Adobe Reader Zero-Day Patched After Months of Exploits
-20260412153323.webp&w=3840&q=75)
Hoplon InfoSec
12 Apr, 2026
Has the Adobe Reader zero-day finally been patched, and why does it matter right now?
Yes. Adobe released an emergency security update on April 11, 2026, for Acrobat and Reader after confirming that CVE-2026-34621 was being exploited in the wild. The flaw affects Windows and macOS versions of Acrobat and Reader, and successful exploitation can lead to arbitrary code execution.
That matters because PDF files still move through inboxes, legal teams, finance departments, HR workflows, and government systems every single day. A booby-trapped PDF is still one of the easiest ways to reach real people inside real organizations.
There is a reason this story landed hard across the security world. Most people still think of PDF files as boring. Safe, even. They feel like digital paper. But this case is a reminder that documents can act like delivery vehicles, especially when attackers understand how trusted software behaves in enterprise environments.
In this incident, Adobe acknowledged active exploitation, and multiple researchers linked the campaign to malicious PDFs seen in the wild for months before the patch arrived.
That time gap is the part many quick news posts rush past. A patch is one story. A vulnerability quietly exploited across months is a very different story.
It suggests the attackers were patient, selective, and likely looking for meaningful targets rather than random clicks. That is what makes this incident important beyond the headline.
What happened?
Adobe pushed APSB26-43 for Acrobat and Reader after confirming that CVE-2026-34621 had been exploited in the wild. The official bulletin says the flaw is critical and can lead to arbitrary code execution.
It affects Acrobat DC, Acrobat Reader DC, and Acrobat 2024 on both Windows and macOS. Adobe also gave the update a Priority 1 rating, which tells you this is not a routine cleanup job. It is an urgent fix.
Public reporting adds the missing timeline. Researchers had already been discussing a live Adobe Reader zero-day exploit several days before Adobe’s bulletin went live.
Those reports described malicious PDF documents that triggered obfuscated JavaScript when opened and used privileged Acrobat APIs in ways that were never meant for hostile input.
In other words, this was not a harmless parsing bug. It was the kind of issue that turns trusted software into an attack surface.
Some early reports and later advisories also shifted on severity details. Adobe’s bulletin revision on April 12 changed the attack vector from network to local, which lowered the CVSS score from 9.6 to 8.6. That revision matters for accuracy, but it does not change the core takeaway.
The company still says the flaw was actively exploited, and a successful attack could still end in code execution.
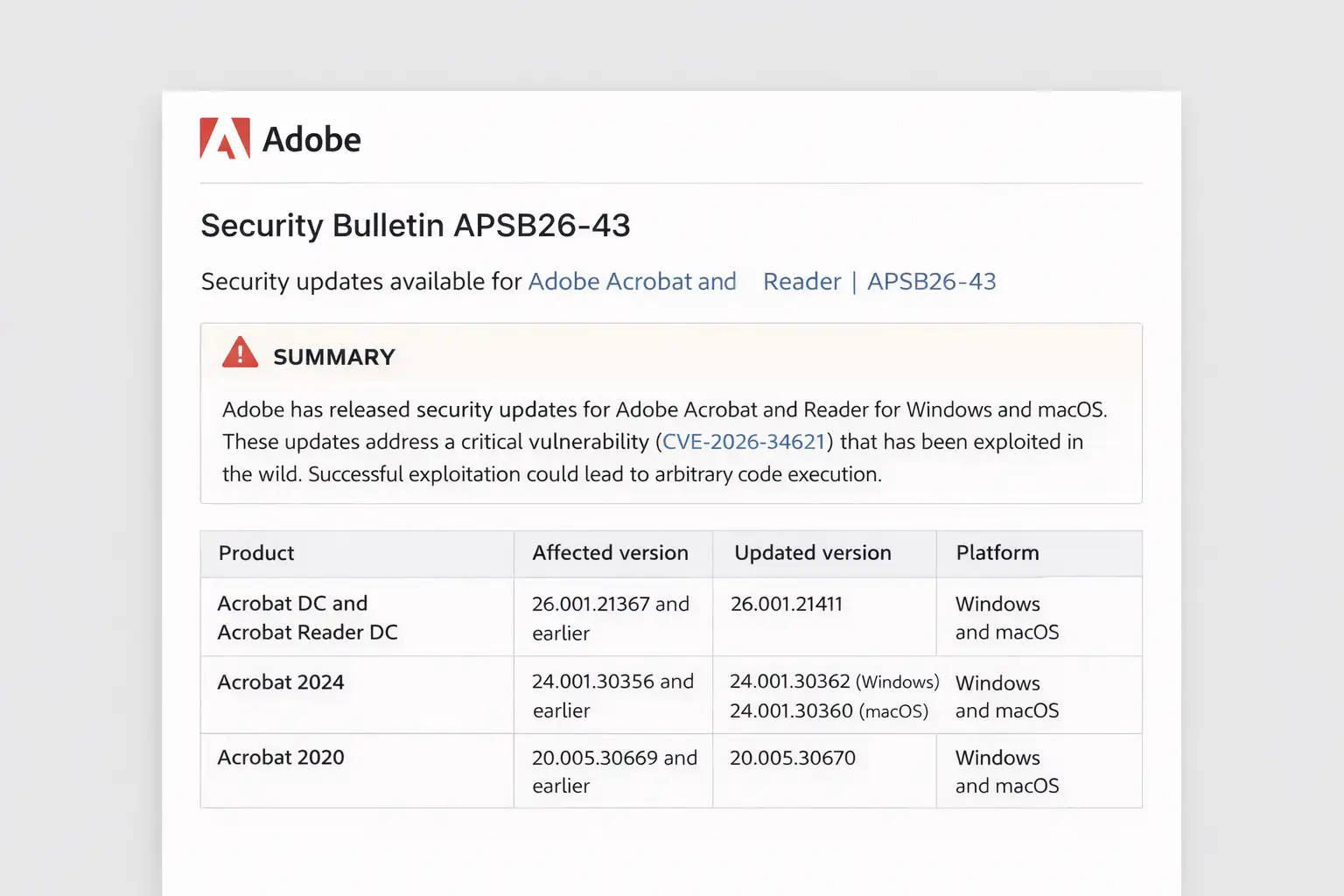 Adobe security bulletin details update impact
Adobe security bulletin details update impactWhy this bug is a bigger deal than a normal PDF flaw
A lot of vulnerability news sounds dramatic on the day it breaks and then fades out. This one deserves more attention because it hits a product category that sits in the middle of everyday business.
People open invoices, legal drafts, vendor documents, contracts, product specs, and scanned forms without a second thought. That habit is exactly why a strong Adobe Acrobat Reader zero-day has real-world weight.
