more research is needed.
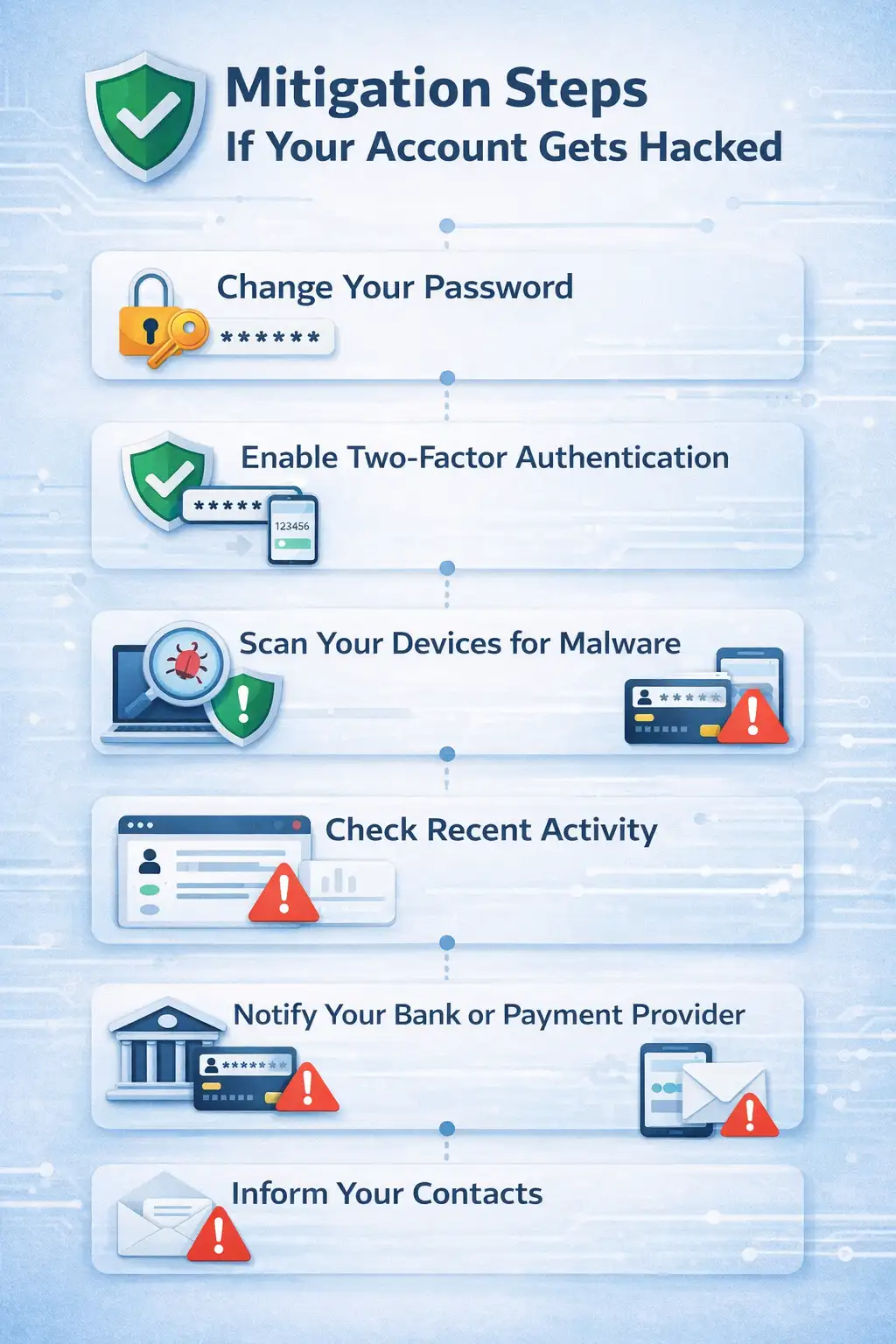
What To Do After a Hack
If you think someone has accessed your account without permission, acting quickly can help a lot. First, change the password that was stolen right away. Pick a new password that is long, one-of-a-kind, and not related to your old one.
