What Is Dark Web Monitoring? Complete 2026 Guide
-(1)_compressed-20260213173559.webp&w=3840&q=75)
Hoplon InfoSec
14 Feb, 2026
What is dark web monitoring, and why are security teams talking about it more than ever in 2026?
Dark web monitoring is the act of keeping an eye on stolen data, leaked passwords, and criminal conversations that take place in secret parts of the internet. The FBI and CISA say that compromised credentials are still one of the most common ways for hackers to get into systems. That means that every year, millions of people and thousands of businesses are affected.
If your email, password, API key, or customer database is posted on a dark web forum, hackers could use it to steal your account, hold you for ransom, or send you phishing emails. This is why security experts, IT leaders, students, and even regular people are asking more questions about how dark web monitoring works and if it really lowers risk.
This guide will tell you what it is, how it works technically, why it is important for modern cybersecurity, and how businesses can use it in a responsible way.
What is keeping an eye on the dark web?
A clear definition and context
In terms of real-world cybersecurity, what is dark web monitoring?
Dark web monitoring is a way to keep your information safe by looking for exposed credentials, personal data, or confidential business information on hidden online marketplaces, forums, encrypted chat channels, and leak sites. You can usually get to these hidden places through networks like Tor, which hide who you are when you use them.
We need to make something clear here. The dark web is not the whole internet. A small part of the deep web that needs special tools to get to. There are a lot of criminal marketplaces there because it's hard to catch criminals when they don't have to show their faces.
Dark web monitoring is necessary because stolen data is often sold, traded, or leaked to the public after a breach. Monitoring helps organizations find that exposure early.
Why the Dark Web Is There
The dark web was first made to keep people safe. Journalists, activists, and whistleblowers use networks that hide their identities to keep themselves safe. That part is real and has been written about by groups like the Electronic Frontier Foundation.
But cybercriminals also take advantage of the same anonymity. There are ads for stolen login information, remote desktop access, corporate VPN accounts, and even zero-day exploits.
Because of this situation, there was a need for organized dark web threat monitoring systems that keep defenders up to date.
How to Keep an Eye on the Dark Web
A Look at the Technology
To understand how dark web monitoring works, you need to look at both automation and human intelligence.
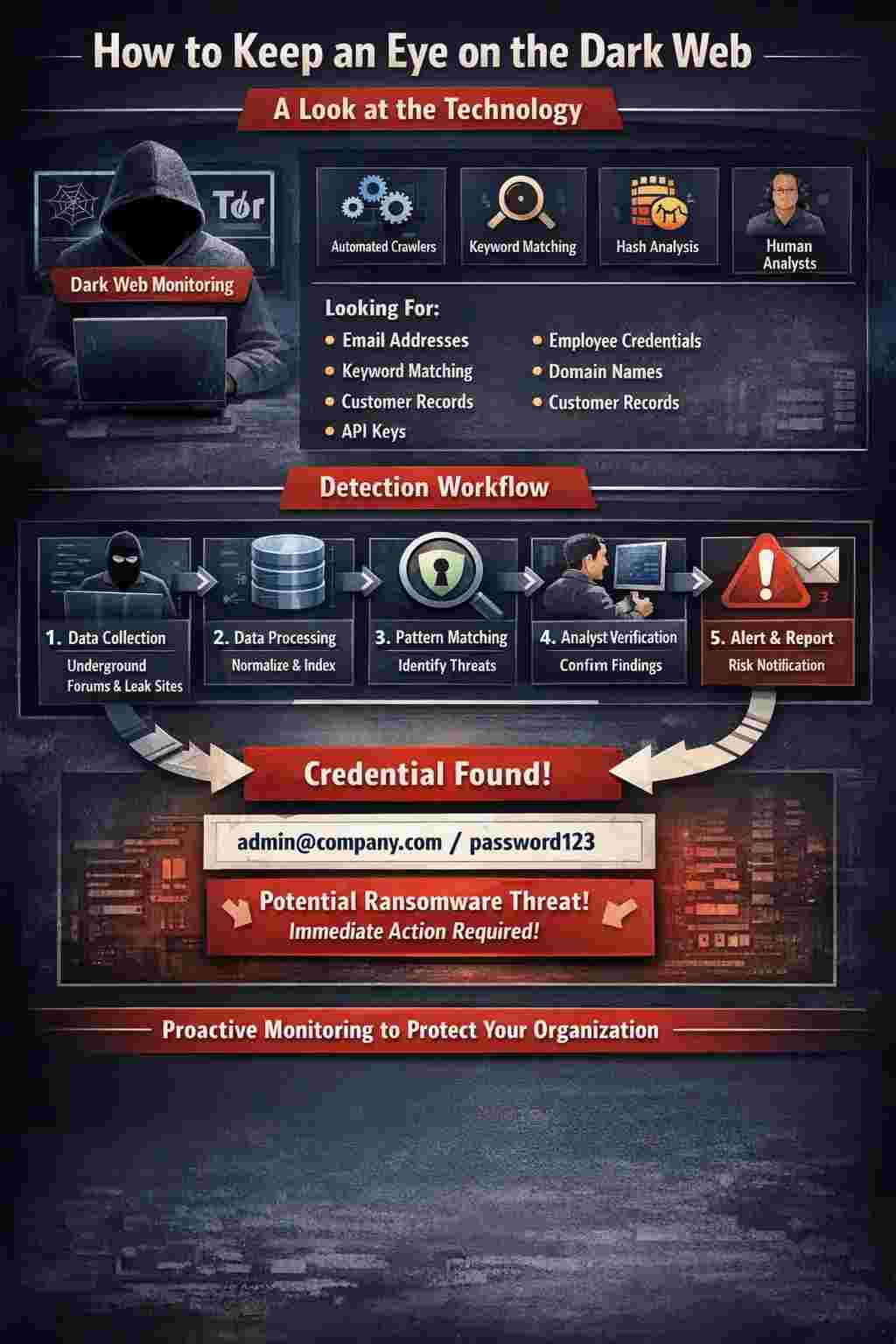
