Cybersecurity News Roundup: Chrome, Linux, vm2, Crypto Risks

Hoplon InfoSec
08 May, 2026
Cybersecurity Weekly Recap: Chrome 148 Fixes 127 Bugs, Linux Copy Fail Hits Servers, and Crypto Scam Centers Face Global Crackdown
What happened this week in cybersecurity?
Cybersecurity News Roundup, May 8, 2026: This week was heavy on browser fixes, Linux server risk, developer tool vulnerabilities, supply chain compromise, and crypto fraud enforcement.
Google promoted Chrome 148 to stable and said it includes 127 security fixes. CISA and NVD confirmed that CVE-2026-31431, also known as Copy Fail, is in the Known Exploited Vulnerabilities catalog.
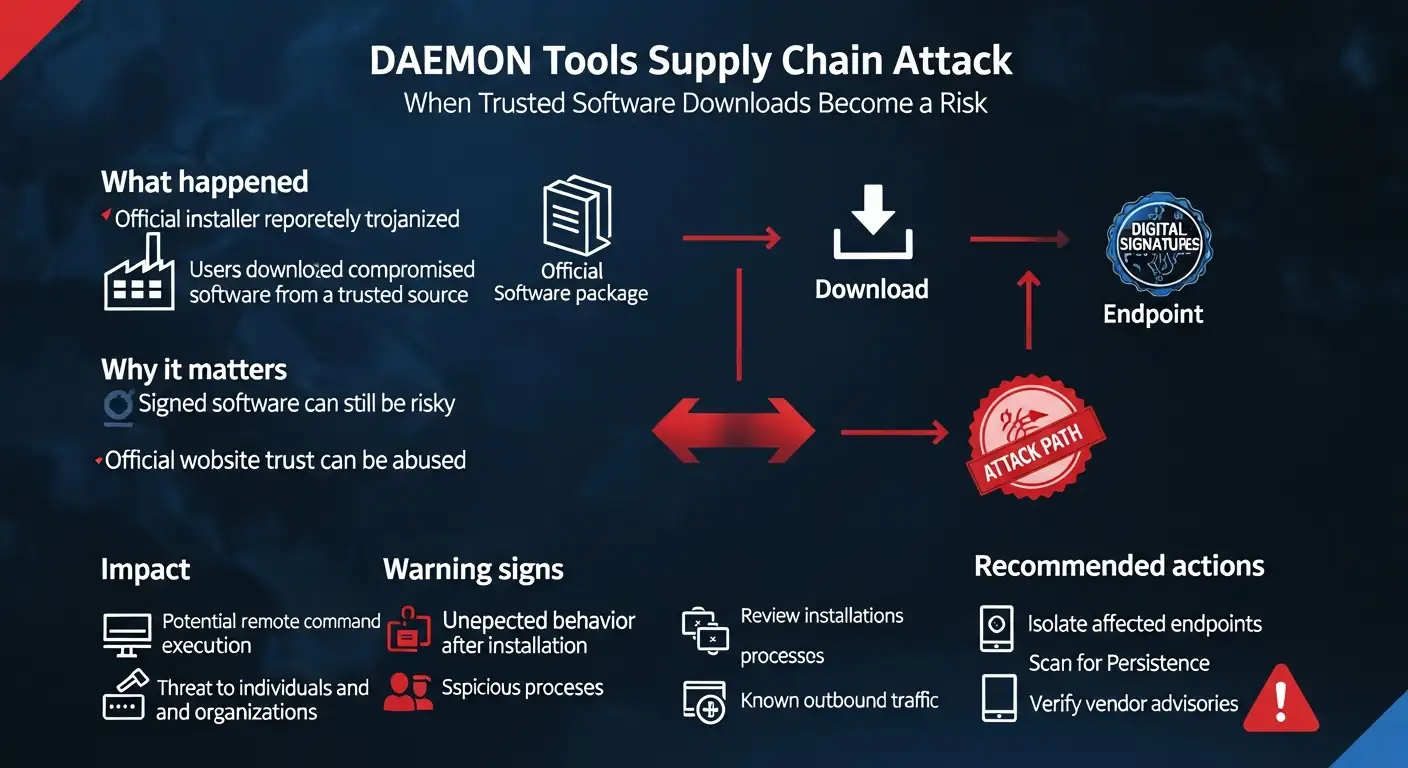
Meanwhile, Kaspersky reported an active DAEMON Tools supply chain attack, and the U.S. Justice Department announced at least 276 arrests tied to crypto investment scam centers.
