Weekly Cybersecurity Intelligence Brief: Important Threats

Hoplon InfoSec
06 Mar, 2026
Important Cyber Threats This Week
What are the most important threats that businesses need to know about right now?
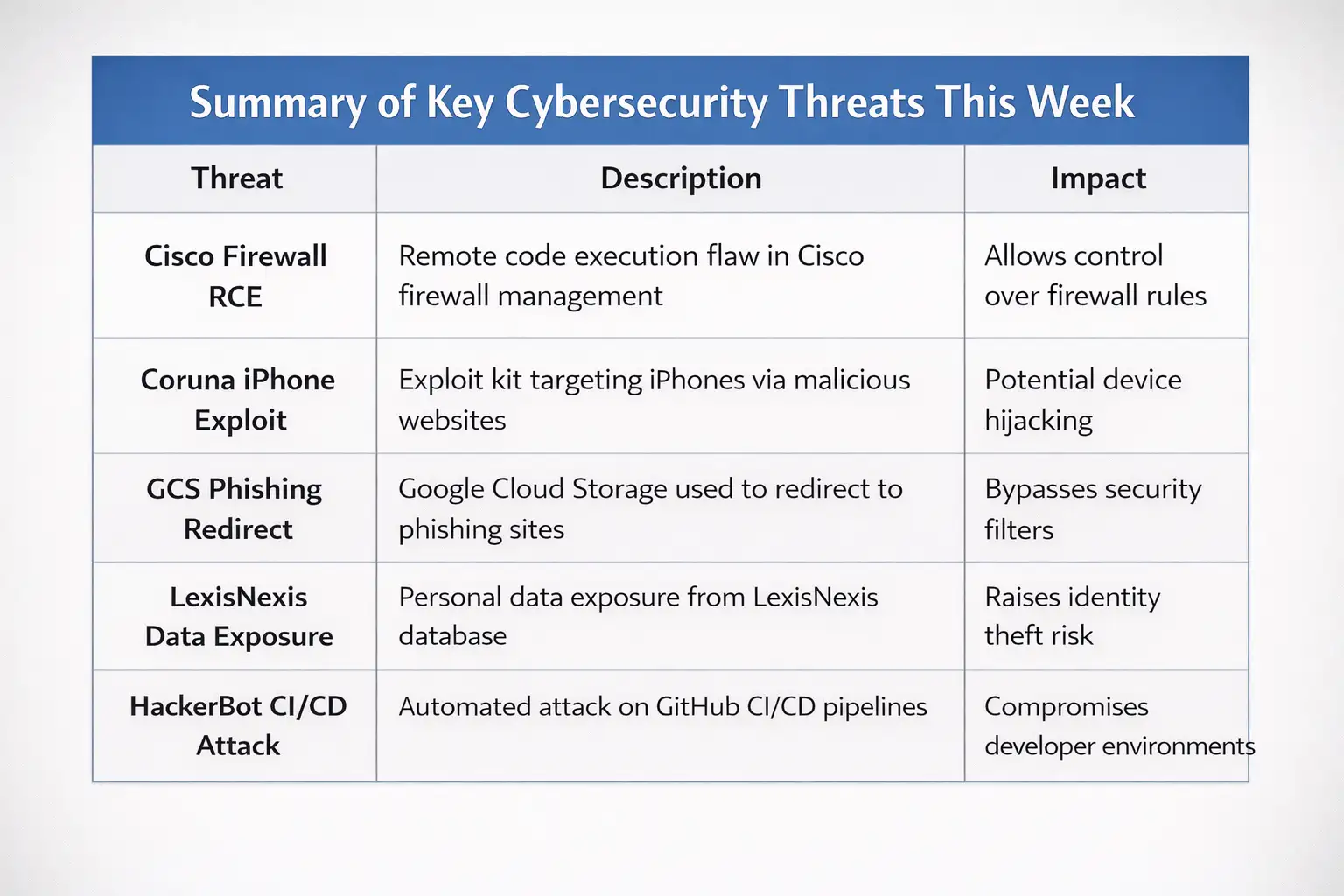
What are the most important threats that businesses need to know about right now? New security studies show a group of threats that include corporate firewalls, cloud infrastructure, policy conflicts in AI, supply chain weaknesses, and privacy concerns on a large scale.
Things like Google Cloud storage, developer pipelines, Mac software downloads, and even smart TVs in people's houses are all affected by these problems.
In the past, cybersecurity was reactive. After damage showed up, companies fixed their systems.
The shift has changed.