A lot of dark web monitoring services depend on:
• Automated crawlers set up to work with Tor and other similar networks
• Matching keywords with known domains, email patterns, and company names
• Hash comparison for databases of leaked passwords
• SIEM platforms that work with threat intelligence feeds
• People checking the context
Monitoring systems look for:
• Addresses for email
• Credentials of employees
• Names of domains
• Records of customers
• Keys for the API
• Numbers on credit cards
When a match is found, alerts are sent to security teams.
Architecture and Flow of Detection
This is what a simpler workflow looks like:
1. Data collectors go to underground forums and leak sites
2. The scraped data is put into a standard format and indexed.
3. Pattern matching finds identifiers that are unique to an organization.
4. Analysts check to make sure that the findings are real
5. Alerts come with information about the risks.
For instance, if a credential pair like admin@company.com shows up on a ransomware affiliate leak site, a monitoring platform might flag it within hours.
This proactive visibility is what sets dark web monitoring services apart from regular antivirus software.
What do dark web monitoring services really do?
A lot of companies want to know if dark web monitoring services are just alert systems or something more useful.
Most good providers will include:
• Constantly tracking credential exposure
• Services that keep an eye on data breaches at known leak sites
• Risk scoring for accounts that are open
• Short reports for compliance teams
• Working with incident response workflows
Some services also offer dark web features for individuals that protect against identity theft, like keeping an eye on Social Security numbers or other financial identifiers.
But keeping an eye on things doesn't stop a breach. It only finds out about exposure after it happens.
How to Use Dark Web Monitoring Tools and Software
When IT teams look at dark web monitoring tools, they often compare stand-alone platforms to threat intelligence systems that are built in.
Tools for keeping an eye on the dark web
These tools might give you:
• Scanning the whole domain
• Comparing hashes of credentials
• Scraping marketplaces
• Following Telegram and encrypted channels
SOC analysts who need raw intelligence feeds often use them.
Software for Monitoring the Dark Web
Most of the time, dark web monitoring software is more focused on businesses. It works with:
• Systems for SIEM
• SOAR platforms
• Tools for managing identities
• Systems for detecting endpoints
For instance, if someone finds stolen VPN credentials, automated workflows might force password resets right away.
This integration helps businesses that want to lower their risks in a measurable way by allowing them to monitor a wider range of the dark web.
