What is Brute Force Attack? Types, Risks, and Prevention

Hoplon InfoSec
23 Mar, 2026
What is a Brute Force Attack?
It is a password and credential attack in which an attacker keeps trying login combinations until one works. In plain terms, the attacker relies on repetition, automation, or both to break into an account, device, or service. That basic definition aligns with guidance from OWASP, NIST, Microsoft, and CISA.
In the old way, many teams assumed a password alone was enough. The new way is that organizations treat login security as a layered control with rate limiting, MFA, lockout protections, and monitoring.
As a result, the cost of guessing credentials goes up sharply, and successful account takeover becomes much harder. That shift matters because brute force activity is still present in modern attacks, including real intrusions tracked by CISA.
If you are a business decision-maker, this topic is not just technical trivia. It touches revenue, trust, compliance, support costs, and customer experience.
One weak authentication flow can turn into account takeover, fraud, or a noisy incident response cycle. That is why understanding what a brute force attack is is less about theory and more about operational risk.
Why this topic matters now
A brute force attack sounds old-fashioned. In one sense, it is. Attackers have guessed passwords for years. But the method still survives because many environments still have predictable passwords, exposed login portals, stale accounts, and inconsistent protective controls.
CISA has documented recent campaigns where threat actors used brute force and password spraying to gain access to organizations, then modified MFA settings to keep that access.
That is the practical issue. The attack itself may be simple, but the business impact rarely is. Once an attacker gets in, the story changes from “failed login attempts” to “unauthorized access,” “data exposure,” or “service disruption.” You might not notice the first stage if no one is watching authentication logs carefully enough.
What is a brute force attack in cybersecurity?
A brute force attack is a password-guessing attack that systematically tests credentials until the correct combination is found. It can target a single account, many accounts, or even encrypted data depending on the attack design.
The idea is brutally simple. Try enough combinations; eventually one may work. In online attacks, the attacker submits guesses through a login page, VPN prompt, admin panel, RDP endpoint, or another authentication interface.
In offline attacks, the attacker may try to crack stolen password hashes after obtaining them through some earlier compromise. NIST specifically notes that short passwords are vulnerable to brute-force and dictionary attacks, and that online guessing can be reduced with login rate limits.
People often imagine a hoodie-wearing attacker manually typing random passwords. Real attacks are usually less dramatic and more automated. Scripts, botnets, cracking tools, and credential lists do the repetitive work.
That is one reason why what is a brute force attack remains such an important search topic for both security teams and general users.
Why brute force attacks still exist
You would think everyone learned this lesson already. Apparently not.
Attackers keep using brute force methods because they are cheap to attempt and sometimes still work. If users choose weak passwords, reuse old credentials, or leave exposed admin portals with minimal protection, an attacker does not need a clever exploit.
They just need patience, infrastructure, and a target that makes guessing practical. Microsoft and OWASP guidance both focus on reducing this exact risk with stronger authentication controls, lockout, and layered protection.
There is another reason too. Authentication failures often sit in that awkward zone between “background internet noise” and “real threat.” Teams can become numb to them. That is dangerous.
Repeated failed logins from one IP, one ASN, or one device type can be an early warning sign, not just harmless clutter. Fortinet’s operational guidance points directly to repeated authentication failures and abnormal login frequency as practical indicators defenders should investigate.