The second reason is timing. Independent reporting tied exploitation to at least December 2025, and one report said evidence from a sample uploaded to VirusTotal suggested activity may date back to November 2025.
That is not a smash-and-grab campaign. It points to a quiet, sustained window where attackers had an edge over defenders.
And then there is the delivery method. An Adobe Reader malicious PDF is effective because it hides in plain sight. It does not need to look suspicious.
A PDF can wear the mask of a market report, a tax form, a vendor statement, or an urgent memo. In busy companies, people open files first and ask questions later. That human behavior is often the softest spot in the whole chain.
The vulnerability itself
Adobe describes CVE-2026-34621 as an “Improperly Controlled Modification of Object Prototype Attributes,” which is a prototype pollution issue under CWE-1321. That sounds abstract if you do not live in vulnerability databases.
The practical meaning is simpler. An attacker can manipulate how certain objects behave inside the application, then steer the software into actions it should not perform. In this case, Adobe says the end result can be arbitrary code execution.
This is why the phrase "Adobe Reader arbitrary code execution" matters. Data theft is bad. Fingerprinting a system is bad. But code execution means the attacker may be able to run malicious instructions on the victim machine.
That opens the door to follow-on activity such as credential theft, system reconnaissance, persistence, or another stage that escapes application boundaries.
Public researcher analysis before the patch also warned that later stages could include remote code execution and even sandbox escape.
The technical reporting around the case repeatedly referenced Adobe Reader prototype pollution, which is not a term average readers search every day, but it is an important bridge keyword for serious search intent.
It helps connect this incident to the broader class of JavaScript-related abuse in document viewers and web-style runtimes.
How the attack likely worked
Based on public research and media analysis, the attack chain began with a specially crafted PDF file. When opened in Reader, it executed obfuscated JavaScript and invoked privileged Acrobat APIs.
Researchers said the sample appeared designed to gather user and system information first, which suggests careful target selection instead of broad opportunistic spam.
That detail matters because it changes how defenders should think about the campaign. Not every exploit drops ransomware in the first minute. Some attacks start by measuring the room.
What machine is this? Which user opened the file? What language settings are present? Is this system valuable enough to continue? It is a bit like a burglar pressing against a door before deciding whether to force it open.
Public analysis also noted Russian-language lures tied to current events in the Russian oil and gas sector. That has led several researchers to suggest the campaign may have been targeted rather than random.
Attribution remains uncertain in public reporting, and that uncertainty should stay on the table. Still, the lure quality and timing suggest a focused operation, not a spray-and-pray attachment blast.
