CIA Triad in Cybersecurity: 3 Security Pillars You Must Know
Hoplon InfoSec
18 Apr, 2026
What is the CIA triad in cybersecurity, and why does it matter in 2026?
It is the core model security teams use to protect information by keeping it private, accurate, and available when needed.
CISA defines cybersecurity as protecting networks, devices, and data from unauthorized access or criminal use while ensuring confidentiality, integrity, and availability, and NIST uses the same three outcomes as the foundation of information security.
That sounds simple. The hard part is operational reality. A data leak is a confidentiality failure. A silent database change is an integrity failure.
A ransomware lockout or outage is an availability failure. If you understand those three failures, you understand what cybersecurity and the CIA triad are at the level that actually helps you defend a system.
Technical reference
|
Item |
Detail |
|
Model |
CIA Triad in Cybersecurity |
|
Stands for |
Confidentiality, Integrity, Availability |
|
Official basis |
CISA and NIST definitions of cybersecurity and information security |
|
Applies to |
Data, systems, networks, applications, cloud services, users, and business processes |
|
Threat categories |
Unauthorized access, tampering, disruption, destruction |
|
Typical controls |
Encryption, MFA, access control, hashing, audit logs, backups, failover |
|
CVE or campaign |
None by default. The CIA triad is a security model, not a single vulnerability or malware family |
|
Why it matters |
It helps teams judge whether controls protect privacy, trust, and uptime together |
What is cybersecurity?
The cleanest working definition comes from CISA: it is the protection of networks, devices, and data from unauthorized access or criminal use, plus the practice of ensuring confidentiality, integrity, and availability of information.
That line is useful because it ties the broad field of cybersecurity directly to the triad instead of treating them as separate ideas.
In practice, cybersecurity is not just blocking hackers. It is also controlling who can see a file, proving that a record was not altered, and making sure the service still works during an attack or hardware failure.
That is why cybersecurity principles become real only when they are tied to business risk. A hospital needs records to be accurate. A bank needs transactions to stay private. An online store needs checkout to stay up.
Attackers do not always steal data first. Sometimes they tamper with it. Sometimes they just shut systems down. That is why a narrow view of cyber defense misses the point. The bigger question is this: what failed, and what did that failure cost? The triad gives a clean answer.
Main goals
The main goals of cybersecurity are straightforward:
Protect data
Stop unauthorized access
Reduce attack impact
Keep systems running
Those goals line up directly with confidentiality, integrity, and availability. That is not a coincidence. It is the design logic behind modern security programs.
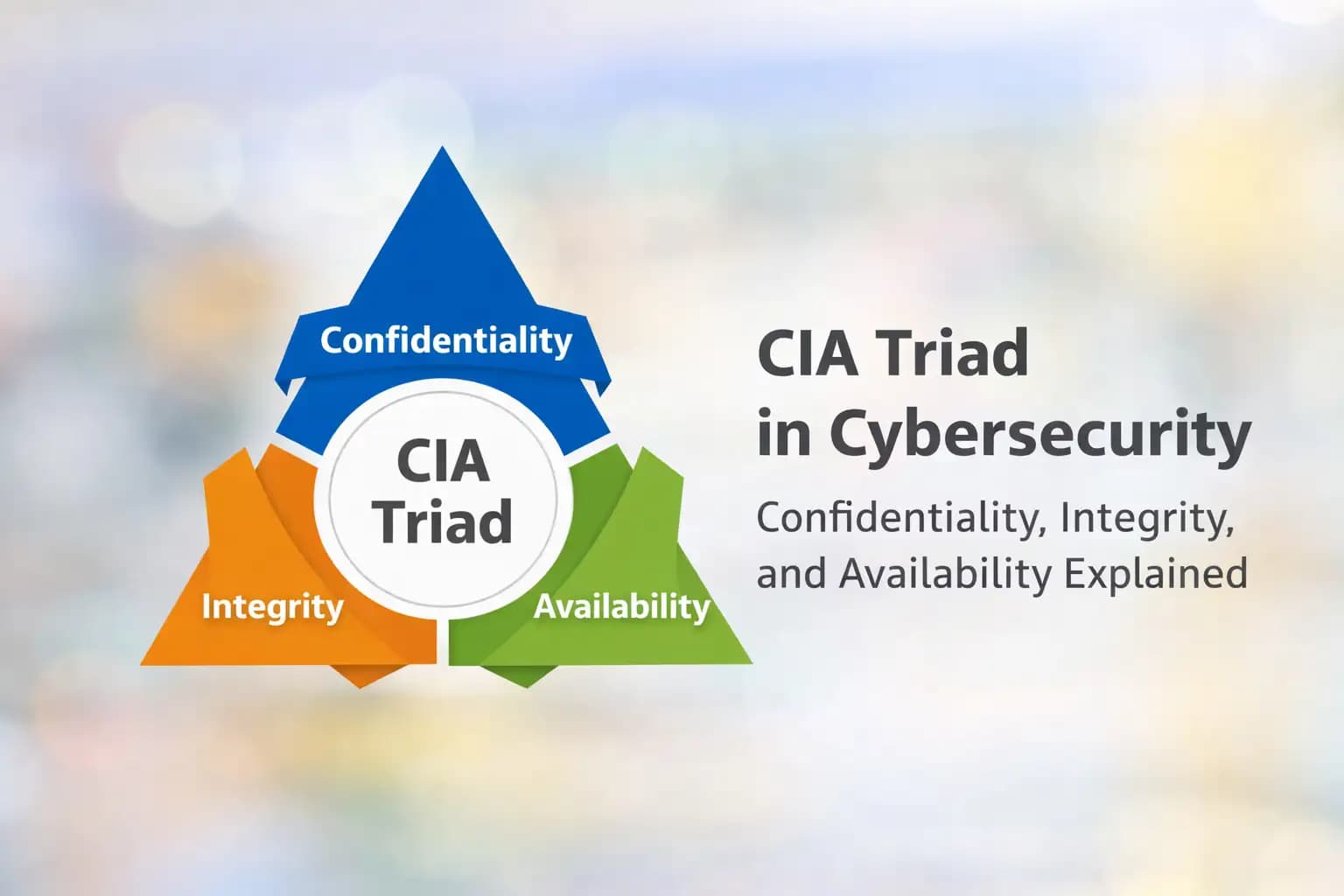
