Eurail Data Breach 2025 Exposes 300,000 Users
-20260409113905.webp&w=3840&q=75)
Hoplon InfoSec
09 Apr, 2026
Did the breach really affect more than 300,000 people?
Yes. The clearest public record so far shows that Eurail’s December 26, 2025 cyber incident led to notifications for 308,777 people, and at least one official notice confirms the exposed data included name and passport number. Eurail first disclosed the security issue in January 2026, and later notices filled in more of the scope.
Eurail Data Breach
The short version of the Eurail breach that happened is that Eurail detected unusual activity in a segment of its network, launched an investigation with outside cybersecurity specialists, and determined that an unauthorized actor had transferred files out of the company’s environment on December 26, 2025.
That timeline comes directly from the company’s breach notice and lines up with the broader public reporting that followed in January and April 2026.
This is where the story became more serious than a typical service interruption. The January disclosure described unauthorized access to customer data, but later reporting and regulatory filings added harder numbers and more concrete data elements.
By April 2026, public reporting tied the incident to more than 300,000 affected people, which moved the story from a niche rail-travel problem into major travel data breach news.
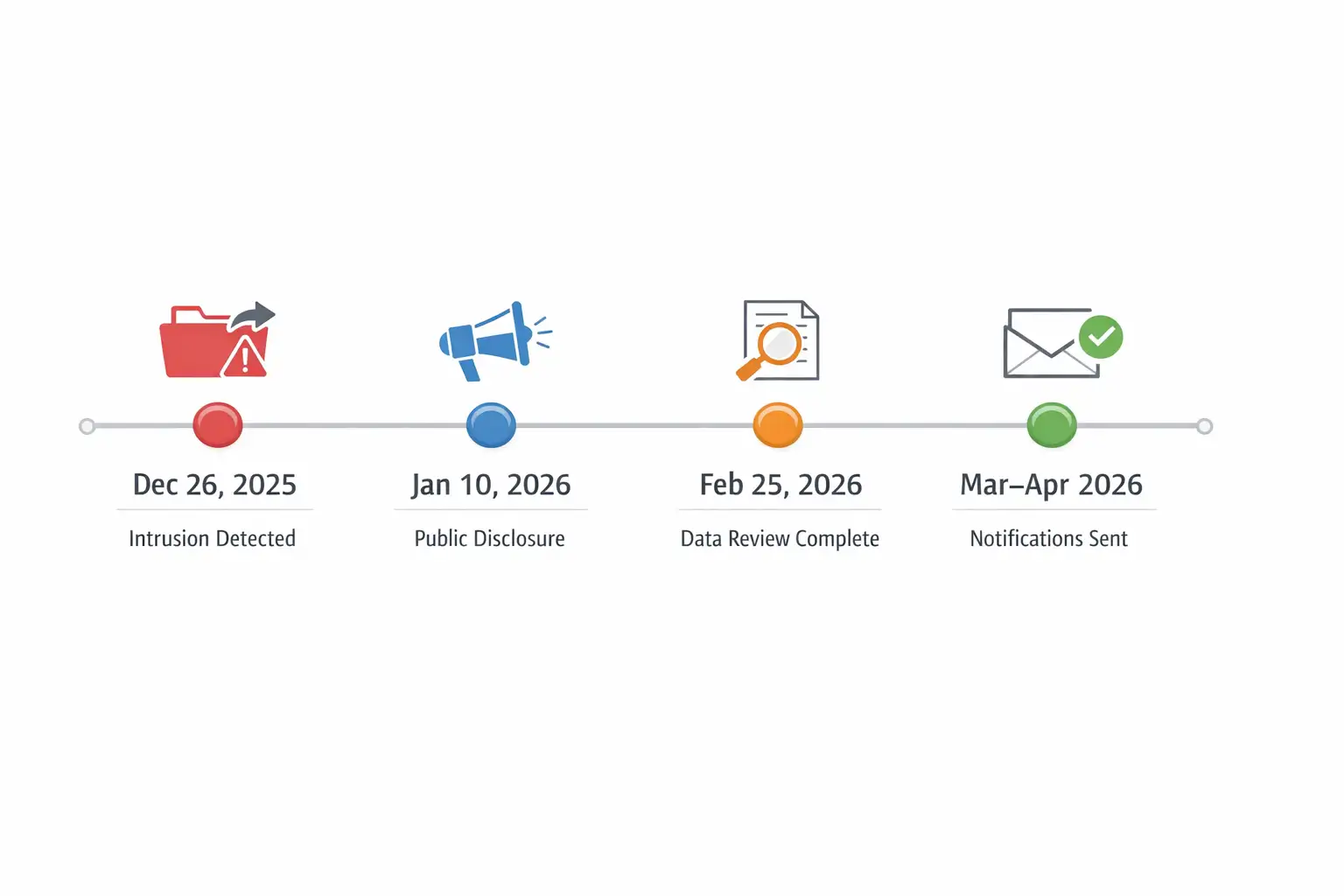
The confirmed timeline
December 26, 2025
Public breach-notice language says the unauthorized actor transferred files from Eurail’s network on this date. That is the most precise date publicly confirmed so far.
January 10, 2026
Eurail posted a notice saying it had experienced a security breach that resulted in unauthorized access to customer data. At that stage, the company was still framing the issue around an ongoing investigation rather than a fully measured incident count.
February 25, 2026
The California sample notice says Eurail finished reviewing the files involved and determined on February 25 that they contained personal information. That detail is important because it explains the lag between the December attack and the later customer notifications.
Late March and early April 2026
Public filings and later reporting showed the impact count at 308,777 people. That is the number most searchers will care about when looking up Eurail data leak explained.
What data was exposed
For at least some affected individuals, the answer is unusually clear. The California breach notice says the information involved included name and passport number. That alone is enough to treat this as a serious personal-data event, even without bank-card exposure.