Old method: find breach after deal
Different way: Monitoring threat information all the time
The end result is faster defense, a smaller attack area, and fewer problems with operations.
It looks at confirmed security news from the past week, such as the
Firewall flaw, the Corona iPhone exploit kit, Google Cloud phishing redirect abuse, the LexisNexis data leak, CI/CD pipeline attacks, AI governance conflicts, macOS supply chain threats, and a big smart TV privacy settlement.
Understanding these changes early on helps lower operating risk for people in charge of security and business decisions.
Why this week is important
Malware operations aren't the only type of cyber threat anymore. This is what the attack surface has grown into:
• Buildings for the cloud
• The use of AI
• Pipelines for CI/CD
• IoT gadgets for consumers
• Distribution of open-source software
Attackers now have a new way to get into each of these places.
Misconfigurations and automation tools are becoming main targets for hackers, according to studies from a number of different companies and incident reports.
Companies that use automated deployment tools or hybrid clouds should pay extra attention.

Firewall RCE from Cisco
What took place
Security experts found a flaw in Cisco Secure Firewall Management Center that lets hackers run code remotely. If the flaw is used correctly, it could let an attacker run orders from afar.
Cisco admitted the flaw and put out official security advice and patches.
Because of a flaw in Cisco Secure Firewall Management Center, attackers from afar might be able to control systems that are impacted. Cisco confirmed the problem and sent fixes to lower the risk.
How It Works
The weakness is in the management tool that is in charge of setting up firewall policies.
This is how the process works in simple terms:
Requests for configurations are handled by the management center.
Some data are not properly validated.
A carefully written request could let a command run.
Remote code execution bugs are a bigger group that this type of flaw belongs to.
Attackers could get more control over firewall technology if they found a way to use it.
Why it's important
Firewall management tools decide what rules apply to network traffic. If hackers got in, they could:
• Change the rules for security.
• Turn off safety features
• Move from side to side in business networks
When big businesses use centralized firewall control, the risk is no longer just an idea; it becomes real.
Coruna iPhone Hack
What it is
Security experts have found an attack kit called Coruna that targets iPhone users by using bad web infrastructure.
Exploit kits make it easier to find holes in devices and send messages to them automatically.
Coruna is an exploit system that looks for holes in users' browsers or devices when they visit websites that have been hacked.
How to use an exploit kit
It's easy to see how exploit kits work.
The user goes to a rogue page.
Fingerprinting of the device starts.
The exploit starts if a flaw is found.
Often, steps include:
• Finding the device and OS
• Matching by vulnerability
• Delivery of payload
Apple devices have always had strong security features, but attack kits are still trying to break into systems that haven't been updated.
GCS Redirect for Phishing
What took place
Attackers were abusing Google Cloud Storage (GCS) to host redirect tools that were used in phishing operations, according to security experts.
These ads take advantage of people's trust in cloud technology.
Attackers used links to Google Cloud Storage to take people to phishing sites. They did this by using the trustworthiness of cloud platforms to get around security screens.
Why Hackers Get into the Cloud
Attackers are relying more and more on legitimate cloud services.
Some reasons are:
• Sites you can trust
• HTTPS traffic that is encrypted
• Available everywhere
Malicious material can get mixed up with good traffic because many security filters let cloud infrastructure work by default.
LexisNexis Data Breach
What took place
Several reports came out about a data breach involving a LexisNexis dataset. According to investigations, some records of personal information were open to the public.
LexisNexis is used by a lot of people to check their identities and find legal information.
It was said that a LexisNexis dataset was made public, which raises worries about who could see personal data used in identity verification systems.
The importance of identity data
Identity information is very private.
Information such as:
• Name
• Address
• Identification numbers
• Credit history
can be used in fraud or identity theft.
Financial institutions and credit agencies rely heavily on these databases.
HackerBot Attack on CI/CD
What took place
Researchers found an automated attack method called HackerBot Claw that targets CI/CD processes by misconfiguring GitHub Actions.
HackerBot Claw is an automated scanning tool that looks through GitHub projects for secrets that are out in the open or pipelines that aren't set up correctly.
Why Pipelines Are Being Sought
Automation is a big part of how modern software is delivered.
Constant integration channels keep private parts like:
• API keys
• cloud credentials
• tokens for deployment
Attackers can quickly get into infrastructure if these secrets are found in files.
A single repository that isn't set up right can make whole systems vulnerable.
Claude Memory Battle
What took place
People talked about the Claude AI memory feature and how data could be moved from other AI systems, like ChatGPT.
