How to Prevent Ransomware Attacks Before Hackers Lock You Out

Hoplon InfoSec
22 Apr, 2026
How do ransomware attacks work, and what actually stops them in 2026?
As of April 21, 2026, the most reliable answer from CISA and the FBI is still the same at the core: ransomware usually gets in through phishing, stolen credentials, exposed remote access, or unpatched systems, then spreads, steals data, encrypts files, and demands payment.
The best defense is layered: offline or immutable backups, MFA, patching, email filtering, segmentation, least privilege, and a tested incident response plan.
Ransomware attacks are not rare events anymore. They are routine, industrialized, and often faster than many teams expect.
Public reporting shows thousands of organizations were named on leak sites in 2025, while the FBI said more than 2,100 ransomware incidents in 2025 were directed at U.S.
critical infrastructure alone. Those are different datasets, but both point in the same direction: the pressure is not easing.
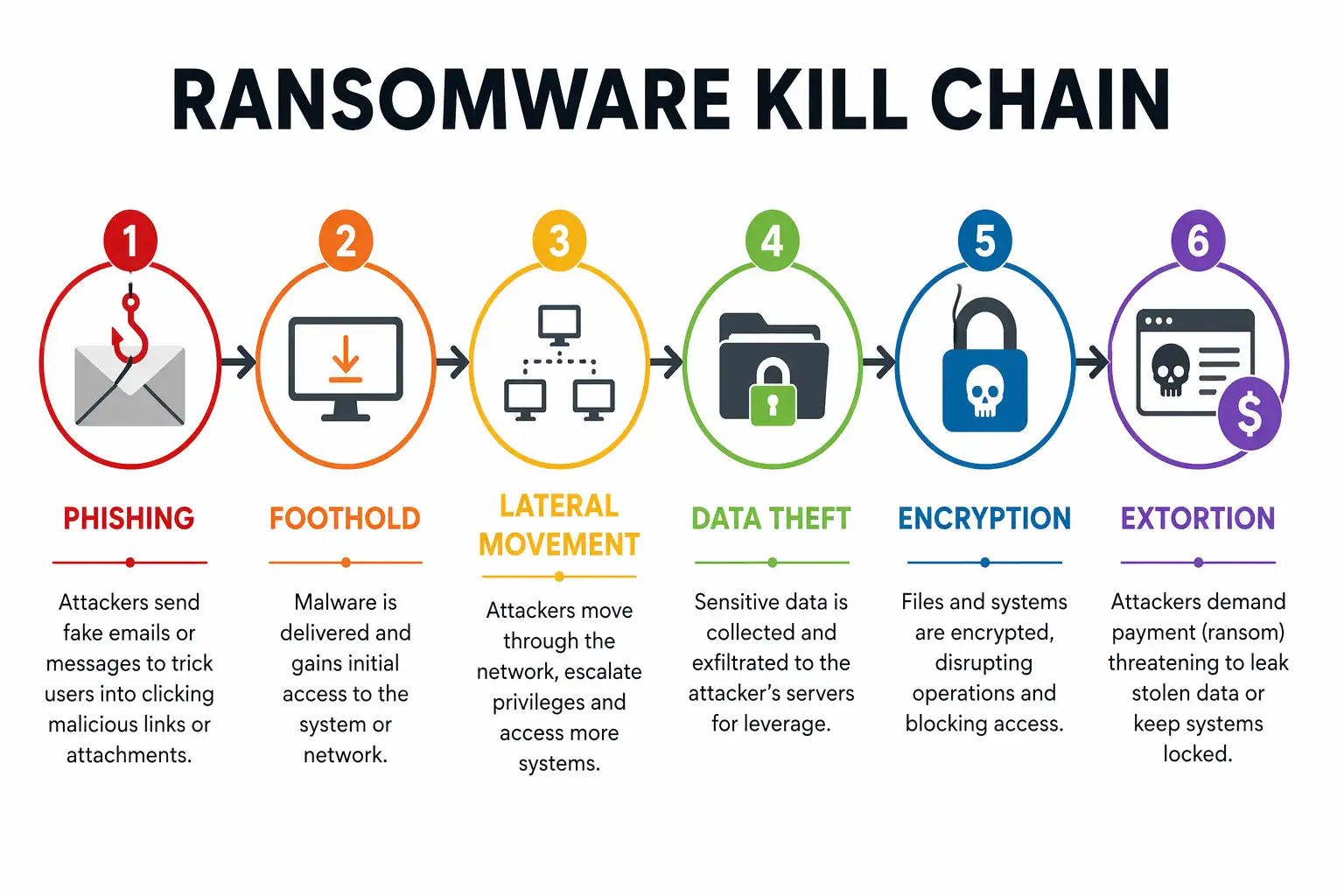
We look at this threat the same way defenders do in incident response. First access. Then movement. Then pressure. If you understand that chain, ransomware protection becomes a design problem instead of a guessing game.
