Vercel Breach: Context.ai Hack Exposed Customer Data?
Hoplon InfoSec
20 Apr, 2026
What happened in the Vercel breach?
On April 19 to 20, 2026, Vercel disclosed that attackers accessed certain internal systems after a Context.ai compromise enabled takeover of an employee’s Google Workspace account, affecting a limited subset of customers and potentially exposing non-sensitive environment variables.
Vercel says attackers gained unauthorized access to certain internal systems after a compromise tied to Context. AI let them take over a Vercel employee’s Google Workspace account.
The company says a limited subset of customers had credentials compromised, and environment variables not marked as sensitive may also have been exposed.
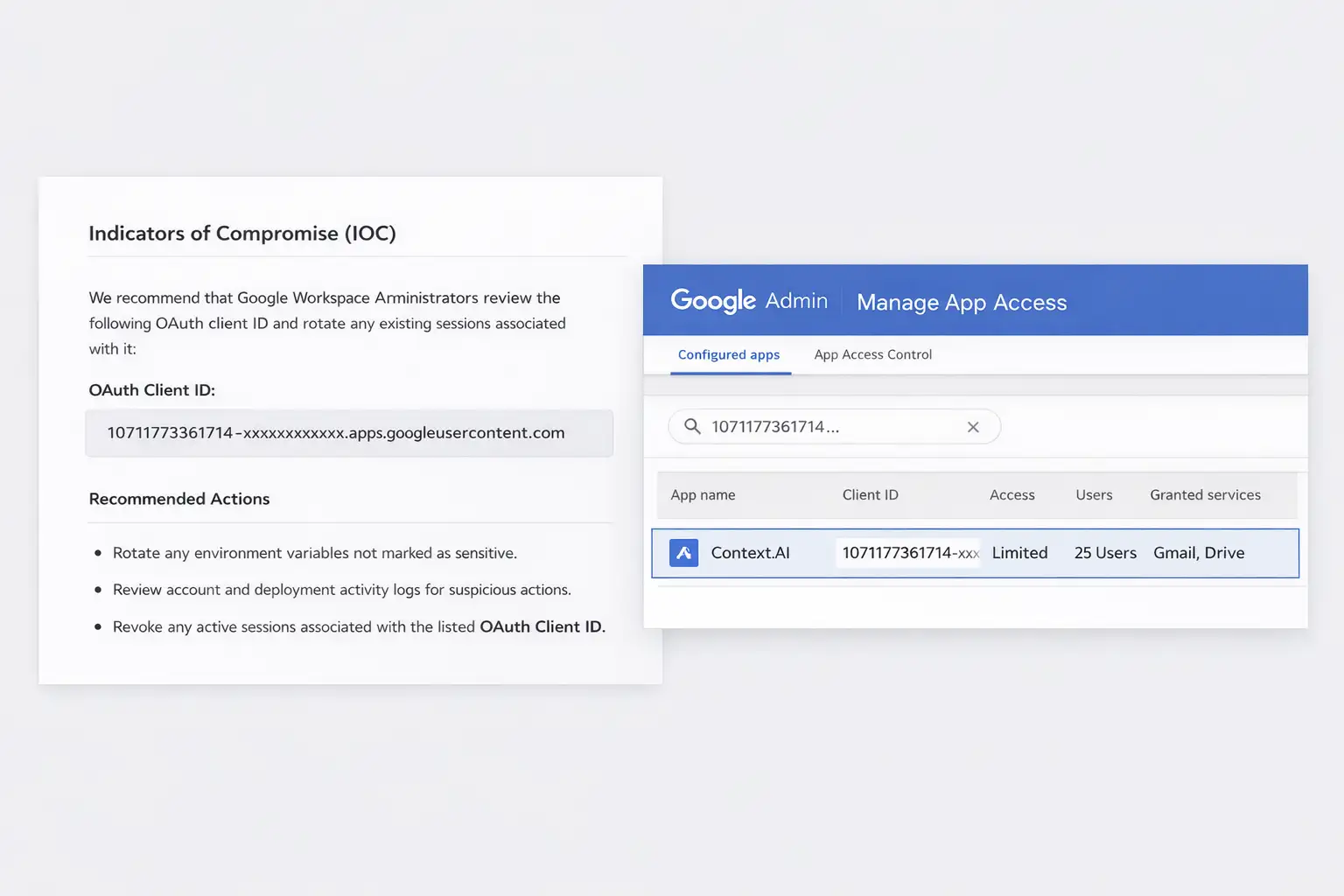
Vercel has published mitigation steps and an OAuth IOC for Google Workspace admins to review immediately.
