CISA Flags FileZen Risk: CVE-2026-25108 Alert

Hoplon InfoSec
25 Feb, 2026
Is the CISA Warning on FileZen Actually a Wake-up Call for Your Infrastructure?
On February 24, 2026, the Cybersecurity and Infrastructure Security Agency (CISA) officially added a critical vulnerability, tracked as CVE-2026-25108, affecting Soliton FileZen appliances to its Known Exploited Vulnerabilities (KEV) catalog. This decision follows confirmed reports of active exploitation in the wild, where attackers are bypassing security perimeters to execute unauthorized commands. (Reference: CISA KEV Bulletin).
CISA Confirms FileZen Security Risk
Look, we have all been there. It is another Tuesday, and another critical patch lands on your desk. But the recent news regarding how CISA confirms FileZen Security Risk feels different this time. This is not just a theoretical bug discovered by a researcher in a quiet lab. It is a live, breathing threat. For years, organizations relied on FileZen as a secure gateway for moving large files, assuming that a dedicated hardware appliance was inherently sturdier than a standard software portal.
The old way of thinking, trusting the "black box" appliance under your desk, has officially failed us. The new reality requires a "Zero Trust" lens where every device is a potential liability. When CISA confirms FileZen Security Risk, they are telling us that the very tools we bought to stay safe are being turned against us. It is a bit like finding out the bank vault back panel was made of cardboard.
You might be wondering if your business should be worried. If you use Soliton hardware, the answer is a firm yes. These appliances are staples in government offices and large corporate data centers. When CISA steps in, it means the risk has moved beyond the "maybe" stage and into the "active damage" stage. Attackers are currently using this hole to walk into networks without needing a single password.
The Technical Reality of CVE-2026-25108
At its core, this flaw is an OS command injection vulnerability. In plain English, an attacker can send a specifically crafted request to the FileZen web interface and trick the underlying operating system into running their own malicious code. This happens before any login screen appears. You do not need a username. You do not need a password. You just need a network connection to the device.
What makes this particularly nasty is the level of access. Because FileZen often sits in a privileged spot in the network to facilitate file transfers between internal and external zones, a compromise here gives an attacker a perfect beachhead. From this single device, they can pivot deeper into your sensitive databases or move laterally across to your workstations. It is a nightmare scenario for any sysadmin.
Hacker groups have clearly been doing their homework. They found a gap in how FileZen validates user-supplied data, allowing them to slip through the cracks. This is not a fluke. It is the result of persistent threat actors looking for the path of least resistance. They know that if they can use a trusted tool like FileZen to get inside, they can stay hidden much longer than if they tried to brute-force a firewall.
-20260225142723.webp)
Why Was This Vulnerability Left Open?
It often comes down to how these appliances handle input. Developers sometimes focus so much on the "it just works" aspect of file transfers that they might overlook how the system interprets weird characters or unexpected commands in the URL. For a long time, these devices lived in the shadows of the network, rarely getting the same scrutiny as a Windows server or an iPhone.
Active Exploitation: CISA only adds vulnerabilities to the KEV list when there is hard evidence that hackers are using them.
Ease of Access: The fact that no authentication is required makes it a "low effort, high reward" target for cybercriminals.
Critical Infrastructure: Many sectors, like healthcare and finance, use these devices to move HIPAA- or PCI-compliant data.
Bypassing Firewalls: Since the attack looks like normal web traffic, it often sails right past traditional perimeter defenses.
How the Attack Actually Functions
The mechanism is surprisingly simple for a sophisticated hacker. First, they scan the internet for the specific digital signature of a FileZen appliance. Once they find a target, they send a malicious payload via a GET or POST request to the web management or file transfer interface. The FileZen software fails to sanitize this input, passing it directly to the system shell.
Once the command runs, the attacker usually installs a web shell. This is a tiny piece of code that lets them come back whenever they want. They don't need to exploit the bug again. They just use the "backdoor" they created. From there, they can start the final step: quietly siphoning off the very files the device was meant to protect.
I have seen similar cases where the IT team thought they were safe because they had an encrypted VPN. But if the FileZen box is sitting at the end of that VPN, and the box itself is broken, the encryption does not matter. The attacker is already "inside" the trusted zone. It is a sobering reminder that software quality is just as important as network architecture.
A Real-World Perspective: Before and After
Before this news broke, most IT departments viewed their FileZen boxes as "set it and forget it" hardware. It was just a utility. Files went in, files went out, and everyone was happy. There was a false sense of security because the device was proprietary. Many thought that because it was not a common target like Windows, it was "secure by obscurity."
After the exploit, the atmosphere changed to one of quiet panic. Companies are realizing that their most sensitive intellectual property, blueprints, financial audits, and legal contracts may have been sitting on an open shelf. The impact is not just a technical glitch. It is a massive blow to brand reputation and a looming threat of regulatory fines.
I once spoke with a colleague who discovered an intruder in their file-sharing system months after the initial breach. The hacker had been sitting there, reading every contract the company signed for nearly half a year. That is the kind of long-term damage we are looking at when CISA confirms the FileZen security risk. It is not just about the one-time hack. It is about the loss of control over your data.