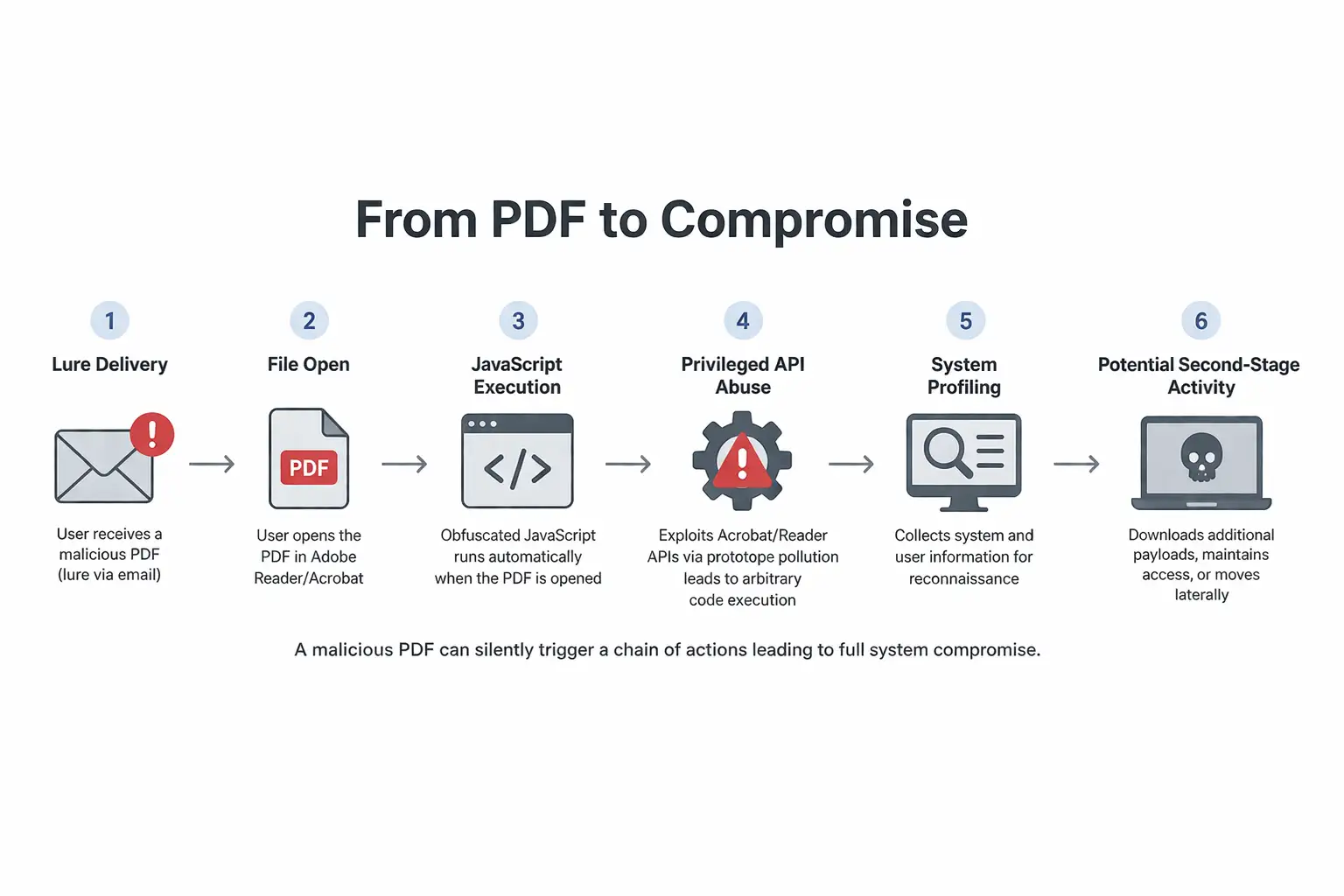 From PDF to compromise diagram
From PDF to compromise diagramWho is affected?
The official Adobe bulletin lists three affected tracks. Acrobat DC and Acrobat Reader DC versions 26.001.21367 and earlier are affected on Windows and macOS. Acrobat 2024 version 24.001.30356 and earlier are also affected on both platforms.
The fixed versions are 26.001.21411 for Acrobat DC and Reader DC, 24.001.30362 for Acrobat 2024 on Windows, and 24.001.30360 for Acrobat 2024 on macOS.
That means the risk is not limited to one niche deployment model. Adobe Reader vulnerability coverage here extends across consumer endpoints, managed enterprise fleets, creative teams, legal departments, procurement desks, and government contractors who still depend on Acrobat workflows. Anyone opening externally sourced PDFs should treat this as relevant.
It also means Adobe Reader patch coverage has to be more than a quick reminder at the desktop level. In larger environments, patching Reader is often not just a user action. It is a software management task.