This is not just another breach headline. It is a sharp example of how a trusted Software as a Service (SaaS) integration can become the bridge into engineering systems, secrets, and deployment workflows. That is why the Vercel breach matters beyond one vendor or one day of news coverage.
Key Takeaways
· The Vercel breach began with a compromise of Context.ai, a third-party AI tool used by a Vercel employee.
· Vercel says a limited subset of customers had credentials compromised.
· Environment variables marked sensitive are stored in a way that prevents them from being read, and Vercel says it has no evidence those values were accessed.
· Environment variables not marked sensitive should be treated as potentially exposed and rotated.
· Google Workspace admins should verify the published OAuth app IOC and review app access controls and OAuth grant activity.
Technical Overview
|
Item |
Current public detail |
|
Incident type |
Unauthorized access to certain internal Vercel systems |
|
Public disclosure |
April 19 to 20, 2026 |
|
Initial access path |
Context.ai compromise tied to a Vercel employee’s Google Workspace account |
|
Confirmed customer impact |
Limited subset of customers had credentials compromised |
|
Secret exposure concern |
Non-sensitive environment variables may have been accessible |
|
Sensitive vars status |
No evidence sensitive-marked values were accessed |
|
IOC published |
OAuth app client ID published for Google Workspace review |
|
CVE status |
Public incident bulletin, not a CVE advisory |
What is the Vercel Breach?
The Vercel breach became public through Vercel’s security bulletin, which states that attackers obtained unauthorized access to certain internal systems. The company updated that bulletin on April 19 and lists additional recommendations plus an IOC (Indicator of Compromise) for the wider Google Workspace community.
What Vercel officially confirmed matters. It did not say every customer was affected. It said a limited subset of customers had Vercel credentials compromised, and those customers were contacted directly.
It also said it continues to investigate whether data was exfiltrated and would notify users if more evidence appears.
That wording is important for readers searching “was Vercel hacked in 2026” or “did Vercel leak customer credentials.”
The answer is yes, there was a real security incident, but the company’s current public statement points to limited customer impact rather than a platform-wide exposure.
