Windows 11 KB5083769 KB5082052 Update: Big Fixes Live
-20260414191440.webp&w=3840&q=75)
Hoplon InfoSec
15 Apr, 2026
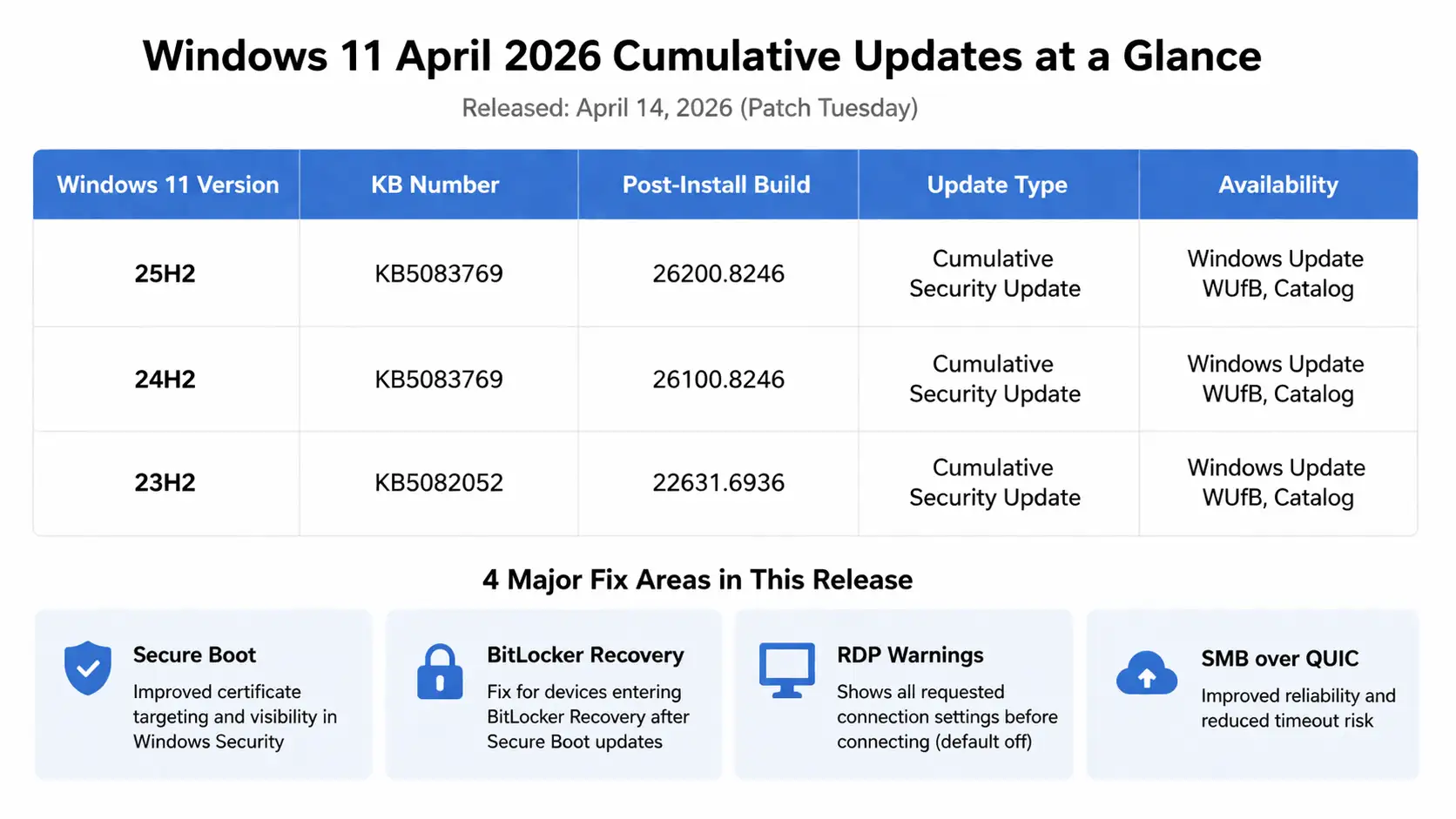
Microsoft released KB5083769 for Windows 11 25H2 and 24H2 and KB5082052 for Windows 11 23H2 on April 14, 2026.
These are cumulative April 2026 Patch Tuesday security updates; they are mandatory through normal update channels, and they also carry forward fixes from the prior month’s preview releases.
The most reliable source for the release details is Microsoft’s own support documentation.