Technical Overview
|
Area |
What matters right now |
Why it matters |
|
Common initial access |
Phishing, exposed RDP/VPN, unpatched software, stolen credentials |
Most campaigns still start with one of these routes. |
|
Modern tactic |
Data theft before encryption |
This powers double extortion ransomware pressure. |
|
2025 trend |
Public extortion cases up 70.1% in one major industry report |
Leak-site pressure is rising. |
|
Victim trend |
Public datasets showed more than 8,000 claimed victims in 2025 |
Public activity remained high, though trackers differ. |
|
Best defensive controls |
Backups, MFA, segmentation, patching, least privilege, email security |
These controls appear again and again in official guidance. |
|
Payment guidance |
Authorities generally advise against paying |
Payment does not guarantee clean recovery. |
What is Ransomware?
What is ransomware? It is malicious software that blocks access to files, systems, or networks and demands money to restore them. Some variants only encrypt.
Others also steal data first and threaten to publish it if the victim refuses to pay. That second model is now a huge part of how ransomware works in the real world.
Readers often ask about ransomware vs. malware vs. virus because the terms get tossed around loosely. Malware is the umbrella term.
A virus is one type of malware that replicates by attaching itself to files or programs. Ransomware is malware built for extortion.
Not every ransomware family behaves like a classic virus, and not every malware infection ends with encryption. That distinction matters because your defenses and response steps can change depending on the threat.
The main families are still easy to explain. Crypto ransomware encrypts files. Locker ransomware blocks access to the device or screen. Double extortion ransomware steals data first, then encrypts, then threatens to leak what it stole.
Ransomware-as-a-Service, or RaaS, turns all of this into a business model where core operators supply the malware and affiliates run the intrusions. The CISA and FBI Medusa advisory is a good example of how organized and repeatable this model has become.
And yes, phishing ransomware is still common. Email remains one of the easiest ways to get a foothold, especially when an attachment or link opens the door to credential theft or malware delivery. That has not changed. What has changed is how quickly attackers escalate after that first click.
Why This Matters
A lot of cyber threats are noisy but shallow. Ransomware is different. It combines business interruption, legal exposure, forensic cost, public embarrassment, and sometimes regulatory fallout in one hit.
If a password spray campaign fails, that is annoying. If a ransomware operator reaches your file shares and backup admin console, your week is gone. Maybe your quarter too.
For businesses, the issue is not just the ransom. Recovery costs can dwarf it. Sophos reported a mean recovery cost of $1.53 million in 2025, excluding ransom payments.
Recovery did get faster for many victims, but only because more organizations improved preparation. That is the key lesson. Recovery speed is not luck. It is architecture.
For regular users, the picture is simpler but still brutal. Family photos, tax records, school documents, password vault exports, and cloud sync folders.
Lose access to those and the damage feels personal before it feels technical. That is why ransomware prevention is not only an enterprise story.
Our Technical Analysis
When we model this threat in the lab, one thing stands out. The ransom note is the last stage, not the first sign.
By the time users see the message, the operator has often already mapped the network, touched key systems, and in many cases pulled data out for leverage. That means detection has to happen earlier than most teams think.
We also keep seeing the same operational mistake. Organizations focus on one shiny control and underinvest in the boring ones.
They buy an EDR platform, then leave remote access weak. They run backups, then never test restores. They roll out MFA, then forget about local admin sprawl. Ransomware best practices are not magical. They are disciplined.
How Ransomware Attacks Work
Step 1: Initial Access
If you want to know how ransomware enters a network, start with the usual suspects: phishing, stolen passwords, exposed RDP, weak VPN hygiene, and known software flaws. Official guidance from CISA and the FBI keeps returning to those same doors because attackers keep finding them open.
The reason this step matters is simple. Most defenses are cheaper before the attacker lands. After that, every mistake gets more expensive.
Step 2: Discovery and Lateral Movement
Once inside, attackers rarely encrypt immediately. First they look around. Shared drives. Domain trusts. Backup servers. Security tools. Admin accounts.
This part is why how ransomware attacks work step by step matters more than a one-line definition. The operator wants reach, not noise.