This cybersecurity weekly recap matters because these stories are not isolated. They all point to the same uncomfortable truth: attackers are abusing trusted software, old assumptions, weak identity controls, and delayed patching. That affects regular browser users, Linux admins, developers, enterprises, and crypto investors at the same time.
Why this cybersecurity weekly recap is different this week
Some weeks in security feel like a list of random bugs. This one does not. The pattern is clearer.
Chrome users need updates because browser flaws can turn a simple web session into a risk. Linux teams need to patch because a local foothold can become root access. Developers using vm2 need to rethink how much trust they put in JavaScript sandboxing.
DAEMON Tools users need to check whether a trusted installer became a backdoor. And crypto users need to remember that fraud today often starts with a friendly message, not a scary pop-up.
That is why this cybersecurity weekly recap focuses on impact, not only headlines. A vulnerability is not just a CVE number. A supply chain attack is not just malware. A scam takedown is not just an arrest count. Each one shows where people and companies still leave doors open.
Top 5 security stories at a glance
|
Topic |
What happened |
Who is affected |
Action priority |
|
Chrome 148 |
Stable release includes 127 security fixes |
Windows, macOS, Linux, Android users |
High |
|
vm2 sandbox escape |
Multiple critical flaws allow sandbox escape and code execution |
Node.js apps running untrusted code |
Critical |
|
DAEMON Tools attack |
Official installers were trojanized |
Windows users and organizations using DAEMON Tools |
Critical |
|
Copy Fail Linux CVE |
Local privilege escalation can lead to root |
Linux servers, cloud workloads, Kubernetes environments |
Critical |
|
Crypto scam crackdown |
276 arrests and nine scam centers dismantled |
Crypto investors and fraud victims |
Awareness plus reporting |
1. Google Chrome 148 fixes 127 security issues
Google’s official Chrome Releases blog confirmed on May 5, 2026 that Chrome 148 was promoted to the stable channel for Windows, Mac, and Linux.
The release includes 127 security fixes, including critical issues such as CVE-2026-7896, an integer overflow in Blink, and CVE-2026-7897, a use-after-free issue in Mobile. Android Chrome 148 also carries the same security fixes as the corresponding desktop releases unless otherwise noted.
For normal users, the advice is simple: update Chrome and restart the browser. The restart matters. Many people leave Chrome open for days, sometimes weeks, assuming automatic updates are already protecting them. In reality, the new version usually needs a relaunch before the patched code is active.
For businesses, this cybersecurity weekly recap should be treated as a reminder to check browser fleet management. Chrome is often treated like a simple productivity tool, but it is also one of the most exposed applications on any endpoint. Employees open emails, dashboards, SaaS apps, file previews, and unknown links inside it all day.
What users should do now
Check Chrome’s version from Settings > About Chrome. Let it update, then restart. Enterprise teams should verify update status through endpoint management tools, especially for remote devices that may not check in every day.
A useful visual for this section would be a screenshot of Chrome’s “About Chrome” update page showing the installed version. It is simple, helpful, and directly tells readers what to check.

2.
vm2 sandbox escape shows the risk of running untrusted JavaScript
The vm2 Node.js library had a rough week. Reports disclosed multiple critical vulnerabilities that can let attacker-controlled JavaScript escape the sandbox and execute code on the host system. The listed flaws include CVEs such as CVE-2026-24118, CVE-2026-43997, CVE-2026-44005, CVE-2026-44008, and CVE-2026-44009, with several carrying CVSS scores near or at critical severity. Users were advised to update to version 3.11.2.