We spent time reviewing the official release notes, the Microsoft Update Catalog entries, and the broader April 2026 patch context.
The short version is simple: this is a meaningful Windows 11 security rollout, not a cosmetic maintenance drop.
For home users, the updates matter because they carry the month’s security fixes and improve how Windows handles Secure Boot certificate rollout, Remote Desktop warnings, and stability in a few specific areas.
For businesses, there is more to watch, especially around Secure Boot readiness, BitLocker recovery behavior, and RDP-based phishing abuse.
Technical Overview
|
Item |
KB5083769 |
KB5082052 |
|
Release date |
April 14, 2026 |
April 14, 2026 |
|
Applies to |
Windows 11 25H2 and 24H2 |
Windows 11 23H2 |
|
New build |
26200.8246 and 26100.8246 |
22631.6936 |
|
Update type |
Cumulative security update |
Cumulative security update |
|
Distribution |
Windows Update, WUfB, Catalog |
Windows Update, WUfB, Catalog |
|
Known issues status |
Microsoft says none currently known |
Microsoft says none currently known |
|
Catalog availability |
Arm64 and x64 packages |
Arm64 and x64 packages |
All of those data points come directly from Microsoft’s update pages and catalog listings. Microsoft also pairs KB5083769 with servicing stack update KB5088467 for the 24H2 branch and KB5082052 with servicing stack update KB5086307 for 23H2.
What is new in KB5083769?
The KB5083769 update is the package for Windows 11 25H2 and 24H2. At a baseline level, it includes the latest security fixes plus the improvements that shipped earlier through the March 2026 preview and out-of-band releases.
That matters because some readers will notice features or behaviors that were first documented in late March and assume they are seeing something brand new. In reality, cumulative updates roll that work forward.
The most important change is around Secure Boot. Microsoft says Windows quality updates now include additional high-confidence device targeting data so more eligible devices can automatically receive new Secure Boot certificates in a controlled rollout.
Windows Security may also show the status of Secure Boot certificate updates on the device. There is also a fix for a case where the device could enter BitLocker recovery after secure boot updates.
That is a serious detail for IT teams because boot trust, recovery workflows, and certificate rollover are not the kind of things you want to discover during a rushed maintenance window.
There are two more changes worth calling out.
First, Microsoft improved reliability when Windows uses SMB compression over QUIC, reducing timeout risk.
Second, Remote Desktop now shows all requested connection settings before it connects when an . The RDP file is opened, and those settings are turned off by default. A one-time security warning also appears the first time the file is opened on a device.
That is quietly one of the smartest changes in this month’s release because weaponized or misleading RDP files are still a real social engineering path.
KB5083769 also fixes a "Reset this PC" issue tied to earlier March hotpatch conditions, where reset could fail even when choosing “Keep my files” or “Remove everything.”
That is not flashy, but it matters. When reset breaks, support teams lose one of the simplest recovery paths available to standard users.
What is new in KB5082052?
The KB5082052 update is the Windows 11 23H2 package. Its build number is 22631.6936, and its changelog closely tracks the same core themes as KB5083769.
That includes Secure Boot certificate visibility, improved device targeting for new certificates, a fix for BitLocker recovery after Secure Boot updates, better SMB over QUIC consistency, and stronger protection when opening Remote Desktop files.
There is one extra item here that deserves attention because it affects ordinary sign-in behavior.
Microsoft says KB5082052 fixes a problem where some users, after installing Windows updates released on or after March 10, 2026, could hit a “no Internet” error while signing in to apps with a Microsoft account even when the device actually had working connectivity.
That could block access to Microsoft services and apps, including Teams. If you saw odd sign-in behavior recently on 23H2, this is probably the line that matters most to you.
So, what is new in KB5082052 in practical terms? Better trust and boot preparation, better RDP hygiene, better network behavior in specific enterprise scenarios, and a meaningful fix for Microsoft account sign-in friction.
That is a stronger package than the usual one-line “security fixes and improvements” summary suggests.
Why This Matters
Every Patch Tuesday matters. Not every Patch Tuesday arrives with the same weight.
April 2026 was a heavy Microsoft security month. Zero Day Initiative counted 163 new Microsoft CVEs in the broader release cycle and called it one of the company’s largest monthly releases.
That number does not mean every one of those flaws lands directly in these two Windows 11 cumulative packages, but it does tell you the security backdrop is unusually busy.
When the monthly patch set is this large, deferring updates for too long becomes a bigger risk decision than usual.