What Makes Dark Web Monitoring Important in Cybersecurity?
The Real Threat Landscape
Why is it important to keep an eye on the dark web today?
This is because credential compromise is still one of the most common ways that attackers get into systems. The Verizon Data Breach Investigations Report always shows that stolen credentials are one of the main reasons for breaches.
Attackers buy real login information to get around security measures. Once they get in, they use ransomware, steal data, or move sideways.
Dark web threat monitoring lets you know ahead of time when attackers are going to use those credentials.
A Real Life Situation
Think of a healthcare provider that is in the middle. An employee uses a company password on a consumer site that has been hacked. That pair of credentials looks like it's for sale on a dark web market.
If no one is watching, attackers could buy it and try to use a VPN.
When monitoring is on, the security team gets an alert, forces a reset, and looks over access logs.
A small window. A big difference.
What kinds of information can you find on the dark web?
Security experts often discover:
• Login information that was stolen
• Data from a ransomware leak site
• Information that can be used to identify a person
• Records of money
• Intellectual property of a business
• Kits for exploiting
• Get to the broker listings
Some leak sites post full dumps of SQL databases. Some people post sample data to show that it is real.
You should be careful with any claim you see online that you can't confirm with reliable sources. This looks like false or misleading information, and there are no official sources that back it up.
Verification is very important.
-20260213182526.webp)
Businesses should keep an eye on the dark web
Reducing Business Risk
It's not just about stolen passwords when businesses keep an eye on the dark web. It also helps find:
• Compromises by the vendor
• Exposure to third parties
• Campaigns that pretend to be a brand
• Leaks of executive credentials
Industries that are regulated, like finance and healthcare, use monitoring to help them follow rules like HIPAA and PCI DSS.
Real-Life Incident Context
CISA and FBI alerts have documented several ransomware campaigns in which initial access was gained through exposed credentials or access broker sales.
The pattern stays the same, even though the specific credentials change from case to case. Underground markets sell stolen login information for money.
Dark web monitoring helps find these weaknesses before attackers can fully use them.
What Businesses Should Do Now
1. Use multiple factors of authentication everywhere
2. Don't use the same password twice.
3. Use tools to help you remember your passwords
4. Add alerts for monitoring to SOC workflows
5. Check access on a regular basis
Monitoring without a plan for how to respond is not very useful.
Lessons for the future and for a wider audience
Cybercrime markets are becoming more structured. Access brokers are experts at selling ways to get in. Ransomware groups hire other people to get in at first.
Stolen information will keep going around as long as data breaches happen.
Monitoring the dark web is still a way to see things, not a way to fix them. The real defense is a mix of monitoring, strong identity management, and the idea of "zero trust."
Hoplon Infosec's cybersecurity services offer expert advice
• Use alerts from the dark web to start incident response
• Change the passwords on accounts that have been hacked automatically
• Put monitoring executive and admin credentials at the top of your list of things to do
• Use threat intelligence feeds from the dark web and keep an eye on things
• Do tabletop exercises based on situations where credentials get out
-20260213173650.webp)
Last Thoughts
So, where does monitoring the dark web fit into the bigger picture of keeping computers safe?
It is an early warning system that helps businesses find stolen passwords, leaked databases, and criminals talking about their assets. It doesn't stop breaches from happening, but it makes them less likely to happen and makes it easier to deal with them.
People who work in security, students, and people who make decisions need to know how dark web monitoring works because stolen data can spread quickly.
It's easy to get the main point. Resilience comes from seeing things and doing things.
Questions that are often asked
1. Is it legal to watch the dark web?
Yes, but only when done through legitimate providers that look at publicly available criminal forums without getting in without permission.
2. Can people use dark web monitoring?
Yes. Many services send alerts to personal email addresses and financial identifiers when they find identity theft on the dark web.
3. How often should companies check for dark web alerts?
Through SOC integration, it would be best to do it in real time. At the very least, you should look over it every day.
4. Does monitoring get rid of stolen data?
No. It finds out if someone is exposed. Taking something down or getting rid of it often requires police or other legal processes.
5. Which fields need it the most?
Companies in healthcare, finance, e-commerce, and SaaS that have a lot of user data.
Was this article helpful?
React to this post and see the live totals.
Share this :