If the service allows it, turn on two-factor authentication. This adds another step to the login process to make sure it's you.It's important to get in touch with the bank or payment provider if your financial accounts might be involved.
While the situation is being looked into, a lot of organizations can temporarily stop transactions.Next, use trusted security software to scan all of your devices for malware.It's also a good idea to look at recent login activity.
Many services show where devices are located or when they last logged in, which can show suspicious access.Lastly, let your contacts know if someone has hacked into your email or social media account. This stops attackers from using your name to go after other people.
Common Hacking Methods
It is very important to know how attacks work. Cybercriminals don't often use just one method.Instead, they use a mix of strategies based on the situation.
Data Breaches
One of the most common answers to the question of how hackers get into accounts is simple. They get credentials from databases that have already been leaked.Sometimes, attackers break into the security of big companies and get to stored user data. These events put millions of login details at risk.
Then, attackers use these credentials on other platforms, which is called credential reuse.This method often works surprisingly well because a lot of people use the same passwords for more than one account.
Phishing
Phishing is one of the most common ways that people commit cybercrime.A criminal pretends to work for a real company, like a bank or an online service, in a phishing attack. The victim gets a message telling them to log into their account using a link that is given to them.The link takes you to a fake website that looks just like the real one.As soon as users type in their login information, the attacker gets it.Security groups always say that phishing is one of the main reasons why accounts get hacked.
Fake Password Reset
Sometimes hackers send messages asking for a password reset. These messages seem important and may look like they come from a government agency.If the victim clicks the link, they might end up on a fake website that is meant to steal their credentials.
This method is very similar to phishing, but it is only used to get into account recovery processes.
Malware and Keyloggers
Malware is software that is meant to do bad things to a device.Some types of malware keep track of what you type. People often call these programs "keyloggers."Once they are installed, they record everything typed on a keyboard, even passwords and codes that prove you are who you say you are.
Malware infections usually happen when you download something unsafe or open an email attachment that has malware in it.
Brute Force Attacks
Another way to explain how hackers get into accounts is through automated password guessing.In a brute force attack, software quickly tries out thousands of different password combinations.Hackers might be able to guess the password if it is short or easy to guess.
Dictionary attacks are another way that hackers try to break into systems by testing lists of common passwords.Weak passwords, like simple number sequences, are very easy to guess.
Social Media Clues
Sometimes, attackers look at information that is available to the public to guess passwords.People often use their birthdays, pet names, or favorite sports teams as parts of their passwords.
If these details are on social media profiles, hackers might be able to guess your login information.People often call this method "open source intelligence gathering."
WiFi Attacks
People who use unsecured wireless networks may have their data stolen.Attackers who are watching network traffic may be able to get sensitive information that is sent over the connection.Users who connect to public networks without encryption are at a higher risk.
Shoulder Surfing
Some attacks don't need much technology at all.In busy places like libraries or cafes, an attacker might just watch someone type in their password.This method may seem simple, but it works surprisingly well in public places.
Credential Stuffing
Credential stuffing happens when hackers use stolen login information from one breach to get into other systems.If a user uses the same password for more than one service, attackers may be able to get into more than one account with the same login.Researchers in the field of security always warn about this risk.
Real-World Example
Think about a common situation.A person signs up for a small online forum by giving their main email address and a simple password. Months later, the forum has a security breach that lets hackers into the user database.
The user might not even notice the breach.But attackers get the leaked credentials and try them out on big sites like email providers and social networks.The attacker can now get into those accounts if the user used the same password somewhere else.
This situation shows a real-life example of how hackers get into accounts.You don't need to be a skilled hacker to do the attack. All it needs is leaked login information and automated testing tools.
Who is Most Affected
Different groups are affected by account compromise in different ways.People who use it a lot often lose access to their personal accounts or fall victim to financial fraud.Companies are at greater risk.
Corporate accounts might have private documents, sensitive customer information, or private communications.People like journalists, developers, and executives are often targeted because their accounts may have useful information.
Cybersecurity incidents that involve hacking into accounts can also hurt a company's reputation and trust.
Security Tools Today
In the last few years, security tools have gotten a lot better.Multi-factor authentication adds an extra layer of security by requiring a second step to confirm your identity. Attackers might still be stopped even if they get a password.