The core issue is easy to explain with a real-world analogy. A sandbox is supposed to be like a glass room where unknown code can move around but cannot touch the building outside. A sandbox escape means the glass was not really sealed. Once code escapes, it may reach the host machine, file system, environment variables, secrets, or command execution paths.
BleepingComputer also reported a separate vm2 flaw, CVE-2026-26956, affecting vm2 3.10.4, where proof-of-concept code was published and users were advised to upgrade to 3.10.5 or later, with 3.11.2 being the latest version at the time of reporting.
This cybersecurity weekly recap should make developers pause. If your platform runs user-submitted code, automation scripts, plug-ins, workflow logic, or AI-generated snippets inside vm2, patching is only the first step. You also need isolation outside the JavaScript process, such as containers, seccomp profiles, locked-down runtime permissions, resource limits, and separate credentials.
3. DAEMON Tools supply chain attack hits trusted downloads
The DAEMON Tools story is one of the most serious items in this cybersecurity weekly recap because it involves trust. Kaspersky reported that attackers compromised the official DAEMON Tools website and distributed modified installers directly through the vendor’s domain beginning April 8, 2026.
The trojanized software was signed with a valid developer certificate and affected DAEMON Tools versions 12.5.0.2421 through the current release at the time of Kaspersky’s notice.
That is the scary part. Users did not download a random crack from a shady forum. They downloaded software from the official source. In security, that changes the whole story. Traditional advice like “only download from the official website” is still good, but this case shows it is not enough by itself.
Kaspersky said the compromised installer could deliver malicious software alongside the legitimate app, allowing attackers to execute arbitrary commands and remotely control infected devices. Researchers also observed wider distribution across more than 100 countries, with a smaller subset of organizations receiving additional payloads.
A Kaspersky researcher summed up the problem well: users “implicitly trust digitally signed software downloaded directly from an official vendor.” That is exactly why supply chain attacks work.
What organizations should check
Organizations should identify any endpoints with DAEMON Tools installed, especially installations or updates after April 8, 2026. Kaspersky recommended isolating affected endpoints, auditing for unusual activity, monitoring unauthorized command execution, and running security sweeps for persistence or lateral movement.
This is also a good time to review software allowlisting. A signed installer is not automatically safe forever. Security teams need telemetry, hash checks, vendor advisories, and behavior monitoring.
4. Linux Copy Fail, CVE-2026-31431, becomes an urgent server issue
The Linux Copy Fail vulnerability, tracked as CVE-2026-31431, is another major story. NVD shows the CVE is in CISA’s Known Exploited Vulnerabilities catalog, with a May 1, 2026 addition date and a May 15, 2026 due date for required action under applicable federal guidance.
Microsoft Defender researchers described CVE-2026-31431 as a high-severity local privilege escalation vulnerability affecting multiple major Linux distributions, including Red Hat, SUSE, Ubuntu, and AWS Linux. The vulnerability can let an unprivileged local user escalate to root. Microsoft also noted concern for cloud Linux workloads and Kubernetes clusters.
Here is the plain-language version. Copy Fail is not a remote “click this link and get hacked” bug by itself. The attacker usually needs some local access first, such as a low-privilege account, a compromised container, a malicious CI job, or a foothold gained another way. But once inside, this bug may help them become root. That is why it is dangerous in cloud and shared environments.
This cybersecurity weekly recap should push Linux admins to prioritize kernel patching. Local privilege escalation bugs are often used after the first breach. Attackers do not always need to break the front door if they can slip in through a small account and climb from there.