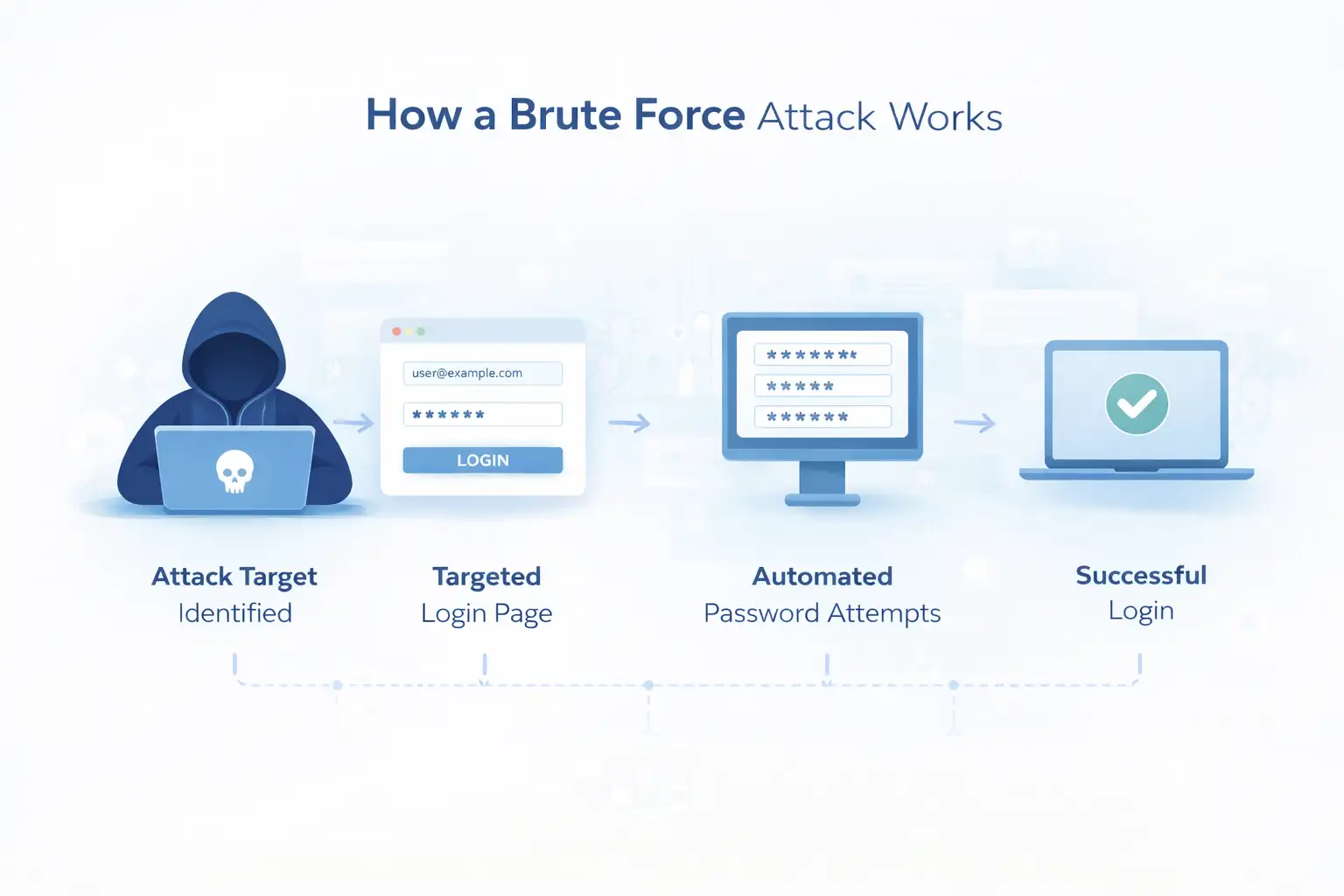
How a brute force attack works
In most cases, the attacker identifies a login surface, gathers likely usernames or emails, then uses automated attempts to test passwords until one succeeds or defenses block the activity.
Here is the process in plain language.
First, the attacker picks a target. That could be a customer login page, a WordPress admin URL, a VPN portal, a Microsoft 365 sign-in flow, an RDP service, or an SSH endpoint. Public-facing login interfaces are attractive because they are easy to find and easy to test at scale.
Next, the attacker decides what to guess. Sometimes it is a huge list of passwords. Sometimes it is a short list of very common passwords applied across many accounts. Sometimes it is a set of stolen username-password pairs from another breach.
This is where many readers confuse brute force with credential stuffing or password spraying. They are related, but not identical. OWASP and CISA both treat these as closely connected authentication attack patterns, with overlapping defenses.
After that comes automation. The software sends repeated authentication attempts and watches for success signals, lockout responses, MFA prompts, or other useful feedback. If the environment lacks throttling, smart lockout, CAPTCHA, anomaly detection, or MFA, the attacker has more room to keep trying. Microsoft’s smart lockout guidance exists for exactly this reason.
Finally, if an attempt works, the attacker moves from guessing to abusing access. That may mean data theft, mailbox access, privilege escalation, persistence, or lateral movement. And that is when a simple password attack turns into a broader incident.
