Loblaw Data Breach: Is Your PC Optimum Account Safe?

Hoplon InfoSec
14 Mar, 2026
Is the Loblaw Data Breach a real security concern for guests?
Yes. The Loblaw Data Breach verified that unauthorized actors penetrated a limited section of the company’s IT network and attained introductory client contact information.
still, sanctioned statements indicate that watchwords, payment data, and health records were n't compromised, and sensitive systems remained protected.
For numerous druggies, the concern started when they were suddenly logged out of their digital accounts. That moment touched off questions. What happed? Was fiscal information stolen? And most importantly, what should guests do next?
This composition explains the incident in clear terms, using only verified information.
A Cybersecurity Incident That Caught guests Off Guard
The Loblaw Data Breach snappily came a content of discussion among Canadian guests after the company bared that hackers had gained access to part of its internal network.
Old reality utmost people assumed retail platforms were fairly safe unless payment systems were targeted.
New reality indeednon-critical systems can contain precious client data.
Result companies now treat indeed small breaches as significant security events.
In this case, bushwhackers penetrated a contained terrain within the Loblaw IT structure. That section stored client contact information but did n't contain fiscal records, login watchwords, or drugstore data.
Indeed though the stolen data appears limited, the exposure still creates threat. Names, phone figures, and dispatch addresses can come tools for phishing juggernauts. Cybersecurity judges frequently describe this as the first step in broader social engineering attempts.
What happed During the Loblaw Data Breach?
The Loblaw Data Breach passed when unauthorized trouble actors sneaked anon-critical section of the company’s IT network and penetrated client contact information similar as names, phone figures, and dispatch addresses. Sensitive systems including fiscal databases and health records remained secure.
Detailed Explanation
According to sanctioned statements, security brigades detected unusual exertion inside the company’s network terrain. This touched off an internal disquisition.
What investigators set up was fairly specific.
Hackers had entered a segmented portion of the structure, meaning the system was separated from core functional platforms. This armature averted bushwhackers from moving deeper into sensitive surroundings.
