Payouts King Ransomware: BlackBasta Link and Attack Analysis
-20260417145628.webp&w=3840&q=75)
Hoplon InfoSec
18 Apr, 2026
Is Payouts King ransomware a real threat tied to former BlackBasta affiliates?
As of April 17, 2026, multiple security reports say yes on the threat itself, and they present strong overlap with the tradecraft used by former Black Basta operators, especially around spam bombing, Teams impersonation, Quick Assist abuse, and enterprise-focused ransomware deployment.
The most credible public reporting traces the latest activity to threat research derived from Zscaler and aligns it with previously documented Black Basta intrusion patterns and Microsoft’s reporting on Quick Assist-driven ransomware access chains.
Payouts King ransomware is a newly tracked ransomware operation linked in public reporting to former BlackBasta affiliates.
Researchers say the group uses social engineering, Microsoft Teams lures, Quick Assist abuse, payload download chains, and strong encryption to compromise enterprise networks.
Organizations should treat it as a serious, current threat and review guidance from authorities such as CISA and Microsoft.
Payouts King Overview
Payouts King ransomware is being described in public reporting as a technically capable ransomware family that appears to have gained momentum after the disruption of Black Basta’s public operations.
Researchers tracking the malware note strong encryption, anti-analysis features, and behavior consistent with modern enterprise-focused ransomware rather than low-skill commodity malware.
What makes this more than just another malware name is the context. Payouts King ransomware group activity is not being framed as a random newcomer with no lineage.
The strongest public analyses connect the intrusions to tradecraft long associated with Black Basta affiliates, which changes the risk picture.
A new brand with old operators is often more dangerous than a truly new entrant because the attackers already know what works.
Overview
|
Item |
Publicly documented detail |
|
Threat name |
Payouts King ransomware |
|
Public linkage |
Reported overlap with former BlackBasta affiliates |
|
First publicly noted |
Public reporting says first observed in April 2025, with activity becoming more visible in early 2026 |
|
Initial access style |
Spam bombing, phishing, vishing, Microsoft Teams impersonation, Quick Assist abuse |
|
Payload behavior |
Scripted download chains, command execution, foothold establishment, lateral movement prep |
|
Encryption |
RSA plus AES-256 documented in reporting; samples observed using AES for file content |
|
Evasion |
Stack-based string obfuscation, API/string hashing, direct system calls for process termination |
|
Victim focus |
Enterprise environments and high-value targets |
|
Key defender focus |
User awareness, MFA, monitoring remote support tools, EDR tuning, rapid containment |
BlackBasta Connection
The ransomware linked to Black Basta angles matters because this is where the story stops being a simple malware brief and starts looking like ecosystem continuity.
Public reporting says that after Black Basta’s internal chats leaked in February 2025, the brand’s main operation fell apart. That did not mean the people, access paths, or working playbooks vanished. It meant they had to move.
That is why the overlap is so important. The latest intrusions attributed to Payouts King ransomware linked to BlackBasta reportedly use the same pressure-heavy social engineering model that defenders already associate with Black Basta-style campaigns.
Attackers flood inboxes, create urgency, pose as internal support, move the conversation to Teams, and push the victim into Quick Assist. That chain is not generic background noise. It is specific enough to matter.
Researchers are careful with attribution language, and that caution should stay in any serious article. The public record supports a strong link through tactics, timing, and affiliate behavior.
It does not publicly prove that every operator behind Payouts King is identical to the old Black Basta core. That distinction matters. Threat lineage is often clearer at the tradecraft level than at the membership level.
BlackBasta Fallout
Black Basta first appeared in 2022 and became one of the more active ransomware operations targeting businesses and critical sectors.
A joint advisory from CISA and partners said Black Basta affiliates had impacted more than 500 organizations globally as of May 2024. That is the scale defenders need to keep in mind when they hear the phrase “former BlackBasta affiliates.” This is not a fringe legacy.
Then came the leak. Public reporting says a major internal chat log exposure in February 2025 pulled back the curtain on the group’s methods and internal dynamics, contributing to the shutdown of its primary public-facing operations. But cybercrime groups do not retire the way startups close.