For businesses, the Secure Boot messaging is the real headline. Microsoft says certificates used by most Windows devices begin expiring starting in June 2026, and it is urging customers to prepare in advance.
That puts these updates in a larger readiness story. If your estate includes managed laptops, mixed hardware generations, devices protected by BitLocker, or strict boot policies, you should not treat this as “just another cumulative.” You should treat it as part security patch and part boot trust preparation.
For regular users, the danger is simpler. Unpatched systems sit further behind, and many users will not know whether a weird sign-in problem, a suspicious RDP attachment, or an odd recovery prompt is tied to something Microsoft already addressed. That uncertainty creates the kind of chaos attackers love.
Our Technical Analysis
From a defensive standpoint, the smartest change in this cycle may be the stricter Remote Desktop behavior.
Why? Because .rdp files rarely get the same suspicion that people apply to obvious executable attachments. An email attachment that says “quarterly remote access profile” can still get opened in some environments.
Microsoft’s move to show requested settings first and keep them off by default reduces blind trust at the point of execution. That is a security UX improvement, and those often age better than headline features.
The Secure Boot work also deserves a more careful read than most coverage gives it. Certificate expiration projects sound boring until a device refuses to boot properly or lands in recovery.
Microsoft is trying to widen automatic certificate delivery while keeping the rollout controlled. That balancing act tells you the company knows the blast radius is real if anything goes sideways.
A security update that touches boot trust is always worth testing on representative hardware before broad enterprise deployment.
There is also a trust signal in what Microsoft says is not happening. As of the current support pages, Microsoft is not aware of any known issues with either update.
That does not guarantee flawless rollout in every environment, but it is still a useful starting point, especially after March included a preview update that had to be replaced due to an installation issue.
When we ran through the release notes and compared them with the rougher March cadence, one thing stood out right away: Microsoft is trying to remove ambiguity around risky actions.
We saw it in the RDP prompts. We saw it in the Secure Boot certificate status visibility. Those are not cosmetic choices.
They are the kind of controls that help users pause before a bad click or before a surprise recovery event.
In our practical review, the most useful admin clue was not a flashy feature bullet. It was the servicing stack pairing and the catalog availability.
That usually tells you Microsoft expects real-world deployment through more than one channel and wants update installation reliability to stay solid.
If you manage Windows at scale, you know how often “the patch exists” and “the patch installs cleanly everywhere” become two very different conversations.
We also noticed that many fast news summaries treated KB5083769 and KB5082052 almost like duplicates.
They are closely aligned, yes, but the 23H2 sign-in fix is a good example of why version-specific reading still matters.
A lot of patch confusion starts when people skim one article and assume every branch got every exact fix.
How to Protect Your System
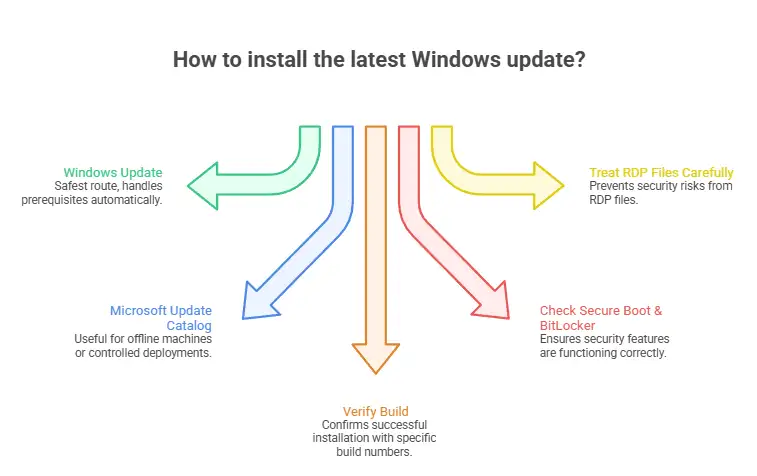
1. Check which Windows 11 version you are running.
Open Settings > System > About and confirm whether the machine is on 23H2, 24H2, or 25H2. That determines whether you should expect KB5082052 or KB5083769.
Microsoft’s update history pages for 23H2 and 24H2 are still the cleanest way to confirm the branch logic if you are unsure.
2. Install through Windows Update first
Go to Settings > Windows Update and check for updates. Microsoft says both updates are available through Windows Update and Microsoft Update, and they install automatically under normal policy conditions. For most users, this is the safest route because prerequisites and servicing components are handled for you.