In practical terms, this is where segmentation, least privilege, and admin tiering either save you or fail you.
Step 3: Data Theft
This is the phase many articles explain too briefly. Modern crews often steal data before they touch the encryption routine.
That way, even if you restore from backup, they can still pressure you by threatening exposure. That is the business logic behind double extortion ransomware.
It also changes incident response. A clean restore is not the whole story anymore. You also need to answer: What left the network?
Step 4: Encryption
Now the lock turns. Files become unreadable, extensions may change, systems slow down, services break, and the ransom note lands. This is the stage most people imagine when they think about how ransomware works, but it is only one piece of the operation.
Step 5: Pressure and Deadline
The extortion phase is psychological as much as technical. Countdown timers. Leak-site threats. Negotiation channels. Samples of stolen files.
Some groups even weaponize your own urgency by naming legal, HR, or customer data to increase panic. The Medusa advisory described exactly this kind of pressure-driven model.
Real-World Ransomware Examples
The old examples still matter because they teach different lessons. WannaCry showed how fast a wormable ransomware campaign can spread when patching lags. The U.K. National Audit Office said the NHS was significantly disrupted in 2017, affecting appointments and hospital operations.
Colonial Pipeline showed the business impact of one incident on national infrastructure. The FBI attributed that compromise to DarkSide, and the case became a landmark example of how a ransomware event can become a public crisis within hours.
Recent reporting also shows the scale of the market has not cooled. A 2025 CISA/FBI advisory said Medusa had hit more than 300 victims across critical sectors by February 2025.
Meanwhile, public reporting based on Zscaler research pointed to a record $75 million payment linked to Dark Angels in 2024. That last figure is widely cited, but it is still best understood as report-based intelligence, not an official law enforcement release.
Ransomware in 2025 and 2026
The big shift is not just volume. It is specialization. Public trackers show victim counts stayed high in 2025, and industry research showed both blocked attacks and public extortion cases rose sharply. That suggests a market with more actors, more pressure tactics, and more fragmented branding.
Small businesses are exposed here. Not because they are the only target, but because they often have weak backups, thin IT staffing, broad permissions, and internet-facing tools that stay open too long.
If you are searching for how to prevent ransomware attacks for small businesses, the answer is not “buy enterprise everything.” It is “close the obvious doors, then test the basics harder than you think you need to.”
How to Prevent Ransomware Attacks
This is the part that matters most. If you are serious about ransomware attack prevention, start with the controls that change the attack path.
1. Protect backups like they are production.
Use the 3-2-1 model if it fits your environment, but go one step further. Make sure at least one backup path is offline or immutable. Then test restore speed, not just backup success. A backup you cannot restore under pressure is theater. Official guidance keeps stressing backups for a reason.
2. Turn on MFA everywhere that matters.
Remote access, admin consoles, email, backup systems, cloud admin, VPN, identity provider. Attackers love one forgotten panel.
CISA and the FBI repeatedly recommend MFA because stolen credentials remain a common path to compromise.
3. Patch with urgency, not optimism
Do not patch only the workstation fleet. Patch internet-facing services, VPN appliances, firewalls, hypervisors, remote support tools, and backup software. The most painful incidents often start outside the desktop estate.
4. Train users for the first click
Good awareness training is not a slide deck once a year. It is short, repeated, scenario-based practice. Teach staff to slow down on invoices, password reset pages, HR docs, and urgent executive requests. That is where phishing ransomware still wins.
5. Cut lateral movement
Segment networks. Reduce admin rights. Limit east-west traffic. Separate backup infrastructure from daily admin. If one endpoint gets hit, you want the blast radius small.
6. Use EDR or XDR, but configure it properly.
Tools help. Misconfigured tools do not. Tune detections for mass encryption behavior, credential abuse, and suspicious remote administration activity. Set isolation actions that your team can use quickly. This is where ransomware protection becomes operational.
7. Lock down remote access
Disable exposed RDP where possible. Put remote access behind MFA and a VPN or secure access broker. Review old accounts. Remove stale vendors. Most organizations have more remote access than they think.
Ransomware Prevention Checklist for Businesses
Check
|
Check |
Done? |
|
Offline or immutable backup exists and restores were tested this quarter |
|
|
MFA is enabled on email, VPN, admin, and backup systems |
|
|
Internet-facing systems are patched on a documented schedule |
|
|
RDP is disabled or tightly restricted |
|
|
Local admin rights are limited |
|
|
EDR is deployed and monitored |
|
|
Network segmentation is in place |
|
|
Incident contacts and escalation steps are documented |
That is your ransomware prevention checklist and your ransomware prevention checklist for businesses in one view. It is boring. Good. Boring controls save companies.