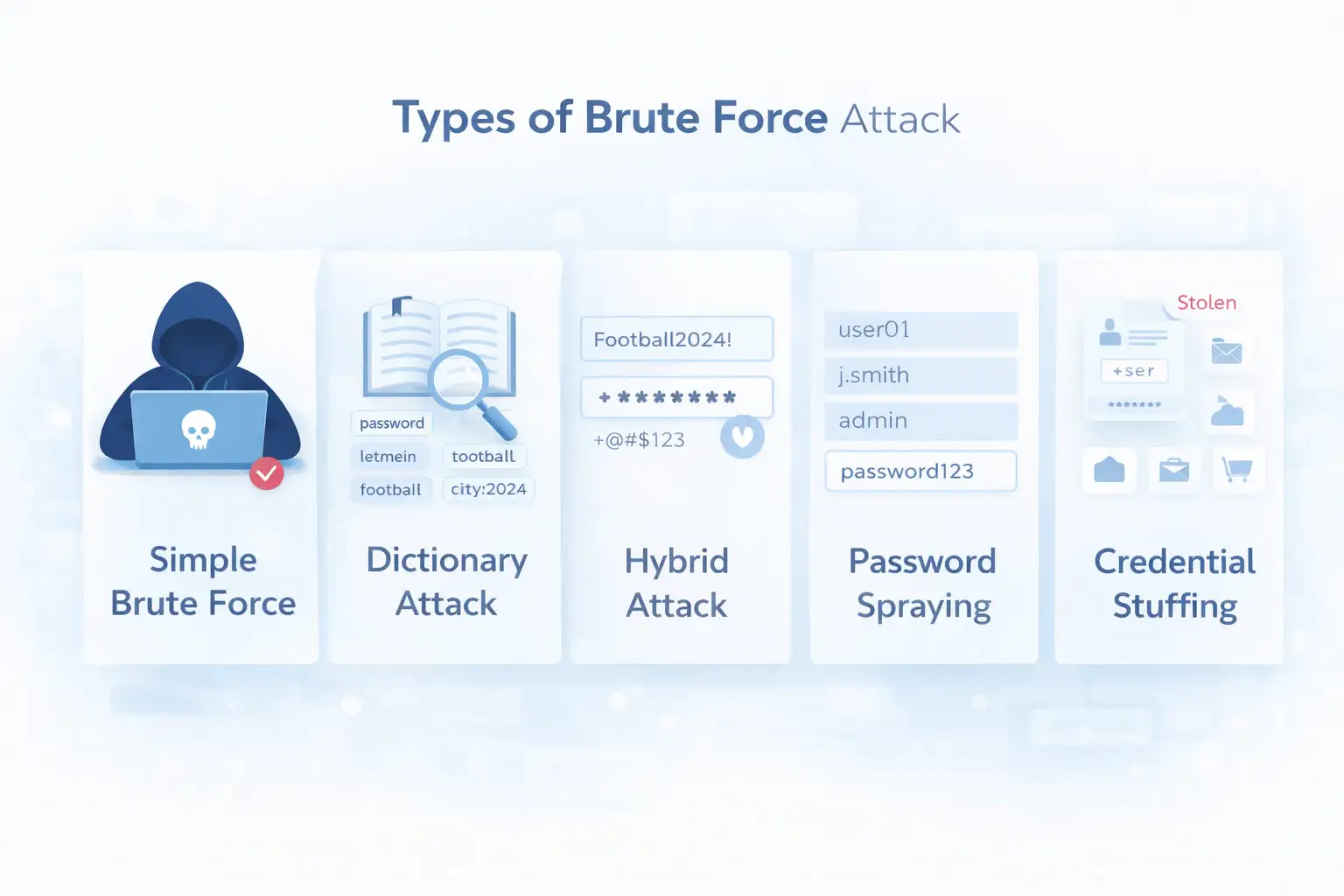
Main types of brute force attack
Simple brute force attack
A simple brute force attack tries many possible passwords against one account until a match is found. It depends heavily on weak or predictable passwords.
This is the classic model people picture first. One account. Many guesses. If the password is short, common, or built from obvious personal clues, the attacker has a better chance. NIST warns that short passwords are more vulnerable to brute-force and dictionary attacks, which is exactly why password length matters so much.