What is the CIA triad in cybersecurity?
The CIA Triad in Cybersecurity is a three-part model used to evaluate whether information and systems are protected well enough to support real operations.
Fortinet describes it as a common model that forms the basis for security-system development, while NIST describes the same three outcomes as the pillars of information security.
So, what is the CIA triad in practical terms? It is a way to ask three hard questions about any system:
Can the wrong person access this data?
Can someone change it without detection?
Can authorized users still get it when they need it?
If the answer to any one of those questions is shaky, the system is weaker than it looks.
The CIA triad in information security is foundational because it cuts through product marketing and gets back to outcomes. A shiny tool may generate alerts, but if it does not protect privacy, preserve trust in data, or keep services available, it is not solving the right problem.
CIA triad vs. cybersecurity
This confuses a lot of readers. Cybersecurity is the broad discipline. The CIA triad is one of its core models. One is the field. The other is the measuring stick. When people search "CIA triad vs. cybersecurity," that is the answer they usually need.

The 3 pillars
Confidentiality
Confidentiality in cybersecurity means information is disclosed only to authorized people, systems, or processes. NIST defines confidentiality as preserving authorized restrictions on access and disclosure, including protections for privacy and proprietary information.
The goal is simple. Keep secrets from the wrong eyes. That includes personal data, payroll files, API keys, merger documents, patient records, and session tokens.
Common threats include phishing, stolen credentials, excessive permissions, exposed cloud storage, and insider misuse.
Common controls include encryption, MFA, role-based access control, and least privilege. A real-world example is a payroll file shared to an open folder. Nothing was deleted. Nothing crashed. But confidentiality failed the moment unauthorized users could read it.
Integrity
Integrity in cybersecurity means data remains accurate, complete, authentic, and protected from improper modification or destruction.
NIST defines integrity as guarding against improper information modification or destruction and ensuring non-repudiation and authenticity.
This pillar gets less attention than confidentiality, but it can be more dangerous. A stolen file is obvious. A silently altered number in a financial report can sit there for weeks. Same with changed medication records, tampered log files, or modified software packages.
Common threats include malware, unauthorized database edits, supply-chain tampering, bad scripts, and human error.
Common controls include hashing, digital signatures, change approval, version control, and audit logs. Think about a hospital chart where a dosage entry is altered. The system is still online. Access controls may still work. Yet the trustworthiness of the data is broken.
