Top 5 Benefits of Security Penetration Testing for Your Business

Hoplon InfoSec
15 Feb, 2026
Does your organization really have security, or does it just look that way on the outside? According to the FBI's Internet Crime Complaint Center and CISA, U.S. businesses will still be dealing with record levels of ransomware campaigns, cloud misconfigurations, API abuse, and credential theft in 2026. One thing that many of these events have in common is that they all involve untested weaknesses. That's where security penetration testing is very important.
Penetration testing for security is a planned and moral way to mimic real attacks on systems, apps, networks, and people. It helps businesses find weaknesses that hackers can use before they do. It's no longer optional for IT managers, CISOs, compliance officers, and even cybersecurity students to learn about this field. It is the basis.
This guide will explain what security penetration testing is, how it works on a technical level, why it's important in today's world of threats, and the five main business benefits it offers. We will also look at methods, reasons for compliance, common mistakes, and useful information from real-world assessments.
What is testing for security breaches?
Security penetration testing, also called a security penetration test or ethical hacking engagement, is a controlled cybersecurity test that finds and uses weaknesses in systems, networks, or applications with permission.
A basic vulnerability scan only shows possible weaknesses, but security penetration testing goes further. It tries to find out if those weaknesses can really be used. That difference is very important. A vulnerability report could have hundreds of results. A penetration test shows which of those results are the most important.
History and Goal
The idea came from early military security assessments and red team drills. As enterprise IT systems grew and internet access became more common, companies needed a way to measure risk exposure that was proactive. The outcome was a standardized penetration testing methodology employed across various industries.
Security penetration testing is now used in places like:
Business networks
Cloud infrastructure platforms
Web applications and APIs
Mobile applications
Industrial control systems
Financial platforms
Its main goal is easy: find weaknesses that can be used before the enemy does.
How Security Penetration Testing Works
Knowing how things work helps you tell the difference between hype and reality. A structured penetration testing methodology is used in a professional engagement.
1. Planning and Setting Limits
Before testing starts, the scope is set. This includes:
IP ranges and systems that are in scope
Type of testing, like black box, gray box, or white box
Legal permission and rules for how to act
When to talk and how to do it
Clear scoping keeps operations running smoothly and makes sure that the law is followed.
2. Reconnaissance and Enumeration
Testers use both active and passive methods to get information. This could mean:
DNS enumeration
Researching public records
Finding subdomains
Port scanning
Service fingerprinting
People in professional settings often use tools like Nmap, Burp Suite, and Metasploit.
3. Finding Weaknesses
This step may use vulnerability assessment methods like:
Automated scanning
Manual configuration reviews
Credential testing
Checking old versions of software
For instance, testers check to see if a system has an unpatched Apache Log4j component that is vulnerable to CVE 2021 44228 and can be used to exploit it.
4. Exploitation
This is where security penetration testing starts to be different. Testers try to safely take advantage of weaknesses.
Some common ways to exploit people are:
SQL injection in web applications
Cross-site scripting during web application security testing
Privilege escalation
Credential reuse attacks
Access to cloud storage that isn't set up correctly
5. Post Exploitation and Reporting
If they get in, testers check:
Risk of data exposure
Options for lateral movement
Opportunities for persistence
Severity of the impact
A detailed report follows that talks about the findings, evidence, risk ratings, and how to fix the problems.

Why Security Penetration Testing is Important for Cybersecurity
The threat landscape isn't just a theory. It is always working and operational.
Ransomware operators take advantage of RDP services that are open. Cloud misconfigurations let sensitive data leak out. Errors in APIs put customer data at risk. These events are often caused by vulnerabilities that could have been found through security penetration testing.
