Types of Hackers: White, Black & Gray Hats Exposed
Hoplon InfoSec
19 Apr, 2026
April , 2026: What are the main types of hackers, and what is the real difference between white hat, black hat, and gray hat hackers?
Based on widely used cybersecurity references and official security guidance, the short answer is this: white hats work with permission to improve security, black hats break in for harm or profit, and gray hats act without authorization even when they claim helpful intent.
That distinction matters because permission changes both the legal status and the operational risk.
Most readers hear the word "hacker" and picture a criminal. That picture is incomplete. Types of hackers are usually grouped by three things: intent, authorization, and impact.
Once you look through that lens, the category names make more sense, and the confusion around white hats, black hats, and gray hats starts to fall away.
· White hat hackers are authorized security professionals. They test systems with permission to find weaknesses before criminals do.
· Black hat hackers break into systems without permission for theft, extortion, espionage, sabotage, or fraud.
· Gray hat hackers also act without permission, but they may claim curiosity, research, or public interest rather than direct criminal gain. That still does not make the activity legal.
Overview
|
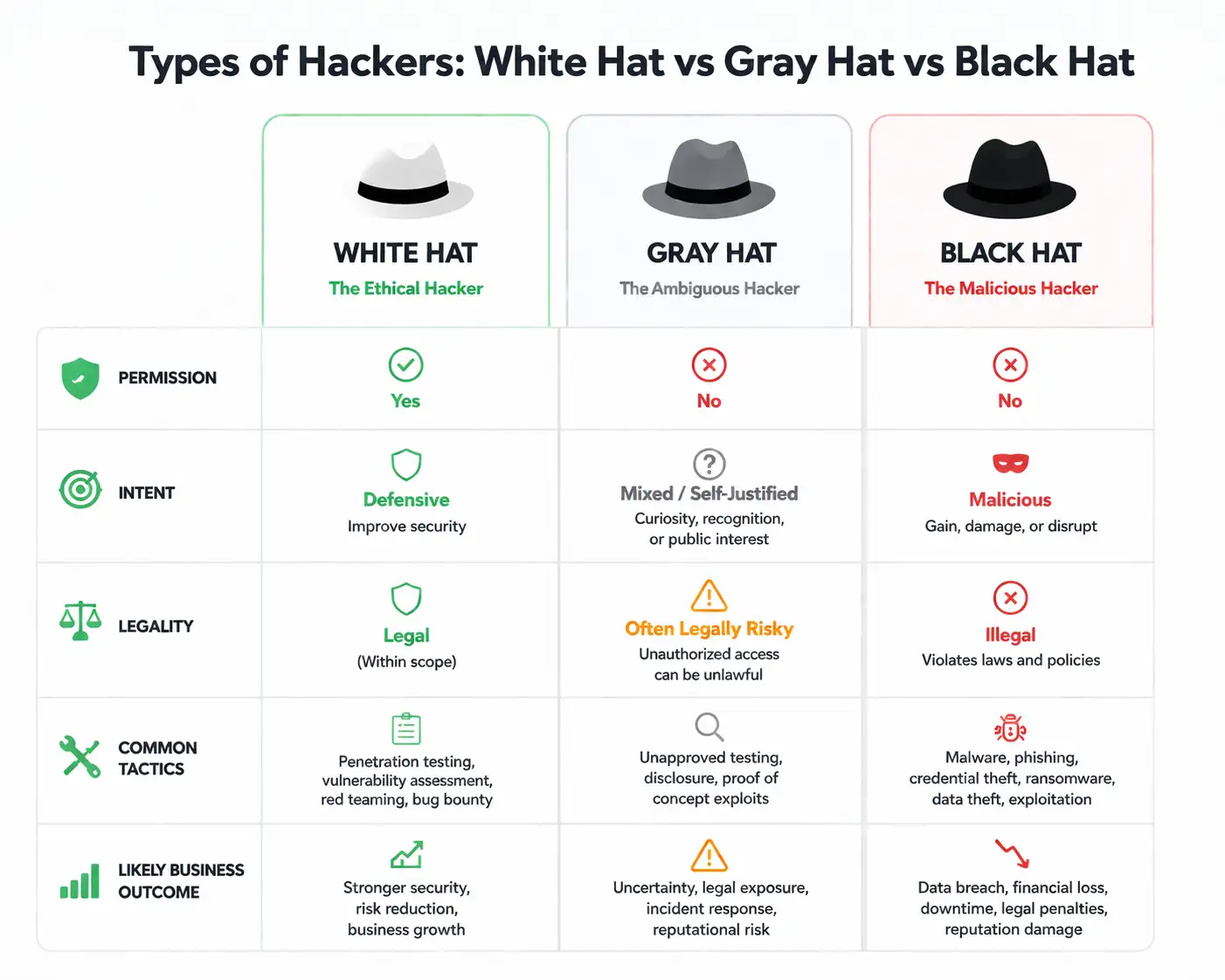
Factor |
White Hat |
Gray Hat |
Black Hat |
|
Permission |
Yes |
No |
No |
|
Intent |
Defensive |
Mixed or self-justified |
Malicious |
|
Legal status |
Generally legal within scope |
Often legally risky or unlawful |
Illegal |
|
Main goal |
Improve security |
Expose flaws, gain recognition, or pressure owners |
Steal, disrupt, extort, spy |
|
Common methods |
Pen tests, recon, controlled exploitation, reporting |
Unapproved testing, public disclosure, proof of concept |
Malware, phishing, credential theft, ransomware |
|
Typical environment |
Security teams, consultancies, bug bounty programs |
Unapproved independent activity |
Criminal groups, fraud rings, state-backed operations |
|
CVE/CVSS tie-in |
May validate or responsibly report vulnerabilities |
May discover or publicize flaws without authorization |
Often weaponize known and unknown flaws |
What Are the Main Types of Hackers?