Availability
Availability in cybersecurity means systems and information stay accessible and usable on time by authorized users. NIST frames availability as timely and reliable access to and use of information.
Availability is often reduced to uptime. That is too narrow. A service can technically be up and still be functionally unavailable because authentication is failing, storage is corrupted, or response time is unusable.
Common threats include ransomware, DDoS attacks, hardware failure, expired certificates, bad patches, and single points of failure.
Common controls include backups, redundancy, failover, patching, monitoring, and DDoS protection. When checkout fails during peak traffic, availability has failed even if the server never fully went dark.
|
Principle |
Meaning |
Goal |
Threats |
Controls |
Example |
|
Confidentiality |
Prevent unauthorized disclosure |
Keep data private |
Phishing, weak passwords, misconfigurations |
Encryption, MFA, least privilege |
Exposed HR records |
|
Integrity |
Prevent unauthorized change |
Keep data accurate and trustworthy |
Malware, tampering, bad scripts |
Hashing, digital signatures, audit logs |
Altered transaction record |
|
Availability |
Prevent disruption of access |
Keep systems usable on time |
Ransomware, DDoS, outages |
Backups, failover, redundancy |
Store checkout outage |
Real-world examples
Online banking
A banking app needs all three pillars at once. Account details and balances must stay private. Transaction records must stay accurate. The service must remain reachable during business hours and peak usage.
Break one pillar and the impact changes. Expose credentials, and confidentiality fails. Alter transaction records, and integrity fails. Knock the app offline during payroll day, and availability fails. This is why CIA triad examples work best when tied to the business function, not abstract definitions.
Hospital data system
Hospitals are a perfect test of confidentiality, integrity, and availability examples. Patient data must be restricted. Lab values must be accurate. Records must be available during treatment, not after an outage report is written.
Ask yourself this: which failure would be worst in an emergency room? A stolen record is serious. A changed allergy entry may be worse.
A total outage during triage can be catastrophic. The triad helps teams rank risk in a way generic security talk often does not.
E-commerce website
For an e-commerce company, confidentiality covers payment details and customer accounts. Integrity covers pricing, order data, and inventory counts. Availability covers search, checkout, and order confirmation flows.
This is where CIA triad real-world examples become useful for business owners. A 30-minute outage can cost more revenue than a minor internal policy mistake. At the same time, a silent price manipulation attack can damage trust faster than downtime.
Cloud storage
Cloud platforms create a false sense of safety. People assume availability is handled by the provider and stop there. But how the CIA triad protects data in cloud systems still depends on customer-side identity controls, logging, backup design, and segmentation.
A bucket with public access settings is a confidentiality problem. A deleted or altered object without versioning is an integrity problem. A region outage without recovery planning is an availability problem.
Common threats
Phishing and stolen passwords mainly attack confidentiality first, but they often become integrity and availability incidents later. Malware and ransomware can hit all three pillars in one move.
Insider threats blur the line between negligence and abuse. DDoS attacks hit availability directly. Misconfigurations and human error can break any pillar, often without an attacker needing sophisticated tools.
That overlap matters. Real incidents rarely stay inside one bucket. A compromised admin account can expose files, alter settings, and disable recovery paths in the same session.
Security controls that protect each pillar
Controls for confidentiality
Start with encryption for data at rest and in transit. Add MFA to reduce damage from stolen passwords. Enforce strong access control. Use least privilege. Review shared folders, cloud roles, and service accounts more often than you think you need to.
One common pitfall is assuming privacy equals security. It does not. A file can be hidden from most users and still be overexposed to admins, contractors, or old API tokens.
Controls for integrity
Use hashing to detect changes. Use digital signatures where authenticity matters. Track changes through version control. Keep audit logs protected from tampering.
Teams often forget that logging itself needs integrity protection. If an attacker can alter the logs, your visibility becomes fiction. That is one reason integrity is so central to incident response and forensic confidence.
Controls for availability
Backups matter only if you can restore them. Redundancy matters only if failover actually works. Patching matters because many outages begin as preventable compromises. DDoS protection matters because public-facing systems are judged by how they behave under stress, not in calm conditions.
This is where CIA triad security controls should be chosen like engineering decisions, not as checklist items.
CIA triad and risk management
Security teams use the triad to identify weak points fast. During architecture reviews, it helps clarify the expected outcome of a control. During incident response, it helps classify what was actually harmed. During vendor reviews, it sharpens the questions that matter.