Risk Context
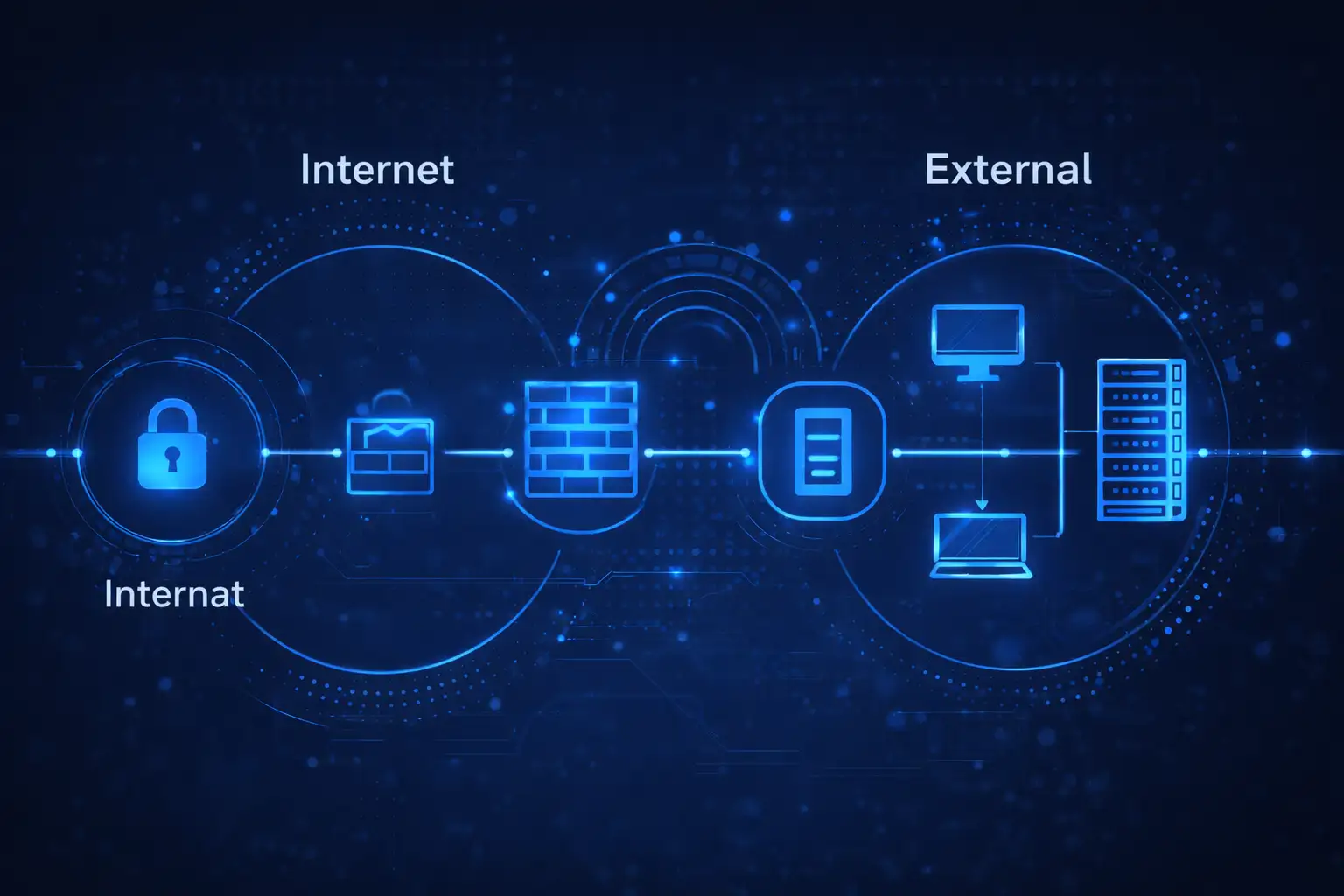
Think about external penetration testing. It acts like attacks from the public internet. A lot of breaches start with services that were never properly secured.
Internal penetration testing, on the other hand, looks at the risk of insiders or what happens when a perimeter is broken. This is important because a lot of modern attacks start with a breach of the perimeter.
Real-World Scenario
Think of a medium-sized healthcare company in the US. They do a regular cybersecurity assessment, but they never check to see if it can be exploited. Months later, an attacker uses a known VPN flaw to get in, raise their privileges, and install ransomware.
If network security penetration testing had been done, it would have been possible to safely show the exploit path and fix it.
Security penetration testing helps companies go from guesswork to proof.
Top 5 Reasons Why Your Business Needs Security Penetration Testing
A lot of businesses think that just putting in firewalls and antivirus software is enough. No, it isn't. Defensive tools are important, but they don't show that someone is strong. Security penetration testing is a way to test how well your defenses work.
It answers one important question: What would happen if someone tried to break in today?
A Summary of the Benefits
The main benefits are:
Finding weaknesses that really matter
Making cybersecurity programs stronger
Testing defenses in full
Helping with following the rules
Lowering the risk of long-term financial loss
Let's look at each one in detail.
Benefit 1: Finding Weaknesses
Vulnerability Assessment
A vulnerability assessment finds problems like old software, open ports, or settings that aren't secure. But not all vulnerabilities are equally dangerous.