The broader picture is more layered. Earlier reporting around the incident said hackers stole files containing basic identity and contact information, and one January report said the incident affected personal, order, and reservation information for customers with a Eurail pass and for people who made seat reservations.
That is why searchers are seeing phrases like "Eurail breach details" and "Eurail customer data leak" in results.
There is also an important special case involving DiscoverEU travelers. The European Youth Portal said the data that may be involved for that group could include name, surname, date of birth or age, passport or ID information or photocopies, email address, postal address, country of residence, phone number, IBAN, and health data.
That is a much more sensitive mix. It also means some discussions around Eurail customer info leaks are not exaggerating, but the exact data elements vary by affected group.
One clarification matters here. SecurityWeek reported that Eurail said it does not store bank or credit card information, nor visual copies of passports, even while the European Youth Portal warned that DiscoverEU participants may face exposure involving passport or ID photocopies, IBAN references, and health data.
The safest factual conclusion is this: confirmed exposure differs by dataset, and not every affected person appears to face the same level of risk.
How the attack appears to have unfolded
Eurail’s own public language remains cautious. It has described a security breach and unauthorized access, but it has not published a full technical postmortem naming a threat actor, malware family, or CVE.
So if you were hoping for a neat one-line answer about the Eurail hack 2025, that answer is not publicly available yet. Any article claiming a specific exploit chain as settled fact is moving too fast.
What has been reported is that, in February, a hacker claimed to have stolen roughly 1.3 terabytes of data from Eurail’s AWS S3, Zendesk, and GitLab instances, including source code, support tickets, and database backups.
Later reporting said the company confirmed that stolen data was being offered on the dark web and that a sample dataset had appeared on Telegram. Those claims are serious, but readers should separate hacker boasts from fully audited company forensics.
The existence of public sale activity increases credibility, but it does not prove every forum claim is accurate in scope.
That distinction matters because breach stories often grow legs online. Once “millions of records” enters the conversation, it tends to outrun the verified record.