If IT admins assume auto-update has already handled everything, they may miss unmanaged devices, offline systems, VDI images, kiosk machines, or macOS endpoints sitting outside the usual tooling.
Timeline at a glance
Here is the simplest way to understand the sequence:
Late November 2025 to December 2025: Public reporting suggests the exploitation window began around this period, with some analysis pointing to sample evidence dating back to November 2025.
April 7 to April 9, 2026: Researchers publicly described the live zero-day activity and linked it to malicious PDFs, targeted lures, and information-harvesting behavior.
April 11, 2026: Adobe published APSB26-43 and released fixes for Acrobat and Reader.
April 12, 2026: Adobe revised the bulletin, adjusting the CVSS vector and score from 9.6 to 8.6.
That sequence supports another long-tail query people are already searching for: "Adobe Reader exploit since December 2025." It is awkward as a phrase, but it maps cleanly to real search behavior around this case.
A quick comparison table
|
Item |
Details |
|
Vulnerability |
CVE-2026-34621 |
|
Product impact |
Acrobat DC, Reader DC, Acrobat 2024 |
|
Platforms |
Windows, macOS |
|
Exploit method |
Malicious PDF with obfuscated JavaScript |
|
Vulnerability type |
Prototype pollution |
|
Outcome |
Adobe Reader arbitrary code execution |
|
Public exploitation |
Confirmed by Adobe |
|
Patch bulletin |
APSB26-43 |
|
Fixed DC version |
26.001.21411 |
|
Fixed Acrobat 2024 version |
Windows 24.001.30362, macOS 24.001.30360 |
What users and organizations should do now
First, update immediately. Adobe says users can update manually through Help > Check for Updates, and managed environments should deploy through their normal administrative methods. That is the nonnegotiable first step.
Second, treat recent inbound PDFs with more caution than usual, especially those tied to unexpected business events, urgent policy notices, vendor disputes, invoices, or sector-specific news. That does not mean every PDF is hostile. It means this is a moment to respect the attack path that is actually being used.
Third, security teams should review email and web controls for PDF detonation, sandboxing, and attachment analysis.
Sophos CTU also recommended automatically scanning PDF email attachments, blocking suspicious files, warning users about unsolicited documents, and even temporarily avoiding Adobe Reader for opening PDFs while waiting for an official patch.
That advice came before the patch landed, but the operational logic still holds for environments catching up on updates.
Fourth, hunt for signals of prior exposure. Public reporting mentioned indicators of compromise and noted that the exploit appeared to collect local system and user data.
If a user opened suspicious PDFs over the last several months, defenders should review endpoint logs, browser launches from document handlers, suspicious outbound traffic, and follow-on process behavior.
Business impact beyond the headline
For executives, this incident is a reminder that “widely used” and “low drama” software can still create outsized risk. Acrobat and Reader are not fringe tools. They are infrastructure.
When a flaw in that layer is exploited over months, the concern is not only one compromised workstation. It is the possibility of quiet intelligence gathering inside high-value teams.
For regulated sectors, the risk expands further. A compromised PDF workflow can touch confidential filings, contracts, partner data, and personal information.
That raises questions around legal exposure, incident response cost, and trust. Even when exploitation is selective, the cost of checking every suspicious interaction can be high.
There is also a reputational angle. If your organization knew there was an Adobe patch exploited vulnerability case underway and still delayed patching document viewers for days or weeks, that is a hard conversation after the fact.
Document software rarely gets a seat at the glamour table in security planning. Cases like this are exactly why it should.
Hoplon Insight Box
What this incident really tells us
Trusted file formats remain one of the best social engineering vehicles.
Patch urgency is not only about browsers, email clients, and VPNs.
Quiet exploitation windows are often more dangerous than flashy mass campaigns.
PDF handling deserves the same security attention as macros once did.
If your team opens high volumes of external documents, document isolation is worth revisiting.
Research note
One useful line from Sophos CTU captures the mood around this issue: organizations should be “wary of unsolicited attachments” while controlling risky PDFs in the environment. Even after a patch ships, that is still good advice.
Final takeaway
The story here is not just that Adobe fixed a bug. It is that a serious Adobe Reader zero-day appears to have lived in the wild for months while attackers used malicious PDFs as a quiet entry point.
That should reset how people think about document risk. PDFs are not passive objects. In the wrong hands, they can become a very believable first move.
If you run Acrobat or Reader on Windows or macOS, patch it now. If you manage endpoints, verify the version instead of assuming the job is done.
And if your organization handles a steady stream of external documents, treat this incident as a good moment to tighten the entire document intake chain, not just one application update. The patch closes the vulnerability. The lesson is bigger than the patch.
Frequently Asked Questions
Was this article helpful?
React to this post and see the live totals.
Share this :