SharePoint Spoofing Vulnerability: 1,300+ Servers Exposed

Hoplon InfoSec
23 Apr, 2026
Is the SharePoint spoofing vulnerability a real and urgent risk right now?
Yes. As of April 22, 2026, the SharePoint spoofing vulnerability tracked as CVE-2026-32201 is not just a patch note buried in Microsoft documentation.
It is a live issue tied to ongoing attacks, and more than 1,300 exposed SharePoint servers were still reported unpatched on the public internet this week.
Microsoft has released fixes, CISA has added the flaw to its Known Exploited Vulnerabilities catalog, and the affected products are on-prem SharePoint Server versions, not SharePoint Online.
That is the part many readers need up front. The risk is concentrated in on-premise deployments. The urgency comes from active exploitation, broad internet exposure, and the fact that SharePoint often sits close to sensitive documents, internal workflows, and identity-linked services. This is why the current SharePoint vulnerability deserves immediate attention from infrastructure, security, and IT operations teams.
What
happened?
Microsoft patched CVE-2026-32201,
a Microsoft SharePoint
spoofing vulnerability that had already been exploited in the
wild.
Who
is affected?
On-prem SharePoint deployments, including SharePoint Server 2016, SharePoint Server 2019,
and SharePoint Server
Subscription Edition.
Is
SharePoint Online affected?
The public Microsoft support pages for this issue focus on on-premises server
products. They do not list SharePoint Online as an affected product for this
CVE.
What
should admins do now?
Patch immediately, verify build levels, review exposure, inspect logs, and
treat internet-facing farms as incident-response candidates until proven
otherwise. CISA’s KEV listing is the strongest signal
that this needs priority handling.
What is the SharePoint Spoofing Vulnerability?
A SharePoint server vulnerability in the spoofing category usually means an attacker can manipulate trust around network-delivered content or server behavior in a way that misleads users or downstream systems.
In Microsoft’s own description, successful exploitation can affect confidentiality and integrity, even if it does not directly map to an availability impact. That makes this kind of flaw different from a ransomware-style outage, but not less serious.
This specific SharePoint server spoofing vulnerability is tied to improper input validation. NVD describes it as a network-based spoofing issue that an unauthorized attacker can exploit.
That detail matters because it suggests defenders should think beyond simple browser warnings or page defacements. Trusted server responses, identity-linked workflows, and document-heavy collaboration paths can all become part of the risk picture.
A lot of readers also mix up spoofing, remote code execution, and privilege abuse. They are not the same. RCE is about running code.
Privilege abuse is about gaining higher rights. Spoofing is about trust and deception. But in real intrusions, these categories can support each other. A spoofing foothold may help hide malicious behavior or improve phishing success inside a trusted business process.
Why This SharePoint Vulnerability Matters Right Now
The first reason is simple. Over 1300 SharePoint servers being vulnerable is not a small tale of stragglers.
It is a large, visible attack surface. Reporting tied to Shadowserver data said fewer than 200 systems had been patched since Microsoft released the fix, leaving a large number of exposed servers still reachable online. That is exactly the kind of lag attackers watch for after Patch Tuesday.
The second reason is timing. This was flagged as exploited in the wild when Microsoft patched it, and CISA quickly added it to the KEV catalog.
That combination changes the story from “security update available” to “real attacker activity confirmed.” A recent SharePoint vulnerability with public exploitation status deserves a faster patch cycle than a routine maintenance item.
The third reason is architectural. An on-prem SharePoint vulnerability is rarely isolated. These servers often sit near document libraries, identity systems, intranet portals, approvals, workflow tools, and internal search. If one becomes a trusted foothold, the security problem can spread far beyond SharePoint itself.
Which SharePoint Versions Are Affected?
