Windows Zero-Day Exploit Code Leak Raises Full Access Risk
-20260407064803.webp&w=3840&q=75)
Hoplon InfoSec
07 Apr, 2026
Windows Zero-Day Exploit Code Leak Raises New Full Access Fears for Windows Users
On April 6, 2026, public reporting said exploit code for an unpatched Windows privilege-escalation flaw called BlueHammer was released online, raising fears that attackers with local access could jump to SYSTEM or elevated administrator permissions on affected machines.
If you have been seeing headlines about a Windows zero-day exploit, the big question is simple: did someone really publish code that could help attackers take over a Windows system? Based on current public reporting, yes, that is the concern.
The flaw, referred to publicly as BlueHammer Windows zero-day, was described as an unpatched Windows privilege-escalation issue, and the reported risk is serious because it could allow an attacker with local access to move up to SYSTEM or elevated administrator rights.
That detail matters more than the drama around the leak. A lot of security stories flare up for a day and disappear. This one landed differently because the claim was not just about a bug. It was about working exploit code showing up while the issue still appeared to be unpatched.
In security terms, that is exactly the kind of moment that makes defenders sit up straight, cancel a quiet afternoon, and start checking endpoints.
What happened
Public reporting says exploit code was released for an unpatched Windows vulnerability that had been privately reported to Microsoft. The coverage says the issue could let attackers gain SYSTEM or elevated administrator permissions, which is why this quickly became one of the more alarming Windows security stories of the week.
The researcher behind the public release reportedly published the code under the BlueHammer name after expressing frustration with Microsoft’s handling of the disclosure process.
There is a reason this caught so much attention so quickly. A bug alone is one thing. A bug plus public code is something else. Once code is out in the open, even if it is rough around the edges, the timeline changes. Defenders have less breathing room. Threat actors do not need to discover the weakness from scratch. They can simply start testing, adapting, and looking for the easiest route into real environments.
That is why people searching for Windows exploit code released or researcher released Windows exploit code are usually not just after gossip. They want to know whether this is another forgettable proof of concept, or the kind of security event that forces immediate hardening and monitoring. Right now, the safer reading is the second one.
Why this is being treated as a zero-day
Microsoft’s own documentation defines a zero-day as a software flaw for which no official patch or security update is available yet. Its guidance also notes that zero-days often carry high severity and are actively exploited.
That definition is important here because it cuts through the noise and keeps the discussion grounded. If there is no official fix yet, the term zero-day is not just headline decoration. It has a clear meaning.
So when people describe this as a Windows zero day vulnerability or a Microsoft zero-day exploit, they are pointing to the same core problem: a known weakness, no official patch at the moment, and public exploit code circulating before defenders can rely on a clean patch cycle. That combination is where the risk comes from.
One subtle but important point: Microsoft’s documentation also says some zero-days may appear under temporary internal names before a CVE is assigned. At the time of writing, I could not verify a public CVE specifically tied to BlueHammer. That does not make the issue less real. It just means some of the labeling may still be catching up with the reporting.
Is this really a Defender issue, or a wider Windows problem?
Search traffic is already mixing together “Windows Defender,” “Microsoft Defender,” and Windows itself. That is understandable. Most users recognize the Defender brand first because it is the visible security layer they interact with.
But the strongest public reporting around this incident describes it as a Windows privilege-escalation flaw, not a simple antivirus detection miss or a basic Defender signature issue.
That is why the more accurate framing for readers is broader. This appears to be a Windows privilege escalation exploit with major implications for endpoint defense.
You can still cover Microsoft Defender zero-day as a supporting search phrase, because readers are using it, but the real story is about privilege escalation on Windows and what happens after an attacker gets a foothold.
That distinction is worth making clearly. If a reader thinks this is only about consumer antivirus settings, they miss the bigger problem. A Windows local privilege escalation flaw is dangerous because it sits deeper in the chain. It can turn a limited compromise into a far more serious one.
BlueHammer exploit explained
Here is the simplest version of BlueHammer exploit explained without turning the article into a lab manual. This appears to be a local privilege-escalation issue. In plain language, that means an attacker would usually need some kind of access on the machine first. They might already have a low-privilege account, a foothold through malware, or code execution gained another way. The exploit then helps them climb from limited permissions to a much more powerful level.
Public reporting says the technique combines a time-of-check, time-of-use issue with path confusion. Those phrases sound technical, but the core idea is easier to picture than it sounds.