They fragment. Initial access brokers move. Specialists take their skills elsewhere. Infrastructure gets reused, repackaged, or quietly abandoned.
This is the broader lesson in the former BlackBasta affiliates' new ransomware story. Defenders who focus only on names are always one step behind.
The better question is this: what tactics survived the brand collapse? In this case, the answer appears to include social engineering, remote access abuse, scripted payload staging, and selective enterprise-focused execution.
Attack Flow
Initial Access
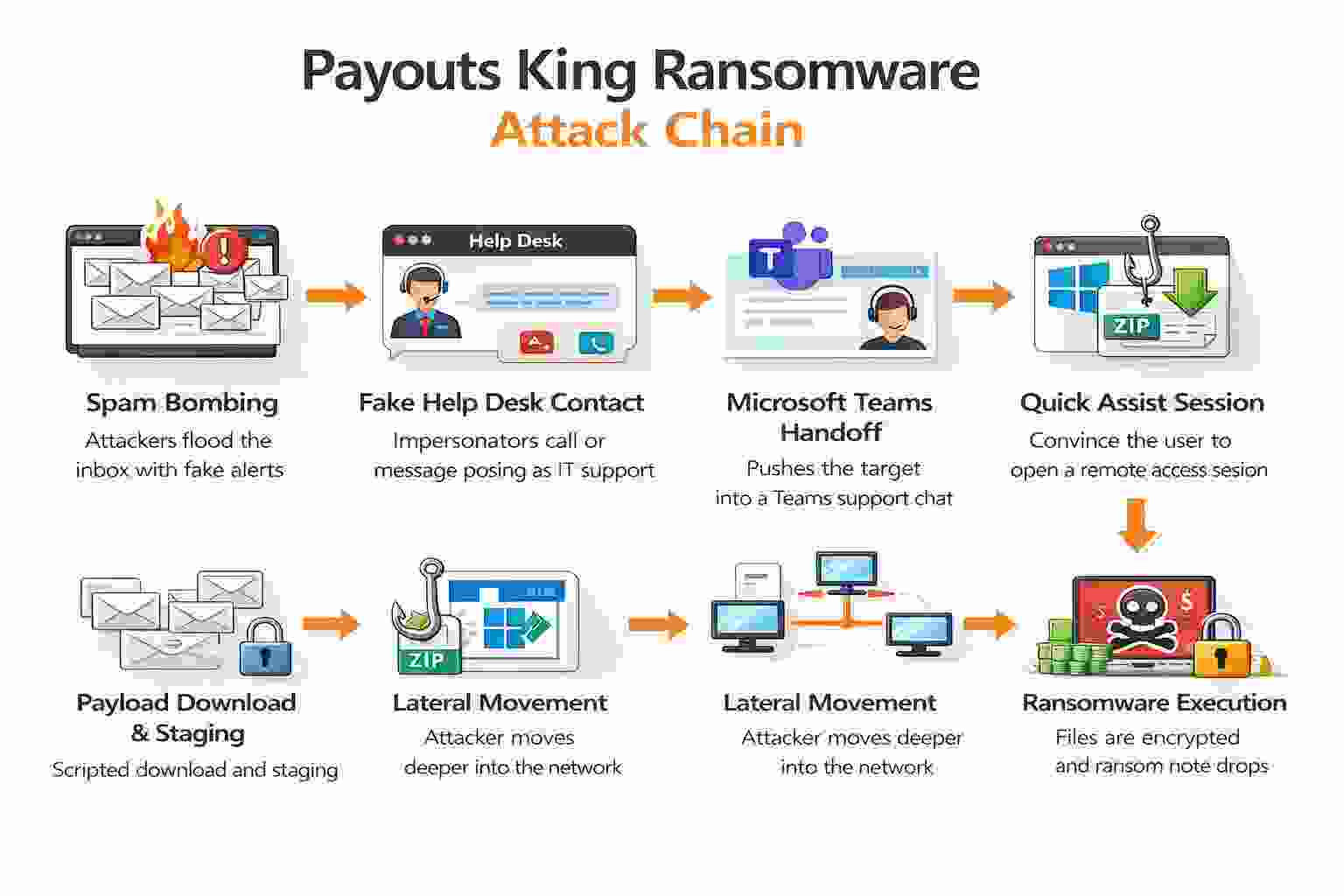
The initial access pattern is one of the clearest parts of the reporting. In the observed campaigns, attackers rely on spam bombing, phishing, and voice contact to create confusion and urgency. That pressure campaign sets up the next move: impersonating internal IT or help desk personnel.