still, within that isolated section the bushwhackers were still suitable to recoup stored client data.
The information penetrated included
• First and last names
• Registered dispatch addresses
• Phone figures associated with accounts
No other orders of client information were verified as exposed.
From a cybersecurity perspective, this type of incident is frequently described as data exfiltration from a contained network zone.
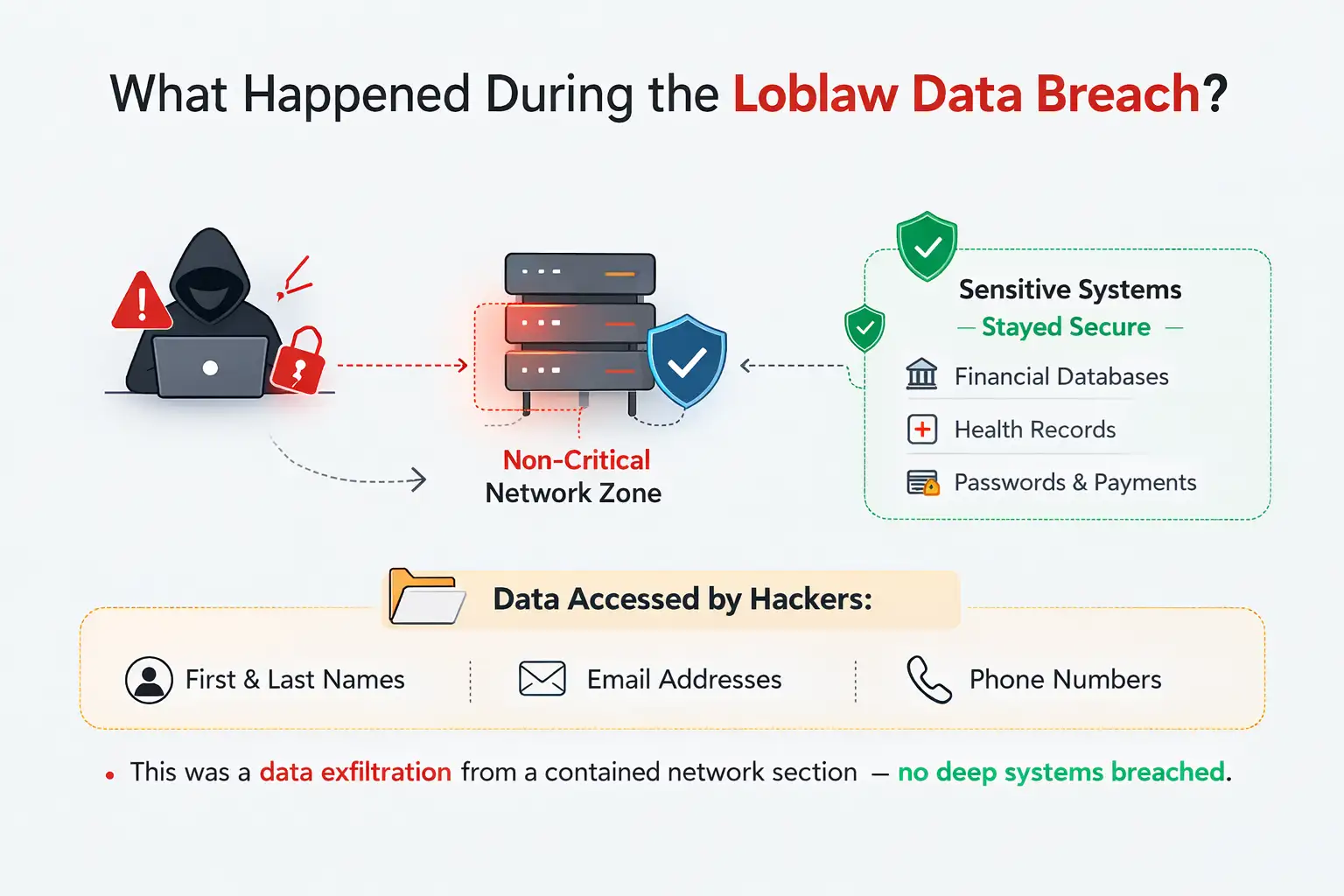
What client Information Was NOT Compromised?
examinations verified that watchwords, login credentials, credit card figures, and drugstore records were n't penetrated during the Loblaw Data Breach. fiscal services systems associated with PC Financial also remained secure.
One of the most important details about this incident is what bushwhackers did n't reach.
The compromised terrain was designedly separated from systems that manage fiscal and medical data. Because of that separation, the breach did n't spread into those critical databases.
verified secure systems include
• client watchwords and login credentials
• Credit card and payment information
• drugstore or health related records
• PC fiscal banking systems and linked accounts
This matters because those types of data are generally the primary targets of cybercriminals.
The fact that they were n't penetrated suggests the network segmentation worked as intended.
Still, indeed introductory contact information can have value in cybercrime operations.
Why Contact Information Breaches Still Matter
Numerous people assume a data breach only becomes serious when fiscal information is involved. In reality, cybersecurity professionals know that contact data is frequently the first step in a larger attack chain.
When hackers gain names, phone figures, and dispatch addresses, they can launch targeted phishing juggernauts.
Then's how it generally works
• bushwhackers shoot emails pretending to be client support.
• They shoot SMS dispatches claiming account issues.
• Victims click links that lead to fake login runners.
Because the communication includes real particular information, it appears more satisfying.
This type of attack is known as phishing or smishing, depending on whether the communication arrives by dispatch or textbook.
So while the Loblaw Data Breach did n't expose watchwords, cybersecurity experts still encourage guests to remain conservative.