Imagine a security guard checks the label on a box at the door, then someone swaps the destination before it reaches a restricted room. The system made a check, but not at the moment that really counted. That kind of gap is exactly the sort of thing attackers love.
This is why so many people are searching how BlueHammer works. They are trying to understand whether the exploit is just theoretical or whether it could fit into real attacks. And that is the uncomfortable part. Privilege escalation bugs often become highly valuable after the first compromise, not before it.
Why SYSTEM access changes the story
The phrase SYSTEM privilege exploit Windows may sound abstract to everyday readers, but in practice it means near-total control over the affected machine. Once an attacker reaches SYSTEM, the problem is no longer just suspicious activity or a low-level intrusion. At that point, the host may no longer be trustworthy in any practical sense.
That is where the phrase Windows zero-day full access exploit starts to make sense. Full access is not just a dramatic headline line.
It can mean disabling security tooling, planting persistence, tampering with settings, stealing credentials, or preparing for movement into other systems. It is the difference between someone sneaking into the lobby and someone walking away with the building master key.
And that is why this story matters even though it is described as a local issue. Local privilege escalation is often the second step in a real intrusion. The first step might be phishing, a malicious download, stolen credentials, or another vulnerability. The second step is where a small incident starts becoming a full-scale response problem.
Who is most exposed to this kind of risk
The users most exposed are usually not random home users browsing on a Sunday afternoon. The bigger concern is organizations with lots of Windows endpoints, mixed privilege policies, and enough complexity that a compromised device can hide for a while before someone notices. Enterprises, schools, hospitals, managed service providers, and heavily distributed workforces all fit that pattern.
That does not mean home users can ignore the story. It just means the threat model is a little different. A Windows security flaw exploit code leak matters most when attackers already have a path onto the device.
If the initial barrier is low, the escalation step becomes more valuable. If the initial barrier is harder, the same exploit still matters, but fewer attackers can make use of it easily.
So when readers ask, can attackers gain SYSTEM access on Windows, the most accurate answer is this: potentially yes, based on current public reporting, but this appears to be a local privilege-escalation scenario, which means some initial foothold is usually part of the chain.
Why public exploit code makes defenders nervous
Security teams see vulnerability disclosures all the time. Most of them are important, but manageable. What changes the mood is public code.
Once a Windows zero-day exploit code released headline is attached to an issue, the sense of urgency shifts from “watch this” to “assume someone is already testing this.” That is not fearmongering. It is how security operations tends to work in the real world.