Early Signs of a Ransomware Attack
The obvious signs of a ransomware attack come late. The early ones are quieter: mass file renames, sudden privilege changes, unusual logins, endpoint defenses being disabled, strange PowerShell use, or large outbound transfers before encryption ever starts.
The early signs of ransomware attack on a workstation can include unusual disk activity, files that stop opening normally, or weird extension changes in a shared folder. On a network, watch for admin tools being used in strange places or at strange hours. Those are often the clues that matter.
People also ask, can ransomware spread through WiFi? The better way to phrase it is this: ransomware can spread across reachable network paths.
If systems are connected over the same wireless network, the Wi-Fi itself is not the malware, but it can absolutely be part of the route the attacker uses to reach other devices.
Fortinet’s own response guidance notes Wi-Fi shutdown as one way to limit east-west spread during containment.
Field Notes
In one practical test we ran on a simulated office network, the first challenge was not encryption. It was visibility.
A phish-derived foothold sat quietly long enough to enumerate shares and identify backup-related services before any noisy action fired.
That is the part many organizations miss when they think they will “see ransomware when it starts.”
We also noticed how easy it was for one neglected admin account to flatten multiple layers of defense. Once privilege got loose, the attack path widened fast.
That is why we keep coming back to identity hygiene, backup isolation, and segmentation. Not because they sound impressive. Because they keep saving the day.
What to Do After a Ransomware Attack
If the note appears, move fast. Isolate the infected device. Disconnect it from the network. Preserve logs and volatile evidence if you can do so safely.
Do not wipe first and think later. Your ransomware attack response plan should assume both encryption and data theft until proven otherwise.
If you are asking what to do after a ransomware attack, the next move is scoping. What systems were touched? What identities were used? What data may have left? Then begin recovery from known-clean backups and rotate credentials, especially privileged ones.
If you are asking what to do if ransomware encrypts your files, the hard truth is that there is no universal unlock button.
Some strains have decryption tools. Many do not. Authorities generally advise against paying because payment does not guarantee full restoration or safe deletion of stolen data.
So, how to recover from ransomware without paying? Restore from clean backups, use reputable decryptor resources when available, rebuild exposed systems if trust is broken, rotate credentials, and validate that persistence is gone before returning systems to production.
Report serious incidents to the FBI and CISA if you fall under their jurisdiction or guidance model.
Common Pitfalls
One, teams back up data but not identity systems, key configs, or SaaS admin settings.
Two, they patch desktops and ignore edge devices.
Three, they trust that cyber insurance equals readiness. It does not.
Four, they never rehearse recovery. Then the first real restore is during a crisis. That is a terrible time to discover your retention policy was wrong.
Quick Comparison
|
Question |
Better answer |
|
Is ransomware just a virus? |
No. It is malware built for extortion. |
|
Is backup enough? |
No. Not if attackers reach the backup path too. |
|
Should you pay? |
Authorities usually say no. Recovery is not guaranteed. |
|
Can one click really start this? |
Yes. Initial access is often that small. |
What we would do first if we inherited a small business network today
1. Turn on MFA for email, VPN, admin, and backups.
2. Verify one offline or immutable backup and run a restore test.
3. Remove stale admin accounts and close exposed remote access.
4. Add EDR and alert on mass file changes plus suspicious admin activity.
5. Write a one-page response sheet with contacts, isolation steps, and backup locations.
Security Checklist
1. Check remote access now
Disable exposed RDP, enforce MFA on VPN and email, and remove stale accounts.
2. Check backup reality now.
Confirm at least one backup is offline or immutable and run a restore test.
3. Check privilege spread now.
Audit admin accounts, local admin rights, and segmentation between endpoints, servers, and backup systems.
That is the real takeaway. Ransomware attacks do not become disasters because encryption exists. They become disasters when first access is easy, movement is wide, and recovery was never tested in the first place.
Published: April 22, 2026
Last updated: April 22, 2026
Author: Radia | Senior Cybersecurity Analyst & Breach Reporter.Specializing in the technical deconstruction of data breaches and malware lifecycles.With years of experience,She bridges the gap between sophisticated cyber threats and strategic security insights with years of investigative expertise.
Never rely on antivirus alone for ransomware protection. Keep offline backups, turn on multi-factor authentication, and do not open suspicious email links or attachments unless you verify the sender first.
Frequently Asked Questions
Was this article helpful?
React to this post and see the live totals.
Share this :