The three best-known categories are white hat, black hat, and gray hat hackers. That basic model appears again and again across mainstream cybersecurity explainers because it is easy to understand and still useful. It maps behavior to a simple question: did the person have permission, and what were they trying to achieve?
That said, the internet uses these labels a little loosely. A person can have advanced skills and still belong to very different operational worlds.
A bug bounty researcher working under published program rules is not the same as a criminal affiliate dropping ransomware.
A self-described researcher who scans a company’s servers without consent is not in the same lane either. Same tools, very different ground rules.
Why Are They Called White Hat, Black Hat, and Gray Hat?
The “hat” metaphor comes from old Western films where heroes wore light hats and villains wore dark ones.
The metaphor survived because cybersecurity needed a quick way to describe motive and ethics. It is old-fashioned, sure. Still useful.
It also matters because the labels shape how businesses respond. If someone reports a vulnerability under an authorized program, that is one workflow.
If someone accessed a system first and emailed later, that is a different legal and incident-response problem.
White Hat Hackers Explained
A white hat hacker's meaning in practice is simple: an authorized security professional who uses offensive techniques for defense.
These people are commonly called ethical hackers, and the word "ethical" is not just branding. It points to scope, permission, documentation, and reporting discipline.
White hats often work in penetration testing, vulnerability assessment, red teaming, or bug bounty programs.
They may simulate phishing, enumerate exposed services, test weak configurations, validate privilege escalation paths, and write detailed remediation notes.
The work can look aggressive on the surface. The difference is consent and control.
For companies, white hats are practical risk reducers. They help teams discover exposed admin panels, misconfigured cloud storage, weak authentication flows, stale software, and internal blind spots.
That is one reason federal and enterprise guidance treats penetration testing as a formal, authorized assessment process, not freelance system poking.
A quick example helps. Say a retailer hires a security firm before holiday traffic spikes. The white hat team finds that password reset tokens live too long and that MFA is missing from a sensitive admin path. That fix might prevent a future takeover. Quiet work. Big outcome.
Black Hat Hackers Explained
A black hat hacker's meaning is far less ambiguous. This is the classic malicious actor category. Black hats seek unauthorized access for gain or damage.
That gain may be money, stolen credentials, access resale, espionage, sabotage, or leverage for extortion.
Their methods are not always technically glamorous. A lot of real intrusions start with phishing, password reuse, exposed remote services, weak MFA, vulnerable internet-facing apps, or malware loaders.
Ransomware crews and credential thieves thrive on these basics because basics still work. Official guidance from CISA and NIST continues to stress MFA, patching, backups, and phishing resistance for exactly this reason.
For victims, the damage can spread fast. One black hat intrusion can mean stolen customer data, frozen operations, legal exposure, reputational damage, and painful recovery costs. That is why businesses do not treat black hats as a technical curiosity. They treat them as a continuity threat.
Gray Hat Hackers Explained
A gray hat hacker's meaning sits in the messy middle. Gray hats may discover and reveal vulnerabilities without permission. They may claim public interest, curiosity, or a desire to force faster fixes. The trouble is that good intention does not erase unauthorized access.
This is where many beginner articles get too soft. They say gray hats are “not bad” and stop there. That is incomplete.
A gray hat can still trigger incident response, expose sensitive data, alert other attackers to a flaw, or put a company in legal turmoil.