Security penetration testing checks which findings can be used and how bad they really are. A missing patch may look like a big deal on paper, but segmentation controls might stop it from being used. On the other hand, a moderate finding could lead to administrative access if it is linked to another flaw.
Network Vulnerability Testing
When you perform network vulnerability testing, you look at routers, switches, firewalls, and services that run on your network. It finds:
Weak encryption methods
Default login information
Open management interfaces
Bad segmentation
When organizations combine vulnerability assessment with exploit validation, they get clear information instead of noise.
Benefit 2: Improving Cybersecurity Measures
Cybersecurity Assessment
A full cybersecurity assessment looks at policies, controls, and architecture. Security penetration testing adds to this by putting those controls to the test in real-world situations.
A red team penetration testing engagement can confirm a company's claim that it has strong endpoint detection capabilities.
Putting What You Learned into Security Protocols
Results of tests often lead to:
Better logging practices
Stronger incident response processes
Improved access control models
Hardened cloud configurations
Instead of using it as a checklist, mature organizations use the results to improve their ongoing security programs.
Benefit 3: All-Inclusive Testing Methods
Internal vs External Penetration Testing
External penetration testing looks at systems that are open to the public. It tells you if attackers can get in at first.
Internal penetration testing looks at what happens after someone gets in. Are attackers able to get to sensitive databases? Can they escalate privileges?
Both points of view are important.
Different Kinds of Tests
Red Team Penetration Testing
Simulates advanced adversaries. It focuses on stealth, persistence, and real-world tactics.
Social Engineering Penetration Testing
Tests human vulnerability. Phishing simulations, pretext phone calls, and physical access attempts evaluate employee awareness.
Cloud Penetration Testing
Looks at cloud configurations, IAM roles, exposed storage, and API security.
Mobile Application Penetration Testing
Examines insecure data storage, improper certificate validation, API misuse, and reverse engineering risks.
This layered approach makes sure that all digital environments are covered.
Benefit 4: Regulatory Compliance and Standards
The Importance of Compliance
A lot of businesses in the U.S. need to test their products on a regular basis. Some examples are:
PCI DSS for payment systems
HIPAA for healthcare organizations
SOC 2 for service organizations
Federal frameworks aligned with NIST guidelines
Compliance bodies often want proof that security penetration testing has been done.
How to Meet Standards
A formal security penetration test gives you:
Written proof of due diligence
Identified remediation steps
Risk prioritization
Compliance doesn't always mean safety, but it does mean accountability.
Benefit 5: Cost Effectiveness in the Long Run
Risk Management and Financial Impact
A breach can have a big financial impact, such as:
Incident response costs
Legal expenses