The Payouts King ransomware Microsoft Teams attack angle is especially important. Microsoft documented that Black Basta-linked activity used Teams messages and calls from fake help desk identities to build credibility with targets.
Public reporting on payouts King says attackers are following the same basic route, which strongly suggests operational inheritance or close imitation.
Then comes Quick Assist. The Payouts King ransomware Quick Assist technique works because it abuses trust, not just software. Quick Assist is a legitimate Microsoft tool.
If a user believes they are talking to internal support and willingly shares access, the intrusion starts under the cover of a signed, familiar utility. That sharply changes the defender’s challenge.
Payload Delivery
Once access is granted, the next stage is fast and practical. Microsoft’s reporting on similar Black Basta-linked intrusion chains shows scripted cURL commands used to download batch files or ZIP payloads.
That behavior matches the broader reporting around modern operator-led ransomware where remote access is only the opening move. The real work begins after the victim clicks “allow.”
Public reporting on how Payouts King attacks work says the actors establish a foothold, prepare for movement inside the network, and stage the environment for ransomware execution. That includes downloading tools, executing commands, and preparing for privilege expansion or broader access. Even where exact tool lists vary, the pattern is consistent with hands-on-keyboard intrusions rather than automated smash-and-grab malware.
What we have found in similar investigations is that the quiet phase is where teams lose time. The user thinks the issue is resolved because “IT fixed the mailbox problem.”
Meanwhile, the attacker is moving from endpoint trust to domain visibility. That gap between user confidence and defender awareness is what makes this intrusion chain so dangerous.
Encryption
The malware side of Payouts King ransomware is not weak. Reporting says it uses strong encryption with RSA and AES-256, anti-analysis routines, string obfuscation, API hashing, and direct system calls for process termination.
Samples observed by researchers used AES for file content, with encryption parameters wrapped through RSA-protected structures.
That technical detail matters for two reasons.
First, it shows this is not a crude locker thrown together by low-skill copycats.
Second, it shows the operators care about evasion and execution reliability. Direct system calls for process termination are especially telling because they are meant to reduce the value of user-mode monitoring hooks used by security tools.
There is also evidence of selective encryption logic. Reporting says smaller files may be fully encrypted, while larger files can be handled in partial-block fashion, depending on file size and extension conditions.
That approach is common in modern ransomware because it speeds impact while reducing execution time and detection windows.
Key TTPs
The public evidence around Payouts King TTPs points to a familiar but effective stack: social engineering at the edge, legitimate tool abuse for access, script-based payload delivery, anti-analysis logic in the malware, and process interference during encryption. None of those pieces are new in isolation. The problem is how well they fit together.
For defenders, the sequence matters more than the label. Spam bombing alone is noisy but not fatal. Teams' impersonation alone is suspicious but not always successful. Quick Assist alone is legitimate in many environments.
Combined, they create a high-trust bridge straight into the endpoint. That is the operational trick. The attacker makes each step look normal enough until the chain is already complete.
This is also why rhetorical questions matter in a review like this. Would your help desk policy stop a user from accepting Quick Assist from someone they believed was internal IT?
Would your SOC treat a sudden flood of junk mail followed by a Teams support call as a coordinated intrusion indicator? If not, the gap is not theoretical.
Targeted Sectors
Public reporting consistently frames these campaigns around enterprise and high-value targets.
Microsoft tied similar Quick Assist and Black Basta-linked social engineering to financially motivated operations, and other reporting notes strong interest in regulated, high-pressure sectors where downtime carries real leverage.
Healthcare, manufacturing, logistics, and large enterprises fit that profile.
That sector mix makes business sense for attackers. Manufacturing and logistics suffer immediately from operational interruption.
Healthcare carries urgency, sensitivity, and compliance pressure. Large enterprises provide wider identity surfaces, more remote support workflows, and more room for lateral movement.