Dictionary attack
A dictionary attack is narrower. Instead of trying every possible combination, the attacker tries a curated list of likely passwords, words, phrases, and variations. Think seasonal passwords, sports names, city names, and predictable add-ons like “123” or “2024.”
It is faster than full combination guessing because it cuts out many impossible or unlikely tries. NIST explicitly references dictionary attacks alongside brute-force risk in password guidance.
Hybrid brute force attack
Hybrid attacks sit in the middle. The attacker starts with a realistic word or phrase, then appends years, symbols, or number patterns. This works against people who believe they have created a “strong enough” password just because they added one special character at the end. Human habits are surprisingly predictable.
Password spraying
Password spraying flips the pattern. Instead of many passwords against one account, the attacker uses one or a few common passwords against many accounts to avoid lockout on a single user. CISA describes password spraying as a technique that uses a small password list across many accounts specifically to reduce the chance of triggering account lockouts.
This matters in business environments because attackers often know or can guess usernames. If your naming format is predictable and your weak-password hygiene is inconsistent, password spraying becomes far more practical.
Credential stuffing
Credential stuffing is often mentioned beside brute force, but it is slightly different. The attacker is not guessing from scratch. They are testing stolen credentials from another breach or phishing event across other services.
OWASP calls credential stuffing a subset of the brute force category, while Cloudflare explains the difference by noting that credential stuffing uses exposed credentials from elsewhere rather than fresh guessing.
That distinction matters because the defense changes slightly. Strong passwords help, but unique passwords per service matter even more.
Brute force attack vs credential stuffing vs password spraying
If you are explaining what a brute force attack is to leadership, this comparison usually helps:
Brute force is broad credential guessing. Password spraying is low-and-slow guessing across many users with common passwords. Credential stuffing is the reuse of already stolen credentials. The overlap is operational, not semantic.
Defenders usually need a similar control stack for all three: MFA, rate limiting, bot detection, anomaly monitoring, account lockout logic, and better password policy. OWASP’s prevention guidance explicitly notes that protections for credential stuffing and password spraying also help with brute-force attacks.
Real-world impact on businesses and users
The real damage from a brute force attack is not the failed login noise. It is what happens after one login succeeds, such as account takeover, fraud, data theft, persistence, and reputational damage.
A single compromised mailbox can trigger invoice fraud, internal phishing, or sensitive data exposure. A compromised admin console can be worse. It may open the door to configuration changes, user impersonation, or service disruption. CISA has documented cases where brute force activity led to deeper network discovery and credential access.
Here is a simple before-and-after scenario. Before, a company allowed unlimited login retries on a legacy admin panel and relied only on passwords.
After, it adds smart lockout, phishing-resistant MFA where possible, and anomaly monitoring and removes dormant accounts. The visible result is not flashy.
Fewer risky sign-ins succeed. Fewer alerts become incidents. Less cleanup. More resilience. Microsoft and NIST guidance support those controls directly.
Cloudflare has also described large-scale credential abuse, with exposed credentials reaching more than 12,000 HTTP requests per minute in observed attacks. That does not mean every organization faces the same rate, but it is a useful reminder that modern credential attacks can be industrial in scale.
Signs you may be under a brute force attack
You usually do not get a dramatic warning. It is more like a pattern that starts to look wrong.
Repeated failed login attempts from the same IP range are one sign. So are bursts of sign-ins against many accounts, sudden authentication attempts from new geographies, or a spike in lockout events.
Fortinet guidance highlights repeated authentication failures and unusually high login frequency as practical detection clues. Microsoft and OWASP also emphasize monitoring and protective controls around authentication flows.
You may also notice unusual MFA activity, odd password reset requests, or support tickets from users who are locked out unexpectedly. None of these alone proves compromise. Still, together they often point to an authentication attack pattern worth investigating quickly.

How to prevent brute force attacks
The most effective defense is layered. Use a strong password policy, unique passwords, MFA, rate limiting, lockout controls, monitoring, and account hygiene together instead of relying on any single control.
A good first step is password quality. NIST guidance emphasizes length and blocklists over outdated complexity theater. The point is not to force users into weird password gymnastics. The point is to make guessing harder and reduce the use of known weak choices.