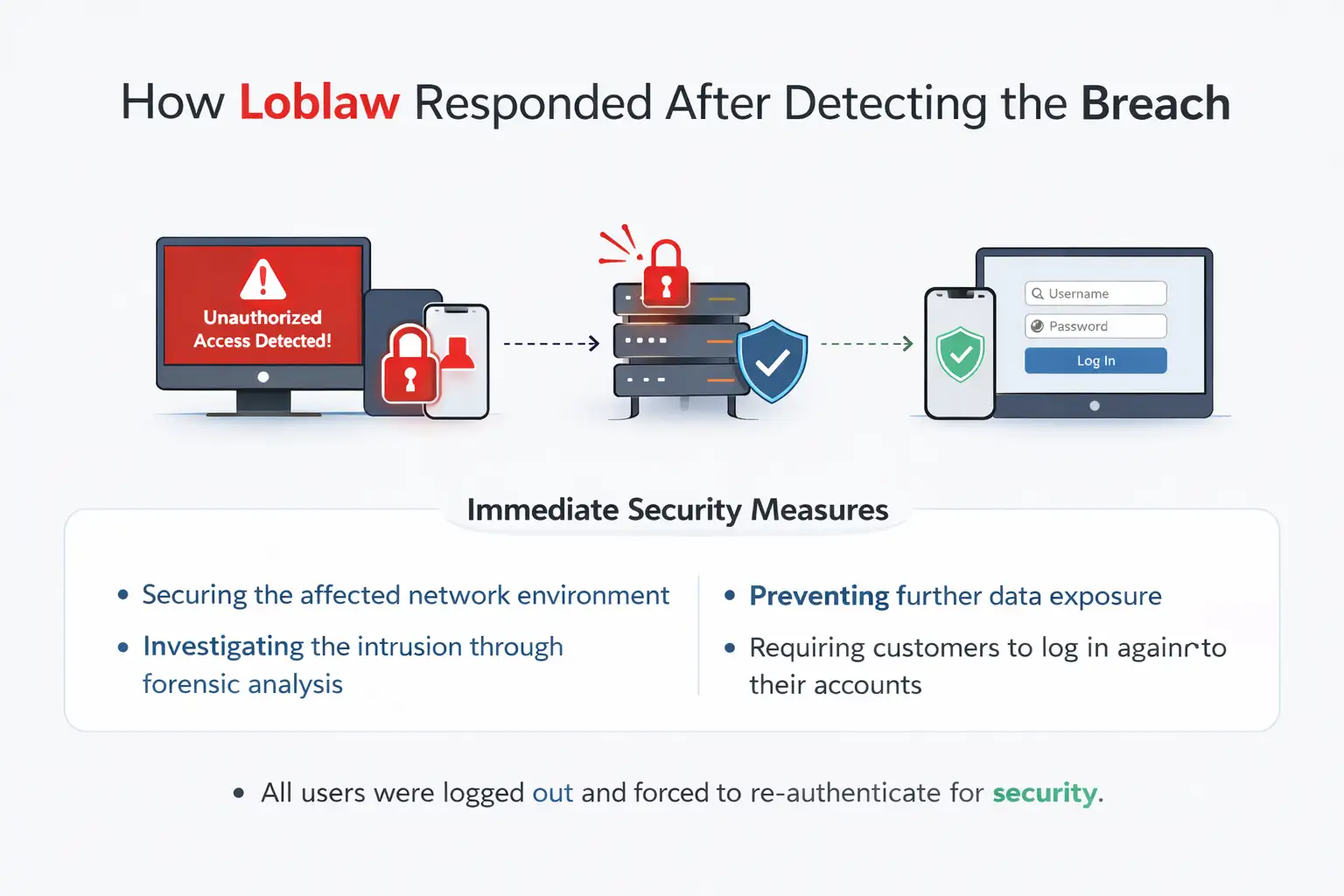
How Loblaw Responded After Detecting the Breach
After discovering the unauthorized access, Loblaw actuated internal security response procedures, secured the affected network member, and forced druggies tore-authenticate their accounts to insure ongoing protection.
Immediate Security Measures
Once the unusual exertion was detected, the company enforced constraint conduct.
These conduct included
• Securing the affected network terrain
• probing the intrusion through forensic analysis
• precluding farther data exposure
• taking guests to log in again to their accounts
One visible effect of these measures was that numerous guests set up themselves automatically logged out of digital services.
That logout was n't arbitrary. It was part of the security protocol designed to abate active sessions and insure druggies authenticate again.
From a protective viewpoint, forced reauthentication helps help unauthorized session access.
How a Contact Data Leak Can Be Exploited
magine a typical situation.
A client receives a textbook communication that appears to come from their grocery prices program. The communication mentions their name and asks them to confirm account details through a link.
Because the communication includes real contact information, it feels licit.
But the link leads to a fake website designed to steal credentials.
This is why the Loblaw Data Breach raises enterprises indeed though fiscal records were n't penetrated.
Cybercriminal groups constantly combine small pieces of stolen data with cerebral tricks to gain deeper access latterly.
Who Could Be Affected by the Loblaw Data Breach?
Guests
individualities who handed dispatch addresses or phone figures during account enrollment may be affected.
This does n't mean their accounts were penetrated. It simply means their contact details may now live in external datasets.
Digital Service druggies
People who use Loblaw’s online services or mobile apps may notice security changes similar as forced logouts.
These conduct are part of the company’s defensive response.
Businesses and Cybersecurity brigades
Retail companies frequently study incidents like the Loblaw Data Breach because they reveal how bushwhackers exploit lower network parts.