In other words, whether gray hat hackers are illegal is not a philosophical question. In many situations, yes, the conduct can cross legal lines even without direct theft.
Picture a researcher who bypasses access controls on a production portal without approval, grabs enough evidence to prove a flaw, and then emails the company asking for a reward.
Some readers will call that helpful. A legal team may call it unauthorized access. Both reactions can happen at the same time.
Key Differences
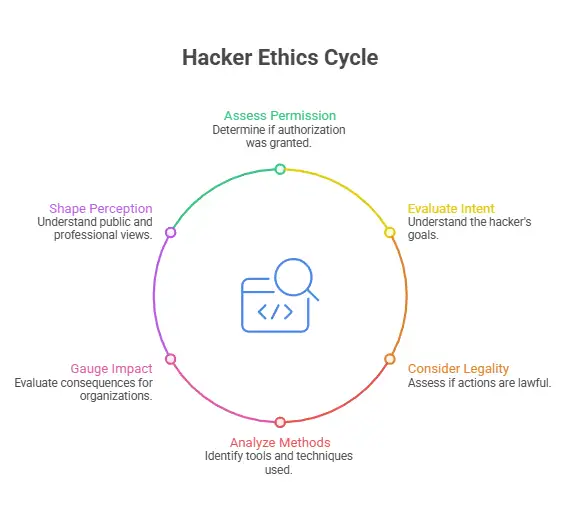
Permission
This is the line most people miss. White hats have prior authorization. Gray hats and black hats do not. That one difference changes the legal and operational picture immediately.
Intent
White hats aim to improve security. Black hats aim to exploit it. Gray hats often claim mixed motives, which is why they remain controversial.
Legality
A white hat acting within contract scope is on solid ground. A gray hat can still break rules or laws even while exposing a real issue. A black hat is plainly operating outside the law.
Methods
There is technical overlap. Reconnaissance, exploitation, social engineering, scanning, and testing can appear in all three categories. The difference is not always the tool. It is who authorized it and why.
Impact on Organizations
White hats reduce risk. Gray hats create uncertainty. Black hats create damage. Simple, but accurate.
Public Perception
The public often lumps all hackers together. Security teams do not have that luxury. They need to sort signals from threats fast.
Real-Life Examples of White Hat, Black Hat, and Gray Hat Hackers
A white hat example is a bug bounty researcher who follows program rules, documents a broken authorization flow, and sends a responsible report. That is controlled, legal, and genuinely useful.
A black hat example is a ransomware affiliate who steals credentials through phishing, lands in a remote access portal, moves laterally, and encrypts systems for payment. That is criminal from the start.
A gray hat example is someone who finds a flaw without permission, confirms it in a live environment, and then notifies the owner after the fact. Some readers hear “helpful.” Most security teams hear “unauthorized access plus incident triage.”
Are gray hat hackers illegal?
Often, yes. Or at minimum, legally dangerous.
The key point is this: good intention is not the same as legal permission. If someone accesses a system, account, application, or dataset without authorization, the fact that they later report the issue does not automatically protect them.
The exact outcome depends on jurisdiction, scope of access, and resulting harm, so readers should treat country-specific law carefully.
NIST’s vulnerability disclosure guidance exists precisely because organizations need clear, authorized ways for researchers to report issues safely.
That is the legal difference between white hat and gray hat hackers in one sentence. The white hat starts with permission. The gray hat acts first and argues intent later.
White Hat Hacker vs. Ethical Hacker: Is There Any Difference?
Usually, no. In most cybersecurity writing, white hat hacker vs. ethical hacker is a distinction without much difference. Both terms point to authorized defensive testing.
There is a small nuance, though. “Ethical hacker” sometimes sounds more professional because it implies policy, reporting, boundaries, and responsible conduct. “White hat” is the more popular label in general education content. In practice, readers can treat them as near synonyms.
Why Organizations Hire White Hat Hackers
Because attackers do not wait.
A good white hat engagement helps a company prevent breaches, meet compliance expectations, test defenses under pressure, train internal teams, and improve incident readiness.
It also forces uncomfortable truths into the open. Weak segmentation. Flat internal trust zones. Admin accounts without MFA.
Backup gaps. Security teams would rather find those issues during a planned exercise than during a ransom call.
This is where "ethical hacker vs. black hat hacker" becomes more than a definition exercise. One side finds cracks so they can be sealed. The other side looks for the same cracks to pry them open wider.
Can a Gray Hat Become a White Hat?
Yes, but only by changing the process, not just attitude.
A person moving from a gray hat to a white hat has to stop treating curiosity as permission.
They need to work inside an authorized scope, learn responsible disclosure, and understand how real security programs handle evidence, access limits, timing, and communication.