The public reporting around BlueHammer says the researcher released the exploit after being dissatisfied with how the issue was handled.
That broader disclosure tension is not new. Vendors want time to fix. Researchers often want urgency and acknowledgment. Somewhere in the middle, defenders are trying to protect real machines while the process plays out.
The result is uncomfortable but familiar. A single disclosure dispute can suddenly become a global endpoint hardening problem. That is one reason stories like this keep drawing attention far beyond the security community.
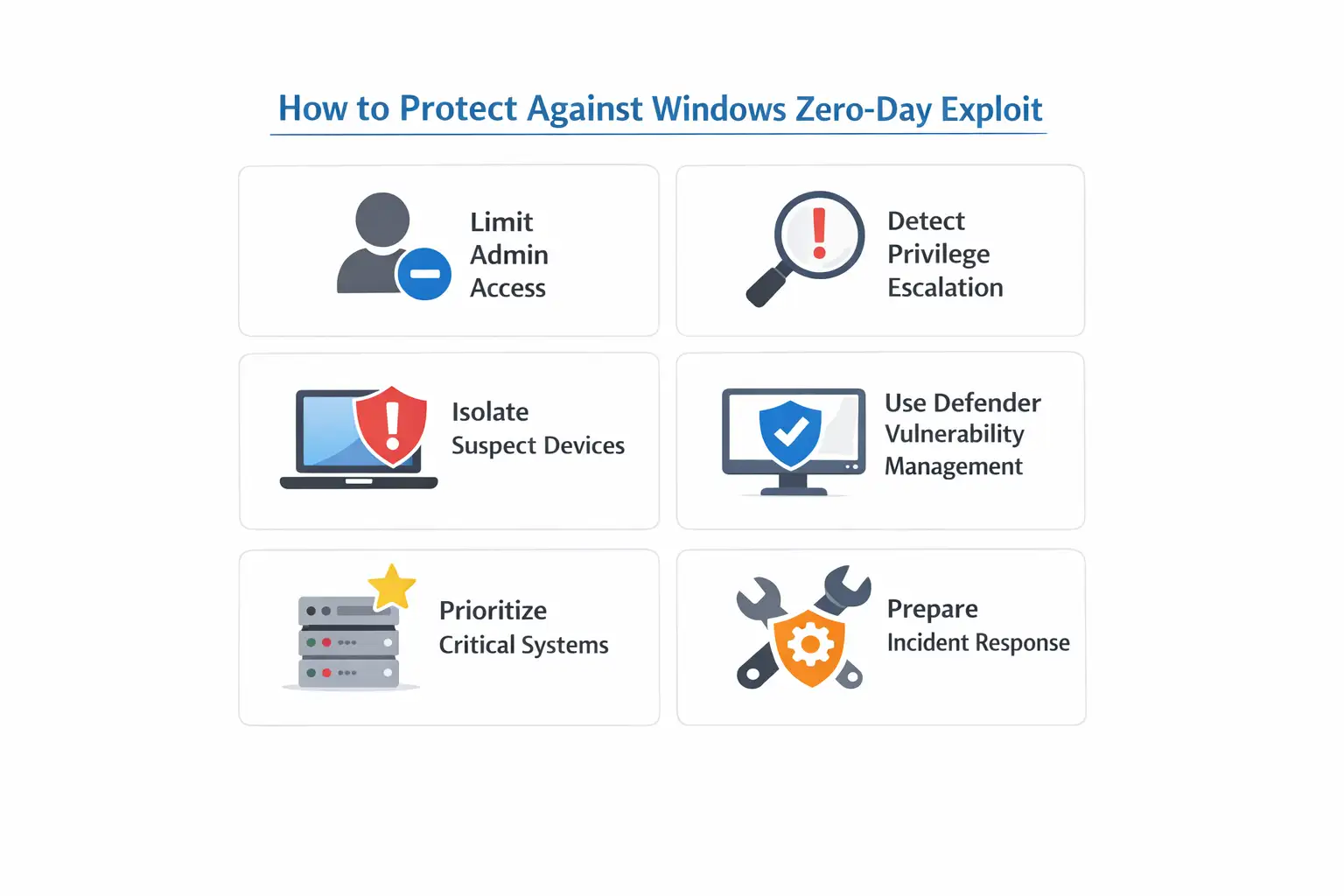
How to protect against Windows zero-day exploit activity
This is the part readers care about most, and honestly, the part that matters most. If you are asking how to protect against Windows zero-day exploit risk before a patch is widely available, the first move is not magic.
It is discipline. Reduce unnecessary local admin access. Monitor for suspicious privilege changes. Isolate suspect devices fast. Make sure endpoint security and response tooling is actually surfacing the events you care about.
Microsoft’s documentation says Defender Vulnerability Management can help identify zero-days in the Microsoft Defender portal by showing Zero day tags in recommendations, software views, and vulnerability pages.
It also says the platform can display mitigation options and workarounds if available, even before a patch arrives. That kind of visibility matters when the normal patch-and-move-on cycle is not possible yet.
There is also a practical reason to involve Microsoft Defender tooling here, even if the flaw itself is not best framed as a simple Defender bug.
Defender Vulnerability Management is designed to prioritize risk using threat intelligence, device context, and remediation guidance.
That makes it useful during exactly this kind of messy window, where the issue is known, the fix may not be ready, and defenders need to decide what deserves immediate attention.
Immediate steps security teams should take
- Review who actually has local admin rights and cut back where possible.
- Hunt for unusual privilege-escalation activity or tampering with services and protections.
- Isolate suspicious Windows hosts quickly if there are signs of compromise.
- Use Defender Vulnerability Management to look for zero-day tags, recommendations, and remediation guidance.
- Prioritize high-value endpoints first, especially machines used by administrators and IT staff.
- Prepare for deeper incident response if SYSTEM-level compromise is confirmed, including credential resets and host rebuild decisions.
That might sound basic, but basic done consistently beats flashy done late. A lot of severe incidents are made worse not by the first missed alert, but by the second and third delays afterward.
Why this matters beyond one week of headlines
A story like this is bigger than a single exploit repo. It highlights a recurring weakness in modern security operations. Too many organizations still rely on the patch cycle as if patching alone is the whole strategy. It is not.