Attackers do not pick sectors at random. They pick places where one compromised user can lead to costly decisions.
Payouts: King vs. BlackBasta
|
Area |
Payouts King |
Black Basta |
|
Public status |
Newly tracked, rising visibility in 2026 |
Established group first identified in 2022 |
|
Public attribution |
Linked through tradecraft overlap with former affiliates |
Directly documented by CISA and partners |
|
Initial access style |
Spam bombing, Teams, Quick Assist, phishing, vishing |
Similar social engineering and affiliate-driven access patterns |
|
Malware traits |
Strong encryption, obfuscation, direct syscalls, anti-analysis |
Mature ransomware with prior code evolution and enterprise focus |
|
Strategic read |
New banner, familiar operator behavior |
Legacy operation whose ecosystem likely fragmented after leaks |
Similarities
The overlap is hard to ignore. Both the public Black Basta record and the current Payouts King reporting emphasize enterprise targeting, social engineering, and operational discipline.
The connection is strongest at the intrusion workflow level, not just in broad ransomware themes.
Differences
The biggest difference is maturity in public visibility. Black Basta has years of documentation and law-enforcement attention behind it. Payouts, King vs Black Basta, is therefore not a clean one-to-one comparison yet.
Payouts King is newer in the open record, which means some conclusions should stay provisional. That does not reduce the risk. It just means defenders should separate “confirmed” from “plausible.”
Defender Takeaway
Here is the practical view from our side: defenders should treat Payouts King as a continuation problem, not a novelty problem.
New branding can fool dashboards and briefings. It should not fool security planning. If the access brokers, lures, and operator habits look familiar, your defenses should assume continuity.
Warning Signs
The warning signs are not subtle once you know the pattern. A sudden wave of junk mail. A Teams message or call from someone claiming to be support.
Pressure to open Quick Assist. Script activity soon after remote access. Unusual outbound traffic from a workstation that was “just getting help.” These are exactly the moments where an early containment decision can stop a much larger incident.
Another warning sign is social mismatch. If a user receives tech support they never requested, that is a red flag.
If the helper identity is generic, oddly named, or comes from a tenant the employee does not recognize, treat it seriously. Microsoft noted fake identities such as “Help Desk” and similar names in Teams-based attacks.
IOCs and Detection
A serious Payouts King ransomware indicators of compromise section should start with behavior, not just hashes.
Look for unusual Quick Assist launches, remote support sessions outside standard processes, cURL or script execution immediately after user-help interactions, and process termination attempts tied to encryption staging. Those signals often arrive earlier than a ransom note.
From a host perspective, watch for command-line abuse, batch script chains, suspicious ZIP retrieval, unexpected RMM tooling, and bursts of file-access activity inconsistent with user behavior.
From a network angle, investigate outbound connections that begin right after remote assistance sessions or Teams-based support interactions. This is one of those cases where weak signals become strong when you correlate them in time.
Prevention Tips
How to Protect Your System
Review Quick Assist policy today. If your organization does not require it, block or uninstall it. Microsoft explicitly says organizations can reduce risk by blocking or removing Quick Assist and other remote management tools when they are not needed.
Restrict remote support workflows. Require ticket-backed support sessions, named technicians, and approved tenant lists for external collaboration tools. No ad hoc support calls. No exceptions.
Harden Microsoft Teams. Limit external messaging where possible, monitor new tenant interactions, and create awareness banners for unknown senders. The Teams handoff is a core part of this intrusion chain.
Enforce MFA everywhere meaningful. Microsoft and Zscaler both point to stronger identity controls as part of defense-in-depth. MFA will not stop every social engineering path, but it does reduce post-access expansion options.
Watch for cURL and script misuse on endpoints. On Windows, alert on unusual curl.exe execution by non-admin users, especially when it follows Quick Assist or Teams activity.
Tune EDR for behavior, not only signatures. Direct system calls and obfuscation are meant to weaken simplistic detection. Prioritize detections around process kills, mass file modification, and remote tool abuse.
Protect backups and segment the network. Ransomware success is often a recovery problem as much as an intrusion problem. Keep immutable backups and test restore paths regularly.