For now, the strongest confirmed public number remains the roughly 308,777 impacted individuals tied to notice activity, not every larger claim floating around cybercrime forums.
Who is affected?
The incident appears to touch multiple customer pools. Public reporting said the January disclosure covered customers issued a Eurail pass and those who made seat reservations, and Eurail’s own public notice framed the incident as unauthorized access to customer data. That makes this bigger than a single app glitch or a small partner issue.
It also appears wider than one country. Eurail is the travel operator behind digital passes covering 33 national railways, and the brand’s public-facing site positions the pass as a cross-border product for travel across Europe.
A breach in that environment naturally raises cross-jurisdiction data-protection questions because the affected people are likely spread across many markets and booking channels.
The DiscoverEU angle makes the impact even more sensitive. That program is linked to young travelers, which means some records may belong to first-time international rail users who are less prepared for post-breach phishing attempts. In plain English, this is not just a company problem. It is a consumer-trust problem.
-20260409113904.webp)
Why this breach matters more than a routine leak
A lot of data-breach stories blur together. Email and password, then a reset notice, then everyone moves on. This one feels different because passport numbers and travel-linked records are more durable.
You can change a password in ten minutes. You cannot casually replace your identity history, past booking footprint, or a travel profile that may tie together names, routes, contact details, and government ID data.
This also lands in a broader trend. Verizon’s 2025 DBIR says third-party involvement in breaches increased and that credential abuse remains a major path into organizations, while IBM’s 2025 breach-cost report says the global average cost of a data breach was $4.44 million.
That does not mean Eurail’s case followed those exact patterns, but it explains why the personal data leak and travel industry angle is attracting attention. Travel platforms sit at the messy intersection of identity, payments, logistics, vendors, and customer support systems.
Eurail’s response so far
The company’s public statements and notices say it activated incident-response procedures, worked with third-party cybersecurity professionals, notified law enforcement, and took steps to enhance security measures.
The European Youth Portal added more detail, saying affected systems were secured, credentials were reset, monitoring and security controls were enhanced, and forensic work continued.
That response is directionally what users want to hear, but there is still a visibility gap. Travelers looking for "is Eurail safe after breach?" are really asking two things at once: Did the company contain the intrusion, and has it clearly explained what happened?
On the first point, public notices say the issue was contained and that monitoring is ongoing. On the second, the public record is still incomplete because there is no detailed technical breakdown naming the attack path or full system exposure.
Risks for affected users
The immediate risk is phishing. Both the European Youth Portal and U.S. guidance stress caution about suspicious messages, unsolicited contacts, and attempts to trick victims into sharing more information.
That makes sense. Once attackers have names, travel context, and possibly passport-linked details, fake support emails become much more convincing.
The next risk is identity misuse. The FBI says the impact of identity theft can last months or even years because criminals do not always use stolen information right away.
That warning is especially relevant here because passport data is not something most people monitor daily the way they watch a debit card.
There is also the quieter risk of account takeover and repeated scam pressure. The Identity Theft Resource Center’s 2025 annual report says 88 percent of people who received a breach notice experienced at least one negative consequence, with phishing or scam attempts among the most common.
That does not prove every Eurail customer will face the same outcome, but it is a useful reality check. The breach notice is rarely the end of the story.
What affected users should do now
1. Treat every follow-up message with suspicion.
If you receive an email, text, or phone call that claims to be about your pass, refund, reservation, or verification step, slow down. Do not click first and think later.
Go to the official site directly or use the contact information provided in the notice. Eurail’s own guidance says not to share information with someone who contacts you unsolicited and claims to work for the company.
2. Change passwords that overlap
Even if the confirmed notice mentions only name and passport number, breach reporting around the incident discussed broader customer and support data.
If you reused the same password anywhere connected to travel, email, or customer support accounts, change it now and enable multi-factor authentication where possible. This is the practical answer to how to protect data after a breach.