It shows the significance of layered security armature and rapid-fire incident discovery.
Benefits and Limitations of the Security Response
Positive issues
• Sensitive fiscal and health systems remained protected
• The compromised network area was contained
• Security brigades detected suspicious exertion and responded
• guests were logged out to help unauthorized access
Remaining enterprises
Indeed with constraint measures, the exposure of contact information introduces ongoing pitfalls.
guests may encounter
• phishing emails
• SMS fiddle
dispatches
• impersonation attempts
Security mindfulness becomes the most effective defense at this stage.
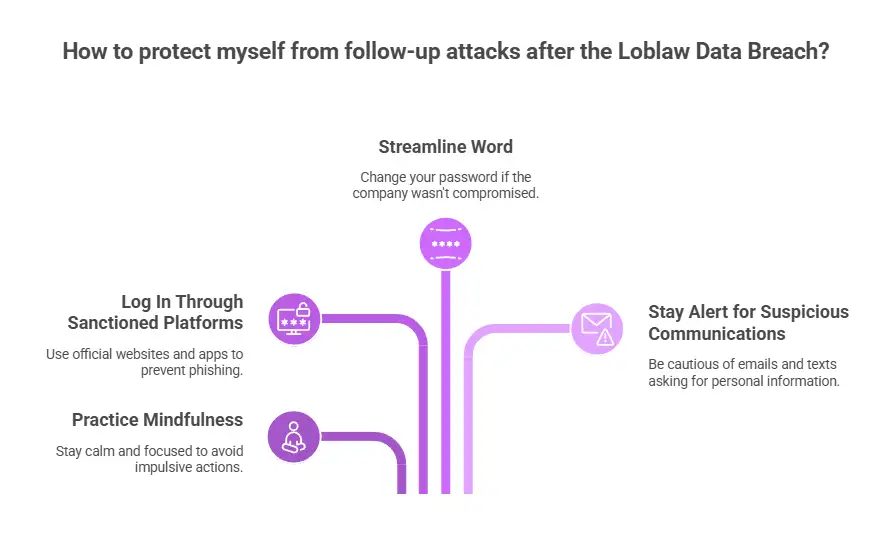
What guests Should Do Now
The safest approach is simple mindfulness combined with a many introductory conduct.
First, log back into your account through sanctioned platforms. Avoid clicking links in unanticipated dispatches.
Alternate, consider streamlining your word indeed if the company states it was n't compromised. This is a palladium that numerous cybersecurity professionals recommend after any breach.
Third, stay alert for suspicious emails or textbook messages.However, corroborate it directly through the company’s functionary website or operation, If a communication asks for login details or payment information.
These way help reduce the chances of falling victim to follow- up attacks related to the Loblaw Data Breach.
Common Questions About the Loblaw Data Breach
Was fiscal information stolen?
No. examinations verified that credit card data, payment information, and PC Financial systems were n't penetrated.
Were client watchwords exposed?
No. watchwords and login credentials remained secure according to the company’s findings.
Why were druggies logged out of their accounts?
The forced logout was a security measure designed to abate being sessions and bear druggies to reauthenticate.
What information was actually penetrated?
The exposed information includes client names, phone figures, and dispatch addresses.
Should guests change their watchwords anyway?
It is n't obligatory grounded on sanctioned findings, but numerous cybersecurity professionals recommend doing so as a palladium.
Key Cybersecurity Assignments From This Incident
Retail platforms handle large volumes of client data, indeed in systems that appear operationally minor.
This incident highlights several assignments
• Network segmentation can help deeper concession
• Early discovery limits damage
• Contact information leaks can still enable social engineering
Security brigades across diligence frequently study incidents like the Loblaw Data Breach because they show how bushwhackers exploit lower sins rather than targeting the most defended systems.
Conclusion
The Loblaw Data Breach demonstrates a common pattern in ultramodern cyber incidents. bushwhackers do n't always go after the most egregious targets.
rather, they look for overlooked surroundings that still contain useful information.
In this case, fiscal and medical records remained safe. That's significant.
still, the exposure of names, emails, and phone figures means guests should remain conservative about implicit phishing attempts.
still, the safest approach is simple, If you're a Loblaw client. Log back into your account, corroborate dispatches precisely, and avoid clicking links in unanticipated dispatches.
Cybersecurity frequently works best when technology and stoner mindfulness operate together.
To learn more, visit our blog page.
Was this article helpful?
React to this post and see the live totals.
Share this :