That is also why the importance of the CIA triad goes beyond classrooms and certification exams. It gives teams a durable way to decide what matters most when money, time, and attention are limited.
Tradeoffs explained
More confidentiality can reduce availability.
The tighter the access restrictions, the harder emergency access can become. Security teams run into this all the time with privileged systems, encrypted archives, and break-glass procedures. CSO notes that tradeoffs are necessary in real-world scenarios, and that is exactly right.
More integrity checks can slow performance.
Extra verification steps can add latency, especially in high-volume systems. That does not mean you skip them. It means you place them wisely and test them under load.
Balancing security and usability
This is the real job. Not picking one pillar. Balancing all three. The strongest teams do not ask, “Which one matters?” They ask, “Which one fails first under pressure?”
CIA triad vs. other concepts
CIA triad vs. information security: Information security is the broader practice; the triad is its core model.
CIA triad vs. cybersecurity: Cybersecurity is the broad field; the triad is a foundational framework inside it.
CIA triad vs. AAA: AAA focuses on authentication, authorization, and accounting. The triad focuses on security outcomes.
CIA triad vs. Zero Trust: Zero Trust is an operating model. It can enforce the triad continuously, but it does not replace it.
Best practices
For students and beginners
Learn the definitions, then map each one to a real incident. That makes the model stick. Memorizing terms is easy. Applying them under pressure is not.
For small businesses
Start with MFA, backups, patching, and access reviews. Most small organizations do not fail because they ignored advanced theory. They fail because the basics were left half-done.
For enterprises
Map business-critical systems to triad outcomes. Decide which pillar is most sensitive per workflow. Then test assumptions. Tabletop exercises are useful, but restore tests, privilege reviews, and change-control audits are better.
When we ran a basic review in our lab on a demo web application, the first issue was not malware. It was permission sprawl. A user role created for convenience had read access to far more data than intended. That was a clean confidentiality failure waiting to happen.
In our practical test, we noticed something else. Integrity problems were harder to spot. The app had logs, but they were stored on the same system and protected poorly. If a privileged attacker modified records, the evidence trail could be changed too. That changed how we scored the risk.
We also encountered a challenge while testing availability assumptions. The backup existed, but the restore path was slow and undocumented. That is a classic mistake. Teams feel safe because backups are present, but recovery has never been timed end to end.
Why this matters
A regular user usually feels the triad only after something breaks. A business lives inside it every day. Privacy obligations map to confidentiality. Data trust maps to integrity. Revenue and operations map to availability.
That is why the CIA triad is important in cybersecurity and is not an academic question. It is a budgeting question, an architecture question, and sometimes a survival question.
How to protect your system
Turn on MFA for admin, email, VPN, and cloud accounts.
Review access rights and remove old users, stale roles, and overbroad shares.
Encrypt sensitive data in transit and at rest.
Enable tamper-aware logging and send logs to a protected central destination.
Use hashing or digital signing where file integrity matters.
Patch internet-facing systems first and track certificate expiry.
Test backups by restoring sample systems and files.
Plan failover for critical services instead of assuming uptime.
Segment critical systems so one compromise does not spread everywhere.
Check official advisories from CISA, NIST, major vendors, and your cloud provider for recommended practices.
FAQ
What is cybersecurity in simple words?
Cybersecurity is the protection of systems, devices, networks, and data from unauthorized access, misuse, disruption, or destruction. CISA explicitly ties that protection to confidentiality, integrity, and availability.
What does CIA stand for in cybersecurity?
It stands for Confidentiality, Integrity, and Availability. NIST and CISA both use these principles as core information-security outcomes.
What is an example of confidentiality, integrity, and availability?
Encrypted employee records are a confidentiality example. A signed software update is an integrity example. A restored service after an outage is an availability example.
How does ransomware affect the CIA triad?
Ransomware often hits availability first by locking access, but it can also threaten confidentiality through data theft and integrity through data manipulation or corruption.
Security Checklist
Check one overexposed asset today. Review a shared folder, cloud bucket, or admin role.
Test one integrity signal. Verify that logs, hashes, or version history can actually prove a change happened.
Restore one backup. Not tomorrow. Today.
Trusted source Note: For official definitions and operational guidance, refer to CISA and NIST. Their language is the cleanest reference point for how the industry defines confidentiality, integrity, and availability. (CISA)
Frequently Asked Questions
Was this article helpful?
React to this post and see the live totals.
Share this :