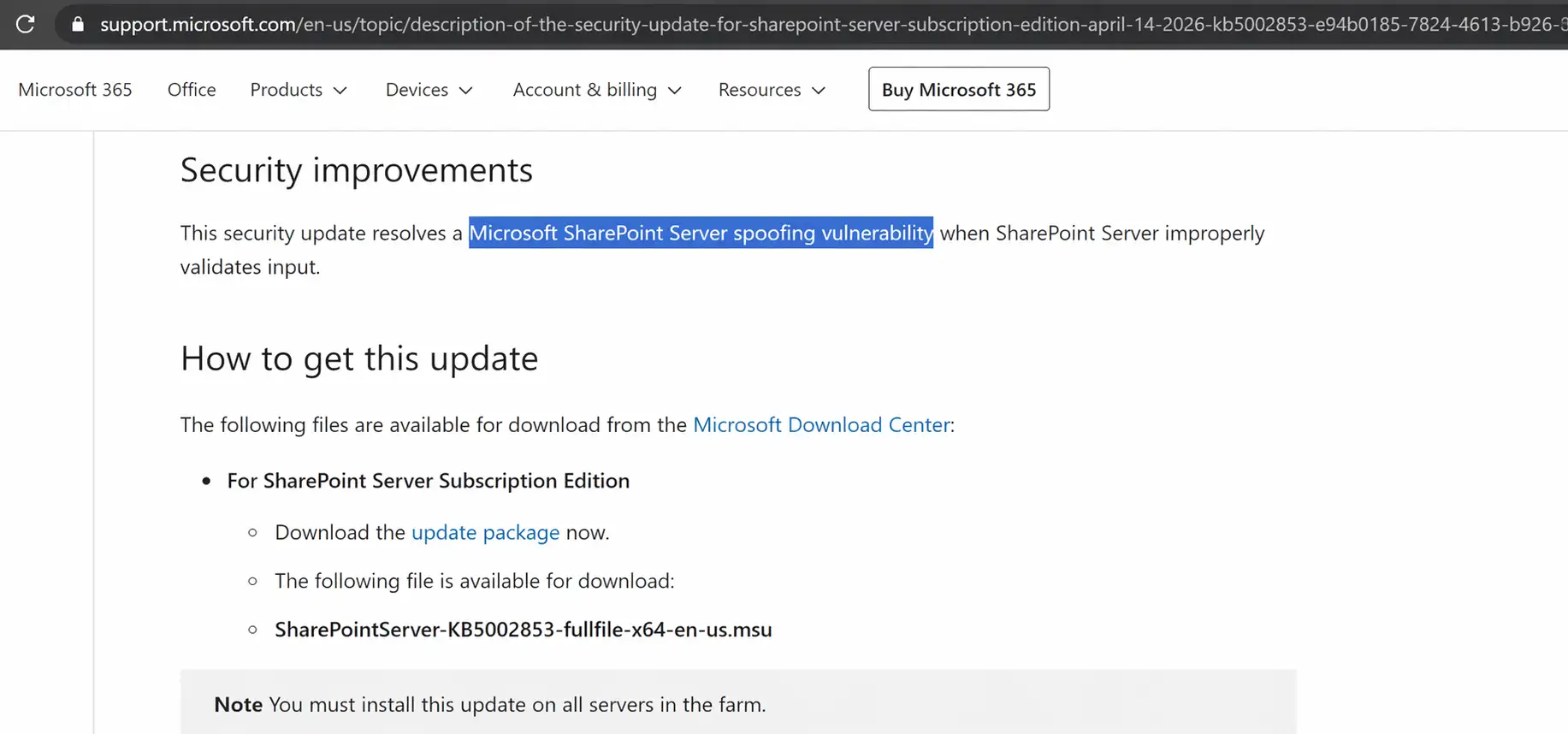
Microsoft’s April 14, 2026, support pages show security updates for SharePoint Server 2016, SharePoint Server 2019, and SharePoint Server Subscription Edition, and those pages explicitly tie the updates to resolving a SharePoint spoofing vulnerability associated with CVE-2026-32201.
For admins searching which SharePoint versions are affected, those are the products to review first.
For SharePoint 2016, Microsoft lists KB5002861 and build 16.0.5548.1003 in the support material surfaced by search.
For SharePoint 2019, the relevant security package is KB5002854 with build 16.0.10417.20114. For the subscription edition, the update is KB5002853 with build 16.0.19725.20210. These build details are useful when a team is trying to validate patch success across multiple farms.
Is SharePoint Online affected?
Public guidance around this on-prem SharePoint vulnerability focuses on SharePoint Server products. That is an important distinction.
If your organization uses only SharePoint Online in Microsoft 365, this specific on-premises SharePoint server vulnerability is not documented in the same product scope.
Still, security teams should communicate that distinction carefully so cloud users do not confuse brand name overlap with product exposure.
CVE-2026-32201 Explained
CVE-2026-32201 is the identifier that ties together Microsoft’s advisory, support pages, vulnerability databases, and most reputable news coverage.
NVD says it involves improper input validation in Microsoft Office SharePoint and allows an unauthorized attacker to perform spoofing over a network. Security reporting and Microsoft-linked sources describe the issue as actively exploited before or at patch time.
Why does that matter? Because a SharePoint CVE with active exploitation and public internet exposure does not need a dramatic CVSS to become dangerous.
This is where many incident queues go wrong. Teams see “important” instead of “critical,” then defer it. Attackers do not care about that label.
They care about exposed systems and delayed patching. This is one of the clearest lessons from this Microsoft SharePoint CVE.
A second point worth making: some public details remain limited. Microsoft has not publicly disclosed exploit-chain specifics or attributed the attacks to a named actor in the materials reviewed here.
When exploit mechanics are still sparse, defenders should avoid guesswork and focus on concrete action: patch, reduce exposure, inspect authentication behavior, and validate integrity.