Mitigation checklist for Copy Fail
Patch affected Linux kernels as soon as vendor updates are available. Where patches are not ready, follow vendor mitigation guidance, restrict local code execution, review container isolation, and monitor for suspicious privilege escalation behavior. Microsoft recommended immediate identification of affected instances and mitigation based on patch availability.
|
Environment |
Risk level |
Why |
|
Internet-facing Linux server with many users |
High |
Local footholds can become root |
|
Kubernetes cluster running untrusted workloads |
High |
Container foothold may increase blast radius |
|
Single-user desktop Linux system |
Medium |
Needs local access first |
|
Fully patched Linux fleet |
Low |
Risk reduced after verified patching |
5. Microsoft Edge password concern needs careful wording
The Microsoft Edge password story is important, but it needs a neutral tone. Several reports said a researcher found that Edge may load saved passwords into process memory in cleartext at startup.
Microsoft’s official Edge security release notes for May 7, 2026 confirm Edge Stable version 148.0.3967.54 and list several Edge-specific CVEs, but those notes do not describe this reported password-memory behavior as a patched CVE.
So the correct wording is this: the Edge password issue appears to be a researcher-reported design-risk claim, not a confirmed emergency CVE patch in Microsoft’s public release notes at the time of writing. This appears to be unverified or misleading information if presented as a newly confirmed Microsoft zero-day without official confirmation.
That does not mean users should ignore it. Browser password managers are convenient, but they become risky when the device is shared, infected, or used with administrator-level access. If malware already has high privileges on a machine, saved credentials can become a rich target.
For readers, the practical advice is calm but firm. Use a dedicated password manager, protect the device with full-disk encryption, avoid running daily accounts as local admin, keep Edge updated, and enable phishing-resistant MFA where available.
6. 2FA vs MFA: why the difference still matters
Two-factor authentication and multi-factor authentication are often used interchangeably, but they are not exactly the same. 2FA means exactly two factors. MFA means two or more factors. CISA explains that MFA may be listed as two-factor authentication, two-step authentication, or similar in account settings, and recommends turning it on for accounts and apps.
The bigger lesson is not the name. It is the strength of the method. SMS codes are better than password-only logins, but they can be phished, intercepted, or socially engineered. Authenticator apps are stronger. Hardware security keys and passkeys are stronger again because they are more resistant to fake login pages.
CISA has separately warned that phishing-resistant MFA is designed to prevent MFA bypass attacks and can include smartcards or FIDO security keys.
This cybersecurity weekly recap connects MFA to almost every other story here. Browser bugs, crypto scams, data breaches, and password theft all become worse when accounts depend only on passwords. MFA is not magic, but it often turns a stolen password from a disaster into a failed login attempt.
7. Global crypto scam crackdown shows fraud is now industrial
The U.S. Justice Department announced on April 29, 2026 that cooperation between the FBI, Dubai Police, and China’s Ministry of Public Security led to at least 276 arrests and the dismantling of at least nine scam centers tied to cryptocurrency investment fraud schemes. The DOJ said the centers targeted Americans who suffered millions of dollars in losses.
The scams described by prosecutors follow the familiar “pig-butchering” pattern. A scammer builds trust through friendship or romance, slowly introduces a fake crypto investment opportunity, shows fake profits, and then pushes the victim to send more money. Once funds move into the fake platform, the victim loses control.
The DOJ also said FBI San Diego’s Operation Level Up had notified almost 9,000 victims and saved an estimated $562 million as of April 2026.
This part of the cybersecurity weekly recap is personal. These scams do not always look technical. They look like a conversation. A wrong number text. A friendly LinkedIn message. A dating app match. A Telegram group. The technical part comes later, once trust has already done most of the work.
What crypto users should do
Do not trust investment advice from strangers who contact you first. Never send funds to a platform you cannot independently verify. Be suspicious of guaranteed returns, pressure to borrow money, or withdrawal fees that appear only after you “profit.” Victims in the U.S. should report to the FBI’s IC3, as DOJ guidance notes.
8. Biggest data breaches of 2025: the lesson is third-party exposure
The 2025 breach landscape was not only about massive record counts. It was about weak identity, vendors, cloud platforms, and delayed detection. Verizon’s 2025 DBIR analyzed more than 22,000 security incidents and 12,195 confirmed data breaches. It found that third-party involvement doubled to 30%, credential abuse accounted for 22% of initial access, and vulnerability exploitation accounted for 20%.