Some online claims said that chat data could be moved directly.
Automatic data transfer between AI systems has not been confirmed by government sources that can be trusted. There is still no proof of claims of cross platform memory movement.
If these kinds of claims show up in reports, they should be taken with a grain of salt until they are backed up by government documents.
Not Real Homebrew Sites
What took place
Researchers found fake websites that looked like Homebrew, a famous package manager for macOS.
Attackers made fake Homebrew websites to spread harmful software that looked like real developer tools.
Why Developers Are Being Sought
Developers often trust command line package managers.
If attackers pretend to be those tools, victims may install malware directly through terminal commands.
The impact can include:
• system backdoors
• credential theft
• software supply chain compromise
Samsung TV Cover for Privacy
What took place
Samsung reached a settlement related to allegations that its smart TVs collected viewing data without sufficient user disclosure.
A legal settlement addressed privacy concerns involving smart TV data collection practices.
Smart TV Data: Why It Matters
Smart TVs collect behavioral data such as:
• viewing habits
• app usage
• device identifiers
This information may be used for advertising analytics.
Privacy regulators have increased scrutiny over how consumer devices handle data.
Outage on AWS EC2
What took place
A regional service disruption affected Amazon Web Services EC2 infrastructure in the Middle East region.
The AWS outage temporarily affected compute availability in a regional cloud infrastructure zone.
Why power outages matter
Even short outages can impact:
• e commerce platforms
• fintech services
• SaaS applications
Organizations relying on a single region may experience downtime during such incidents.
Cloud resilience strategies increasingly rely on multi region deployment.
Pentagon Policy Conflict Over AI
What took place
Policy discussions emerged regarding AI deployment in defense environments and restrictions around certain AI models.
Policy debates around AI usage in defense organizations highlighted governance and security concerns surrounding advanced AI models.
Firefox Cleaner API
What took place
Firefox introduced support for the Sanitizer API, designed to reduce cross site scripting risks.
The Sanitizer API helps developers clean HTML content automatically, reducing the likelihood of XSS vulnerabilities.
Why XSS Is Important
Cross site scripting remains one of the most common web vulnerabilities.
Attackers exploit XSS to:
• steal session cookies
• inject malicious scripts
• hijack user sessions
The Sanitizer API provides a built in browser tool for safer HTML handling.
Business Owners Who Are Affected
Builders
Consumers
Police Forces
Security professionals must monitor multiple environments including cloud platforms, developer infrastructure, and consumer devices.
Pros of Finding Problems Early
Traditional approach relied on delayed incident response.
A threat intelligence model allows:
• faster vulnerability patching
• earlier attack detection
• reduced breach probability
Organizations that monitor vulnerability disclosures often reduce exposure windows significantly.
What Teams Need to Do
Security teams should take practical steps.
Patch critical systems
• Apply Cisco firewall updates immediately
Audit CI/CD pipelines
• remove exposed secrets
• rotate credentials
Monitor cloud infrastructure
• check storage permissions
• audit redirect behaviors
Validate software sources
• download Homebrew only from official repositories
Strengthen web security
• implement sanitization protections
• monitor XSS vectors
FAQ
What is the worst weakness that has been found this week?
The Cisco Secure Firewall RCE vulnerability is very important because it affects the core of business networks.
How do criminals take advantage of cloud services?
Attackers use trusted cloud platforms to host redirect links or malicious content that gets past security screens.
Exploit kits could hurt people who use iPhones.
Exploit kits try to get into devices that haven't been updated. Keeping operating systems up to date cuts risk by a large amount.
Why are attacks being made on CI/CD pipelines?
Often, these systems have passwords that are used for deployment. Attackers can quickly get into cloud technology if it is left open.
Should people who have smart TVs worry about the data they collect?
Privacy officials are still looking into how device makers collect and use data about how people use their devices.
Summary
Cyber threats are changing from simple campaigns of malware to ecosystem risks that affect cloud services, developer infrastructure, and consumer devices that are linked to the internet.
An early edge for businesses today is being seen.
The old model: security reaction after a breach.
Modern model: threat tracking and vulnerability information that happen all the time.
Companies can lower their risk before attackers get in because of this change.
Hoplon Infosec's main job is to help companies understand new threats without having to guess what they are. They do this by giving them security intelligence and vulnerability research.
When verified intelligence and useful ways to reduce risks are available, it's easier to make choices about security.
For more latest updates like this, visit our homepage.
Was this article helpful?
React to this post and see the live totals.
Share this :