How Attackers Can Exploit a SharePoint Spoofing Attack
A SharePoint spoofing attack is dangerous because SharePoint is a trust platform. Users expect document links, internal pages, approval paths, and search results from it to be legitimate.
If an attacker can abuse server-side trust signals or input handling, that can create downstream opportunities that look ordinary at first glance.
The initial access scenario is not always flashy. It may look like a crafted request path, a manipulated response flow, or content that appears to come from a trusted internal server.
From there, attackers may seek unauthorized visibility into information, alter trusted data paths, or support a wider SharePoint server attack aimed at internal users and connected services.
That is why "How serious is SharePoint vulnerability?" is the wrong question if it is asked only through the lens of raw CVSS.
Potential downstream risks include the following:
· Unauthorized access to sensitive document paths or metadata
· Phishing amplification through trusted internal-looking content
· Lateral movement risk if SharePoint is integrated with other business systems
· Trust-chain compromise inside approval or workflow processes
· Document access exposure involving confidential or regulated data
Those are the practical business risks, and they are why "can SharePoint be hacked" is no longer a theoretical search query in this case.
Signs Your SharePoint Server May Be at Risk
If you are asking how to check SharePoint server vulnerability, start with exposure and patch status. Is the server internet-facing? Is it still on a vulnerable build?
Was the April 2026 SharePoint security update applied successfully across every node in the farm? Those checks sound basic, but they catch a surprising number of misses in real environments.
Then look for authentication oddities, unusual page requests, or workflow-related anomalies. A spoofing issue may not present like a loud malware infection.
It can show up as suspicious access patterns, unexpected content behavior, or trust relationships behaving differently than expected.
If a team patched late, that should not end the investigation. It should start it. Unpatched SharePoint servers that were internet-reachable need log review and targeted validation.
How to Fix the SharePoint Spoofing Vulnerability
This is the part readers actually need. How to fix SharePoint spoofing vulnerability starts with patching, but it cannot stop there.
1. Apply the April 2026 SharePoint updates
Use the product-specific update path for your deployment:
· SharePoint Server 2016: KB5002861
· SharePoint Server 2019: KB5002854
· SharePoint Server Subscription Edition: KB5002853
Microsoft’s support pages explicitly tie these packages to the spoofing issue.
2. Verify the build after installation.
Do not trust a deployment dashboard alone. Check the installed build and confirm farm consistency. A partial update can leave one server behind and preserve the attack path. This is one of the easiest ways a SharePoint server vulnerability fix looks complete on paper while failing in practice.
3. Review Workflow Manager prerequisites.
Microsoft’s Subscription Edition support page warns that farms running SharePoint Workflow Manager need an additional update path, and classic Workflow Manager may require a debug-flag workaround to keep functioning. Stefan Goßner’s SharePoint guidance also points admins to patching best practices and a permissions issue affecting some environments.
4. Restrict internet exposure
If your SharePoint farm is reachable from the public internet, ask the hard question: Does it still need to be? Reducing direct exposure is one of the best SharePoint spoofing attack mitigation steps available, especially while organizations validate their patch state.
5. Inspect logs and identity-linked workflows
Look for unexpected requests, odd auth behavior, unexplained page rendering anomalies, and unusual workflow actions.
Because Microsoft has not published detailed exploit IOCs in the sources reviewed here, defenders should be honest about uncertainty and rely on anomaly hunting rather than waiting for a perfect signature set.
6. Rotate credentials or secrets if compromise is suspected.
If there is evidence of tampering, suspicious admin actions, or questionable integration behavior, move beyond patching. Credential rotation and incident-response containment may be necessary. That is the difference between a patch job and real remediation.
SharePoint Vulnerability Mitigation Checklist
Use this list to confirm you have covered the critical bases:
· Patch all affected SharePoint Server versions to the April 2026 build
· Verify build numbers in PowerShell post-patch
· Confirm internet-facing instances are identified and prioritized
· Apply firewall or WAF rules to limit external exposure
· Audit authentication events for anomalous IP addresses or session reuse
· Check admin accounts and review recent permission changes
· Review IIS access logs for unusual request patterns on layout and list endpoints
· Inspect reverse proxy or WAF rules for adequate coverage
· Review CSP headers on internet-facing SharePoint sites
· Back up critical SharePoint content before making major configuration changes
· If exposure window existed, run through incident response validation
· Document every remediation step for audit and compliance records
· Set an internal SLA for future KEV-listed patches of 7 days or fewer
That is the practical SharePoint vulnerability for admins' workflow. Short. Useful. No filler.
SharePoint Online vs On-Prem: What’s the Real Risk?
This is the section many pages skip, and readers need it. Does SharePoint Online have this vulnerability? is one of the most important clarifying questions.