3. Use the catalog only when you actually need it.
If you are patching offline machines, testing one architecture separately, or maintaining controlled deployment rings, use the Microsoft Update Catalog.
Microsoft documents ARM64 and x64 packages for KB5082052, and the same channel is provided for KB5083769. Catalog installs are useful, but they are not the first choice for average users.
4. Verify the build after rebooting
After installation, run winver or return to Settings > System > About. You should see:
26200.8246 for Windows 11 25H2
26100.8246 for Windows 11 24H2
22631.6936 for Windows 11 23H2
5. Watch secure boot and BitLocker behavior.
If you manage protected devices, check for Secure Boot certificate status inside Windows Security after the update.
Also confirm there are no unexpected BitLocker Recovery prompts on rebooted endpoints, especially on test hardware with different OEM firmware baselines.
Microsoft specifically mentions a fix in this area, which tells you the risk was real enough to document.
6. Treat RDP files as high-risk content.
Even with the new warning flow, do not normalize opening. RDP files from email or chat without validation.
This month’s protection improvement helps, but it does not replace good judgment, mailbox filtering, attachment scanning, and least privilege.
Common Mistake
A common mistake is assuming a cumulative update is “small” because the visible changelog is short. That is not how Windows monthly rollups work.
These packages pull in prior security content and earlier non-security improvements from preview releases. A short summary can still represent a large effective change set.
Another mistake is mixing version branches. Readers searching for the Windows 11 24H2 update, Windows 11 25H2 update, and Windows 11 23H2 update often land on the same article.
If the page does not separate the KB numbers clearly, they may try to verify the wrong build number and assume the install failed.
This is one reason the KB5083769 build number and KB5082052 build number need to be shown plainly.
The third mistake is jumping straight to manual repair when an update appears stuck.
Microsoft’s troubleshooting guidance still starts with the basics: make sure Windows Update services are functioning, free up space if necessary, and use the official troubleshooter path before escalating to heavier repairs.
If installation fails
For a KB5083769 install failed fix or KB5082052 not installing case, start with this order:
Reboot and retry.
Check free disk space.
Run the Windows Update troubleshooter.
Open an elevated command Prompt and run:
sfc /scannowThen run:
DISM /Online /Cleanup-Image /RestoreHealthRetry Windows Update.
If needed, move to the Microsoft Update Catalog package that matches your device architecture.
If a business device enters BitLocker recovery after patching, stop and verify whether secure boot-related protections or firmware state changed.
Do not guess. That is a case for measured triage, not button mashing.
FAQ
Is KB5083769 safe to install?
Microsoft currently says it is not aware of any known issues with KB5083769, and it is part of the mandatory April 2026 Patch Tuesday security cycle.
That makes it a normal recommended install for most users, with staged validation still wise for business fleets.
Is KB5082052 a mandatory update?
Yes. It is a cumulative security update delivered as part of the April 14, 2026, Patch Tuesday release for Windows 11 23H2.
Where can I get the KB5083769 download or the KB5082052 direct download?
The preferred route is Windows Update. Manual packages are available through the Microsoft Update Catalog for supported architectures.
Should you install KB5083769 or should you install KB5082052 right away?
For most home users, yes. For businesses, deploy quickly but use ring-based validation on representative hardware, especially if Secure Boot, BitLocker, or managed RDP workflows are sensitive in your environment.
Hoplon Insight Box
Recommendation 1: Patch first through Windows Update unless you have a real operational reason to use the catalog.
Recommendation 2: Validate post-install build numbers instead of trusting “Update completed successfully.”
Recommendation 3: Put extra attention on Secure Boot and BitLocker behavior during this cycle.
Recommendation 4: Use this month’s new RDP warning behavior as a reason to refresh user awareness around remote access attachments.
source
Microsoft Support and the Microsoft Security Update Guide remain the authoritative sources for release status, build mapping, and deployment channels. The Zero Day Initiative review adds useful context on the size of the overall April 2026 patch load.
Security Checklist
1. Confirm your branch and build.
23H2 should land on 22631.6936.
24H2 should land on 26100.8246.
25H2 should land on 26200.8246.
2. Check Windows Security after patching.
Look for the Secure Boot certificate status and watch for any BitLocker recovery surprises on reboot.
3. Review how your users open RDP files.
This month’s patch improves warnings, but policy, training, and attachment controls still matter.
Author: Editorial Security Desk
Publish date: April 15, 2026
Last updated: April 15, 2026
Was this article helpful?
React to this post and see the live totals.
Share this :