3. Monitor for identity misuse
Check for unfamiliar account activity, new account openings, and documents or messages you did not expect. U.S. consumer guidance also recommends reviewing credit reports and considering a fraud alert if identity misuse becomes a concern.
4. Save every official notice
Keep the breach letter, screenshots of suspicious contacts, and any case numbers from support or regulators. If something goes wrong months later, that paper trail helps. It is boring advice, but boring advice is usually the stuff that saves time later.
Quick comparison table
|
Incident |
Confirmed scope |
Confirmed data types |
Key risk |
What stands out |
|
eurail data breach 2025 |
308,777 notified individuals |
Name and passport number confirmed in at least one notice; some groups may face broader exposure |
Identity theft, phishing, spoofing |
Travel context plus ID-linked records |
|
January-stage Eurail disclosure |
Number not yet public at that time |
Customer data, plus personal, order, and reservation information reported |
Uncertainty and underestimation risk |
Early disclosure had fewer hard numbers |
|
DiscoverEU-related exposure |
Exact count not public |
Passport or ID info, possible photocopies, IBAN, health data |
Higher sensitivity for some users |
Impact appears uneven by traveler group |
Travel-industry impact
The biggest lesson here is not only about one company. It is about how much sensitive information modern travel platforms hold by default.
Booking systems, support desks, partner channels, reservation platforms, and identity checks all create a larger digital footprint than many travelers realize. That is why a cybersecurity breach Europe rail story resonates beyond rail passes.
It also raises a fair question about data minimization. If a travel company or its partners retain more identity data than users expect, the damage multiplies when something goes wrong.
Readers asking about the Rail Europe data breach or broader European rail platform safety are really responding to that deeper discomfort: why was so much data in one place, and for how long? The public record does not fully answer that yet. But it should.
What smart travelers should do after this kind of breach
- Change any reused passwords tied to travel, email, and support accounts.
- Watch for fake “reservation problem” or “verify your pass” messages.
- Keep a copy of the notification letter and your recent booking records.
- Be extra cautious if you were part of DiscoverEU or submitted passport or ID documents.
- Use direct website logins, not links in emails, for refunds, seat reservations, or account checks.
- If identity misuse appears, report it quickly through official recovery channels.
A research-backed perspective
IBM’s 2025 breach report, based on research independently compiled by Ponemon Institute, puts the global average cost of a data breach at $4.44 million.
That number is not about Eurail specifically, but it explains why breach response, disclosure timing, and trust recovery now matter almost as much as the initial intrusion itself. In other words, the cleanup is not a side story. It is half the story.
Final takeaway
The reason the Eurail data breach of 2025 is drawing attention is not only the size of the incident. It is the type of information involved and the context around it. Travel data can be messy, personal, and surprisingly sticky. Once names, passport-linked records, and booking-related data leave the building, the risk does not end with the press release.
For readers trying to sort signal from noise, here is the cleanest answer. The breach is real, the impact count is substantial, the confirmed exposure includes passport-linked data for at least some victims, and some broader claims remain under investigation or vary by traveler group. That makes this a serious Eurail customer data leak, not a rumor and not a story to shrug off.
You can also read these important cybersecurity news articles on our website.
· Apple Update,
For more, please visit our homepage and follow us on X (Twitter) and LinkedIn for more cybersecurity news and updates. Stay connected on YouTube, Facebook, and Instagram as well.
Published: April 09, 2026
Last updated: April 22, 2026
Author: Radia | Senior Cybersecurity Analyst & Breach Reporter.Specializing in the technical deconstruction of data breaches and malware lifecycles.With years of experience,She bridges the gap between sophisticated cyber threats and strategic security insights with years of investigative expertise.
Security Alert: The eurail data breach 2025 may expose personal data, including sensitive travel information. Be cautious of phishing emails or suspicious messages. Do not share personal details or click unknown links. Always verify through official sources. Stay alert and protect your data.
Frequently Asked Questions
Was this article helpful?
React to this post and see the live totals.
Share this :