MFA is the next layer. NIST’s small business guidance says enabling MFA on all accounts that support it is essential for reducing cyber risk, while also noting that some MFA methods are stronger than others. In practice, phishing-resistant MFA is better where feasible, especially for high-value users and administrators.
Then comes login protection. Rate limiting, smart lockout, and anti-automation measures reduce the attacker’s ability to keep guessing. Microsoft’s smart lockout guidance is specifically designed to block brute-force password guessing while still allowing legitimate users to recover from occasional mistakes.
Operational hygiene matters too:
Remove dormant or unused accounts so they cannot become easy targets.
Monitor authentication logs in near real time.
Watch for password spraying patterns across many users.
Use bot management, CAPTCHA, or similar friction where appropriate.
Investigate impossible travel, unusual IPs, and repeated lockout events.
Enforce unique passwords and discourage reuse across services.
This is where a security partner can help without turning the article into a sales pitch. For example, Hoplon Infosec can fit naturally into this conversation as a provider that helps organizations assess exposed authentication surfaces, tighten identity controls, improve monitoring, and turn guidance into operating practice.
That is not a magic fix. It is just the difference between knowing the checklist and actually implementing it well.
Common mistakes that make brute force attacks easier
Some mistakes are obvious. Default credentials. Weak admin passwords. No MFA on privileged accounts. Others are more subtle.
An organization may have good password guidance on paper but no rate limiting on a legacy portal. Or it may have MFA for employees but not for contractors, vendors, or older admin interfaces. Sometimes the weak point is not a frontline employee at all.
It is a service account, a test tenant, or an account no one remembered to disable. CISA has warned that service accounts can be especially susceptible when they are hard to protect with MFA.
There is also a bad habit of treating authentication logs as background noise. That approach gets expensive later.
What users and businesses should do now
If you are an individual user, start with unique passwords, a password manager, and MFA. That alone closes off a lot of the easy wins attackers look for. NIST, Microsoft, and OWASP guidance consistently support these basics.
If you are a business, look at the whole authentication chain. Review where users sign in, how retries are handled, which accounts are exempt from modern controls, and whether logs are being reviewed with enough context.
Then test your environment the way an attacker would. You are not just asking, “Do we have a policy?” You are asking, “Can this control actually stop a real brute force pattern?”
A practical way to reduce brute force risk is to focus on three areas at once: identity hardening, login abuse visibility, and account lifecycle hygiene. In many organizations, one of these is decent, one is uneven, and one is quietly neglected.
A sensible recommendation set would be to review all public-facing login points, enforce MFA for high-risk users first, enable lockout or throttling where it is missing, remove unused accounts, and centralize authentication alerts.
That kind of work is where a provider like Hoplon Infosec can add value, especially when internal teams know the basics but need help turning them into repeatable controls.
FAQs
What is a brute force attack in simple words?
It is an attack where someone keeps trying passwords or login combinations until one works. The process is often automated, not manual.
Is credential stuffing the same as a brute force attack?
Not exactly. Credential stuffing uses stolen username-password pairs from other breaches, while brute force usually means guessing credentials directly. They are related and often share similar defenses.
Can MFA stop brute force attacks?
MFA can greatly reduce the chance that a guessed password leads to account takeover, though some MFA methods are stronger than others. Phishing-resistant MFA offers better protection where available.
What is password spraying?
Password spraying is when an attacker tries one or a few common passwords across many accounts to avoid lockouts on a single account.
Why are short passwords risky?
Because short passwords are easier to guess through brute-force and dictionary attacks. NIST specifically warns that passwords that are too short yield to these attacks more easily.
summary
If you came here asking what a brute force attack is, the essential answer is simple: it is a repeated credential-guessing attack that still causes real business harm when login protections are weak.
The main benefit of understanding it clearly is that you stop treating it like an old, low-priority threat and start addressing it as an active identity risk. The useful differentiator is not one fancy tool.
It is the layered approach: stronger passwords, MFA, lockout logic, monitoring, and account hygiene working together. That is also where a capable security partner such as Hoplon Infosec can help translate guidance into a system that holds up under real pressure.
For more latest updates like this, visit our homepage.
Suggested trusted references:
CISA advisory on brute force and credential access activity,
Was this article helpful?
React to this post and see the live totals.
Share this :