When the patch is not there yet, your real posture is exposed. Identity controls, least privilege, segmentation, visibility, response speed, and host hardening suddenly matter a lot more.
That is where the Microsoft zero-day exploit angle becomes more useful than the headline drama. The real lesson is not just that a flaw may exist. The real lesson is what your environment looks like when a flaw exists before a clean fix is available. Some teams discover they have good visibility. Others discover they have too many unmanaged devices, too many privileged users, and too little certainty about what is happening on endpoints.
A strong Windows zero-day exploit article should tell readers that plainly. The incident itself is important. The posture it exposes is even more important.
What readers are asking right now
Is this a Microsoft Defender zero-day or a Windows issue?
Current public reporting points more strongly to a Windows privilege-escalation issue than to a simple Defender product bug. Defender is still relevant because Microsoft’s security platform can help with visibility and mitigation.
Is this a Windows local privilege escalation problem?
Yes, that is how the issue is being described in current reporting. The reported risk is that an attacker with local access could elevate to SYSTEM or administrator-level privileges.
Why are people calling it a Windows security flaw exploit code leak?
Because the reporting says code tied to the flaw was published publicly before an official patch was available, which raises the chance of copycat or adapted attacks.
Is this the same as every other Windows privilege escalation exploit?
No. Privilege escalation is a broad category. What made this case stand out is the combination of an unpatched state, public code, and the reported ability to reach SYSTEM or elevated admin permissions.
What makes this incident serious
|
Risk area |
Why it matters |
|
Public code availability |
Shortens the time between disclosure and abuse |
|
No verified patch at disclosure |
Keeps the issue in zero-day territory |
|
Privilege escalation path |
Can turn a low-level compromise into a high-level one |
|
SYSTEM-level outcome |
Raises the chance of deep host compromise |
|
Enterprise exposure |
Increases the burden on SOC, IT, and incident response teams |
The table may look simple, but that is the whole story in compact form. A bug is manageable. A bug with public code and no confirmed patch is a much harder day at the office.
Hoplon Insight Box
If your team is handling Windows security right now, the smart move is to treat this as a post-compromise escalation risk, not just a headline risk.
Focus on three things first: tighter privilege control, faster endpoint isolation, and better visibility inside Microsoft Defender.
If Microsoft later publishes a formal fix, move it high in your emergency patching queue and validate the rollout instead of assuming the problem is automatically closed.
Final takeaway
The story around Windows zero-day exploit coverage is not just that code appeared online. It is that the reported flaw sits in one of the worst possible places for defenders: the moment after an attacker gets in, but before defenders can rely on a patch.
That is what makes BlueHammer Windows zero-day more than another passing headline. It speaks directly to how fragile many Windows environments become once least privilege and endpoint visibility start slipping.
For now, the most honest conclusion is also the most practical one. Treat the issue seriously. Watch Microsoft channels for updates.
Reduce local privilege where you can. Monitor endpoints more aggressively than usual. And if you are wondering whether a Windows zero-day exploit can still matter even before mass exploitation is confirmed, the answer is yes. Public code alone is enough to change the defensive timetable.
FAQ
What is BlueHammer Windows zero-day?
It is the public name used in reporting for an unpatched Windows privilege-escalation flaw whose exploit code was reportedly released online in early April 2026. The reported impact is escalation to SYSTEM or elevated administrator permissions.
Is there a confirmed patch for this Windows zero day vulnerability?
At the time of writing, I could not verify an official Microsoft patch specifically for BlueHammer. Microsoft says zero-days remain zero-days until a patch or security update is released.
Could this SYSTEM privilege exploit Windows issue affect enterprises more than home users?
Yes, because enterprise environments often give attackers more ways to turn a local foothold into a wider incident, especially where privilege controls and endpoint visibility are weak. This is an informed risk assessment based on how privilege-escalation issues are typically used after initial compromise.
What is the best response to a Windows exploit code released event like this?
The best early response is tighter privilege control, faster triage of suspicious endpoints, and use of Microsoft Defender Vulnerability Management to identify zero-day recommendations, workarounds, and high-risk assets.
You can also read these important cybersecurity news articles on our website.
· Apple Update,
For more, please visit our homepage and follow us on X (Twitter) and LinkedIn for more cybersecurity news and updates. Stay connected on YouTube, Facebook, and Instagram as well.
Windows Zero-Day Exploit
Was this article helpful?
React to this post and see the live totals.
Share this :
-20260407064803.webp)