Password managers also help by making sure that each account has a different password.But these answers aren't perfect.People can still be tricked into giving up their personal information through phishing attacks or social engineering.
Tools for security lower risk, but they can't get rid of it completely.The main benefit comes from using more than one protection instead of just one.
What Users Should Do
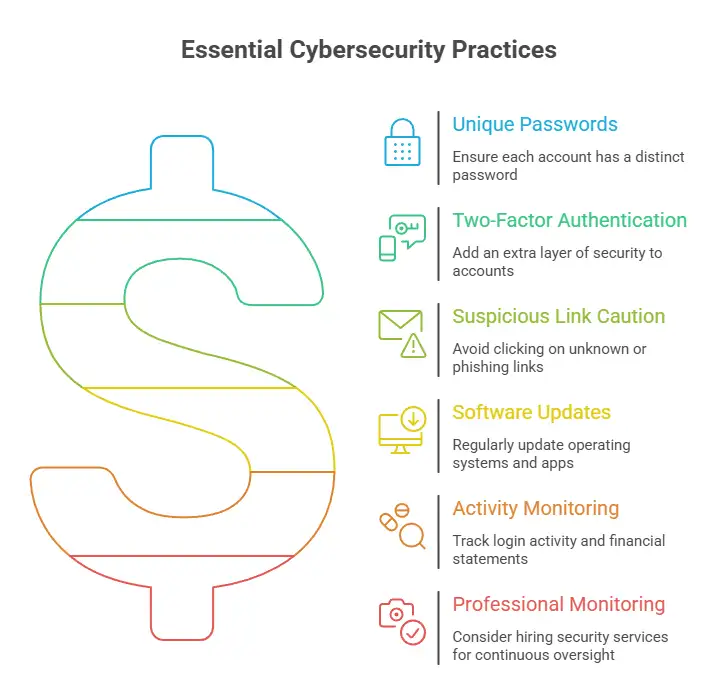
Cybersecurity experts always suggest a few useful steps.
• Make sure that each of your online accounts has a different password.
• Use two-factor authentication whenever you can.
• Don't click on links in emails or messages that look suspicious.
• Keep your operating systems and apps up to date on a regular basis.
• Keep an eye on login activity and financial statementsOrganizations may also want to think about hiring a professional security monitoring service to keep an eye on accounts and systems for any strange activity.
Companies like Hoplon Infosec help businesses find weaknesses, keep an eye on threats, and make their digital security stronger without getting in the way of their normal business.Their method is based on proactive monitoring instead of reacting after a breach has already happened.
FAQ
How do hackers get into accounts without knowing the password?
In some cases, attackers get around passwords by using phishing, malware, or session hijacking. Instead of guessing passwords, these attacks go after authentication systems.
Is it possible for someone to hack my account with just my email address?
Just having an email address is usually not enough. But attackers could use it to try to steal your passwords or send you phishing emails.
What is the most common way for hackers to get into accounts?
Phishing attacks and credential reuse are often listed as the main reasons why accounts get hacked in security reports.
How can I find out if my password has been stolen?
Several security monitoring services keep an eye on known data breaches and let users know if their credentials show up in databases that have been leaked.
Does two-factor authentication really work?
Yes. Studies on security show that multi-factor authentication makes it much harder for people to take over your account.
Summary
The first step to better digital security is to learn how hackers get into accounts.People used to protect themselves with just one password and basic security measures. To protect against modern threats, you need a layered approach that includes strong passwords, authentication safeguards, and constant monitoring.
Proactive security strategies often make it less likely that an account will be hacked.Security companies like Hoplon Infosec help businesses keep their accounts safe by finding risks early and supporting ongoing security operations.It's easy to see the benefit.
When businesses know how attackers work and put the right protections in place, the chances of an account being hacked go down a lot.
For more latest updates like this, visit our homepage.
References
The National Institute of Standards and Technology
Cybersecurity and Infrastructure Security Agency: CISA
Author: Radia,Senior Cybersecurity Analyst
Published: 22 March, 2026
Last Updated: April 20,
2026
Was this article helpful?
React to this post and see the live totals.
Share this :