IBM’s 2025 Cost of a Data Breach Report placed the global average breach cost at $4.4 million, down 9% from the prior year, while also highlighting risks from AI adoption without proper governance and access controls.
This cybersecurity weekly recap uses those reports because they explain the “why” behind the news. Chrome vulnerabilities matter because browsers are entry points. DAEMON Tools matters because suppliers can become attack paths. MFA matters because stolen credentials still open too many doors. Copy Fail matters because one weak internal foothold can become full control.
1. Patch browsers first. Chrome 148 includes 127 security fixes, so delayed browser updates should be treated as endpoint risk, not a minor IT task.
2. Audit Linux exposure. Prioritize CVE-2026-31431 patching on servers, CI/CD runners, Kubernetes nodes, and shared Linux environments.
3. Review software supply chain trust. DAEMON Tools shows that official vendor downloads and valid signatures are not enough. Monitor behavior after installation.
4. Upgrade vm2 immediately. Any app running untrusted JavaScript should update vm2 and add a second isolation layer outside the Node.js process.
5. Move from basic 2FA to phishing-resistant MFA. Passkeys, FIDO2 keys, and device-bound authentication reduce the risk of credential phishing.
6. Warn users about crypto relationship scams. The scam often starts emotionally, not technically. Training should include real message examples, fake trading dashboards, and withdrawal-fee tricks.
|
Date |
Event |
|
April 8, 2026 |
DAEMON Tools trojanized installer distribution reportedly begins |
|
April 29, 2026 |
DOJ announces crypto scam center takedown |
|
May 1, 2026 |
CISA KEV entry for CVE-2026-31431 appears in NVD |
|
May 5, 2026 |
Chrome 148 stable release published |
|
May 7, 2026 |
Microsoft Edge 148 security release notes updated |
FAQs
What is the biggest cybersecurity risk this week?
The biggest enterprise risk is a mix of Copy Fail on Linux systems, vm2 sandbox escapes in developer environments, and DAEMON Tools supply chain exposure. For everyday users, Chrome updates and crypto scam awareness are the most urgent actions.
Is Chrome 148 safe after updating?
Chrome 148 includes important security fixes, including 127 security issues listed by Google. Updating reduces known risk, but users still need safe browsing habits, extension hygiene, and regular restarts after updates.
Is CVE-2026-31431 remotely exploitable?
Not by itself, based on Microsoft’s technical summary. It is a local privilege escalation flaw, meaning an attacker generally needs local code execution first. The danger is that it can turn a low-privilege foothold into root access.
Should I stop using browser password managers?
Not necessarily, but high-risk users should consider a dedicated password manager, phishing-resistant MFA, and stronger device security. The Edge story should be treated carefully because the reported memory behavior is not the same as an officially confirmed emergency CVE in Microsoft’s release notes.
Final takeaway
This cybersecurity weekly recap shows one clear lesson: trust needs verification. A browser update needs a restart. A Linux patch needs deployment. A sandbox needs isolation beyond library code. A signed installer needs behavior monitoring. A crypto opportunity needs independent proof. And a password needs MFA behind it.
The week’s stories look different on the surface, but they all point to the same practical habit: do not wait for a breach headline to check your controls. Patch what is exposed, limit what can run, verify what you install, and teach people how scams actually feel in real life. That is not dramatic. It is just the work that keeps small problems from becoming front-page incidents.
Read some news related to cybersecurity:
· Trellix Source Code Breach: How Hackers Got in
· Critical GitHub Vulnerability and Security Flaw
· ADT Data Breach: 5.5 Million Customers Affected
Published: May 08, 2026
Last Updated:May 08, 2026
Author: Radia, Cybersecurity Content Analyst
Was this article helpful?
React to this post and see the live totals.
Share this :