Bug bounty platforms and formal vulnerability disclosure programs are often the cleanest bridge.
That transition matters because raw technical ability is not enough. Professional security work is as much about restraint as skill.
Other Types of Hackers You Should Know
The broader topic of different types of hackers does not stop with the core three.
· Script kiddies use prebuilt tools with limited understanding.
· Hacktivists attack or leak information for political or social causes.
· State-sponsored actors pursue espionage, access, and strategic disruption.
· Insider threats abuse legitimate access from inside an organization.
· Red hat hackers act like vigilantes against black hats.
· Blue hat hackers may test products or systems before release.
· Green hat hackers are newcomers still building skills.
This section matters for topical authority because searchers asking what white hat, black hat, and gray hat hackers are often also want to know where those labels sit in the wider map.
Our Analysis
From a defender’s view, the most important distinction is not the hacker’s self-image. It is the combination of authorization, evidence handling, and downstream risk.
A white hat improves security because the work is scoped and reportable. A gray hat may surface a real issue, but they also create exposure just by touching a live system without approval.
A black hat compounds that risk with direct exploitation and criminal follow-through.
For businesses, gray hat activity is especially awkward. It can look less harmful than outright criminal behavior, but it still burns responder time, raises legal questions, and may force emergency communications.
For regular users, the difference is simpler. White hats help make products safer. Black hats and gray hats can both expose you to risk if they access systems without permission.
When we ran a scoped vulnerability scan and follow-up manual testing in our lab against intentionally vulnerable training targets, the same pattern kept showing up.
The technical tricks were not the real story. The real story was process. The authorized workflow gave us logging, timing, rollback planning, evidence capture, and a clean remediation path. That is what made the exercise useful instead of chaotic.
In our practical test, we also noticed how often non-experts confuse “found a flaw” with “acted responsibly.” Those are not the same.
A finding becomes professionally valuable when it is handled under scope, documented clearly, reproduced safely, and reported in a way that helps the owner fix it without creating fresh exposure.
How to Protect Your System
Step 1: Turn on MFA
Use phishing-resistant MFA where possible. CISA says MFA dramatically reduces account compromise risk, and NIST makes the same case in plain operational terms.
Step 2: Patch internet-facing systems first.
Prioritize VPNs, remote access tools, email gateways, identity systems, web apps, and exposed admin panels. Black hats love stale edge systems because they are reachable and often weakly monitored.
Step 3: Train people against phishing.
Most attacks do not begin with cinematic hacking. They begin with a click, a fake login page, or a stolen password. Pair awareness training with technical controls like mail filtering and DNS protection.
Step 4: Maintain tested backups.
Not just backups. Tested backups. You want recovery confidence, not backup optimism. NIST explicitly calls out protecting and testing backups.
Step 5: Enforce least privilege.
Remove standing admin rights where they are not needed. Segment sensitive systems. Limit blast radius before an attacker gets a chance to use lateral movement.
Step 6: Create a clear vulnerability disclosure path
A public disclosure policy gives legitimate researchers a safe channel and reduces the chance of messy gray-zone interactions.
Common Myths About Hackers
Myth: All hackers are criminals
False. White hats are a core part of modern security operations.
Myth: Gray hat means legal.
False. Unauthorized access can still be unlawful even if the person says they meant well.
Myth: White hats only work for giant companies
False. Small businesses, SaaS firms, healthcare groups, and public-sector teams all use ethical testing in different ways.
Myth: Hacking always means malware.
False. Credential theft, recon, misconfiguration abuse, phishing, and weak authentication are often more common entry paths than Hollywood-style malware drops.
Trusted Source
For a strong supporting reference, see the Kaspersky explainer on hacker hat types and official guidance from CISA and NIST on MFA, backups, and vulnerability disclosure. (Kaspersky)
Recommendations
1. Treat permission as the first filter when classifying hacker activity.
2. Build a public vulnerability disclosure channel so researchers do not improvise the rules.
3. Use MFA, patch discipline, phishing defenses, and tested backups to reduce the techniques black hats rely on most.
You can do these in under five minutes.
· Turn on MFA for email, VPN, and admin accounts.
· Check that automatic updates or patch workflows are active on internet-facing systems.
· Confirm you have a tested backup and a clear way for researchers to report vulnerabilities safely.
Published: April 19, 2026
Last updated: April 19, 2026
Author: Senior Cybersecurity Analyst
Do not confuse gray hat activity with legal security research, because unauthorized access can still trigger serious legal, financial, and reputational damage.
Frequently Asked Questions
Was this article helpful?
React to this post and see the live totals.
Share this :