Train users on fake IT scenarios. Most awareness training focuses on email links. This threat chain uses human pressure, live calls, and legitimate tools. Your training should too.
Our Technical Analysis
When we mapped the reported intrusion flow against real-world support workflows, one thing stood out: this is a trust abuse problem before it becomes a malware problem.
That changes the playbook. Security teams often put the most energy into blocking malicious binaries, but Payouts King ransomware attack chains appear designed to begin with user-approved access through familiar tools. The first defensive failure is social, not cryptographic.
In our practical review of the public tradecraft, we noticed another problem. Teams, Quick Assist, and scripted downloads each look manageable in isolation.
Together they create a chain that can slip past fragmented monitoring. One team watches email. Another watches an identity. Another watches endpoint alerts.
The attacker moves across all three. That is why unified correlation matters here more than a single “perfect” signature.
When we ran through this attack path as a tabletop exercise, the hardest part was not spotting the ransomware stage.
It was deciding when the event became a security incident. A mailbox flood is annoying. A support call is plausible. A Quick Assist session can look routine. The danger lives in the transitions.
We also encountered a common challenge while modeling detection logic: legitimate admin behavior can resemble attacker behavior if your environment already relies heavily on remote support.
That means the answer is not just “alert on Quick Assist.” The answer is context. Who initiated it? Was there a ticket? Did the user request help? Did script execution follow immediately? That is the level of detail defenders need.
Why This Matters
Why does this matter more than yet another ransomware headline? Because the new ransomware threat here is not only technical. It is procedural.
It exploits the messy middle ground between user support, collaboration tools, and endpoint trust. Businesses that invested in endpoint controls but ignored help desk process design may find themselves exposed anyway.
For regular users inside organizations, the risk is personal too. Many people have been trained to “contact IT” when something feels wrong.
This attack chain flips that reflex. The attacker creates the problem, then arrives as the solution. That is psychologically effective. It also means awareness programs need better realism.
Common Pitfalls
One common mistake is assuming that signed Microsoft tools are low risk by default. They are lower risk in many contexts, yes. But when attackers weaponize trust around a legitimate tool, policy and process become just as important as malware detection.
Another mistake is focusing too much on the final encryption event. By the time file encryption starts, you are already late. The better win is breaking the chain during fake support outreach, unauthorized remote access, or payload staging.
A third mistake is writing detection rules that never meet the business context. If your support team genuinely uses remote tools all day, your alerts will drown unless you can separate approved support from socially engineered support.
What we recommend right now
Disable or tightly restrict Quick Assist unless your support model truly needs it.
Create a “no ticket, no remote session” policy and enforce it.
Add correlation rules for spam surge plus Teams contact plus script execution.
Teach employees one simple rule: internal IT will never ask for remote access through an unexpected Teams chat.
Final Verdict
Payouts King ransomware deserves attention because it looks less like a random new name and more like a practical continuation of a successful operator playbook. The malware appears capable. The access chain is believable.
The social engineering angle is mature. That combination is enough to treat it as a current enterprise threat, not just a passing headline.
We would not overstate what is still unconfirmed. Public reporting does not prove every internal detail of the group. But it does show enough to justify action now.
That is the right posture with threats like this. Wait for perfect attribution, and you are already behind.
Security Checklist
Check Quick Assist exposure now
Confirm whether it is installed, needed, and restricted by policy.Brief staff in under 5 minutes
Tell them to reject unexpected IT messages, Teams calls, or remote-support requests.Hunt for the chain, not just one alert
Look for junk-mail spikes, fake support contact, Quick Assist launches, and script execution in the same timeline.
Trusted source: Microsoft Security’s research on Quick Assist misuse leading to ransomware remains one of the most useful public references for this intrusion style.
Research-backed takeaway: CISA and partners documented Black Basta’s broad impact, and newer reporting shows how those affiliate-era methods may continue under different banners. That is the real lesson here. Names change faster than tactics.
By: Security Research Desk
Published: April 17, 2026
Last updated: April 17, 2026
Frequently Asked Questions
Was this article helpful?
React to this post and see the live totals.
Share this :