Regulatory fines
Business interruption
Reputation damage
It costs a lot less to do security penetration testing than to deal with a full-scale incident.
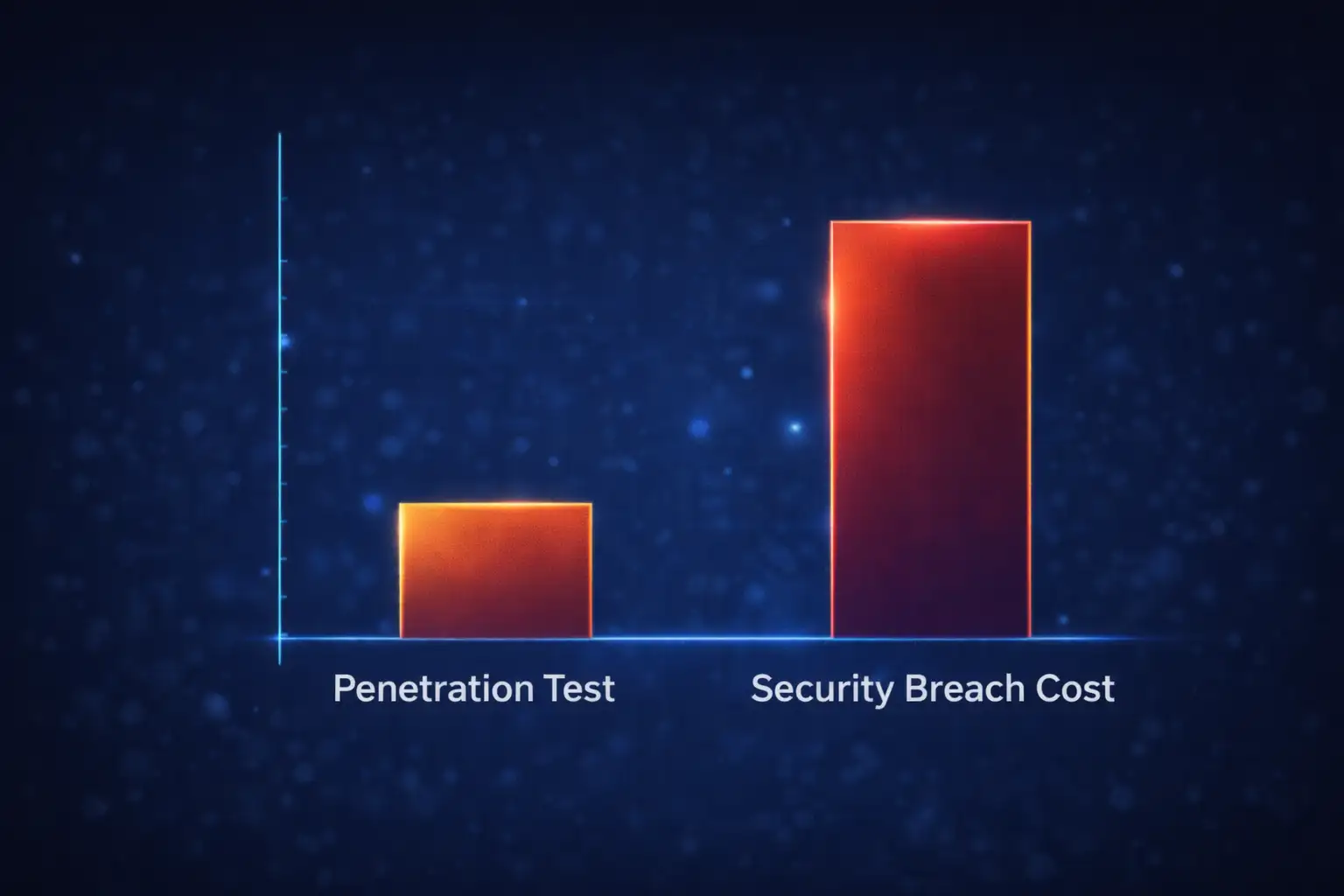
An Example of Saving Money
Think about a retailer that finds a flaw during web application security testing. It costs a few hours of development time to fix it.
If exploited publicly, that same flaw could expose payment information and start PCI investigations that cost millions.
Prevention isn't just a theory. It can be measured.
Things People Get Wrong
Penetration testing makes sure there is no breach.
No, it doesn't. It lowers risk, but no control can eliminate all risk.
Automated scans are all you need.
Automated tools cannot fully replicate human reasoning or chained exploits.
It's only for big businesses.
Small and medium-sized businesses are often targeted.
It is disruptive.
Professional engagements are carefully planned to limit operational impact.
What Organizations Should Do Right Now
Conduct a formal cybersecurity assessment
Set up regular internal penetration testing
Perform external penetration testing at least once a year
Include social engineering penetration testing when appropriate
Ensure remediation tracking
Security isn't something you do once. It is ongoing risk management.
Lessons for the Future
The future of security penetration testing includes:
Testing hybrid and multi-cloud environments
Evaluating AI-enabled applications
Continuous validation models
Instead of yearly events, organizations are moving toward ongoing validation. The main idea is still the same. Test before attackers do.
The Hoplon Insight Box
Expert Advice:
Combine vulnerability assessment with exploit validation
Prioritize findings based on business impact
Integrate results into your security strategy
Train staff alongside technical testing
Use both internal and external perspectives
Final thoughts
Fear is not a part of security penetration testing. It's about clarity. It turns assumptions into measurable insight. It provides real value by identifying weaknesses, strengthening defenses, supporting compliance, and reducing financial risk.
In today's connected world, investing in structured security penetration testing is a smart and responsible way for businesses to build resilience.
Frequently Asked Questions
How often should security penetration testing be done?
Most businesses do it once a year, but high-risk industries may do it more often or after major infrastructure changes.How do vulnerability assessment and penetration testing differ?
A vulnerability assessment identifies weaknesses. Security penetration testing validates whether those weaknesses can be exploited.How is cloud penetration testing different from regular testing?
Cloud penetration testing focuses on IAM policies, storage misconfigurations, and API security rather than physical hardware.Are phishing tests part of penetration testing?
Yes. Phishing simulations are part of social engineering penetration testing.What frameworks support penetration testing?
The OWASP Testing Guide and NIST SP 800 115 are widely recognized references.
Was this article helpful?
React to this post and see the live totals.
Share this :