Based on the Microsoft support materials tied to CVE-2026-32201, the affected products are the on-prem server versions, not SharePoint Online.
Why do people mix them up? Because “SharePoint” is used as one brand umbrella. But from a security response perspective, SharePoint Online and SharePoint Server are different operational realities. Microsoft handles patching in the cloud service.
On-prem admins own the patch window, the exposure decisions, and the recovery plan. That is why this SharePoint 2016 2019 subscription edition vulnerability is especially important for organizations still running internal or hybrid infrastructure.
Why This Important
Our team looks at risk through a business lens first. This Microsoft SharePoint vulnerability is not just a server bug.
It lands in a platform where trust, collaboration, documents, and internal process all meet. If an attacker can abuse that trust layer, the downstream damage is often bigger than the label “spoofing” suggests.
For a business, the danger is not only data exposure. It is process corruption. Approval flows, internal knowledge hubs, legal document access, HR forms, procurement records, and project collaboration can all sit behind SharePoint.
A Microsoft SharePoint spoofing vulnerability can undermine confidence in those systems. Once users stop trusting what the portal shows them, productivity and security both suffer.
For individual users, the issue feels less technical and more personal. A trusted intranet page or internal link is exactly the kind of thing people do not second-guess. That is why how to protect SharePoint from attacks is not just an admin topic. It is also a trust and communication problem.
What stands out here is the mismatch between public severity and operational urgency.
The SharePoint vulnerability CVE is not the highest-scoring issue Microsoft has ever shipped, but it is live, exposed, and aimed at a platform that many organizations forget is still internet-reachable. That combination tends to age badly.
We also think patch latency is the real story. The data point about SharePoint vulnerability—1300 servers still exposed days after patch release, tells you something uncomfortable: a lot of organizations still treat SharePoint as background infrastructure. Attackers do not. They see an old habit in enterprise IT and turn it into an opportunity.
Field Notes
When we ran a practical review of how teams usually respond to this kind of SharePoint patch update, one pattern showed up fast. Admins check whether the patch is installed, then move on.
They do not always confirm farm consistency, connected services, or workflow dependencies. That is how “patched” and “secure” become two different realities.
In our practical test planning, we noticed another challenge. SharePoint environments are often messy in ways that do not show up in the architecture diagram.
There is an old workflow dependency here, a reverse proxy rule there, and maybe a publishing site nobody wants to touch. That is why SharePoint server hardening has to be treated as an ongoing discipline, not a one-day patch event.
Common Mistakes
Three mistakes keep showing up in real environments:
· Assuming SharePoint Online affected is the same question as SharePoint Server exposure
· Treating a successful install as the end of remediation
· Forgetting to review internet exposure after the SharePoint spoofing vulnerability patch
There is also a communication mistake. Security teams sometimes send out a broad advisory that scares Microsoft 365 users who are not actually in the affected product scope. A better approach is to separate cloud reassurance from on-prem urgency.
How to Build a Safer SharePoint Security Posture
A secure SharePoint server starts with routine, not drama. Patch management needs discipline. Exposure should be minimized by design. Logs should be retained long enough to support incident review. External publishing paths should be justified, not assumed.
In the long term, the best SharePoint security best practices are boring on purpose. Regular update cycles. Hardening reviews. Access control cleanup. WAF and reverse-proxy validation.
Segmentation. Backup testing. Workflow dependency mapping. None of these will trend on social media. All of them reduce the blast radius of the next SharePoint vulnerability update.
Quick Comparison
|
Question |
Answer |
|
Is SharePoint vulnerable? |
Yes, on-prem SharePoint Server versions are affected by CVE-2026-32201 |
|
Is SharePoint Online affected? |
Public documentation reviewed here points to on-prem server products, not SharePoint Online |
|
Is this a zero day? |
Microsoft and multiple security outlets describe it as exploited in the wild at patch time |
|
What should admins do first? |
Patch, verify builds, reduce exposure, inspect logs, review auth behavior |
Security Checklist
You do not need a giant war room to start fixing this. Do these three things in the next five minutes:
1.
Identify exposure
Confirm whether any internet-facing SharePoint Server 2016, 2019, or
Subscription Edition systems are still running.
2.
Confirm the patch
Verify the April 2026 SharePoint
spoofing vulnerability patch is installed on every node and the
farm build matches the expected package.
3.
Treat late patching as a
possible compromise
Review logs, auth behavior, admin actions, and connected workflows if the
server was exposed while unpatched.
Published: April 22, 2026
Last updated: April 22, 2026
Author: Radia | Senior
Cybersecurity Analyst & Breach Reporter.Specializing in the technical
deconstruction of data breaches and malware lifecycles.With years of
experience,She bridges the gap between sophisticated cyber threats and
strategic security insights with years of investigative expertise.
Was this article helpful?
React to this post and see the live totals.
Share this :