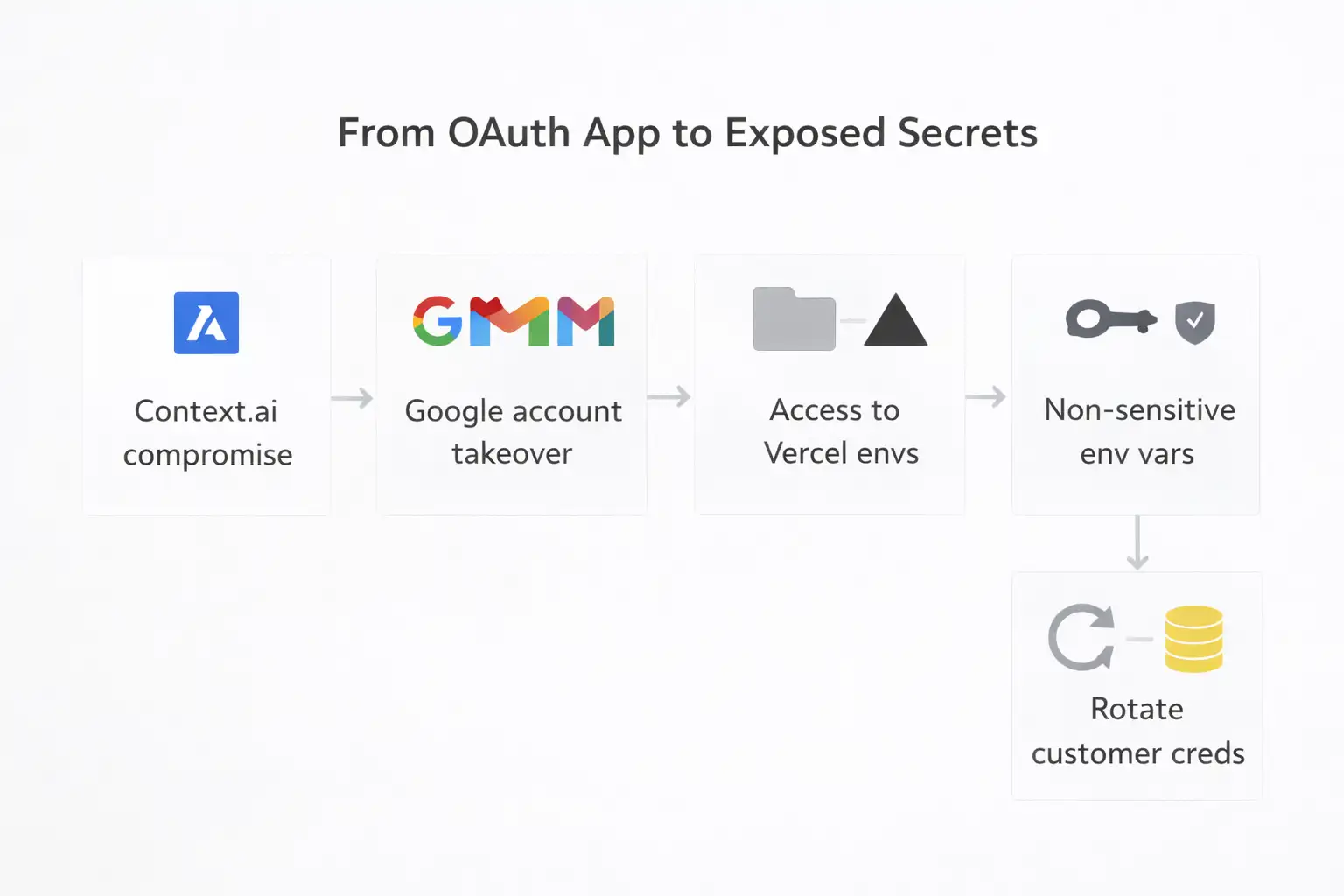
How the context. AI Hack Led to the Vercel Breach
This is where the story gets more useful. Vercel says the incident originated with a compromise of context. AI, a third-party AI tool used by an employee.
That access then enabled the takeover of the employee’s Vercel Google Workspace account. From there, the attacker gained access to some Vercel environments and environment variables that were not marked sensitive.
That sequence explains the Context AI hack angle better than most headlines do. The attacker did not necessarily need to smash through Vercel’s perimeter first.
A trusted OAuth (Open Authorization) relationship and an employee identity became the real pivot point. That is the kind of attack chain security teams worry about because it hides inside normal productivity tooling.
Google’s own admin documentation shows why this matters. Workspace admins can review accessed apps, see OAuth scopes, inspect app IDs, and change app access to trusted, limited, specific Google data, or blocked.
In other words, if a risky OAuth app is already in play, the controls exist, but only if teams know where to look and review them in time.
What Data Was Exposed in the Vercel Breach?
Publicly, the cleanest confirmed point is customer credentials. Vercel says a limited subset of customers had credentials compromised and were contacted. That is the part readers should treat as verified.
The second exposure category is more nuanced. Vercel says the attacker accessed some environments and environment variables that were not marked as sensitive.
This is why searches like “Vercel environment variables exposed” and “Vercel breach environment variables” match the actual story so well. The risk was not framed as a secret in every account. It was tied to non-sensitive-marked values.
What appears protected, at least from current evidence, are environment variables marked sensitive.
Vercel says those values are stored unreadably and that it has no evidence they were accessed. That is not the same as saying the incident was harmless. It means the blast radius may depend heavily on how disciplined teams were with secret classification before the breach, which could affect the extent of the data exposure and the potential risks to customers and their sensitive information.
Who is Affected by the Vercel Security Incident?