Who is Currently in the Crosshairs?
The primary targets appear to be large-scale enterprises and government entities, particularly those in the Asia-Pacific region, where Soliton has a significant market share. However, because FileZen is used globally for secure data exchange, no one is truly off the hook. If your business handles high-value data and uses this appliance, you are a target.
Government Agencies: Especially those handling sensitive policy or personnel files.
Financial Institutions: Banks that use FileZen for secure document exchange with clients.
Tech Firms: Companies sharing source code or R&D documents.
Healthcare Providers: Entities moving patient records between facilities.
Outcomes and Measurable Impact
The fallout from this vulnerability is still being tallied, but the initial data is sobering. Organizations that fail to patch within the CISA-mandated window face a significantly higher chance of a full network compromise. We are not just talking about losing a few files. We are talking about total system downtime.
From a performance standpoint, once an attacker starts running scripts on the device, legitimate users often report significant lag. If your FileZen box is suddenly sluggish or crashing, it might not be a hardware failure. It might be an active breach. The financial cost of cleaning up such an incident can easily reach six or seven figures when you factor in forensics, legal fees, and lost productivity.
If we look at the historical data for similar command injection bugs, the average cost of a breach for a mid-sized company is roughly $4 million. When you add the specific "FileZen" context, the risk is concentrated because these devices hold the "crown jewels" of data. CISA confirms FileZen Security Risk for a reason: the potential for a catastrophic leak is simply too high to ignore.
Executive Action Plan
The first step is a bit of a reality check. Do you even know where your FileZen devices are? You would be surprised how many companies have "shadow IT" or old appliances sitting in a rack that everyone forgot about. You cannot protect what you do not know exists.
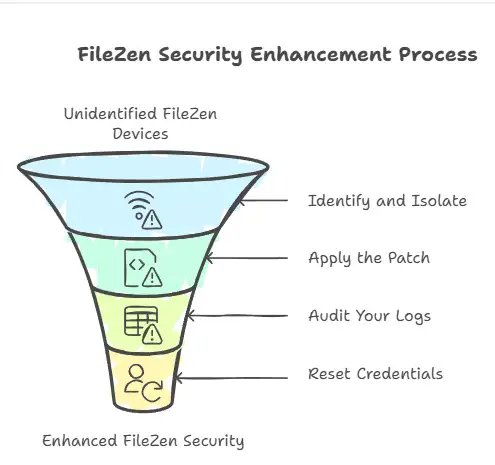
Identify and Isolate: Immediately check if any FileZen devices are exposed to the public internet. If they do not need to be online, pull the plug until you can verify their status.
Apply the Patch: Soliton has released emergency updates. Do not wait for your next maintenance window. Install them tonight.
Audit Your Logs: Look for unusual outbound traffic from the device. If your FileZen is suddenly talking to an IP address in a country where you do not do business, you have a problem.
Reset Credentials: While the exploit does not require a password, once a hacker is in, they likely stole every credential stored on the machine. Change everything.
At Hoplon Infosec, we recommend a "Verify, Then Trust" strategy. Segregate your file-sharing devices into an isolated VLAN and monitor their behavior for any deviation from the norm. We help businesses build these "safety nets" so that a single device failure does not bring down the entire company.
Frequently Asked Questions
Does a firewall protect me from this? Not necessarily. Since the exploit uses standard web traffic on port 443, your firewall likely sees it as a normal request and lets it through. You need a Web Application Firewall (WAF) or a specific patch to stop it.
Is CVE-2026-25108 only for old versions? It affects several versions of the FileZen firmware. You need to check the specific advisory from Soliton to see if your build is vulnerable. Do not assume you are safe just because you bought the box recently.
What if I cannot patch immediately? The safest move is to take the device offline. If that is not possible, restrict access to the web interface to a very specific set of internal IP addresses using an Access Control List.
How do I know if I have already been hacked? Look for new, unauthorized user accounts or files with strange names like "sh.php" or "cmd.aspx" in the web directories. If you see those, call an incident response team immediately.
Summary of the Crisis
The revelation that CISA confirms FileZen Security Risk is a stark reminder that our infrastructure is only as strong as its weakest link. This command injection flaw allows for complete system takeover, and it is being used by threat actors right now. The main benefit of acting today is preventing a catastrophic data breach that could end your business.
we specialize in identifying these hidden risks before they become headlines. Our approach goes beyond simple patching. We look at the entire architecture to ensure that even if one device fails, your data remains secure. Don't wait for the next CISA alert to secure your perimeter.
We combine deep technical forensics with strategic business risk management, ensuring your data is not just patched but truly protected. Immediate reduction in "Zero Day" exposure and a fortified network that resists active exploitation. Hoplon Infosec provides 24/7 monitoring and rapid response for critical infrastructure vulnerabilities.
Ready to harden your defenses? Contact Hoplon Infosec today for a comprehensive vulnerability assessment. Let us make sure your secure devices are actually doing their job.
Author: Cybersecurity Research Team
Published: February 25, 2026
Sources: CISA Known Exploited Vulnerabilities Catalog, Soliton Security Advisory.
Was this article helpful?
React to this post and see the live totals.
Share this :