The first group is straightforward: customers Vercel directly contacted. According to the company, if you did not receive a notification, it currently has no reason to suspect a breach of your Vercel credentials or personal data. That line will reassure some teams, but it should not stop them from reviewing logs and rotating questionable secrets.
The second group is larger than the confirmed victim list. Teams that stored API keys, tokens, database credentials, signing passwords, or private endpoints in environment variables that were not marked sensitive should assume those values deserve review and likely rotation. That is exactly what Vercel recommends.
The third group includes crypto, SaaS, and API-heavy frontend projects. CoinDesk highlighted the pressure on crypto developers to lock down API keys, and that makes sense because frontend deployments often sit close to wallet connectors, RPC providers, analytics tokens, and trading backends. When secrets are mixed into app delivery pipelines, the cost of one bad assumption rises fast, leading to potential security breaches and financial losses for developers and companies involved in crypto, SaaS, and API-heavy frontend projects.
Vercel Breach Timeline
|
Date |
Event |
Why it matters |
|
April 19, 2026, 11:04 AM PST |
Vercel published an IOC |
This widened the response beyond Vercel customers to Google Workspace admins |
|
April 19, 2026, 6:01 PM PST |
Vercel added origin details and more recommendations |
This clarified the Context.ai and OAuth path |
|
April 20, 2026 |
Bulletin shows last updated date |
Confirms the incident remained active and under investigation |
Why This Breach Is Different From a Typical Data Leak
A lot of breach stories sound the same after a while. This one is different because the most important lesson is identity trust, not just infrastructure compromise. The attacker appears to have ridden a business-approved route into a business-critical system. That changes how defenders should think about “safe” tools.
The Google Workspace OAuth app compromise angle is the real warning sign. OAuth is supposed to limit password exposure. It does not remove risk.
It shifts risk into token grants, app trust, scope control, and app review discipline. Google’s own Workspace docs emphasize app access control, app ID review, scope inspection, and reporting on new OAuth grants. Those are not side settings anymore. They are frontline controls.
Our technical view is simple. The Vercel breach is not just about Vercel. It is about how engineering stacks now depend on chains of SaaS trust that most teams barely inventory. One weak OAuth approval can end up much closer to your deployment secrets than your board expects.
Immediate Actions Vercel Users Should Take
Check logs first.
Start with Vercel activity logs for both account and environment activity. Look for unexpected changes, new deployments, access anomalies, or edits around sensitive projects. Vercel specifically recommends reviewing activity logs in the dashboard or via CLI.
Rotate exposed secrets
Next, rotate any environment variable that contained secrets and was not marked sensitive. Prioritize API keys, tokens, database credentials, signing keys, webhook secrets, and private service endpoints.
This is the most important step in how to rotate secrets after Vercel breach searches because it cuts off reuse even if access already occurred.
Review deployments
Then investigate recent deployments for anything unexpected. If a deployment looks suspicious and you cannot explain it quickly, remove it. Vercel also recommends ensuring Deployment Protection is set to standard at minimum and rotating Deployment Protection tokens if configured.
Practical response order
1. Export a list of all environment variables by project
2. Flag any secret not marked sensitive.
3. Rotate by risk order, starting with production
4. Invalidate old tokens on the provider side
5. Review deployments and activity logs
6. Document what changed and when
That is the fastest useful answer to “how to protect Vercel credentials” after this incident.
Google Workspace Admin Checklist After the Context. AI Compromise
Google Workspace admins should begin with the published OAuth app client ID from Vercel’s IOC and check whether it appears in their environment.
Vercel explicitly recommends that Workspace administrators and Google Account owners check for use of that app immediately.
From there, go to Security > Access and data control > API controls > Manage App Access. Google’s admin documentation says this view lets you inspect accessed apps, app IDs, user counts, and requested services and scopes.
You can then change an app’s access status to trusted, limited, specific Google data, or blocked.
Also review the OAuth grants to new apps report in the Security Center dashboard. OAuth grants are permissions that allow applications to access user data on behalf of the user. Google says the report helps monitor new OAuth grant activity over a defined period. In a real incident, that matters because it narrows your review window and gives you a list of apps that appeared recently enough to deserve immediate attention.
Sensitive vs. Non-Sensitive Environment Variables on Vercel
This part deserves its own section because it changes the entire risk conversation. Vercel says environment variables marked sensitive are stored in a way that prevents them from being read. It also says it has no evidence those values were accessed in this incident.
That means the practical issue is not only the Vercel data breach 2026headline. It is secret hygiene.
Teams often rush through environment setup and leave important values in standard variables because it is quick and familiar, and nobody expects a breach this week. Then a story like this lands, and suddenly classification becomes the difference between a scary day and a severe incident.
If there is one operations lesson to keep, it is this: treat every token, API key, signing secret, and database credential as sensitive by default unless you can defend the opposite decision in writing.
What This Incident Reveals About AI Tool Security
Third-party AI tools now sit close to email, docs, chat, source code, deployment workflows, and user identity.
That makes them powerful. It also makes them dangerous when trust reviews are shallow, as this can lead to significant security vulnerabilities and potential misuse of sensitive information. The Context.ai Google Workspace breach angle is not an outlier. It is a preview of where identity abuse keeps going.
Convenience is the trap. Teams approve tools fast because the business case sounds harmless. Search my docs. Summarize my email.
Help me ship faster. Then one OAuth app becomes a route into systems no one originally pictured.
That is the context. AI hack explained: Search intent is really about more than one brand. It is about the gap between app approval and app oversight.
Users should refer to official advisories from Vercel and Google Workspace Admin Help for the live mitigation steps and control paths. Those are the authoritative sources for incident changes, app access control, and OAuth grant review.
Could the Vercel Breach Have Been Prevented?
Not with certainty. But the odds can be pushed in your favor. Restricted third-party app approvals, narrower OAuth scopes, better review of accessed apps, and stronger secret classification would all have reduced the likely blast radius here.
Google’s controls already support much of that if admins actually use them.
This incident is also a least-privilege story. If a third-party AI app can read far more than it truly needs, or if an employee identity sits too close to sensitive operational systems, one compromise can spread farther than expected.
The right question is not, “Could this exact incident have been stopped?” It says, “How many trust shortcuts are still sitting in our stack today?”
I am not claiming to have reproduced the attack chain behind the Vercel breach. No public reporting gives enough detail for that, and it would be irresponsible to pretend otherwise.
What we can say from an incident-response standpoint is that Vercel’s own mitigation order is sound: logs, secrets, deployments, protection controls, and then broader Workspace OAuth review.
That order tracks with how real teams contain identity-led cloud incidents. First you look for evidence of misuse. Then you eliminate the value of any information that may have been exposed.
Then you shut off easy repeat paths. It is boring work. It is also what keeps a limited incident from turning into a long one.
Security Checklist
|
Do this in 5 minutes |
Why |
|
Review Vercel activity logs |
Spot suspicious account or environment activity |
|
Rotate non-sensitive secrets first |
Cut off exposed API keys, tokens, and credentials |
|
Check the published OAuth app in Google Admin |
Confirm whether your Workspace was touched by the broader compromise |
Checklist basis: Vercel recommendations plus Google Workspace admin controls.
Trusted Source
For the core incident facts, use Vercel’s official April 2026 security bulletin as the primary source. For the outside news reference, one cybersecurity trade publication captured the incident scope and mitigation details clearly on April 20, 2026. (Vercel)
Recommendation:
· Treat every OAuth app as a privileged supplier, not a harmless productivity add-on.
· Mark secrets as sensitive by default, not later.
· Build a standing quarterly review for Google Workspace-accessed apps and new OAuth grants.
· If your frontend stack touches money, identity, or signing operations, assume secret rotation is part of normal incident hygiene, not an emergency exception.
Published: April 20, 2026
Last Updated: April 20, 2026
Author: Radia | Senior Cybersecurity Analyst & Breach Reporter.Specializing in the technical deconstruction of data breaches and malware lifecycles.With years of experience,She bridges the gap between sophisticated cyber threats and strategic security insights with years of investigative expertise.
Frequently Asked Questions
Was this article helpful?
React to this post and see the live totals.
Share this :